Azure Virtual WAN IPsec Tunnel Automation
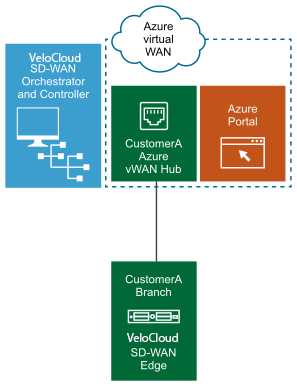
Arista's Edge Cloud Orchestrator supports integration and automation of Azure Virtual WAN from VeloCloud Gateway and VeloCloud Edge to enable Branch-to-Azure VPN Connectivity.
Azure Virtual WAN IPsec Tunnel Automation Overview
Azure Virtual WAN is a network service that facilitates optimized and automated Virtual Private Network (VPN) connectivity from enterprise branch locations to or through Microsoft Azure. Azure subscribers provision Virtual Hubs corresponding to Azure regions and connect branches (which may or may not be SD-WAN enabled) through IP Security (IPsec) VPN connections.
- IPsec from Gateway to Azure virtual WAN hub with automation.
- Direct IPsec from Edge to Azure virtual WAN hub with automation.
Azure Virtual WAN Gateway automation
The following diagram illustrates the IPsec tunnel from Gateway to Azure virtual WAN hub.
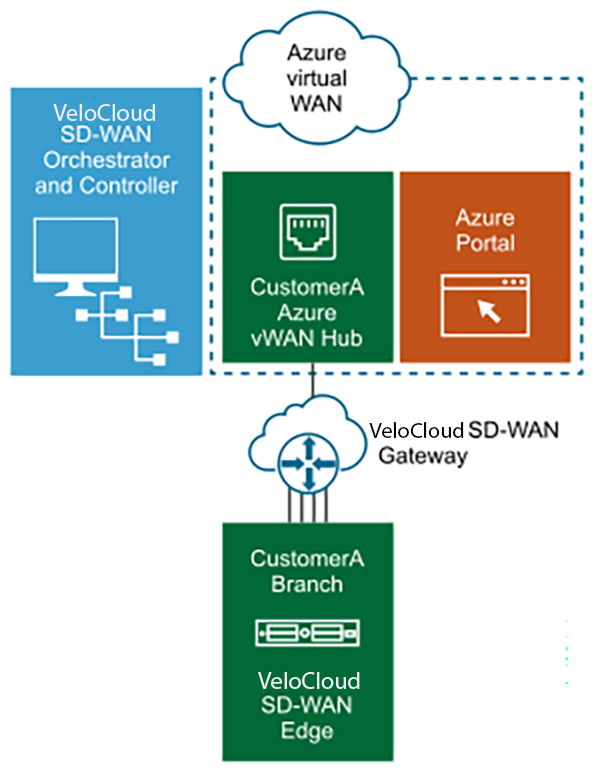
Azure Virtual WAN Edge automation
The following diagram illustrates the IPsec tunnel directly from Edge to Azure virtual WAN hub.
Prerequisite Azure Configuration
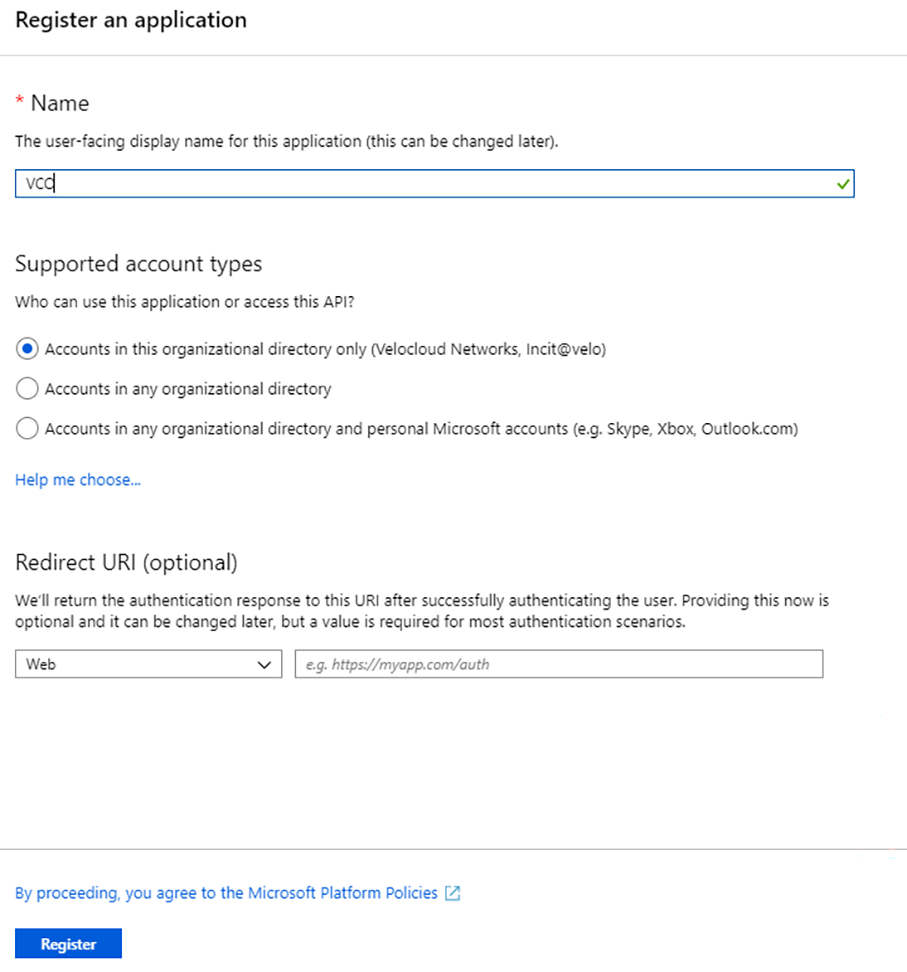
Register Orchestrator Application
To register a new application in Azure AD:
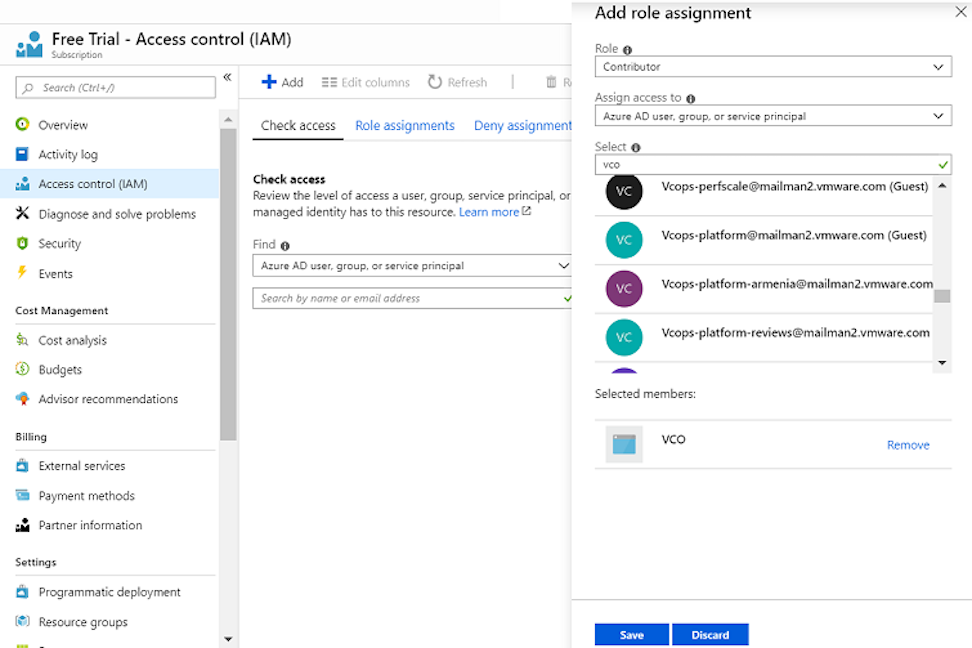
Assign the Orchestrator Application to Contributor Role
To access resources in your Azure subscription, you must assign the application to a role. You can set the scope at the level of the subscription, resource group, or resource. Permissions are inherited to lower levels of scope.
- Ensure you have an Azure subscription. If not, create a free account.
To assign a Contributor role at the subscription scope, use the following steps:
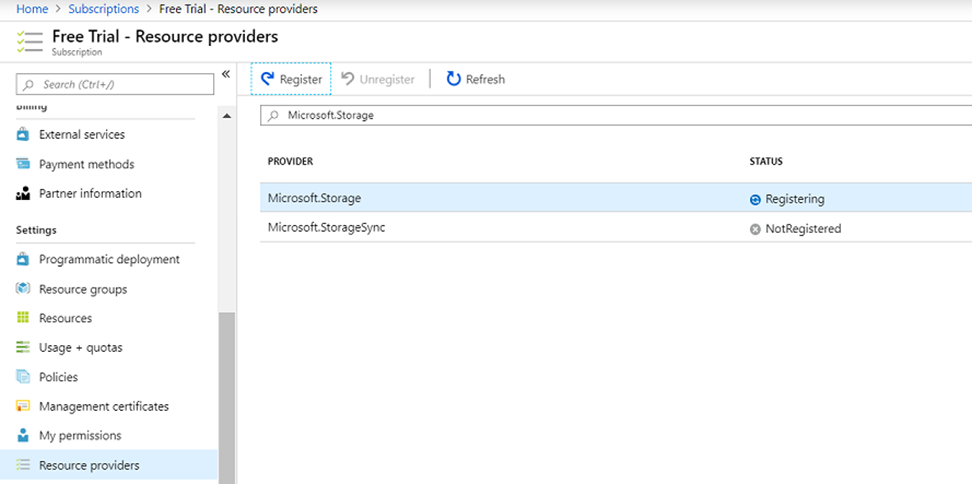
Register a Resource Provider
- Ensure you have an Azure subscription. If not, create a free account.
- Ensure you have the Contributor or Owner roles permission.
To register a resource provider for your subscription:
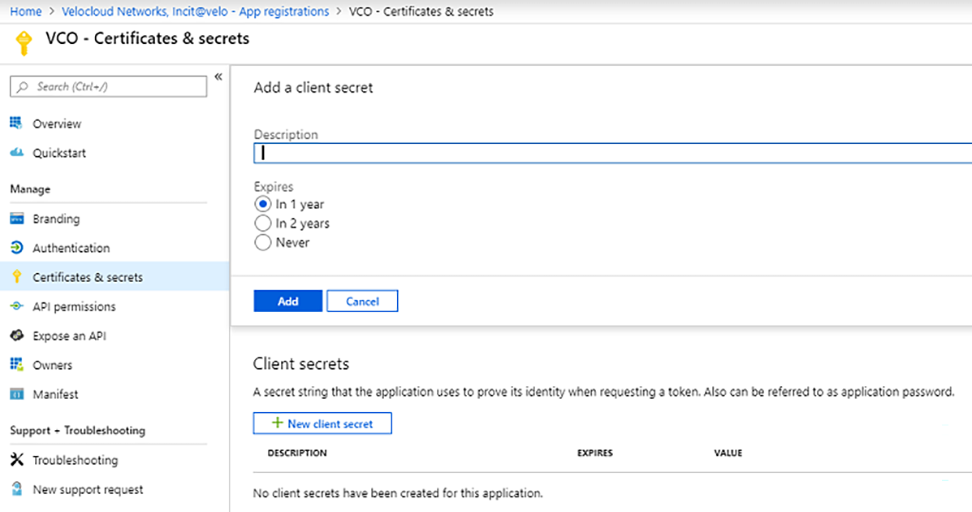
Create a Client Secret
Create a new client secret in Azure AD for the purpose of authentication.
Ensure you have an Azure subscription. If not, create a free account.
To create a new client secret in Azure AD:
Configure Azure Virtual WAN for Branch-to-Azure VPN Connectivity
This section discusses the procedures to configure Azure for integrating Azure Virtual WAN and Gateway to enable the branch-to-Azure VPN connectivity.
- Verify that none of the subnets of your on-premises network overlap with the existing virtual networks that you want to connect to. Your virtual network does not require a gateway subnet and cannot have any virtual network gateways. For steps to create a virtual network, see Create a Virtual Network.
- Obtain an IP address range for your Hub region and ensure that the address range that you specify for the Hub region does not overlap with any of your existing virtual networks that you connect to.
- Ensure you have an Azure subscription. If not, create a free account.
Create a Resource Group
Discusses how to create a resource group in Azure.
- Ensure you have an Azure subscription. If not, create a free account.
To create a resource group in Azure:
- Log in to your Microsoft Azure account. The Microsoft Azure home screen appears.
- Select All Services and search for Resource groups.
- Select Resource groups and select +Add. The Create a resource group screen appears.
Figure 7. Create a Resource Group Screen 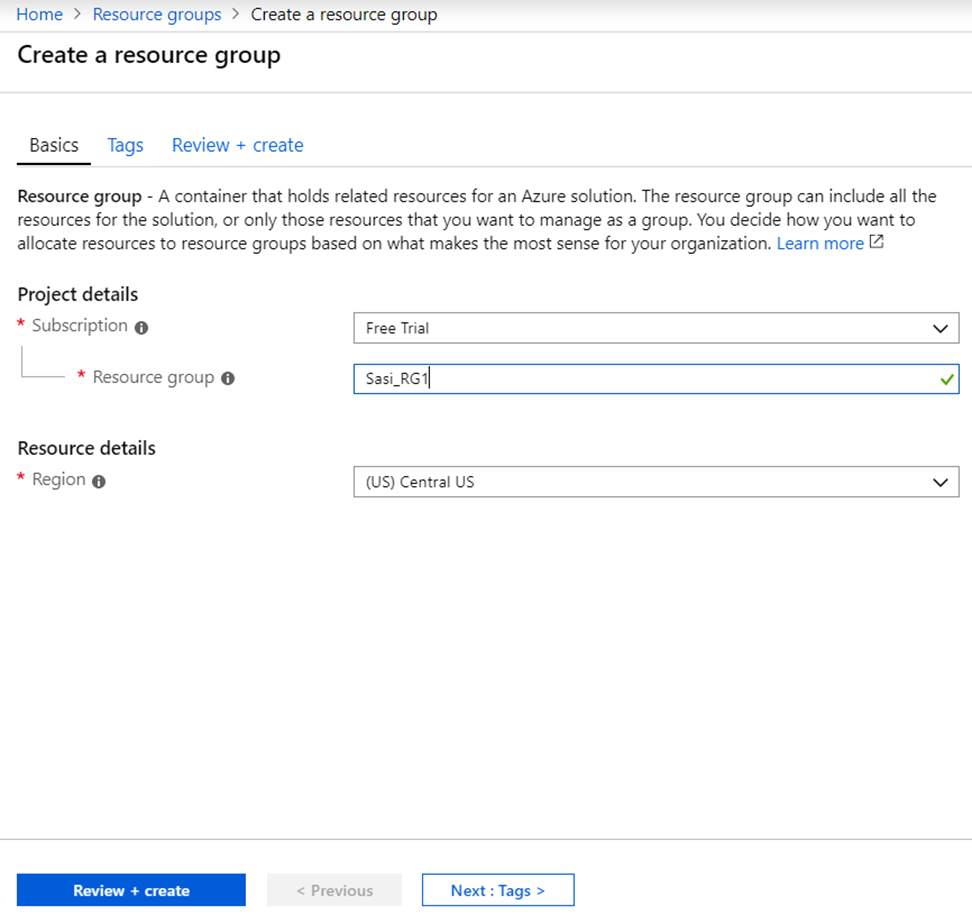
- From the Subscription drop-down menu, select your Microsoft Azure subscription.
- In the Resource group text box, enter a unique name for your new resource group.
A resource group name can include alphanumeric characters, periods (.), underscores (_), hyphens (-), and parenthesis (), but the name cannot end with a period.
- From the Region drop-down menu, select the location for your resource group, where the majority of your resources will reside.
- Select Review+create and then select Create.
A resource group is created and appears on the Azure portal dashboard.
Create an Azure Virtual WAN. For steps, see Create a Virtual WAN.
Create a Virtual WAN
Discusses how to create a Virtual WAN in Azure.
- Ensure you have an Azure subscription. If not, create a free account.
- Ensure you have a resource group created to add the Virtual WAN.
To create a Virtual WAN in Azure:
- Log in to your Microsoft Azure account. The Microsoft Azure home screen appears.
- Select All Services and search for Virtual WANs.
- Select Virtual WANs and select +Add. The Create WAN screen appears.
Figure 8. Create a WAN 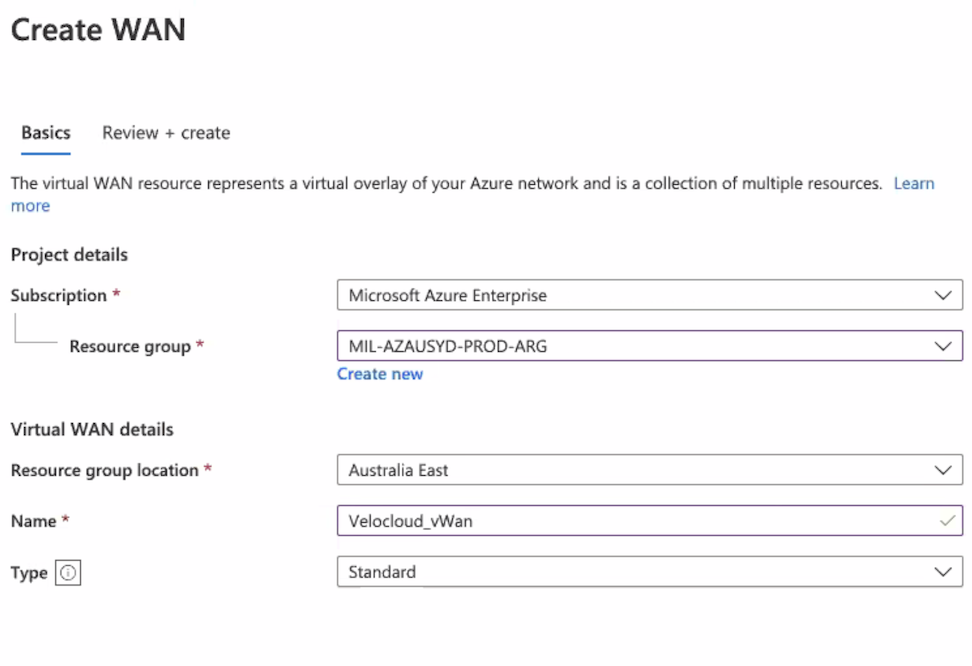
- From the Subscription drop-down menu, select your Microsoft Azure subscription.
- From the Resource group drop-down menu, select your resource group to add the Virtual WAN.
- From the Resource group location drop-down menu, select the location where the metadata associated with the Virtual WAN will reside.
- In the Name text box, enter a unique name for your Virtual WAN.
- From the Type drop-down menu, select Standard as the Virtual WAN type.
- Select Create.
A Virtual WAN is created and appears on the Azure portal dashboard.
Create Virtual Hubs. For steps, see Create a Virtual Hub.
Create a Virtual Hub
Describes how to create a Virtual Hub in Azure.
- Ensure you have an Azure subscription. If not, create a free account.
- Ensure that you have a resource group created to add the Azure resources.
To create a Virtual Hub in Azure:
- Log in to your Microsoft Azure account. The Microsoft Azure home screen appears.
- Go to All resources and from the list of available resources, select the Virtual WAN that you have created.
- Under the Virtual WAN architecture area, select Hubs.
- Select +New Hub. The Create virtual hub screen appears.
Figure 9. Create Virtual Hub Window 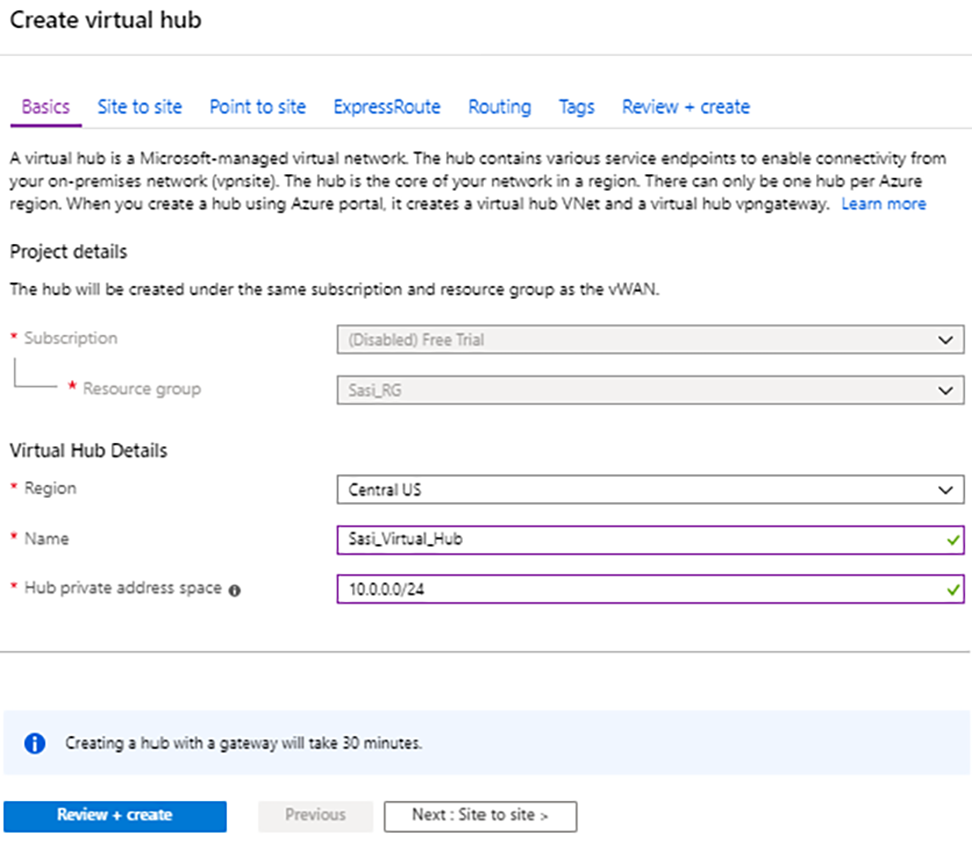
- In the Basics tab, enter the following Virtual Hub details.
- From the Region drop-down menu, select the location where the Virtual Hub resides.
- In the Name text box, enter the unique name for your Hub.
- In the Hub private address space text box, enter the address range for the Hub in Classless inter-domain routing (CIDR) notation.
- Select Next: Site to site > and enable Site to site (VPN gateway) before connecting to VPN sites by selecting Yes.
Note: A VPN Gateway is required for tunnel automation to work, otherwise it is not possible to create VPN connections.
Figure 10. Create Virtual HubSite to Site 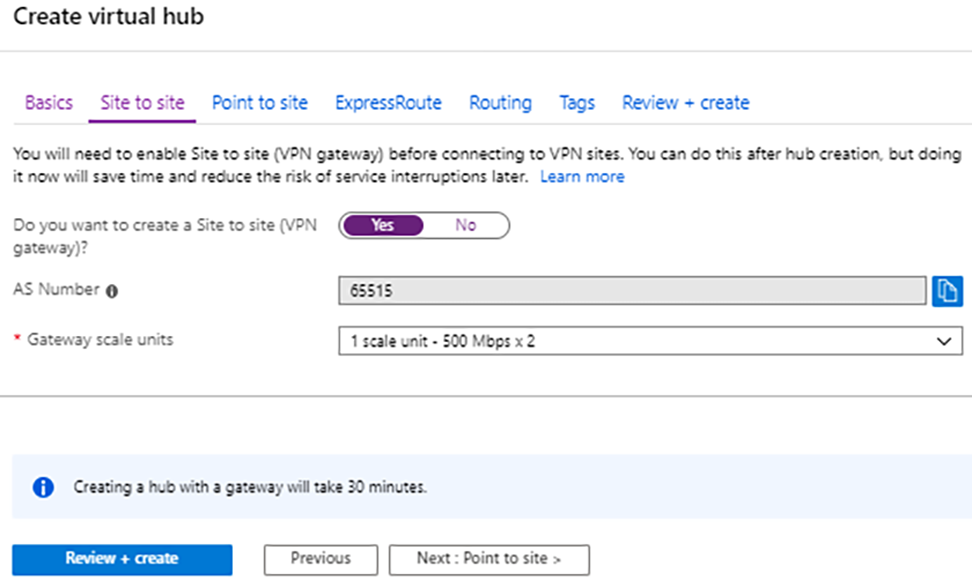
- From the Gateway scale units drop-down menu, select a scaling value.
- Select Review + Create.
- Create Virtual Connection between Hubs and Virtual Networks (VNets). For steps, see Create a Virtual Connection between VNet and Hub.
- If you do not have an existing VNet, you can create one by following the steps in Create a Virtual Network.
Create a Virtual Network
- Ensure you have an Azure subscription. If not, create a free account.
- Log in to your Microsoft Azure account. The Microsoft Azure home screen appears.
- Select All Services and search for Virtual networks.
- Select Virtual networks and select +Add. The Create virtual network screen appears.
Figure 11. Create Virtual Network Window 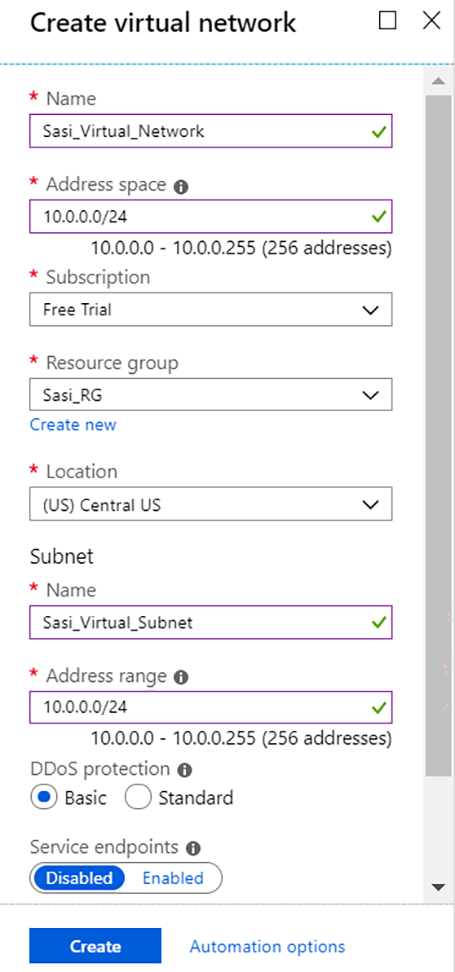
- In the Name text box, enter the unique name for your virtual network.
- In the Address space text box, enter the address range for the virtual network in Classless inter-domain routing (CIDR) notation.
- From the Subscription menu, select your Microsoft Azure subscription.
- From the Resource group menu, select your resource group to add the virtual network.
- From the Location menu, select the location where the virtual network resides.
- Under the Subnet area, enter the name and address range for the subnet.
Do not make any changes to the other default settings of DDoS protection, Service endpoints, and Firewall.
- Select Create.
A Virtual network is created and appears on the Azure portal dashboard.
Create Virtual Connection between Hubs and Virtual Networks (VNets). For steps, see Create a Virtual Connection between VNet and Hub.
Create a Virtual Connection between VNet and Hub
Discusses how to create a virtual connection between Virtual Networks (VNets) and the Virtual Hub in a particular Azure region.
- Ensure you have an Azure subscription.
- Ensure you have Virtual Hubs and Virtual Networks created.If not, create a free account.
- Log in to your Microsoft Azure account. The Microsoft Azure home screen appears.
- Go to All resources and from the list of available resources, select the Virtual WAN that you have created.
- Under the Virtual WAN architecture area, select Virtual network connections.
- Select +Add connection. The Add connection screen appears.
Figure 12. Add Connection Window 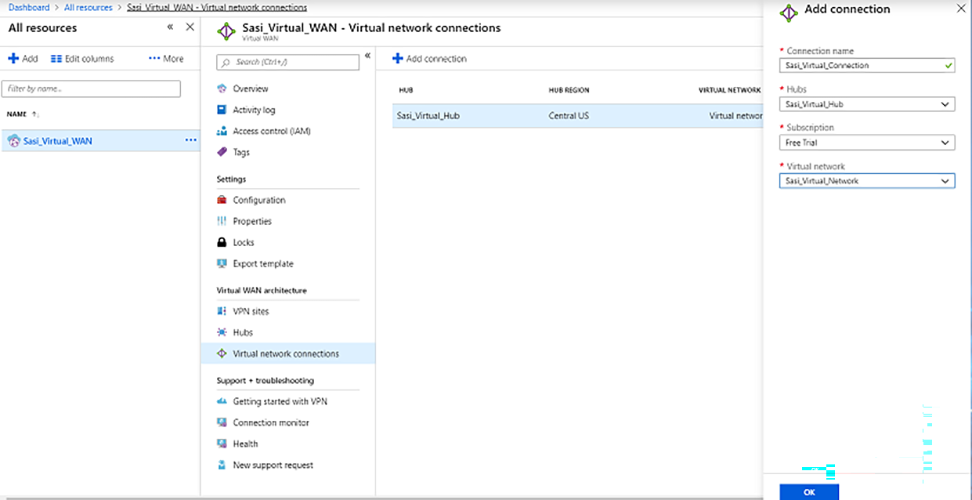
- In the Connection name text box, enter the unique name for the virtual connection.
- From the Hubs menu, select the Hub you want to associate with this connection.
- From the Subscription menu, select your Microsoft Azure subscription.
- From the Virtual network menu, select the virtual network you want to connect to this Hub.
- Select OK.
A peering connection establishes between the selected VNet and the Hub.
Configure Orchestrator for Azure Virtual WAN IPsec Automation from Gateway
You can configure Orchestrator for integrating Azure Virtual WAN and Gateway to enable the branch-to-Azure VPN connectivity.
session.options.enableAzureVirtualWAN system property to true.Before you begin the Orchestrator configuration for Azure Virtual WAN- Gateway automation, ensure you have completed all the steps explained in the Prerequisite Azure Configuration and Configure Azure Virtual WAN for Branch-to-Azure VPN Connectivity sections.
To view the details of Non SD-WAN Destinations network services configured for an enterprise, see Monitor Non SD-WAN Destinations.
Associate a Microsoft Azure Non SD-WAN Destination to an SD-WAN Profile
After configuring a Non SD-WAN Destination of type Microsoft Azure Virtual Hub in Orchestrator, you must associate the Non SD-WAN Destination to the desired Profile to establish the tunnels between Gateways and Microsoft Azure Virtual Hub.
- In the SD-WAN service of the Enterprise portal, go to . The Profiles page appears.
- Select a profile you want to associate your Microsoft Azure Non SD-WAN Destination with, and then select the View link in the Device column.
- In the Device settings page, under VPN services, activate Cloud VPN by turning on the toggle button.
Figure 13. Branch to Branch VPN Window 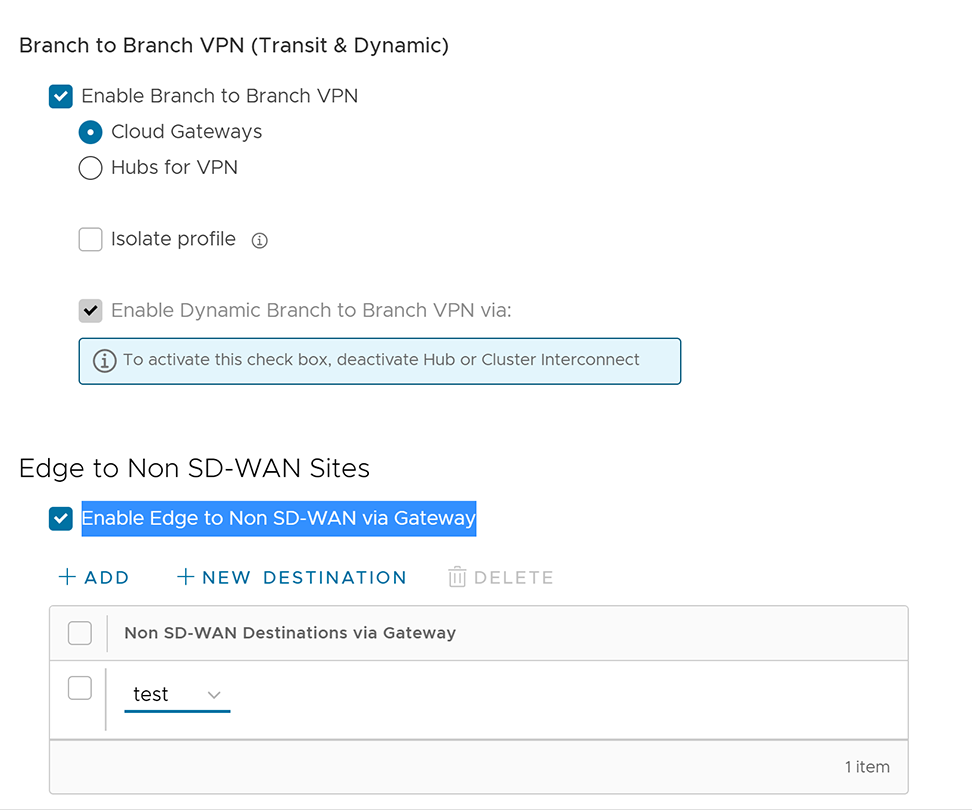
- Under Edge to Non SD-WAN Sites, select the Enable Edge to Non SD-WAN via Gateway check box.
- From the drop-down menu, select your Non SD-WAN Destination of type Microsoft Azure Virtual Hub to establish VPN connection between the branch and the Microsoft Azure Non SD-WAN Destination.
- Select Save Changes.
A tunnel establishes between the branch and the Microsoft Azure Non SD-WAN Destination.
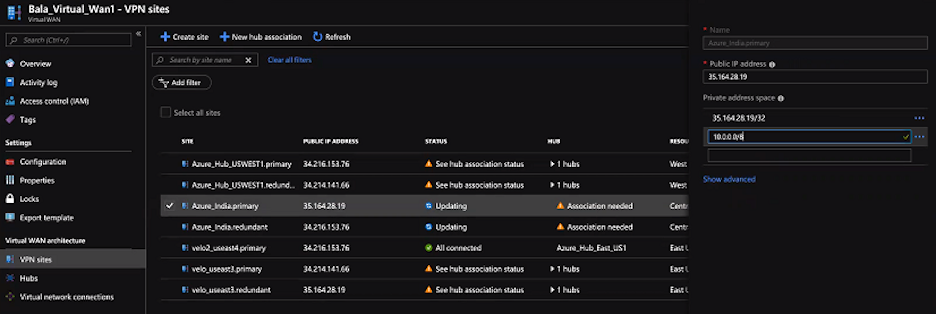
Edit a VPN Site
Describes how to add SD-WAN routes into the Azure network manually.
Ensure you have completed provisioning the Azure VPN sites at the Orchestrator side.
To add SD-WAN routes manually into the Azure network:
Synchronize VPN Configuration
After successful Non SD-WAN Destination provisioning, whenever changes occur on the endpoint IP address of the Azure Hub or static routes, you need to resynchronize Azure Virtual Hub and Non SD-WAN Destination configurations. Clicking the Resync configuration button in the Non-VeloCloud Sites area automatically obtains the VPN configuration details from the Azure portal and updates the Orchestrator local configuration.
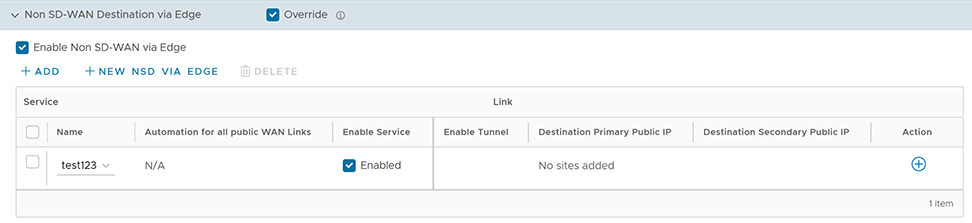
Configure Orchestrator for Azure Virtual WAN IPsec Automation from Edge
You can configure Orchestrator for integrating Azure Virtual WAN and Edge to enable the branch-to-Azure VPN connectivity directly from Edge.
Before you begin, the Orchestrator configuration for Azure Virtual WAN- Edge automation, ensure you have completed all the steps explained in the Prerequisite Azure Configuration and Configure Azure Virtual WAN for Branch-to-Azure VPN Connectivity sections.
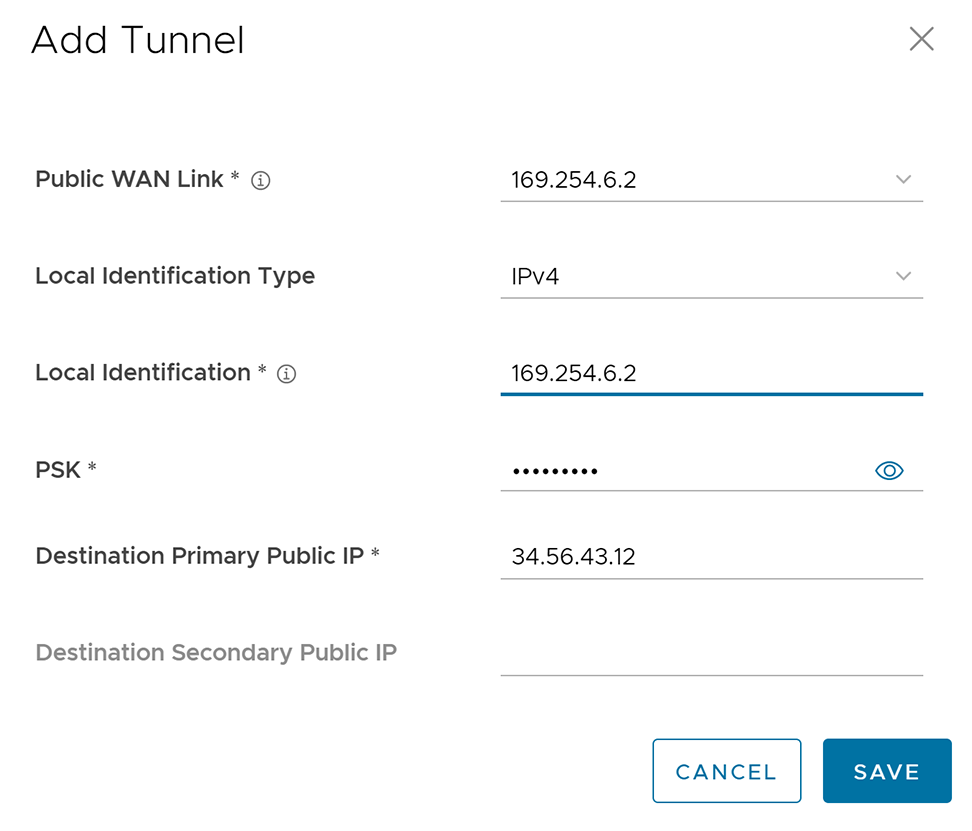
Associate a Microsoft Azure Non SD-WAN Destination to an Edge and Add Tunnels
At the Edge level, to associate a Non SD-WAN Destination to an Edge, perform the following steps:
Monitor Non SD-WAN Destinations
You can view the details of Non SD-WAN Destinations configured for the Enterprise from the MonitorNetwork Services page in the SD-WAN service of the Enterprise portal.
- Non SD-WAN Destinations via Gateway- Displays the configured Non SD-WAN Destinations along with the other configuration details such as Name of the Non SD-WAN Destination, Public IP Address, Status of the Non SD-WAN Destination, Status of the tunnel, Number of profiles and Edges that use the Non SD-WAN Destination, Last contacted date and time, and Number of related state change Events.
- Non SD-WAN Destinations via Edge- Displays the configured Non SD-WAN Destinations along with the other configuration details such as Name of the Non SD-WAN Destination, Public IP Address, Status of the tunnel, Number of profiles and Edges that use the Non SD-WAN Destination, Last contacted date and time, and Deployment status.
Note: Tunnel deployment status monitoring is only supported for Non SD-WAN Destinations via Edge network service.
To monitor the automation deployment status of Microsoft Azure Non SD-WAN Destinations via Edge:
- In the SD-WAN service of the Enterprise portal, select .
The Network Services page appears.
- Under Non SD-WAN Destinations via Edge, select the link in the Deployment Status column to view the deployment status of the Non SD-WAN Destinations.
Figure 17. Network Services Screen 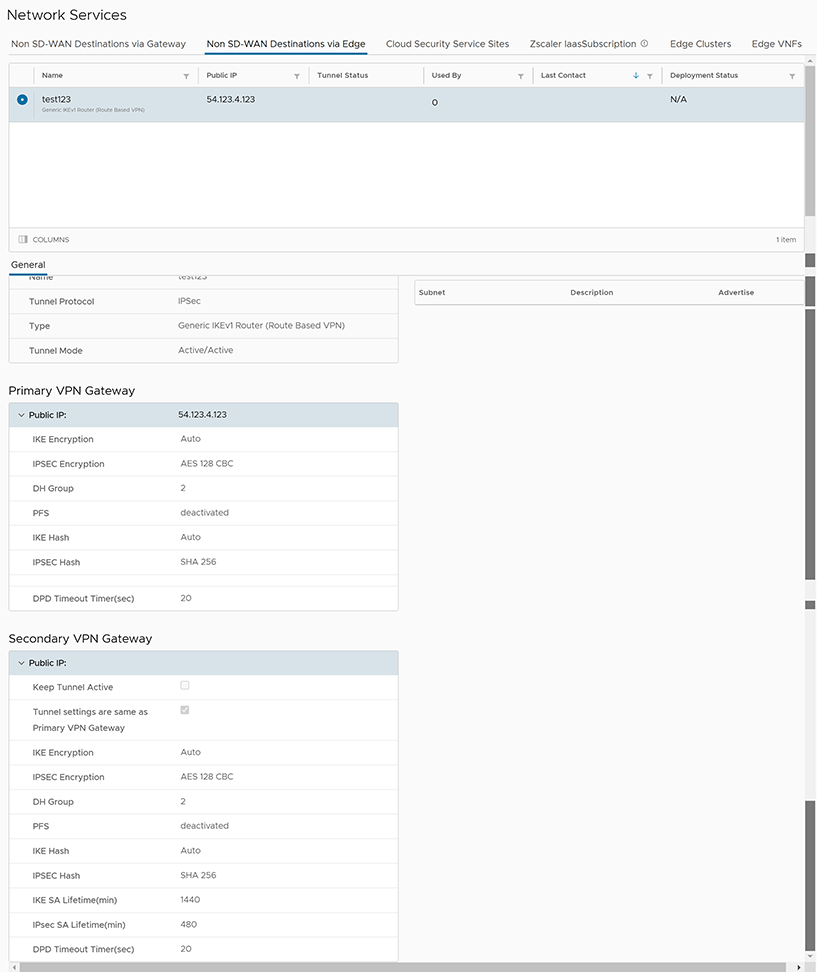 The following are the seven different states for an Edge action:
The following are the seven different states for an Edge action:- Enqueued- The Edge action is enqueued.
- Pending- The Edge action is in this state as it waits for a backend worker process to pick it up and start working on it.
- Notified- The Edge action is in this state after a backend worker process picks up the Edge action and starts working on it.
- Completed- The Edge action is in this state if the Edge action task is successfully completed.
- Errored- The Edge action is in this state if an error has occurred.
- Timed Out- The Edge action is in this state if it takes more than the expected amount of time to complete the Edge action task.
- Pending Delete- The Edge action is in this state if it is pending deletion.