Deployment Strategy
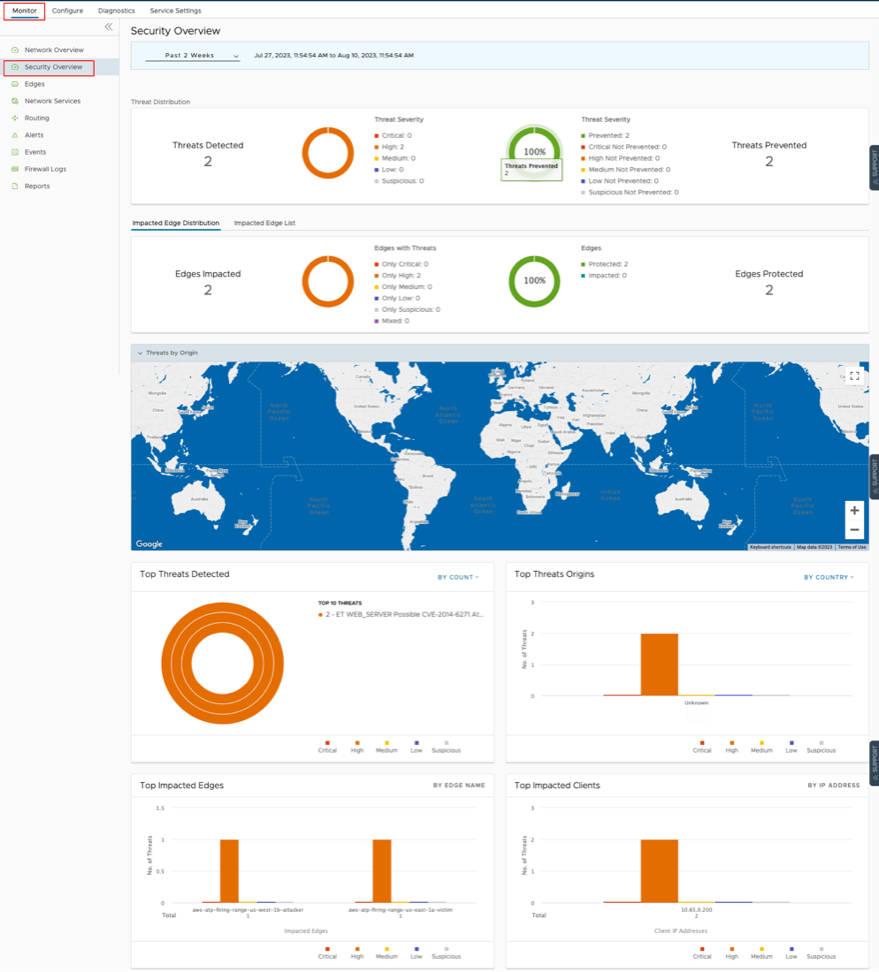
The following is a simple guide on what tools are available in the Orchestrator, how to use the tools, and how to activate EFS to start inspecting traffic.
False Positive Workarounds
A False Positive, with regards to IDS/IPS, is a situation where legitimate traffic is being blocked/flagged by the IDS/IPS.
If you believe that the IDS/IPS might be incorrectly blocking legitimate traffic, follow the steps outlined below, starting from granular approaches and moving to more broad solutions, to resolve the problem.
In all cases, submit a support ticket outlining the type of traffic being dropped and the Signature ID that the traffic is hitting. To collect the appropriate data to submit in your support ticket, refer to the Firewall logs or your logging infrastructure that is collecting your syslogs.
If you use the Orchestrator-hosted logging, navigate to and find the suspected traffic. From these logs, gather the Source IP, Destination IP, Application, and Signature ID and add that to your support ticket.
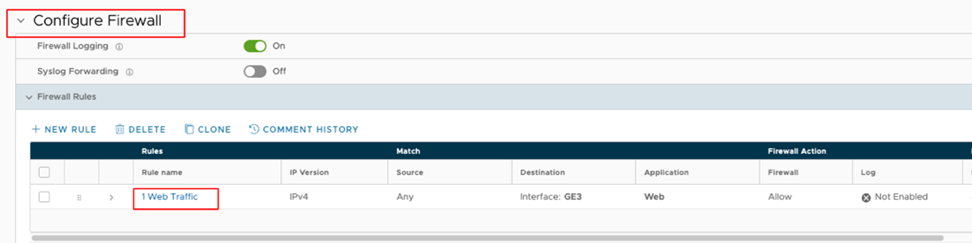
- Method 1: Create a More Targeted Firewall Rule Above the Offending Firewall Rule:The most specific solution is to create a more targeted firewall rule above the offending firewall rule by performing the following steps:
- Navigate to and filter the log entries to match the incorrectly blocked traffic. Note the Source/Destination IP/Port, Protocol, and Application. You will use that information to create a new firewall rule. Also note the Rule and Edge Name.
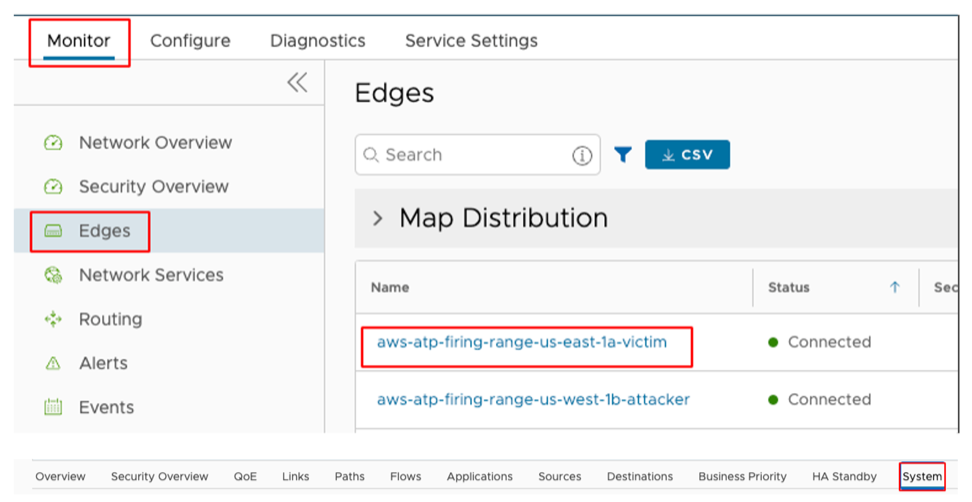
- Under the Configure tab, navigate to the Edges view and select the affected Edge.
- Navigate to the Firewall tab and expand the Firewall Rules area.
- Select + New Rule and create a more specific rule based on the data you collected from the logs. Make sure to not activate IDS/IPS and then select Create.
- Select the firewall rule you just created and drag it to right above the offending firewall rule.
- Select Save Changes.
- Verify the change is working as intended and the traffic is not being blocked.
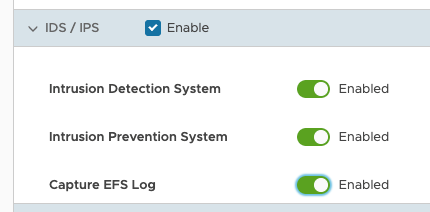
- Method 2: Deactivate EFS at the Rule level: To further limit the scope of change you can select the offending rule and deactivate EFS at the firewall rule level. To deactivate EFS at the Rule level:
- Navigate to and select the appropriate log entry. From the Rule and Edge columns, note the Rule name and the Edge name.
- Under the Configure tab, navigate to the Edges view and select the affected Edge.
- Navigate to the Firewall tab and expand the Firewall Rules area.
- Find the offending Rule and select it. If the Rule is under the Rules From Profile area then you will need to navigate to the Profile and edit the rule from there. The steps to edit the rule at the Profile level are same as editing the rule at the Edge level.
- After selecting the Rule, scroll down to the IDS/IPS section. From the IDS/IPS section you can deactivate both IDS/IPS or you can just deactivate IPS.
- To deactivate both IPS and IDS, unselect the Enable check box.
- To deactivate only the IPS, toggle the Enable button next to Intrusion Prevention System.
- Verify the change is working as intended and the traffic is not being blocked.
- Method 3: Deactivate EFS at the Edge level: If the issue is isolated at a single branch, then to limit the scope of changes, it might be best to deactivate EFS on the affected Edge. To deactivate EFS at the Edge level:
- Navigate to and select the appropriate Edge to deactivate EFS.
- Navigate to the Firewall tab.
- In the Enhanced Firewall Services area, select the Override check box and then toggle the Enhanced Firewall Services button to Off.
- Verify the change is working as intended and the traffic is not being blocked.
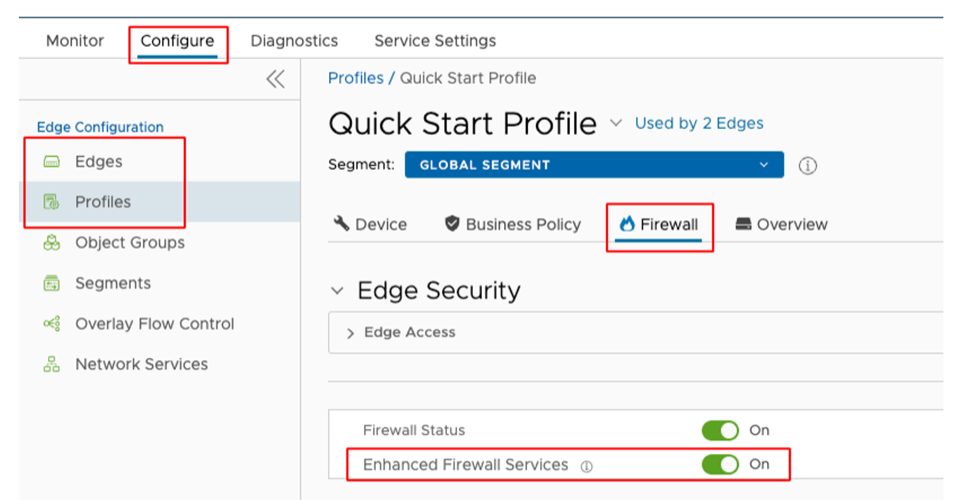
- Method 4: Deactivate EFS at the Profile level: If the issue is seen across several branches, then it might be prudent to deactivate EFS at the Profile level. To deactivate EFS at the Profile level:
- Navigate to and select the Profile that covers the desired Edges.
- From the Profile view, select the Firewall tab.
- Toggle the Enhanced Firewall Services button to Off.
- Verify the change is working as intended and the traffic is not being blocked.