Configuration for Route-Based NSD Via Edge
Route-Based NSD Via Edge to the VMware Cloud AWS Gateway Overview
The example topology illustrates the Integration of Arista VeloCloud SD-WAN and VMware Cloud on AWS, which uses IPSec connectivity between the VeloCloud Edge and the VMware Cloud Gateway.

This section provides step-by-step procedures on how to achieve connectivity between an SDWAN Edge and a VMware Cloud Gateway.
- Log into the VMware Cloud Console based on the URL for your SDDC organization (The VMware Cloud Services Login Page). On the Cloud Services Platform, select VMware Cloud on AWS.
- Find Public IP used for VPN connectivity by selecting the Networking and Security tab. The VPN Public IP displays below the Overview pane.
Figure 2. Overview Pane 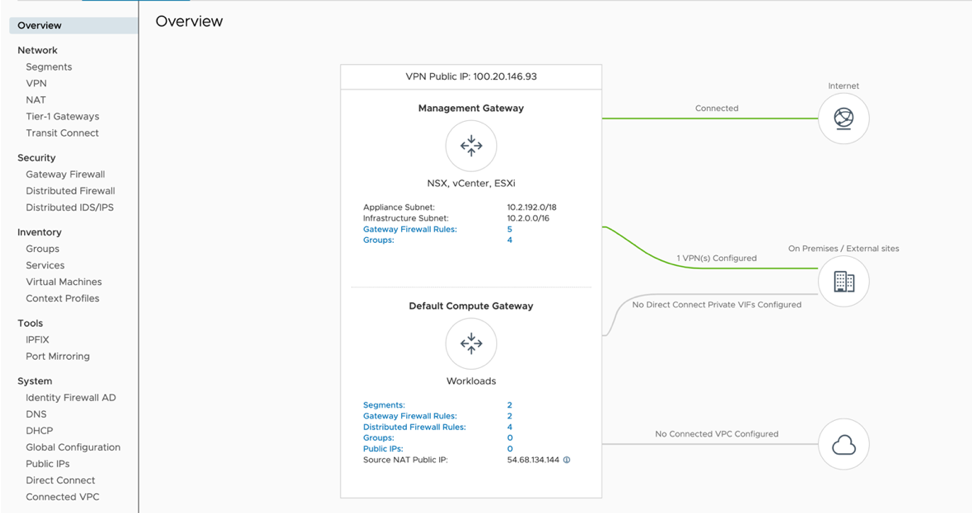
- Determine the networks/subnets for traffic encryption selection (interesting traffic) and note them down. These should originate from Segments in Networking/Security in the VMware Cloud. (Locate this by selecting Segments, under Network.
- Log into the SD-WAN Orchestrator and verify that the Edges are present with a green status icon displayed next to them.
Figure 3. Network Overview 
- Go to the Configure tab and select Network Services, and then under Non SD-WAN Destination via Edge, select the New button.
Figure 4. Network Services 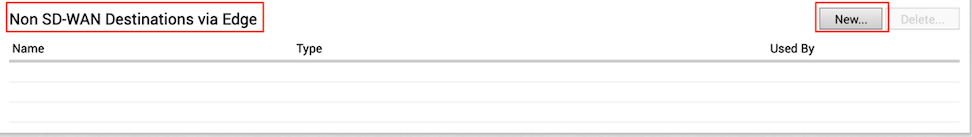
- Provide a name for the Non SD-WAN Destination via Edge, select the type, in this case, Generic IKEv2 Router(Route Based VPN), and select Next
Figure 5. Service name and Type 
- Select the Advanced button and provide below details.
- Enter the Public IP of the VMC obtained in Step 2.
- Ensure encryption set to AES 128.
- Change DH group to 2.
- Enable PFS to 2.
- Auth Algorithm set to SHA 1.
- Subnets will be learned via BGP, (if BGP is not configured then add site subnets which captured at step 3, e.g. static route).
- Select Save Changes.
Figure 6. Non SD-WAN Destinations via Edge 
- On the left pane, select Configure > Edges .
Figure 7. Monitor Edges 
- Go to the device setting page of Edge in which NSD will be associated.
- Under the device setting of Edge complete the following steps.
- Under Cloud VPN and Branch to Non SD-WAN Destination via Edge, select the check box next to Enable.
- In the drop-down menu, select the NSD via Edge.
Figure 8. NSD via Edge 
- Select the Add button and update the following fields below (see image below).
- Select the Edge WAN link from where NSD tunnel to form.
- Local ID type – IP address.
- Local id will be public IP of WAN link.
- Enter the PSK.
- Destination primary Public IP – VMC Gateway Public IP.
Figure 9. Add Tunnel 
- Activate BGP settings for an Edge, as shown in the image below.
Figure 10. BGP Settings 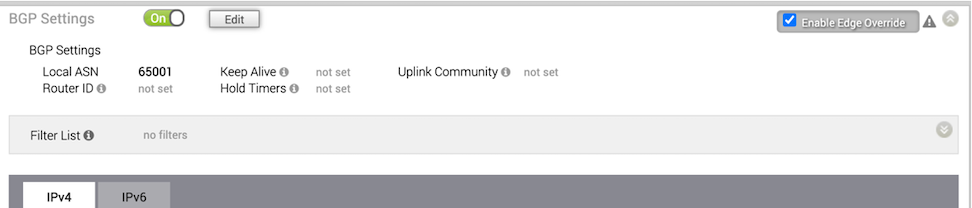
- Select the Edit button and update BGP parameters for NSD neighbor.
- Select configured NSD name.
- Edge WAN link where NSD is associated.
- Configure Local ASN 65001.
- Neighbor IP – 169.254.32.2.
- Peer ASN – 65000 (VMC default ASN is 65000).
- Local IP – 169.254.32.1 NOTE: It is recommended to use a /30 CIDR from 169.254.0.0/16 subnet excluding following VMC reserved addresses- 169.254.0.0-169.254.31.255, 169.254.101.0-169.254.101.3
Figure 11. BGP Editor 
- The tunnel should be ready on the SD-WAN Orchestrator with BGP over IPSec.
- Log into the VMware Cloud Console.
- Navigate to Networking and Security and select the VPN tab. In the VPN area, select Route Based VPN, and select Add VPN.
Figure 12. VMC-SD-WAN 
- Provide a name for the Route Based VPN and configure the following.
- Choose a name. (Choose a name that starts with To_SDWAN_EDGE, so the VPN can be easily identified during troubleshooting and future support).
- Select the Public IP.
- Enter the remote Public IP. (Edge WAN link Public IP).
- Enter the remote Private IP – it should same as section 11c.
- Specify the BGP local ip.
- Specify the BGP remote IP.
- Under Tunnel Encryption, select AES 128.
- Under Tunnel Digest Algorithm, select SHA1.
- Make sure Perfect Forward Secrecy is set to Enabled.
- Enter the PSK, to match Step 12d.
- Under IKE Encryption, select AES 128.
- Under IKE Digest Algorithm, select SHA 1.
- Under IKE Type, select IKEv2.
- Under Diffie Hellman, select Group 2.
- Select Save.
Figure 13. Network and Security 
- Once the configuration is complete, the tunnel is automatically activated and will proceed to negotiate the IKE Phase 1 and Phase 2 parameters with the peer, which is the VeloCloud EDGE.
Figure 14. Route Based VPN 
- Once the tunnel displays (green), verify that the NSD via Edge tunnel/BGP status in the SD-WAN Orchestrator (go to Monitor > Network Services ).
Figure 15. Network Services 
Figure 16. BGP Edge Neighbor State 
- Start a ping from a client connected at each end towards the opposite client, and verify ping reachability. The tunnel configuration has been completed and verified.
Figure 17. Ping Verification 
Figure 18. Verified Status 
