Configuration for Route-Based NSD Via Gateway
Route-Based NSD Via Gateway to VMware Cloud AWS Gateway Overview
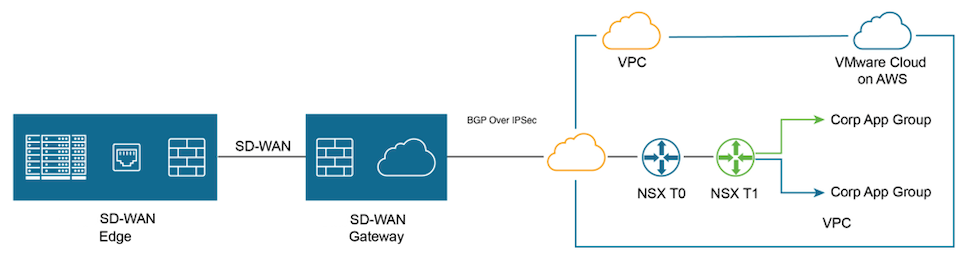
The figure below illustrates the Integration of Arista VeloCloud SD-WAN and VMware Cloud on AWS, which uses IPsec connectivity between the Arista VeloCloud Gateway and the VMware Cloud Gateway.
Perform the following steps to achieve connectivity between an SD-WAN Gateway and a VMware Cloud Gateway.
- Log into the VMware Cloud Console based on the URL for your SDDC organization. On the Cloud Services Platform, select VMware Cloud on AWS.
- Find Public IP used for VPN connectivity by selecting the Networking and Security tab. The VPN Public IP displays below the Overview pane.
Figure 2. Overview Pane 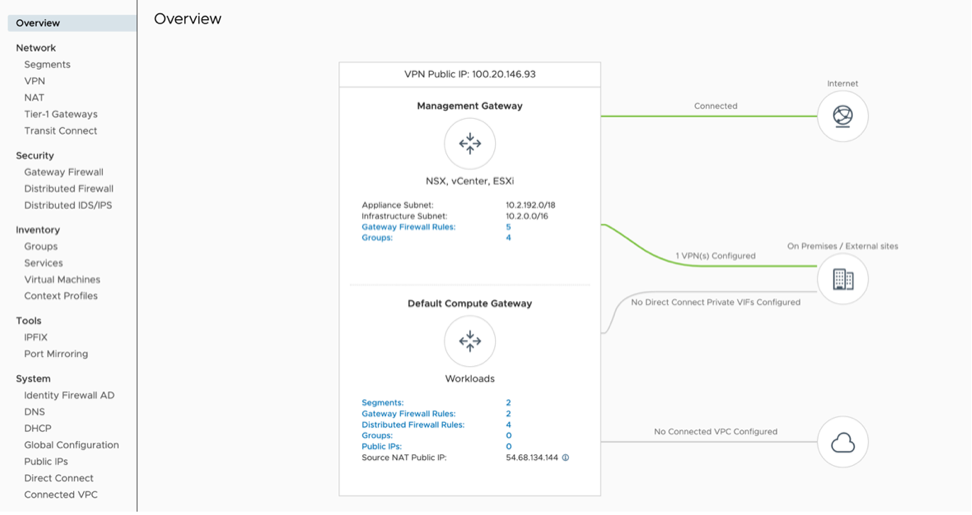
- Determine the networks/subnets for traffic encryption selection, interesting traffic, and write them down. These should originate from Segments in Networking/Security in the VMware Cloud. Locate this by selecting Segments, under Network.)
- Log into the SD-WAN Orchestrator and verify that the Edges are displayed (a green status icon will be displayed next to them).
Figure 3. Network Overview 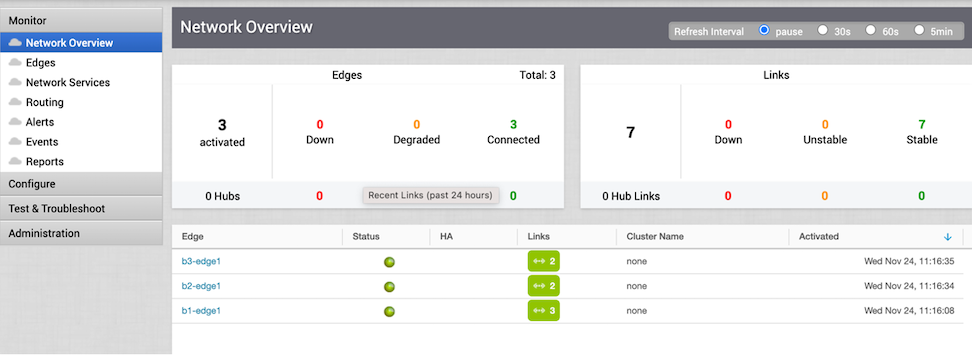
- Go to the Configure tab and select Network Services. Under Non SD-WAN Destination via Gateway, select the New button.
Figure 4. Non SD-WAN Destinations via Gateway 
- Provide a name for the Non SD-WAN Destination via Gateway. Select the type, in this case, Generic IKEv2 Router (Route Based VPN), and Enter the Public IP from the VMC obtained in Step 2, and select Next.
Figure 5. New Non SD-WAN Destination via Gateway 
- Select Advanced and complete the following steps:
- Change to the desired PSK.
- Ensure encryption set to AES 128.
- Change DH group to 2.
- Enable PFS to 2.
- Auth Algorithm set to SHA 1.
- Deactivate site subnet, since subnets are learned via BGP. If BGP is not configured then add site subnets captured at step 3, like static route.
- Select the check box next to Enable Tunnels.
- Select Save Changes.
Figure 6. VMC on AWS 
- Select View IKE/IPSec Template and copy the information into a text file, and then close the window.
Figure 7. IKE IPSec Configuration 
- On the left pane, select Configure > Profiles .
Figure 8. Configuration Profiles 
- Go to the profile for the associated Edge and select the appropriate Profile.
- Under the correct Profile, perform the following. steps:
- Go to the Device tab, under Cloud VPN and Branch to Non SD-WAN Destination via Gateway, select the checkbox next to Enable.
- In the drop-down menu, select the NSD via Gateway that was created (beginning in Step 6).
- Select the Save Changes button at the top of the screen.
Figure 9. Quick Start Profile 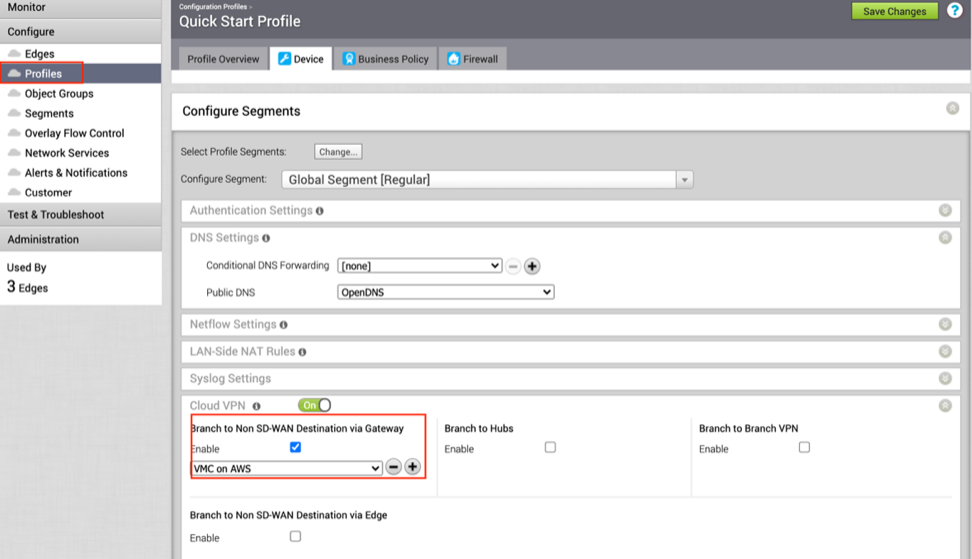
- Navigate to the Network service page, select the BGP button in NSD via Gateway service area.
Figure 10. Non SD-WAN Destinations via Gateway 
- Configure BGP parameters by performing the following steps:
- Configure Local ASN 65001
- Neighbor IP– 169.254.32.2 c) Peer ASN – 65000 (VMC default ASN is 65000)
- Local IP – 169.254.32.1
Note: It is recommended to use a /30 CIDR from 169.254.0.0/16 subnet excluding following VMC reserved addresses- 169.254.0.0-169.254.31.255, 169.254.101.0-169.254.101.3.
Figure 11. BGP Enable 
The tunnel should be ready on the SD-WAN Orchestrator with BGP over IPSec.
- Log into the VMware Cloud Console.
- Go to Networking and Security and select the VPN tab. In the VPN area, select Route Based VPN, and select Add VPN.
Figure 12. VMC-SD-WAN 
- Provide a name for the Route Based VPN and configure the following:
- Choose a name. (Choose a name that starts with To_SDWAN_Gateway, so the VPN can be easily identified during troubleshooting and future support).
- Select the Public IP.
- Enter the remote Public IP.
- Enter the remote Private IP.
- Specify the BGP local IP.
- Specify the BGP remote IP.
- Under Tunnel Encryption, select AES 128.
- Under Tunnel Digest Algorithm, select SHA1.
- Make sure Perfect Forward Secrecy is set to Enabled.
- Enter the PSK, to match Step 7A.
- Under IKE Encryption, select AES 128.
- Under IKE Digest Algorithm, select SHA 1.
- Under IKE Type, select IKEv2.
- Under Diffie Hellman, select Group 2
- Select Save.
Figure 13. VPN Route Based 
- Once the configuration is complete, the tunnel is automatically activated and will proceed to negotiate the IKE Phase 1 and Phase 2 parameters with the peer, which is the VeloCloud Gateway.
Figure 14. VPN 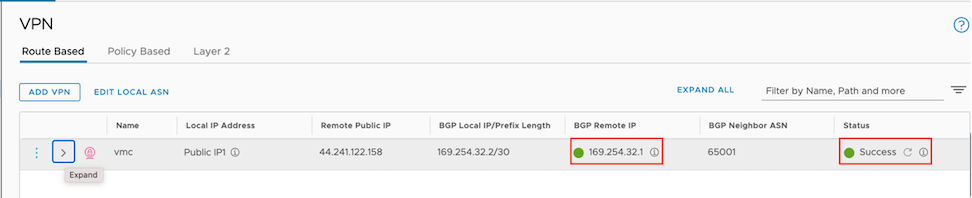
- Once the tunnel displays (green), verify that the NSD via Gateway tunnel/BGP status in the SD-WAN Orchestrator (go to Monitor > Network Services ).
Figure 15. Network Services 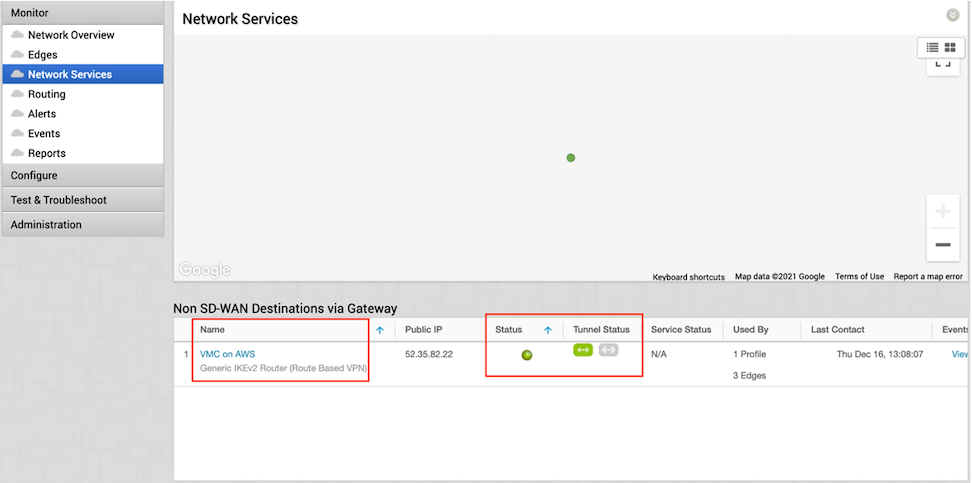
- Start a ping from a client connected at each end towards the opposite client, and verify ping reachability. The tunnel configuration has been completed and verified.
Figure 16. BGP Gateway Neighbor State 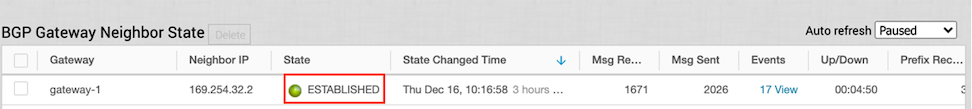
Figure 17. Ping Verification 
