VeloCloud SD-WAN in Azure Virtual WAN Hub Deployment
The VeloCloud SD-WAN in Azure Virtual WAN (vWAN) Hub deployment describes the configurations that are required to manually deploy a Virtual Edge as a Network Virtual Appliance (NVA) in Azure vWAN Hub network.
About VeloCloud SD-WAN in Azure Virtual WAN Hub Deployment
The VeloCloud SD-WAN in Azure Virtual WAN (vWAN) Hub deployment describes the configurations that are required to manually deploy a Virtual Edge as a Network Virtual Appliance (NVA) in Azure vWAN Hub network.
Overview
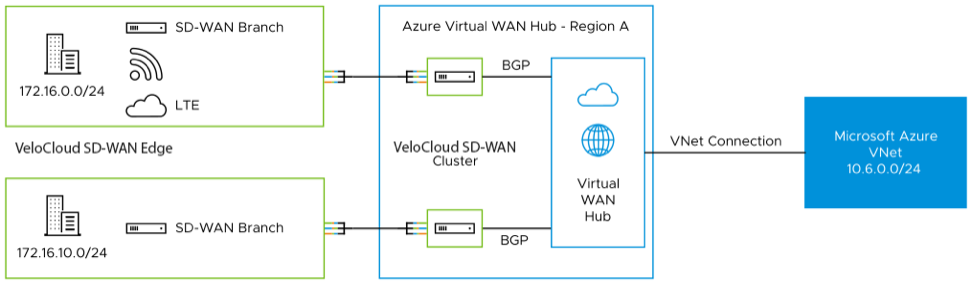
During cloud migration, there were lot of challenges on how to connect remote locations to Azure VNets in a simple, optimized, and secure way across myriad connectivity options. VeloCloud SD-WAN addresses these problems by leveraging Dynamic Multipath Optimization ™ (DMPO) technologies and distributed cloud gateway coverage across the globe. VeloCloud SD-WAN transforms the unpredictable broadband transport to Enterprise-class quality connections, ensuring the application performance from remote locations to Azure Cloud.
To meet different deployment scenarios for customers who deploy Azure Virtual WAN, VeloCloud SD-WAN have been progressively adding more capabilities to the solution. With this new integration, customers can now deploy VeloCloud Edges directly inside Azure Virtual WAN hubs manually, resulting in an offering that natively integrates Azure Virtual WAN’s customizable routing intelligence with VeloCloud SD-WAN’s optimized last-mile connectivity.
Deploy VeloCloud SD-WAN Edge in Azure Virtual WAN Hub
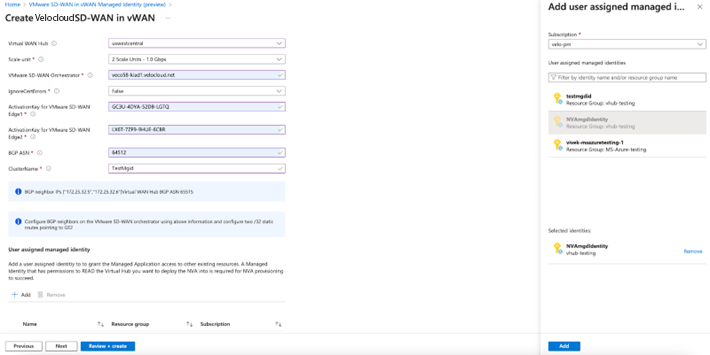
To deploy VeloCloud Edges in a Virtual Hub manually, you must have already created a Resource Group, virtual WAN (vWAN), and virtual Hub (vHUB) on the Azure side.
- Obtain Enterprise account access to VeloCloud Orchestrator.
- Obtain access to the Microsoft Azure portal with the appropriate IAM roles.
- Software image requirements for this deployment are as follows:
- VeloCloud Orchestrator: 4.5.0 and above.
- VeloCloud Gateway: 4.5.0 and above.
- VeloCloud Edges: 4.2.1 and above.
- Create an Azure Managed Identity. For steps, see Create Managed Identity.
To deploy VeloCloud SD-WAN Edge in Azure Virtual WAN Hub, perform the following steps:
Create Managed Identity
This section discusses the steps to create an Azure Managed Identity.
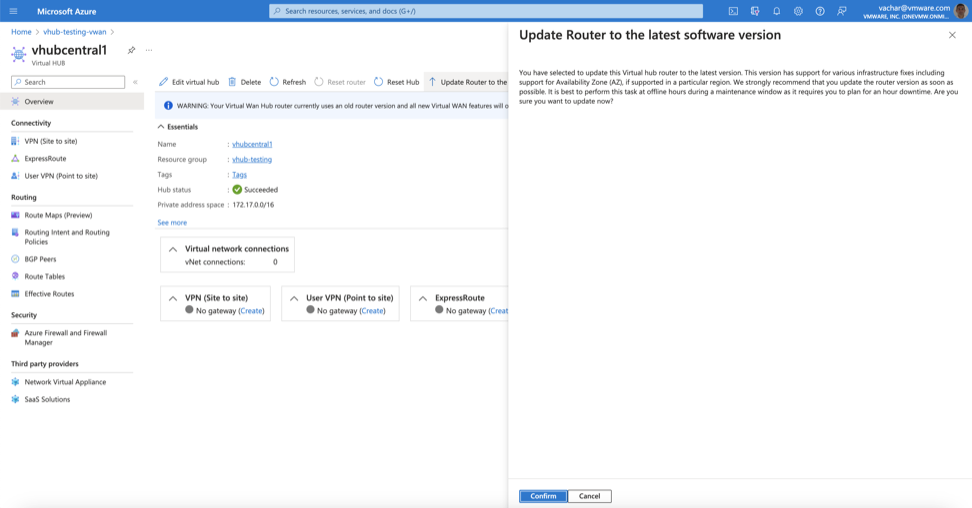
Hub Upgrade Instructions for VeloCloud Edge Deployed as Azure vWAN NVA
This document is intended for customers who use VeloCloud Edges in Azure and deploy them as Network Virtual Appliances (NVAs) in the Azure Virtual WAN (vWAN) Hub.
For additional information, see Virtual WAN FAQ.
Upgrade Instructions



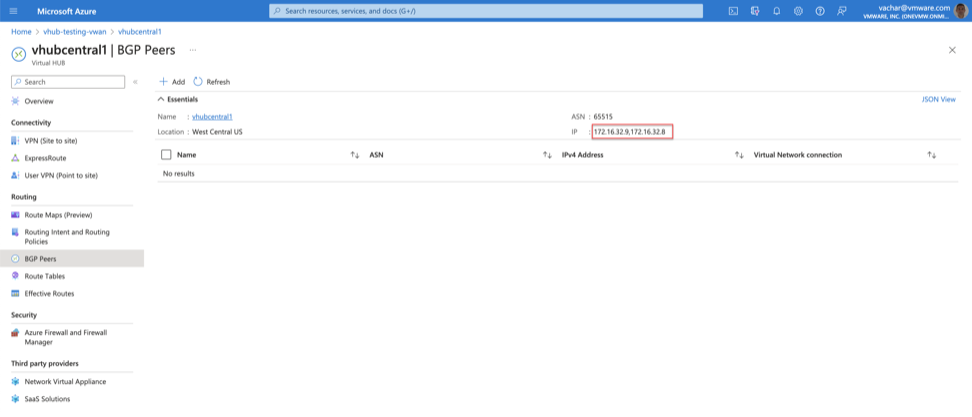
Copy the IP Addresses. For example, in this case the IP addresses are 172.16.32.8 and 172.16.32.9. These are the IP addresses on the Virtual Hub that the BGP Peers ( VeloCloud SD-WAN NVA) will need to be configured.
On the Orchestrator, the Virtual Edge BGP connections to the Virtual Hub will be displayed as Down, either in Connect or Active state.
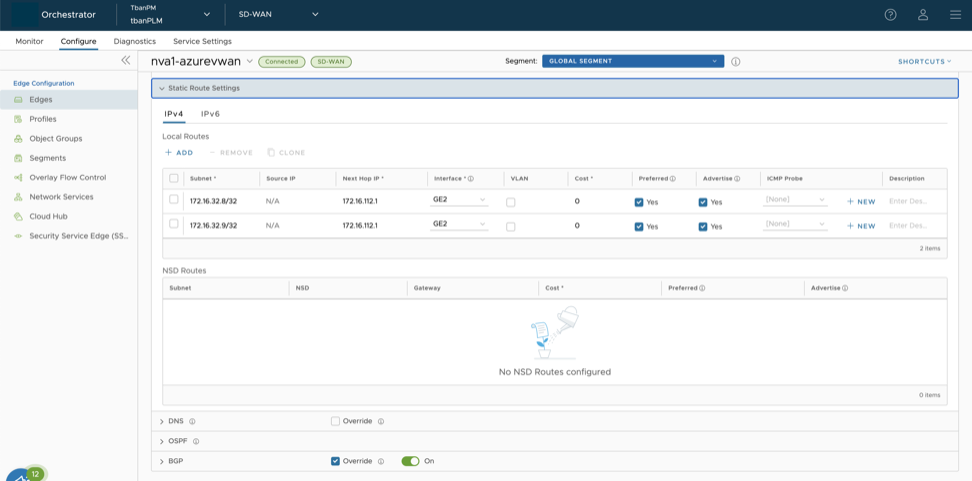
Before configuring BGP neighbors on the Virtual Edge, static routes must be configured to allow the Virtual Edges to connect to the Azure Virtual WAN Hub.
Static Routes Configuration
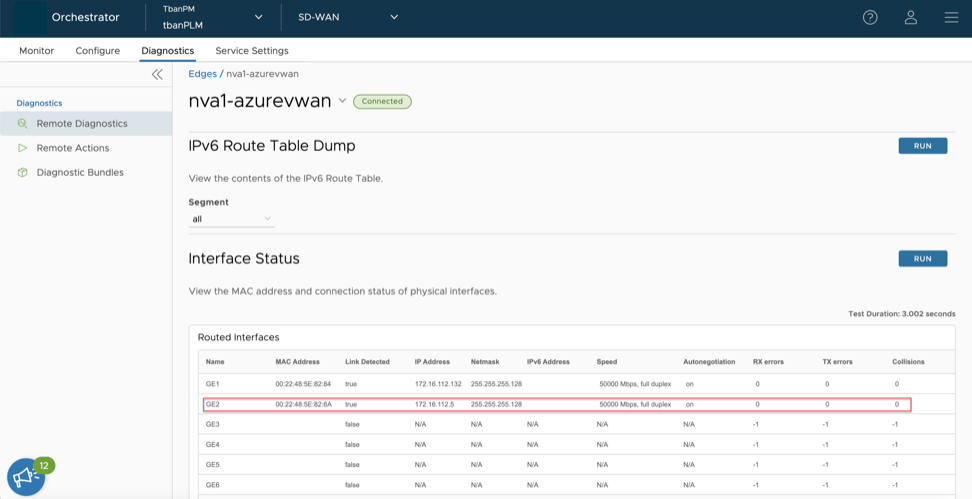
To configure static routes, add sufficient /32 static routes to ensure that there is a unique route pointing to the respective GE2 interface on each Virtual Edge. To add a static route, the Orchestrator requires a next-hop IP address. The next hop IP address can be obtained by running the Remote Diagnostic “Interface Status” test in the Remote Diagnostics UI page of the Orchestrator. Select the first IP address of the subnet assigned to GE2 and configure it as the next hop.
The following image shows an IP address assigned to GE2 as 172.16.112.5/25, with the first IP address of this subnet being 172.16.112.1. This IP address is used to configure the static route on the Orchestrator.
BGP Neighbor Configuration