Introduction

Endpoint Identity and Microperimeter Tags
The first step in planning a microsegmentation strategy involves binding endpoints, workloads, and networks to specific microperimeter tags. MSS automates the management of microperimeters by connecting to external sources and using user-defined tags to assign endpoints into groups of endpoints requiring the same policy. MSS connects to external sources like NAC systems, CMDBs, and virtualization infrastructure management solutions like VMware vSphere.
“Zero Trust” Policy Planning with Traffic Map
Zero trust architecture principles require that all traffic on the network must be explicitly allowed by security policies. To create zero trust policies, it is vital to have complete visibility into existing traffic flows on the network. This complete visibility ensures that policies protect the right resources while at the same time not impeding legitimate business-justified flows. MSS maps all the communications within and across different parts of the network and provides a set of recommended policies to only permit trusted communications based on the observed traffic map.
Microperimeter Enforcement in the Network or Redirect to Firewall
MSS then distributes the zero trust policies to EOS-powered network switches. As traffic ingresses the switch, it can perform wire-speed distributed enforcement itself or redirect the traffic to any L3 firewall for stateful L4-7 inspection.
Importantly, Arista’s switch-based enforcement overcomes the challenges associated with traditional ACL-based segmentation, such as TCAM exhaustion, by leveraging an advanced labeling engine that optimizes hardware utilization and maximizes scalability. Furthermore, because hardware labels are internal to a switch and are not shared across the network infrastructure, MSS can be seamlessly inserted into any multi-vendor network. This approach also avoids any proprietary protocols that force organizations into single-vendor networks.
MSS enforcement occurs at the network's edge, on the TOR switch, where traffic ingresses the MSS-enabled network.
Continuous Traffic Monitoring and Visibility of Policy Violations
After deploying the zero trust policies, MSS can monitor for policy violations, and report on the specific flows dropped in the network. This provides vital intelligence to the administrator to update the zero trust policies when they are valid. Yet, denying new services as well as monitor specific endpoints that are attempting to violate traffic rules.
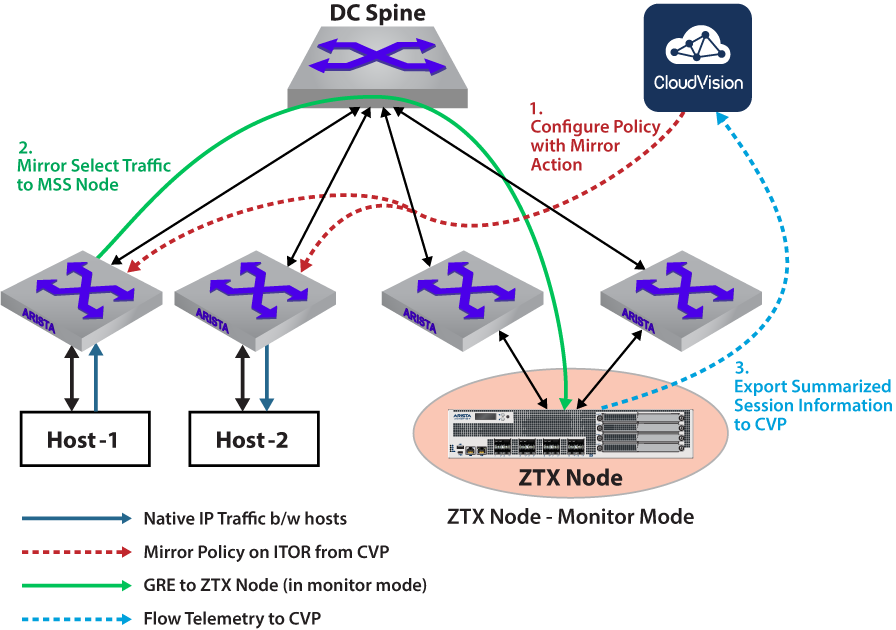
ZTX Monitor Node Role
The primary purpose of a Multi-domain Segmentation Services (MSS) Monitor Node is to provide visibility into app-to-app traffic in the network, and to develop non-intrusive MSS policies that are aligned with applications requirements. It is a baseline capability for any micro or macro segmentation solution and is a practical way to build and deploy policies.
Configuring policies in terms of groups of end-points or prefixes is essential to simplify policy management and secure Data Center and Campus environments. The ZTX monitor node provides visibility into existing traffic needed to build such policies.
Refer to Deploying the ZTX Monitor Node section for configuration information.
Definitions and Acronyms
- MSS - Multi-domain Segmentation Services
- CVP - CloudVision Portal
- CVaaS - CloudVision-as-a-Service
- TOR - Top of Rack
- STOR - Service Top of Rack
- ITOR - Ingress Top of Rack
- GRE - Generic Routing Encapsulation
- Tag - User-defined string of a property used in an end-point management system.
- Group or Field Set - Collection of end-points with the same tag or tags.
- Label - Hardware representation of a collection of tags internal to each switch.
- Security Domain - A security domain, a construct within MSS, manages the scope of a policy. For example, a security domain can be used for all devices within a geo-location, pod, or building.