Configure Tunnels on VeloCloud Gateway
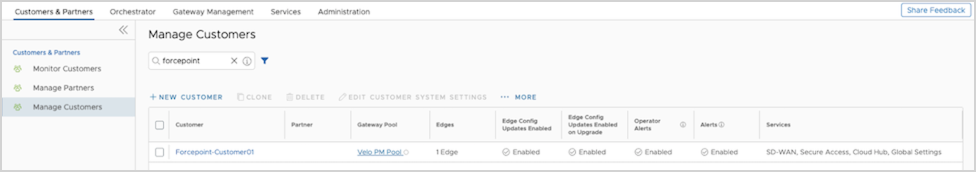
Configure the SD-WAN layer of Orchestrator using a Gateway as the endpoint for the tunnels between VeloCloud SD-WAN and Forcepoint Cloud Security Gateway. Ensure that you have configured the customer.
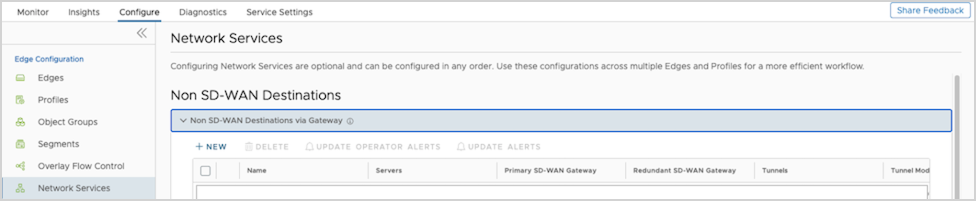
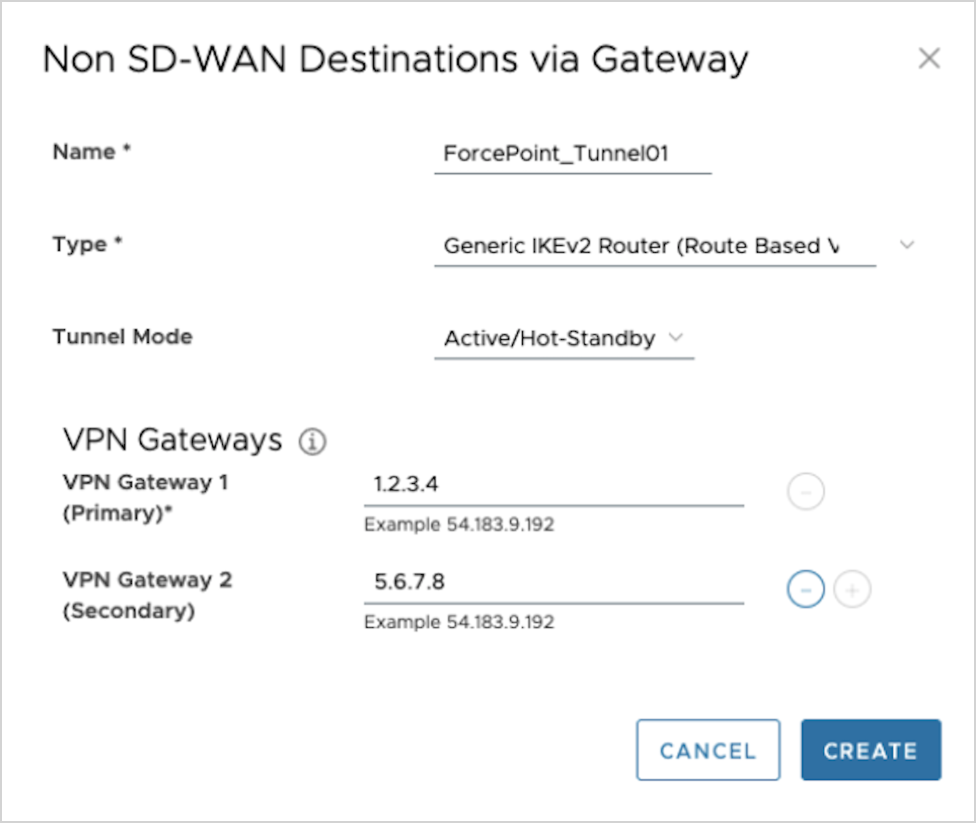
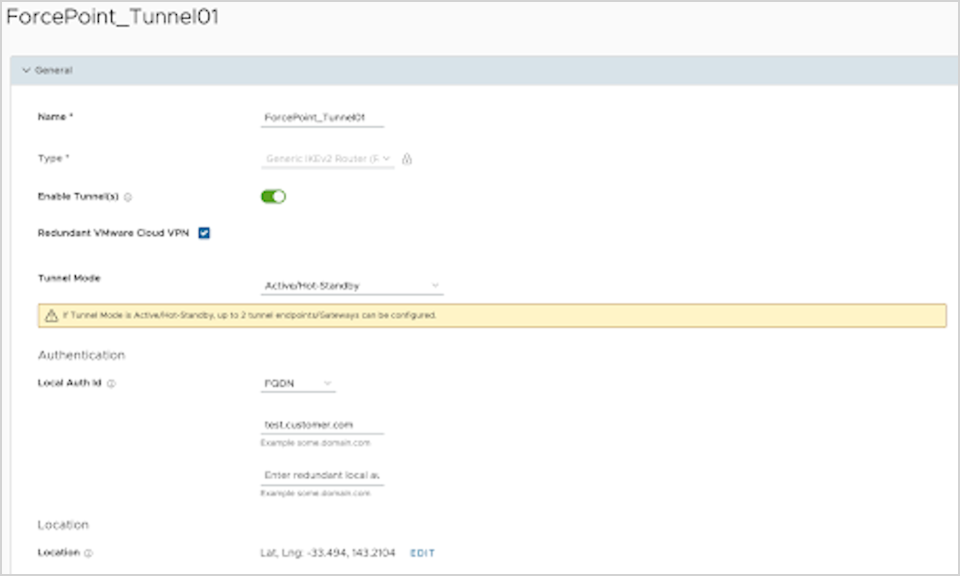
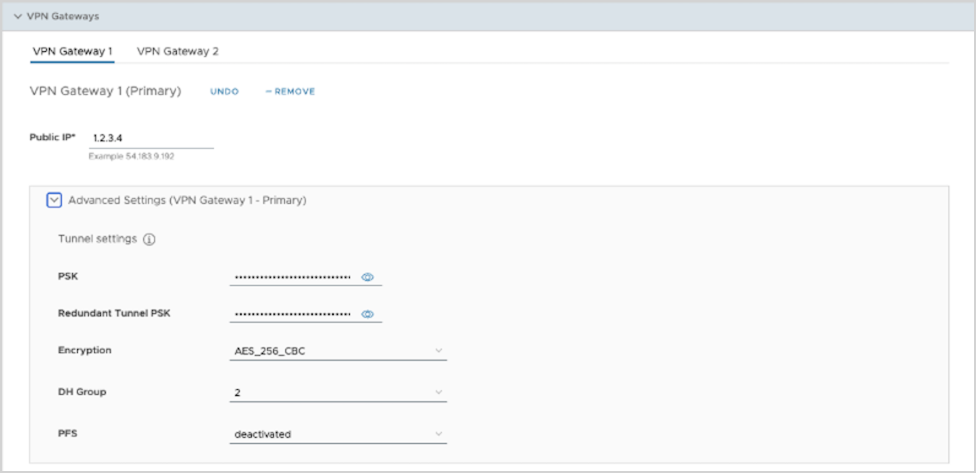
Configure Non SD-WAN Destination via Gateway
You can define and configure a Non SD-WAN Destination instance as Forcepoint Cloud Security Gateway and establish a secure IPsec tunnel to the Forcepoint Cloud Security Gateway through a VeloCloud Gateway.
Ensure that you have Administrator privileges to login to VeloCloud Edge Cloud Orchestrator.
To configure a Non SD-WAN Destination via Gateway:
Configure Profile to use the new Non SD-WAN Destination via Gateway. See Configure Profile with Non SD-WAN Destination via Gateway.
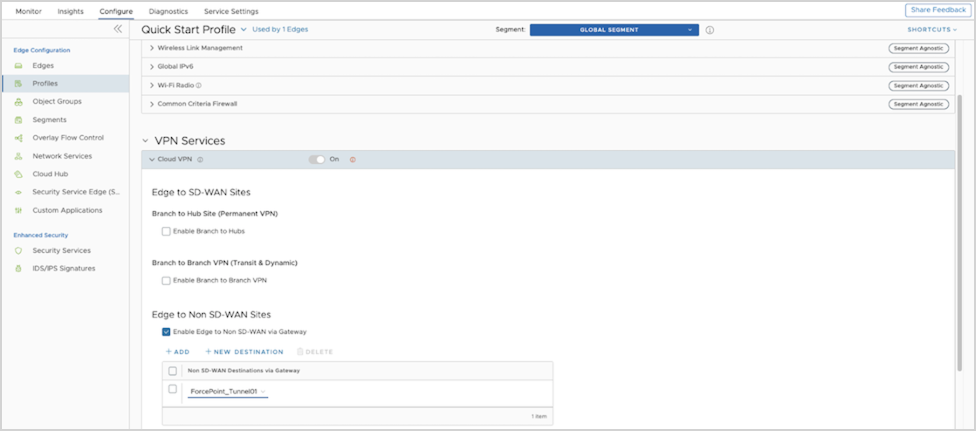
Configure Profile with Non SD-WAN Destination via Gateway
You can configure a profile to establish a VPN connection between a branch and a Non SD-WAN Destination via Gateway.
Ensure that you have created a Non SD-WAN Destination via Gateway with the required IPsec tunnel parameters relevant to Forcepoint Cloud Security Gateway. To create a Non SD-WAN Destination via Gateway, see Configure Non SD-WAN Destination via Gateway.
Create a Business Policy to route the traffic from the Non SD-WAN Destination tunnel to the Forcepoint Cloud Security Gateway. See Create Business Policy for Non SD-WAN Destination via Gateway.
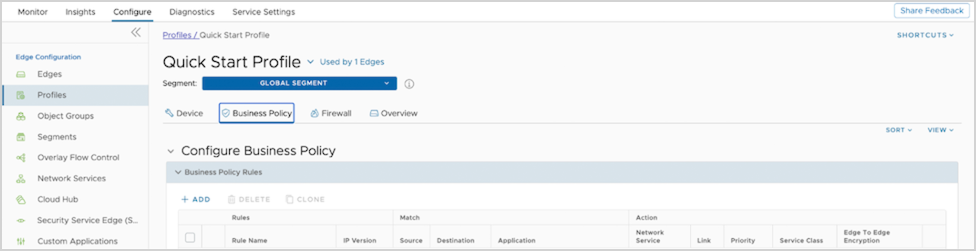
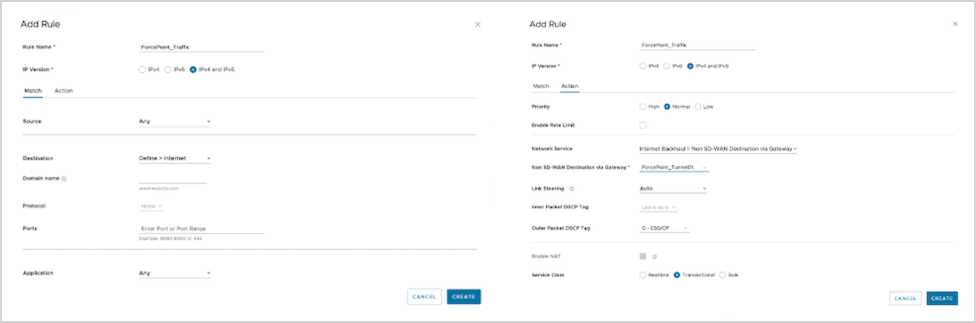
Create Business Policy for Non SD-WAN Destination via Gateway
After you establish a VPN connection between a branch and a Non SD-WAN Destination via Gateway, create a Business Policy to route the traffic from the Non SD-WAN Destination tunnel.
Ensure that you have established the VPN connection between branch and Non SD-WAN Destination via Gateway. See Configure Profile with Non SD-WAN Destination via Gateway.
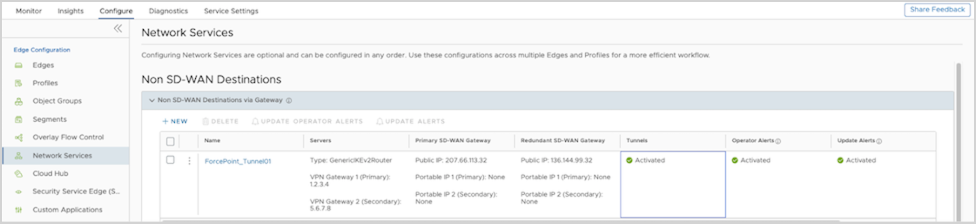
You can verify that the tunnel is online by monitoring the Network Services. See Monitor Non SD-WAN Destination via Gateway.
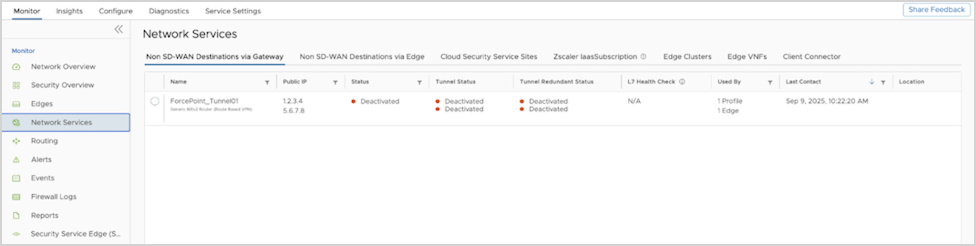
Monitor Non SD-WAN Destination via Gateway
You can monitor and verify the Non SD-WAN Destination Tunnel configuration using the Monitoring tab.
To monitor the Non SD-WAN Destination Tunnel configuration: