VeloCloud SD-WAN in Azure Virtual WAN Hub Deployment
About VeloCloud in Azure Virtual WAN Hub Deployment
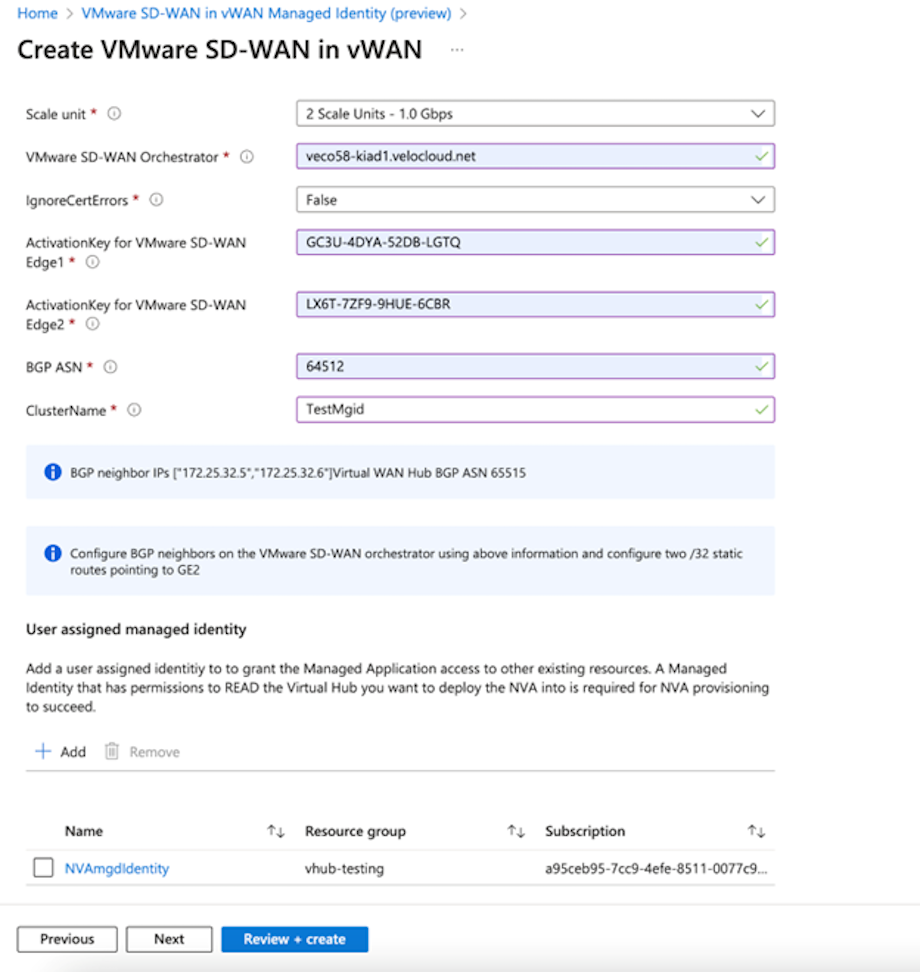
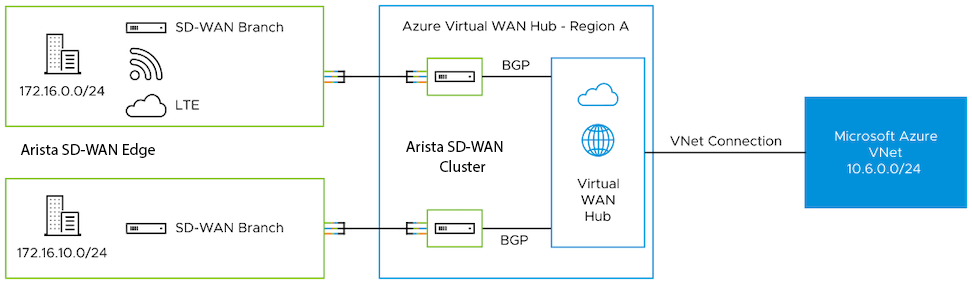
The VeloCloud SD-WAN in Azure Virtual WAN (vWAN) Hub deployment describes the configurations required to manually deploy a Virtual Edge as a Network Virtual Appliance (NVA) in Azure vWAN Hub network.
Overview
During cloud migration, users encountered a lot of challenges with connecting remote locations to Azure vNets in a simple, optimized, and secure way across myriad connectivity options. VeloCloud SD-WAN addresses these problems by leveraging Dynamic Multipath Optimization ™ (DMPO) technologies and distributed cloud gateway coverage across the globe. VeloCloud SD-WAN transforms the unpredictable broadband transport to Enterprise-class quality connections, ensuring the application performance from remote locations to Azure Cloud.
To meet different deployment scenarios for customers deploying Azure Virtual WAN, VeloCloud SD-WAN has progressively added more capabilities to the solution. With this new integration, customers can now manually deploy VeloCloud Edges directly inside Azure Virtual WAN hubs resulting in an offering that natively integrates Azure Virtual WAN customizable routing intelligence with VeloCloud SD-WAN optimized last-mile connectivity.
Deploy VeloCloud SD-WAN in Azure Virtual WAN Hub
To deploy VeloCloud Edges in a Virtual Hub manually, you must already have a Resource Group, virtual WAN (vWAN), and virtual Hub (vHUB) on the Azure side.
- Obtain Enterprise account access to VeloCloud Orchestrator.
- Obtain access to the Microsoft Azure portal with the appropriate IAM roles.
- Software image requirements for this deployment are as follows:
- VeloCloud Orchestrator - 6.4.0 and later.
- VeloCloud Gateway - 6.4.0 and later.
- VeloCloud Edges - 6.1.0.1 and later.
Note: The customer must either avoid upgrading to a different image post-activation or upgrade to version 6.1.0.0; otherwise, SSH access to the NVAs will fail due to a bug.
- Create an Azure Managed Identity. For steps, see Create Managed Identity.
Create Managed Identity
This section describes the steps to create an Azure Managed Identity.
- Under Subscription, create a Custom Role say ‘vWANNVACustomRole’ with the following permissions.
"permissions": [ { "actions": [ "Microsoft.Network/publicIPAddresses/join/action", "Microsoft.Network/publicIPAddresses/read", "Microsoft.Network/networkVirtualAppliances/delete", "Microsoft.Network/networkVirtualAppliances/read", "Microsoft.Network/networkVirtualAppliances/write", "Microsoft.Network/networkVirtualAppliances/restart/action", "Microsoft.Network/networkVirtualAppliances/getDelegatedSubnets/action", "Microsoft.Network/virtualHubs/read" ], "notActions": [], "dataActions": [], "notDataActions": [] } ] - Create a new user-assigned managed identity such as NVAmgdIdentity in the desired Managed Group and Region.
Figure 13. Creating a New Managed Identity 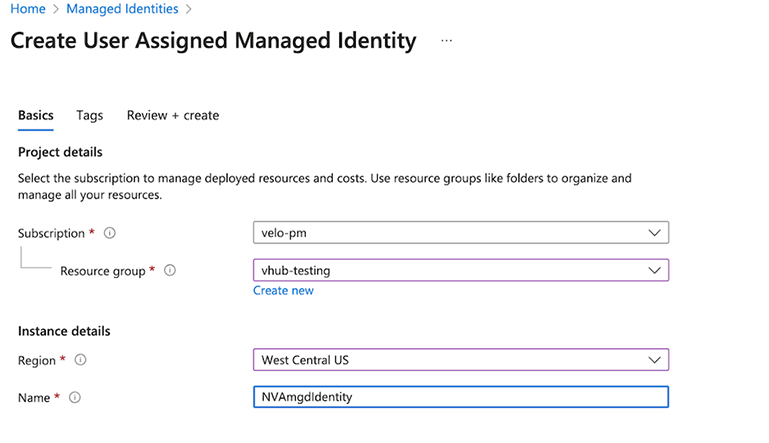
- Under the resource group where the vWAN Hub is deployed, assign the Managed Identity by navigating to .
In the Add role assignment screen, under the Role tab search for the custom role that you created, vWANNVACustomRole.
Figure 14. Adding Role Assignment 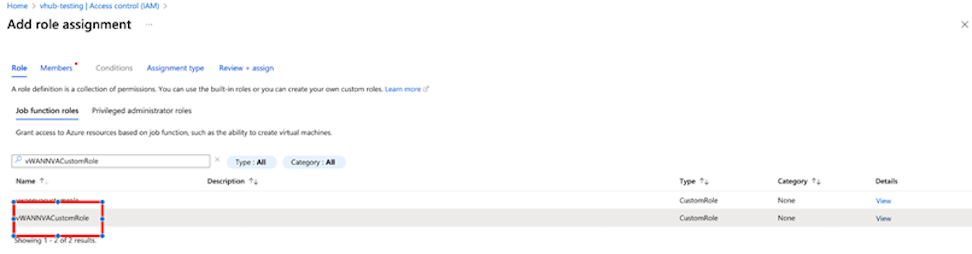
-
In the Members tab, select Managed Identity. In the Select managed identities section that appears on the right-side of the page, select the user assigned managed identity 'NVAmgdIdentity' that you have previously created and select Select. The selected managed identity appears under the Selected Members area.
Figure 15. Members 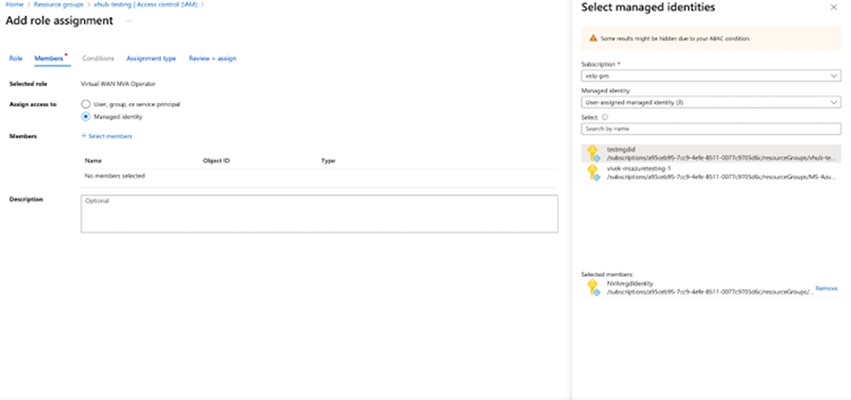
-
Select Review+Assign to assign the selected Managed Identity the custom role with scope as the resource group with the deployed vWAN hub.