Configure Tunnels on VeloCloud Edge
Configure the SD-WAN layer of Orchestrator using an Edge as the endpoint for the tunnels between VeloCloud SD-WAN and Forcepoint Cloud Security Gateway. Ensure that you have configured the customer.
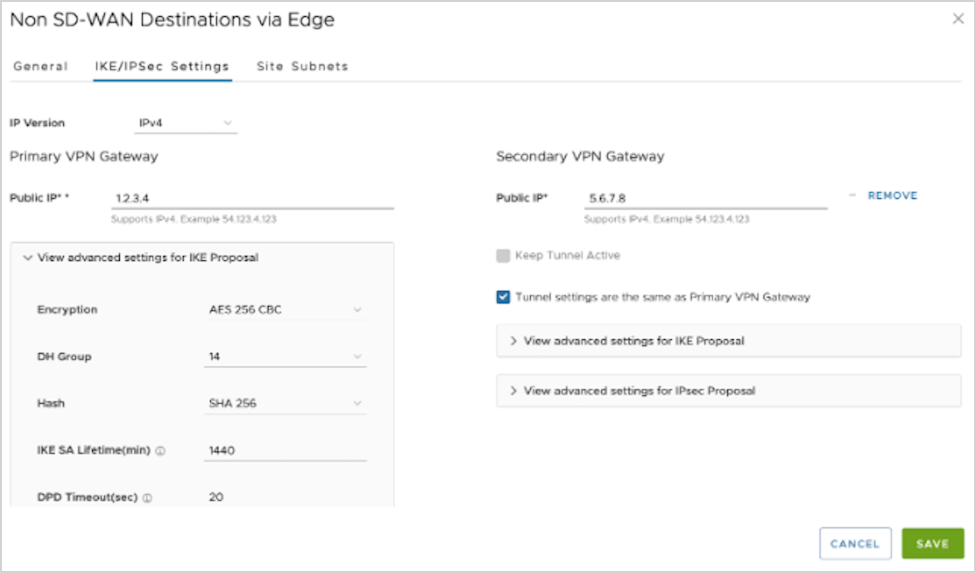
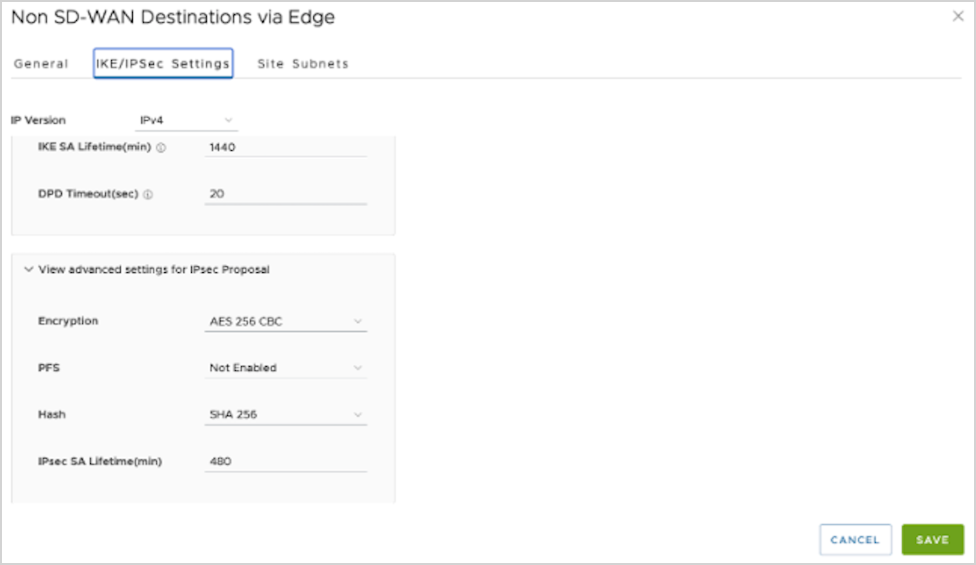
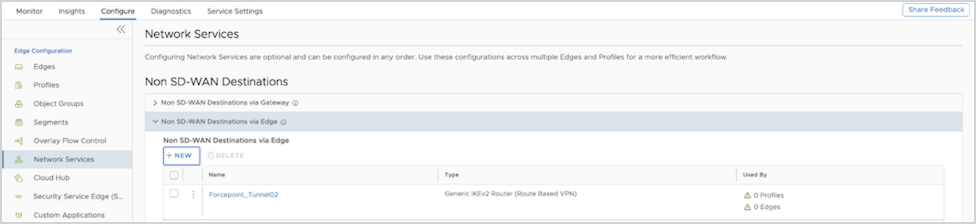
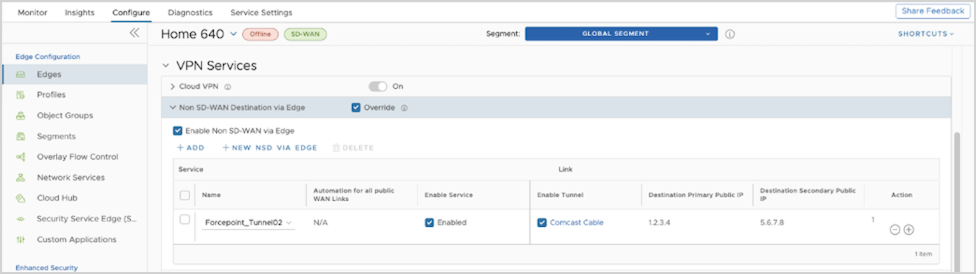
Configure Non SD-WAN Destination via Edge
You can define and configure a Non SD-WAN Destination instance as Forcepoint Cloud Security Gateway and establish a secure IPsec tunnel to the Forcepoint Cloud Security Gateway through a VeloCloud Edge.
Ensure that you have Administrator privileges to login to VeloCloud Edge Cloud Orchestrator.
To configure a Non SD-WAN Destination via Edge:
Configure a profile to use the new Non SD-WAN Destination via Edge. See Configure Profile with Non SD-WAN Destination via Edge.
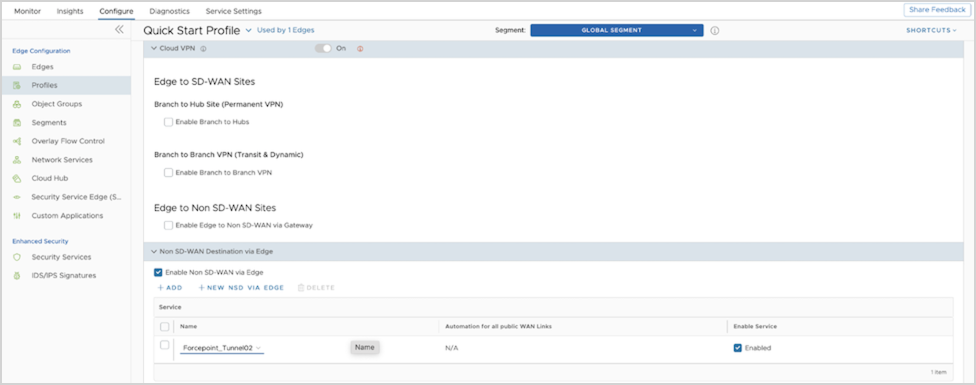
Configure Profile with Non SD-WAN Destination via Edge
You can configure a profile to establish a VPN connection between a branch and a Non SD-WAN Destination via Edge.
Ensure that you have created a Non SD-WAN Destination via Edge with the required IPsec tunnel parameters relevant to Forcepoint Cloud Security Gateway. To create a Non SD-WAN Destination via Edge, see Configure Non SD-WAN Destination via Edge.
Create a Business Policy to route the traffic from the Non SD-WAN Destination tunnel to the Forcepoint Cloud Security Gateway. See Create Business Policy for Non SD-WAN Destination via Edge.
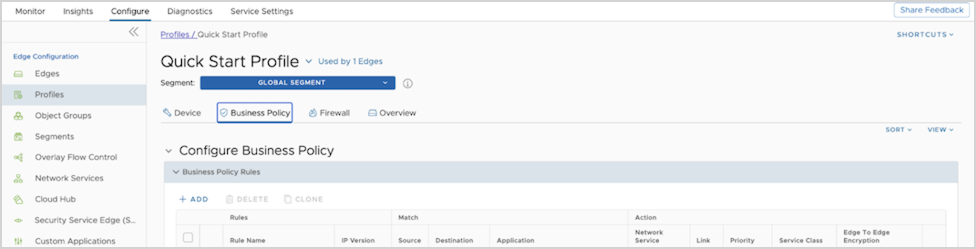
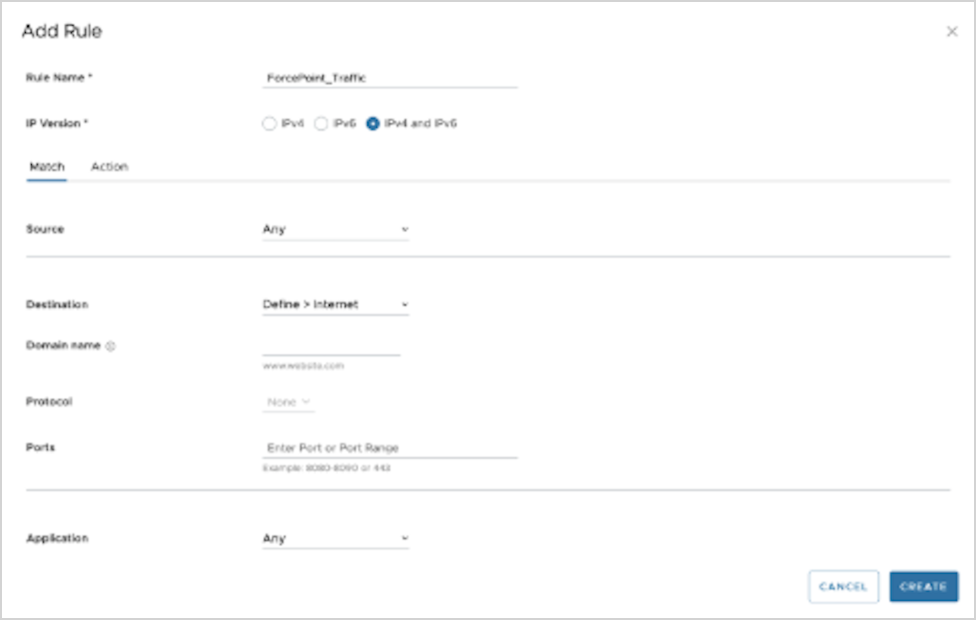
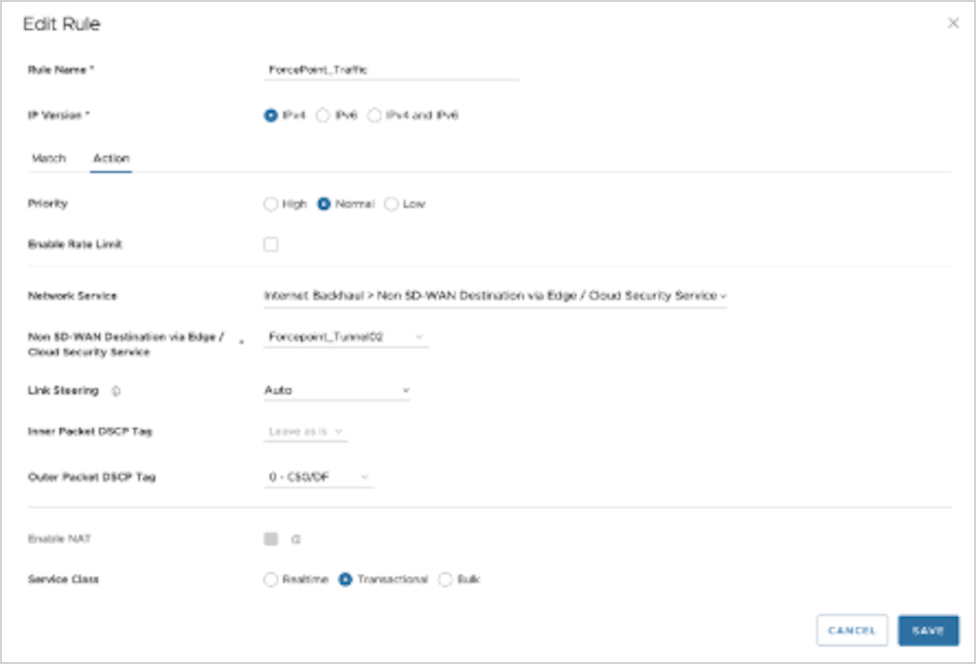
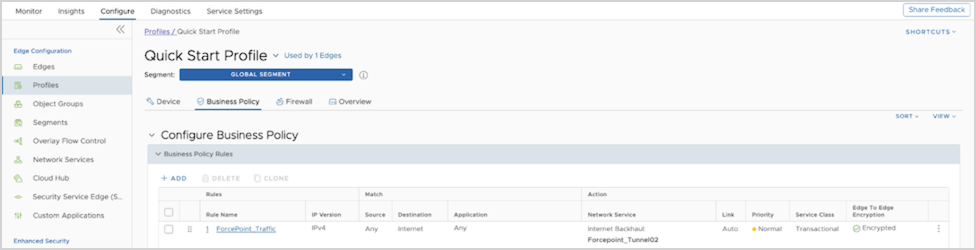
Create Business Policy for Non SD-WAN Destination via Edge
After you establish a VPN connection between a branch and a Non SD-WAN Destination via Edge, create a Business Policy to route the traffic from the Non SD-WAN Destination tunnel.
Ensure that you have established the VPN connection between branch and Non SD-WAN Destination via Edge. See Configure Profile with Non SD-WAN Destination via Edge.
Configure the Tunnel parameters for a selected Edge. See Configure Edge with Tunnel Parameters.
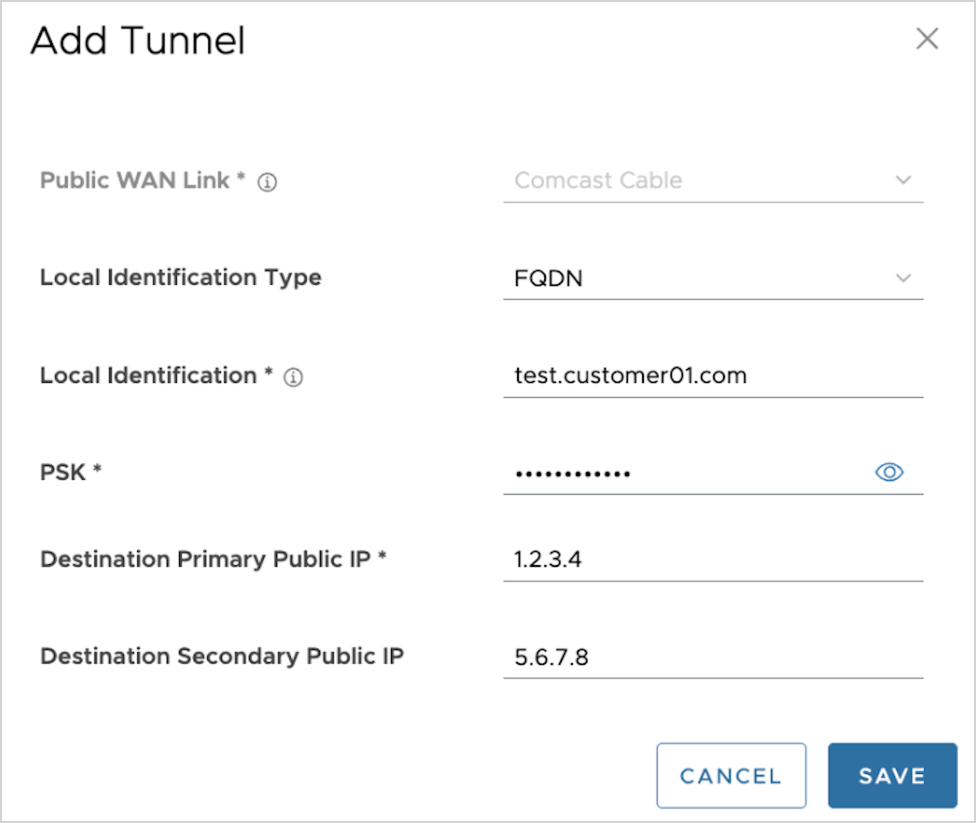
Configure Edge with Tunnel Parameters
When you configure a profile to establish a VPN connection between a branch and a Non SD-WAN Destination via Edge, the settings are automatically applied to all the Edges that are associated with the profile. You can configure the Tunnel parameters for an individual Edge and choose the source of the Tunnel as the WAN IP address.
Ensure that you have established the VPN connection between branch and Non SD-WAN Destination via Edge. See Configure Profile with Non SD-WAN Destination via Edge.
To configure the tunnel parameters for an Edge:
Verify that the tunnel is online by monitoring the Edges. See Monitor Non SD-WAN Destination via Edge.
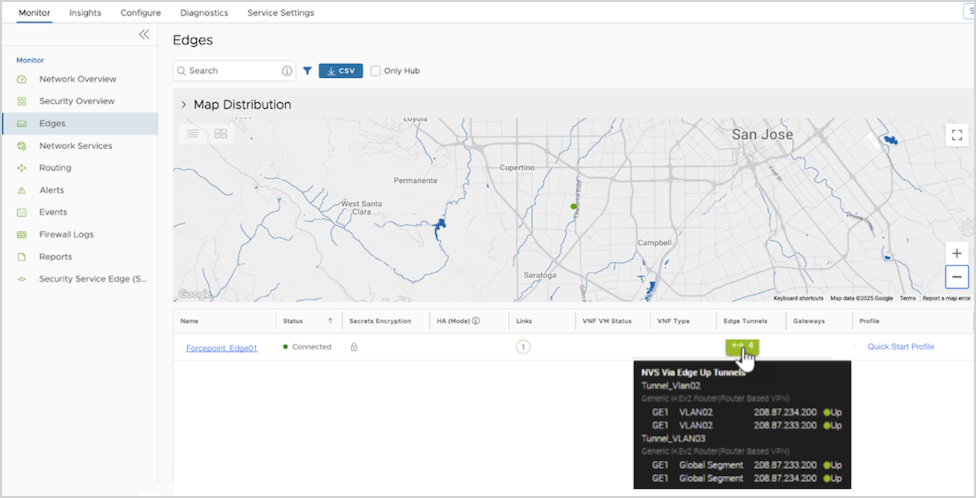
Monitor Non SD-WAN Destination via Edge
You can monitor and verify the Non SD-WAN Destination Tunnel configuration using the Monitoring tab.
To monitor the Non SD-WAN Destination Tunnel configuration: