Configuring Amazon Web Services
VeloCloud supports Amazon Web Services (AWS) configuration in Non SD-WAN Destination.
- Obtain Public IP, Inside IP, and PSK details from the Amazon Web Services website.
- Enter the details you obtained from the AWS website into the Non SD-WAN Network Service in the Orchestrator.
Configure Edge for Amazon Web Services (AWS) Transit Gateway (TGW) Connect Service
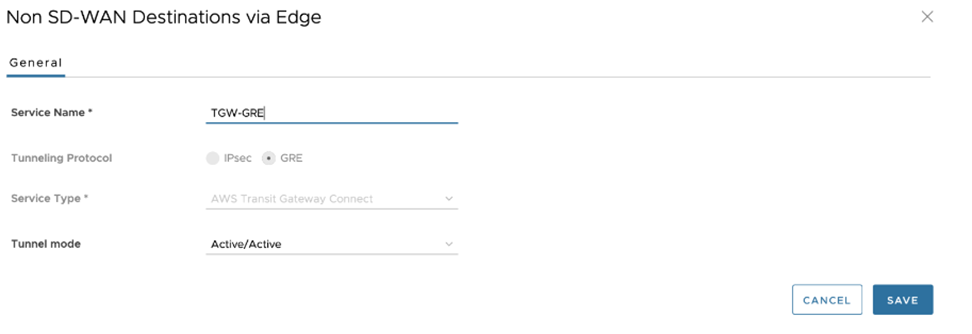
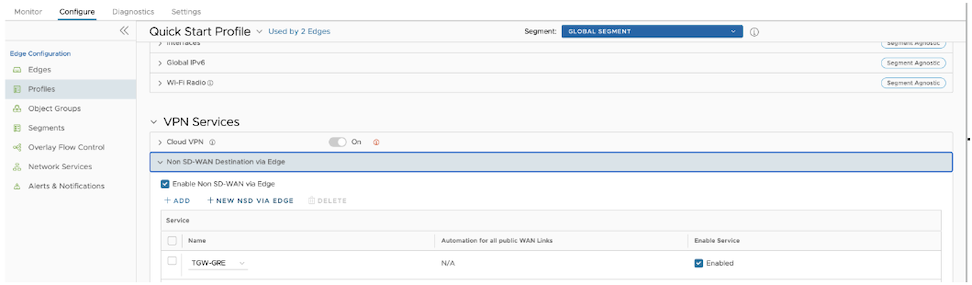
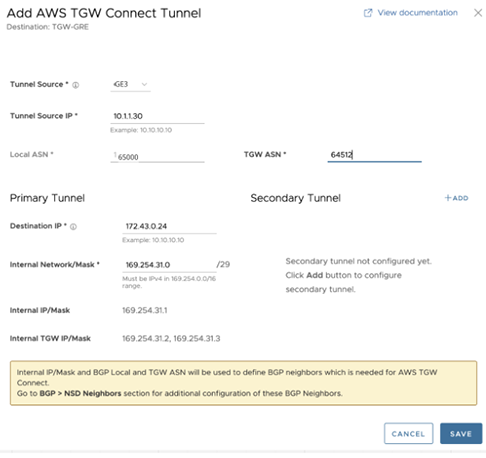
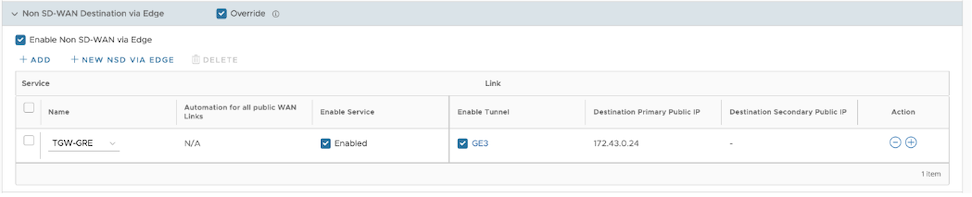
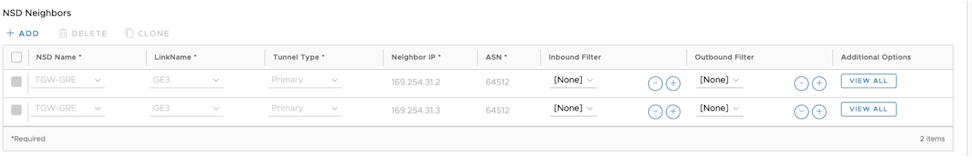
VeloCloud Edges typically deploy in a Transit VPC on Amazon Web Services (AWS). AWS introduced the support for AWS TGW (Transit Gateway) Connect Service for SD-WAN appliances to connect to the Transit Gateway. VeloCloud Edge now has a feature (BGP over GRE support on LAN), which enables support on the VeloCloud Edge to use the AWS TGW Connect Service for connectivity to the AWS Transit Gateway.
For the AWS TGW Connect Service, the Edge provisioned in the Transit VPC needs to use the LAN (routed, non-WAN) interface to set up the GRE tunnel.
Amazon Web Services (AWS) Configuration Procedure
VeloCloud Edge Cloud Orchestrator Configuration Procedure
Obtain Amazon Web Services Configuration Details
- From Amazon's Web Services, create VPC and VPN Connections. Refer to the instructions in Amazon's documentation.
- Make note of the Gateways associated with the enterprise account in the Orchestrator that might be needed to create a virtual private gateway in the Amazon Web Services.
- Make a note of the Public IP, Inside IP and PSK details associated with the Virtual Private Gateway. You need to enter this information in the Orchestrator when you create a Non SD-WAN Destination.
Configuring a Non SD-WAN Destination
After you obtain Public IP, Inside IP, and PSK information from the Amazon Web Services (AWS) website, you can configure a Non SD-WAN Destination.
AWS Cloud WAN CNE Connect using Tunnel-less BGP
AWS has announced Tunnel-less Connect on Cloud WAN. This document describes AWS components and how to configure AWS and VeloCloud SD-WAN.
AWS Cloud WAN CNE Connect uses a Tunnel-less BGP capability provides a simpler way to build a global SD-WAN network using AWS backbone as a middle-mile transport network. With this capability, VeloCloud SD-WAN appliances can natively peer with an AWS Cloud WAN using Border Gateway Protocol (BGP) without requiring tunneling protocols like IPSec or GRE. This simplifies the integration an SD-WAN into an AWS cloud and allows the ability to leverage the high bandwidth AWS backbone for branch-to-branch connectivity across different geographic regions. This feature also supports in-built network segmentation, and enables the building of a secure SD-WAN at a global scale.
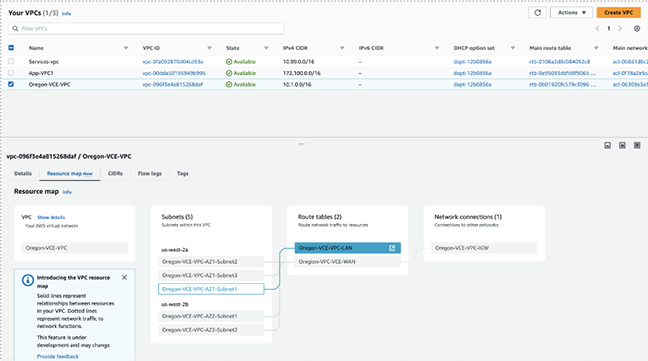
Typically, VeloCloud SD-WAN Virtual Edges (vEdges) deploy into an AWS Transport VPC. This Transport VPC may then peer with other VPCs, TGWs, or in this case, a CNE (Cloud Network Edge) in the Cloud WAN backbone to achieve connectivity with resources in AWS.
For Cloud WAN CNE Connect, the vEdges provisioned in the Transport VPC uses the LAN-facing routed and non-WAN interface to establish native L3 unencapsulated BGP peering with the CNE.
AWS Components
- Cloud WAN Core Network
- Policy definition
- Core Network Edge (CNE)
- Transport VPC
- VPC Attachment
- Connect Attachment
This assumes that you have other resources in other AWS VPCs using VPC peering to CNEs in the Core Network. If not, you must define the Core Network and CNEs and create the attachments to your existing workload VPCs.
AWS Configuration
- Use the following Arista online documentation to create vEdges in an AWS VPC:
- Virtual Edge Deployment Guide
- VeloCloud SD-WAN AWS CloudFormation Template- Green Field
- VeloCloud SD-WAN AWS CloudFormation Template- Brown Field
- On the AWS console, use the AWS Network Manager to create a Global Network, if one does not already exist in the AWS deployment.
Figure 19. Create Global Network 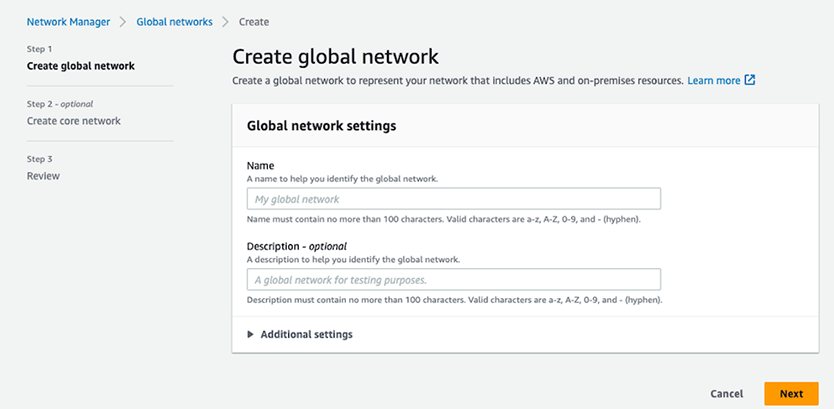
- Create a Policy version.
- A Policy version defines and configures the key details of the solution:
Figure 20. Create Policy Version 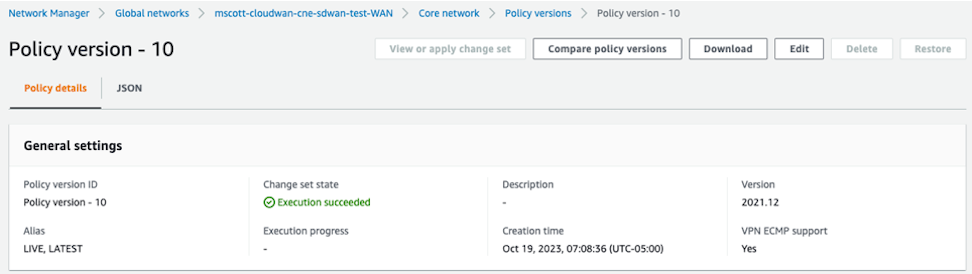
- Enter the BGP ASN ranges used by the CNEs:
Figure 21. BGP ASN Ranges 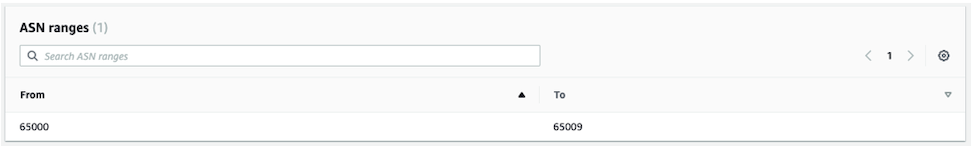
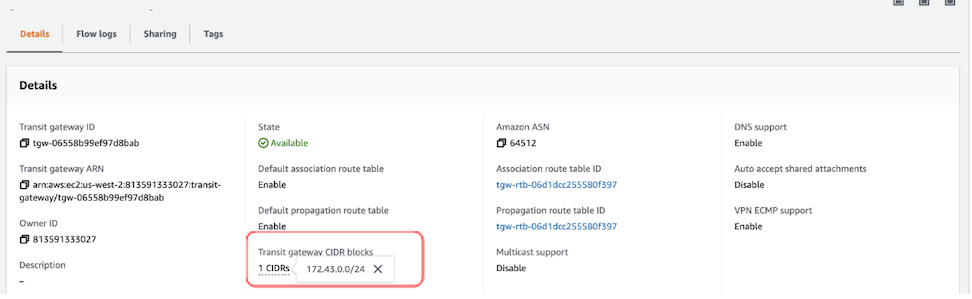
- In the global Inside CIDR blocks field, define the respective CDR blocks for the CNEs.
Figure 22. Adding CIDR Blocks 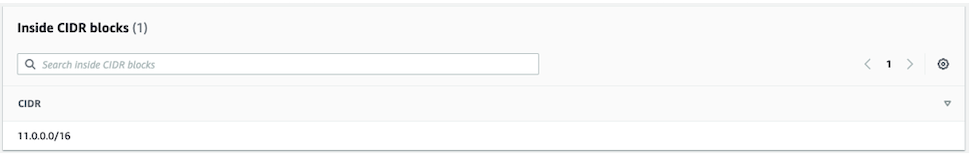
- Search for Edge locations and review the list of specific AWS AZ to place the CNE.
Figure 23. Search for Edge Locations 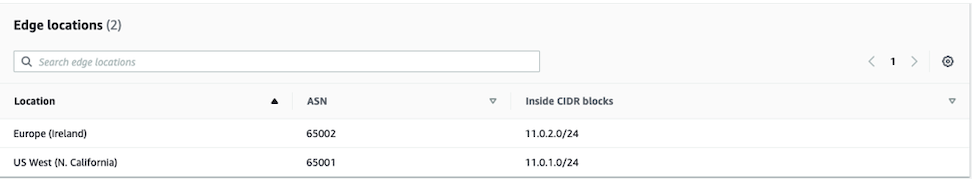 Note: The ASN and Inside CIDR Blocks for each Edge location uses the defined range defined for the Global Network.
Note: The ASN and Inside CIDR Blocks for each Edge location uses the defined range defined for the Global Network. - Search for Segments. Define logical segments using tags. Tag VPCs and Subnets to define segment membership. In this example, the format uses Key=Segment and Value=SDWAN.
Figure 24. Defining Segments 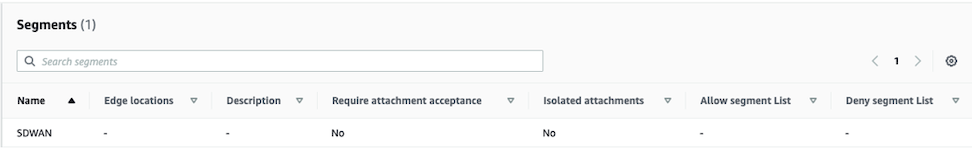 Note: Use the value defined in the policy.
Note: Use the value defined in the policy. - VCP and Connect Attachments specify the Segments used as well as the criteria for the Segments. In the example, a tag-value condition defines membership in the SD-WAN segment. The key-value pair uses the Condition values and must be present in VPCs and subnets in order to become Segment members.
Figure 25. Configuring Attachment Policies 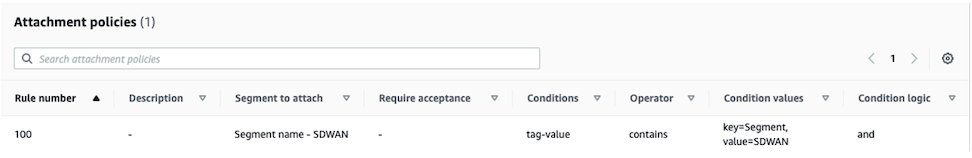
- A Policy version defines and configures the key details of the solution:
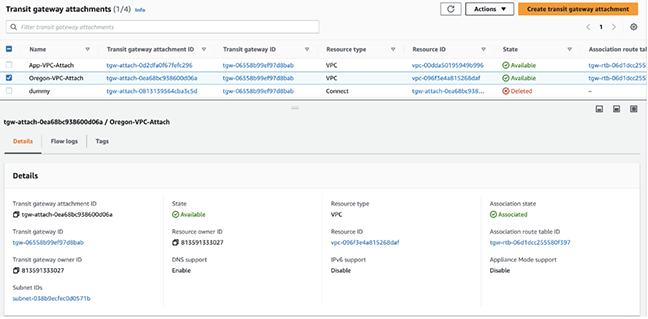
- Use one of the following types of attachments:
- VPC Attachments
- Connect Attachments
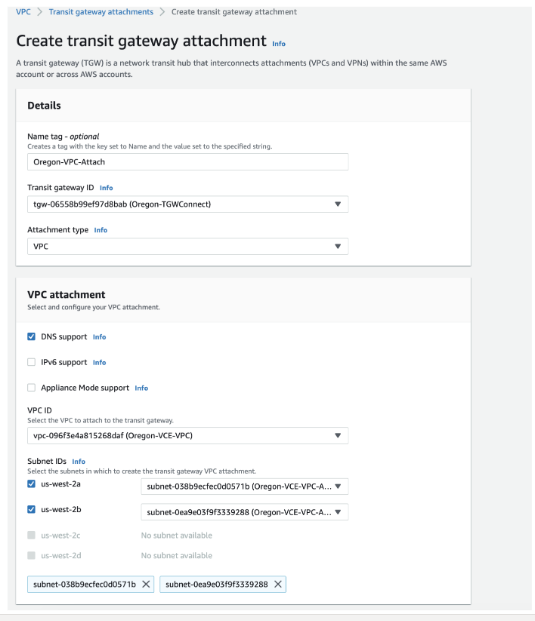
- VPC Attachments- Each SD-WAN Transport VPC has a VPC attachment to the CNE. Specify at least one subnet within the VPC when creating the VPC attachment. In the example, the CNE with the location, us-west-1 AZ peers with the SD-WAN Transport VPC private VLAN subnet. Also define a key-value pair for the Segment membership.
Figure 26. Creating an Attachment 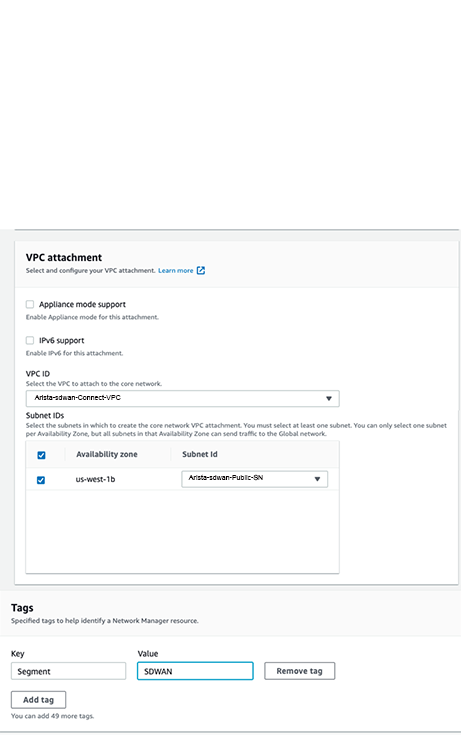
If configured correctly, the Attachment displays the configuration details including SDWAN as the Segment and the Attachment policy rule number.
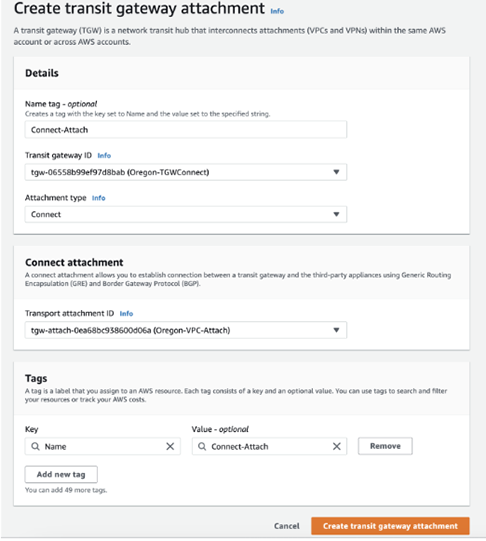
- Configure the Connect Attachment for Tunnel-less (No encapsulation) and specify an existing VPC Attachment as the Transport Attachment ID.
Figure 27. Creating a Connect Attachment 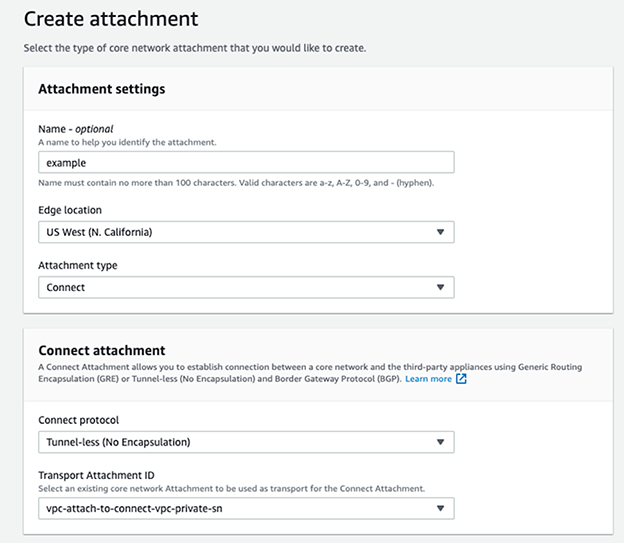
Figure 28. Tags 
If configured correctly, the Attachment displays membership in the SDWAN Segment. It also displays the Attachment policy rule number and NO-ENCAP as the Connect protocol.
Figure 29. Displaying the Configured Policy 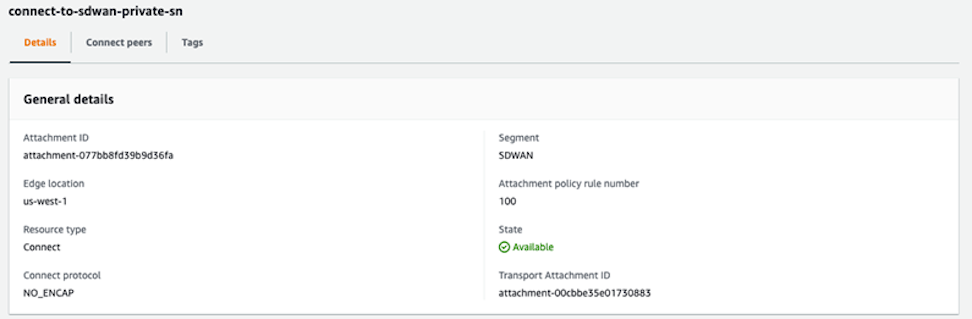
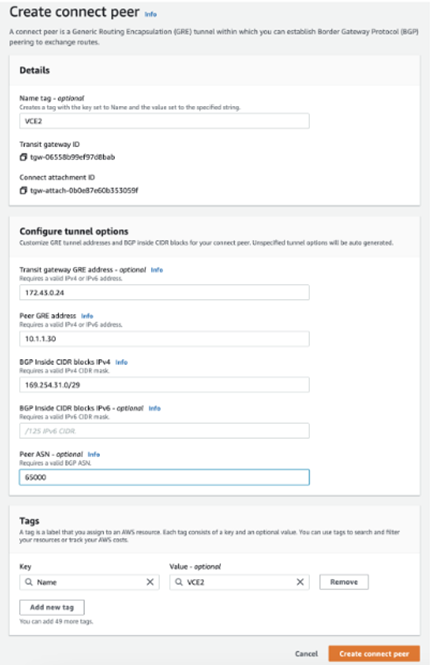
- Create Connect Peers in the Connect Attachment and define the SD-WAN vEdge BGP peerings in terms of the ASN and peer IP address.
Figure 30. Creating Connect Peers 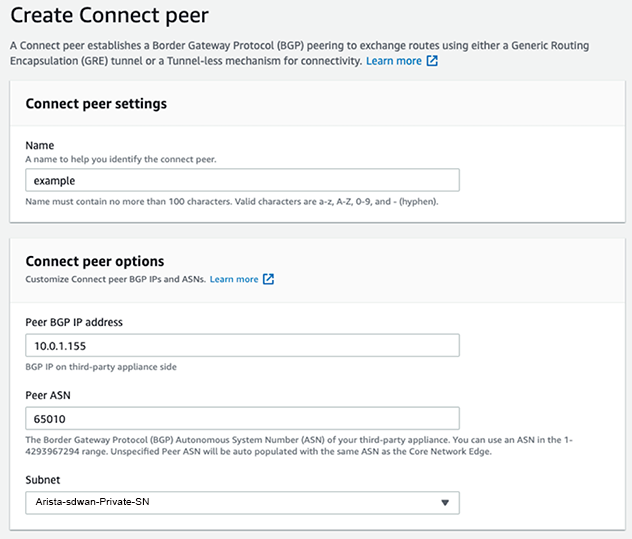 Once configured, the AWS console provides two Core Network BGP peer IP addresses to use on the SD-WAN BGP neighborship and selects them randomly from the Inside CIDR range configuration.
Once configured, the AWS console provides two Core Network BGP peer IP addresses to use on the SD-WAN BGP neighborship and selects them randomly from the Inside CIDR range configuration.Figure 30. Connect Peer Settings 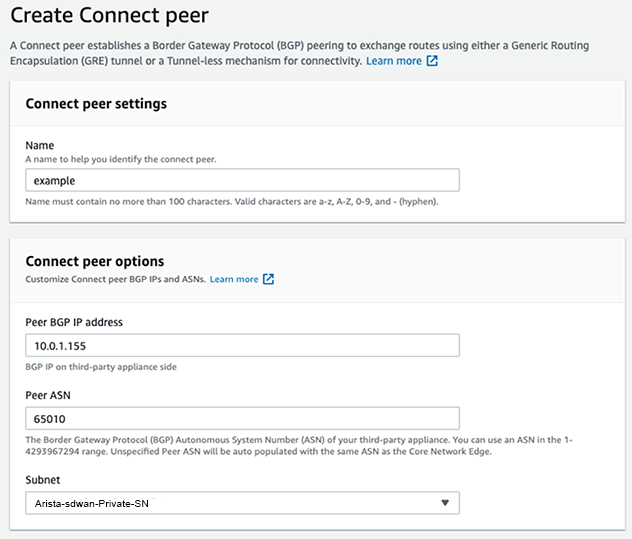
Configuring VeloCloud SD-WAN
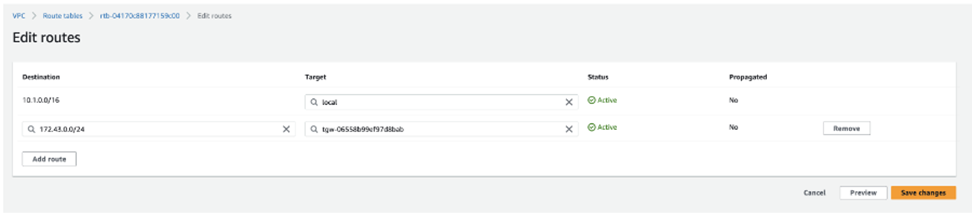
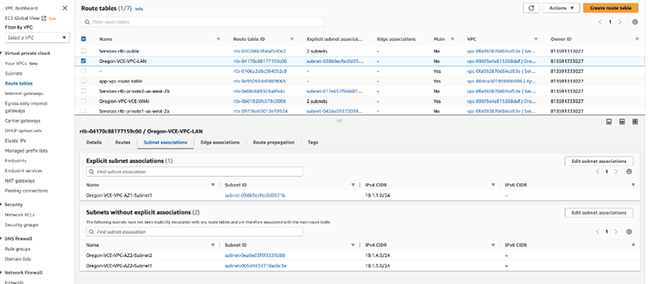
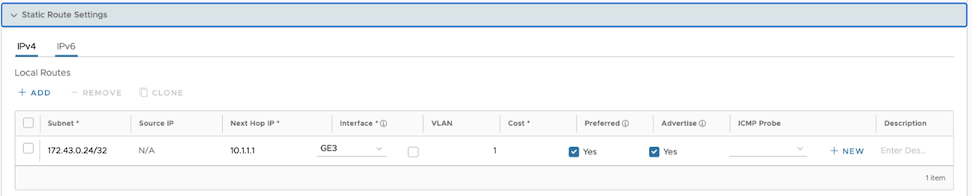
- Configure Static Route Settings.
Figure 32. Configuring Static Routes 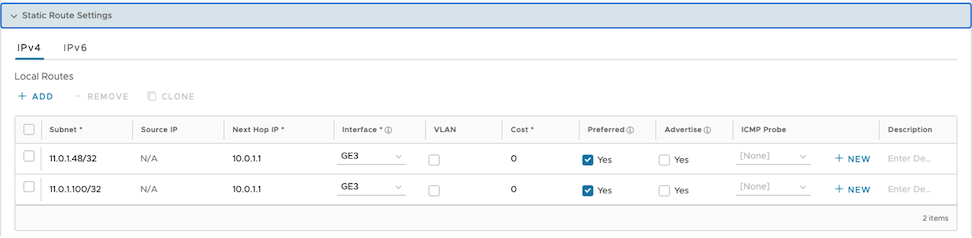
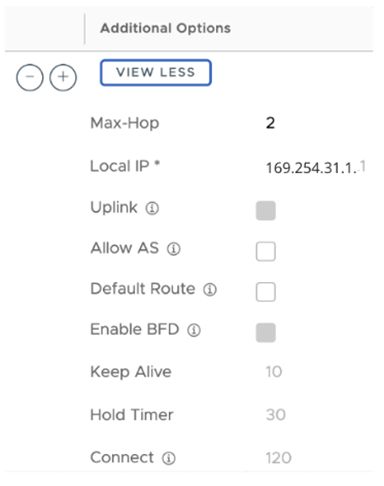
- When creating the BGP Neighbors, set the Max-Hop to two or more in the Additional Options column.
Figure 33. Configuring Additional Hops 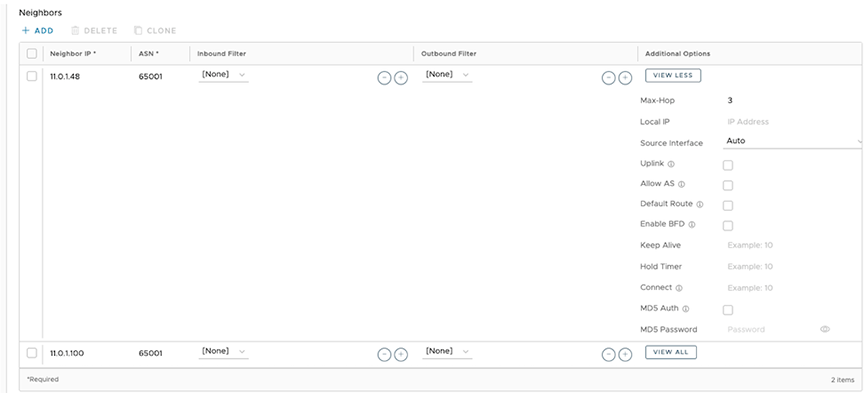
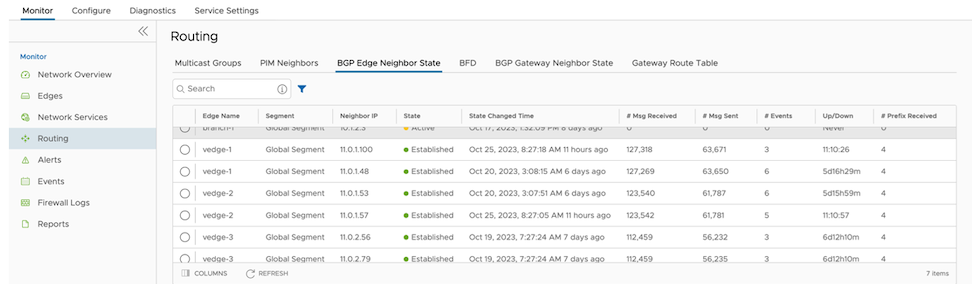
- Use to verify that the BGP peer relationship has established with the configured Neighbor IP addresses.
Figure 34. Configuring Routing