Manage Gateway Pools and Gateways
Arista network consists of multiple service Gateways deployed at top tier network and cloud data centers. The Gateway provides the advantage of cloud-delivered services and optimized paths to all applications, branches, and data centers. Service providers can also deploy their own Partner Gateways in their private cloud infrastructure.
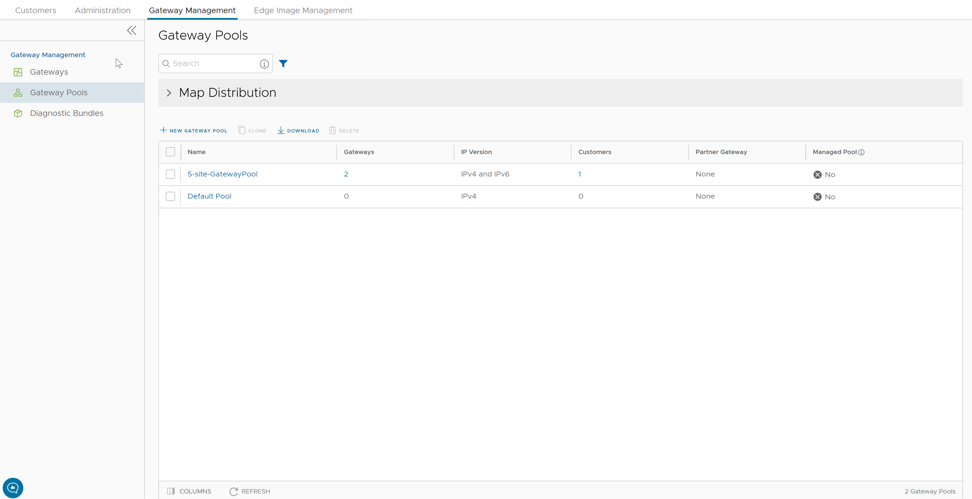
Manage Gateway Pools
A Gateway Pool is a group of Gateways.
Gateways can be organized into pools that are then assigned to a network. An unpopulated default Gateway pool is available after you install Orchestrator. If required, you can create additional Gateway pools.
To manage Gateway pools, perform the following steps:
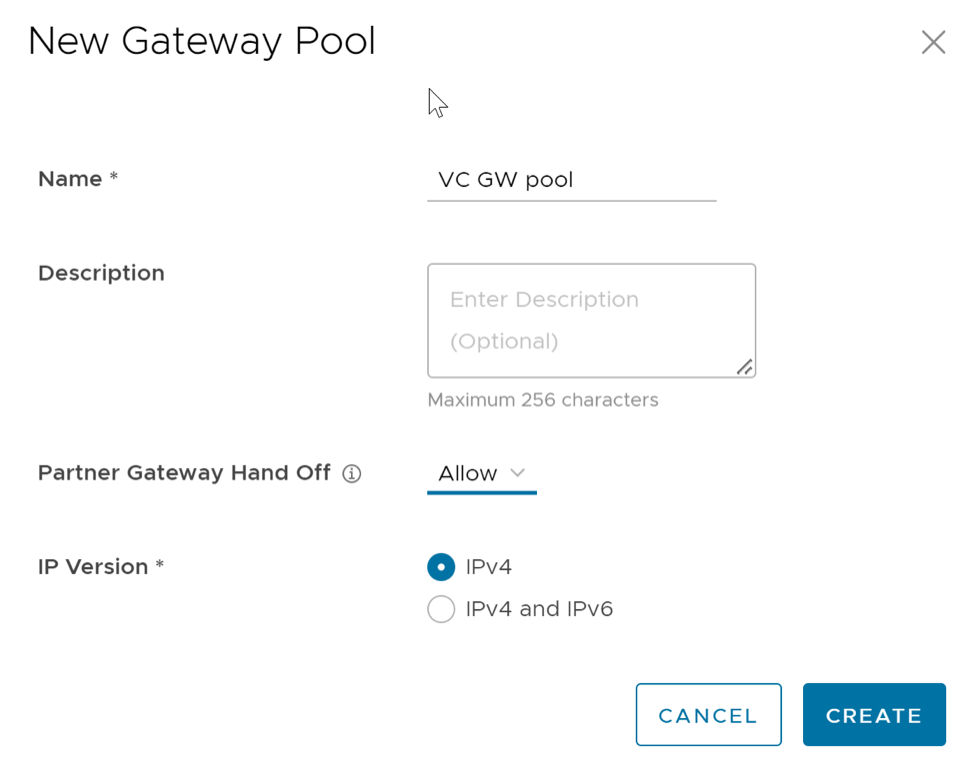
Create New Gateway Pool
In addition to the default Gateway pool, you can create new Gateway pools and associate them with Enterprise Customers.
- Configure the Gateway pool by adding Gateways to the pool. See Configure Gateway Pools.
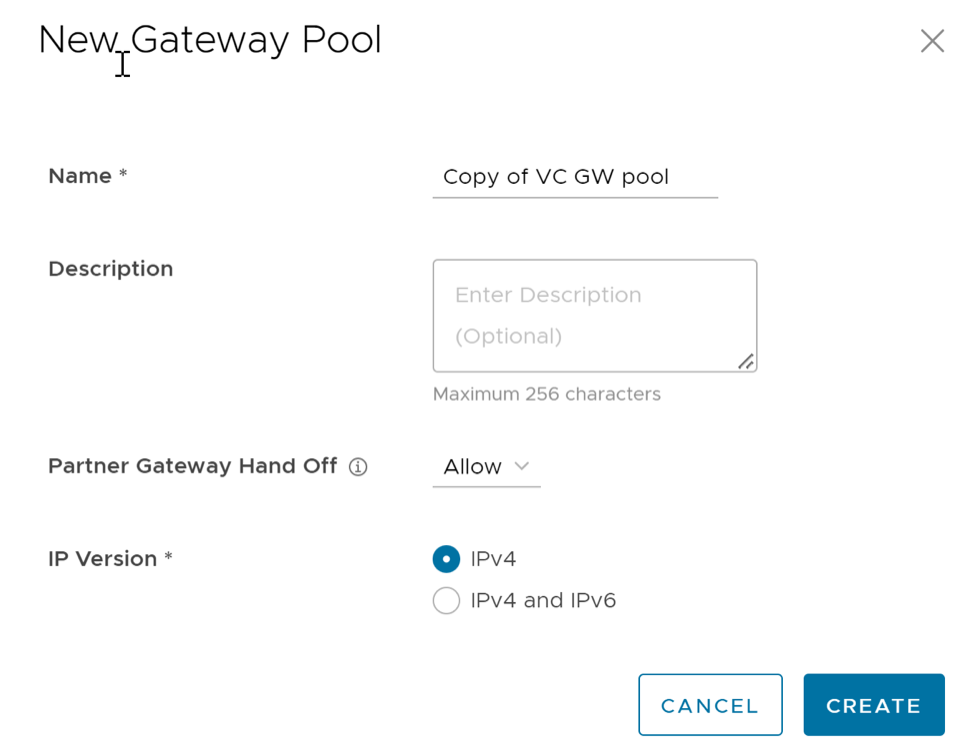
Clone a Gateway Pool
You can clone the configurations from an existing Gateway pool and create a new Gateway pool with the cloned settings.
- Configure the Gateway pool by adding Gateways to the pool. See Configure Gateway Pools.
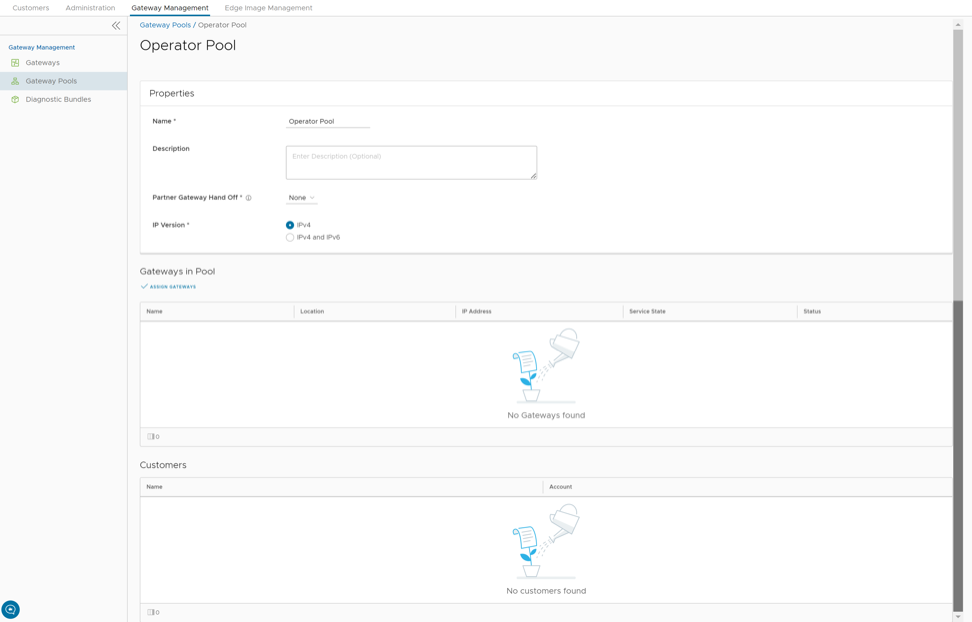
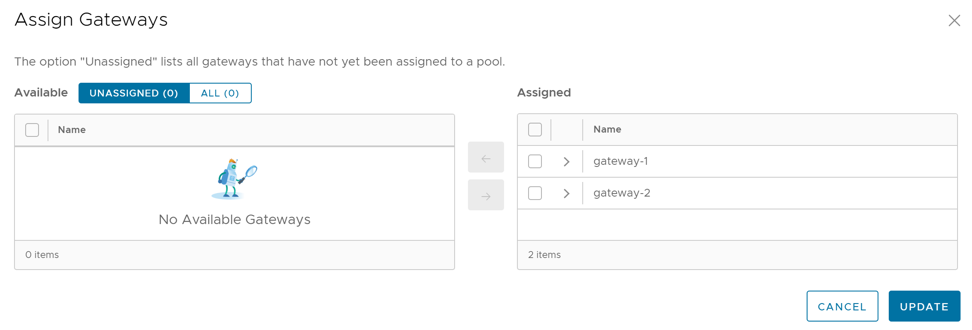
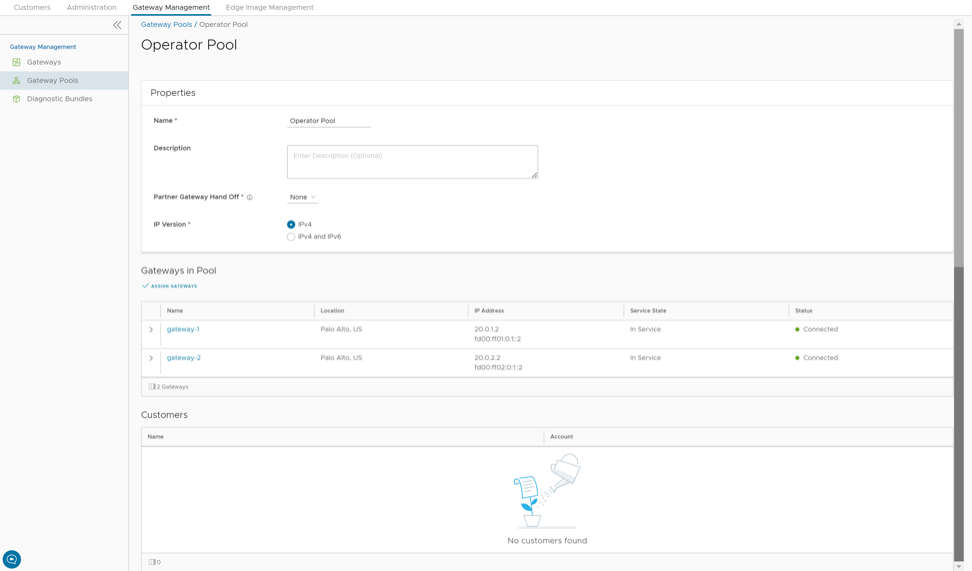
Configure Gateway Pools
After creating a Gateway pool, you can add Gateways to the pool and associate the pool to an Enterprise Customer.
Whenever you create a new Gateway pool or clone a pool, you are redirected to the Gateway Pool Overview page to configure the properties of the pool.
To configure an existing Gateway pool:
You can associate the Gateway pool to a Partner or an Enterprise Customer. The Edges available in the Enterprise are connected to the Gateways available in the pool.
- For a new customer, see Create New Customer.
- For an existing customer, see Configure Customers.
- For a new Partner, see Create New Partner.
- For an existing Partner, see Configure Partner.
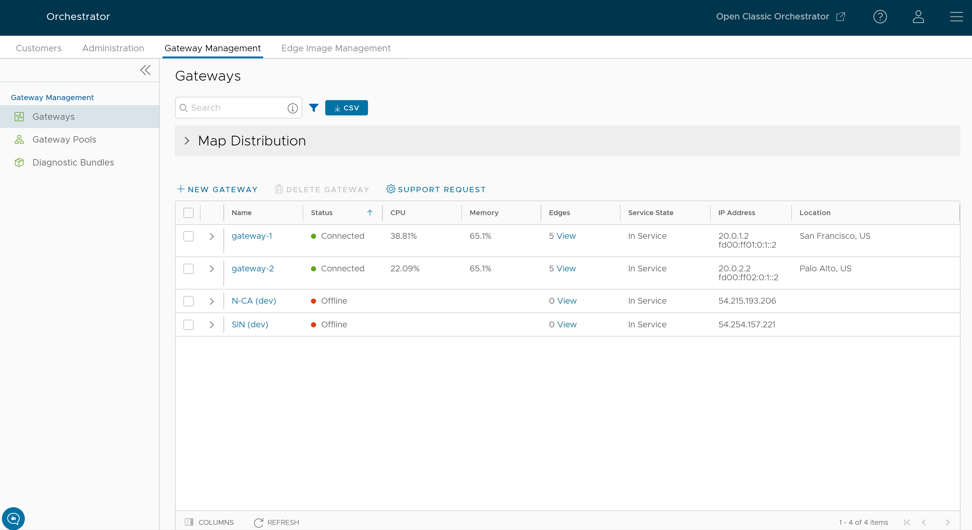
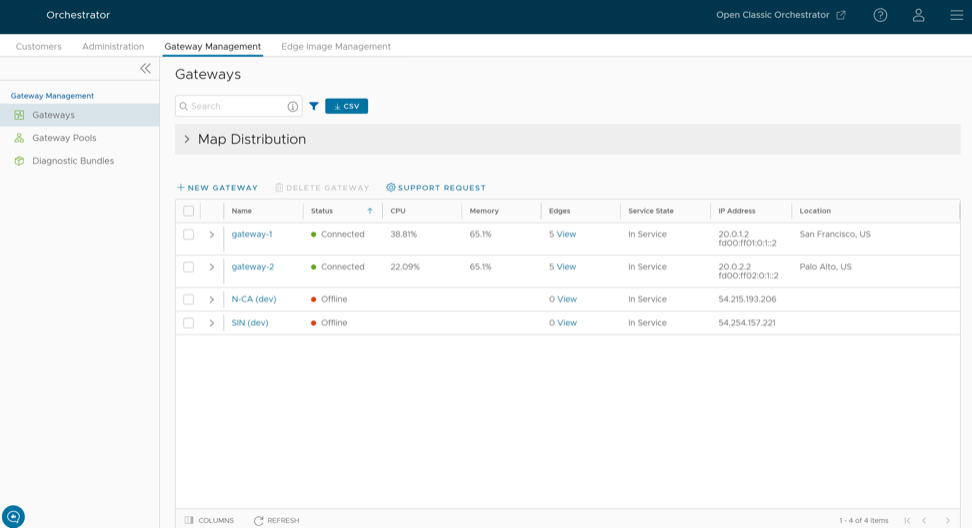
Manage Gateways
VeloCloud Gateways are a distributed network of gateways, deployed around the world or on-premises at service providers, provide scalability, redundancy and on-demand flexibility. The Gateways optimize data paths to all applications, branches, and data centers along with the ability to deliver network services to and from the cloud.
By default, the Gateways named as gateway-1 and gateway-2 are available when you install Orchestrator. If required, you can create additional Gateways.
To manage Gateways, perform the following steps:
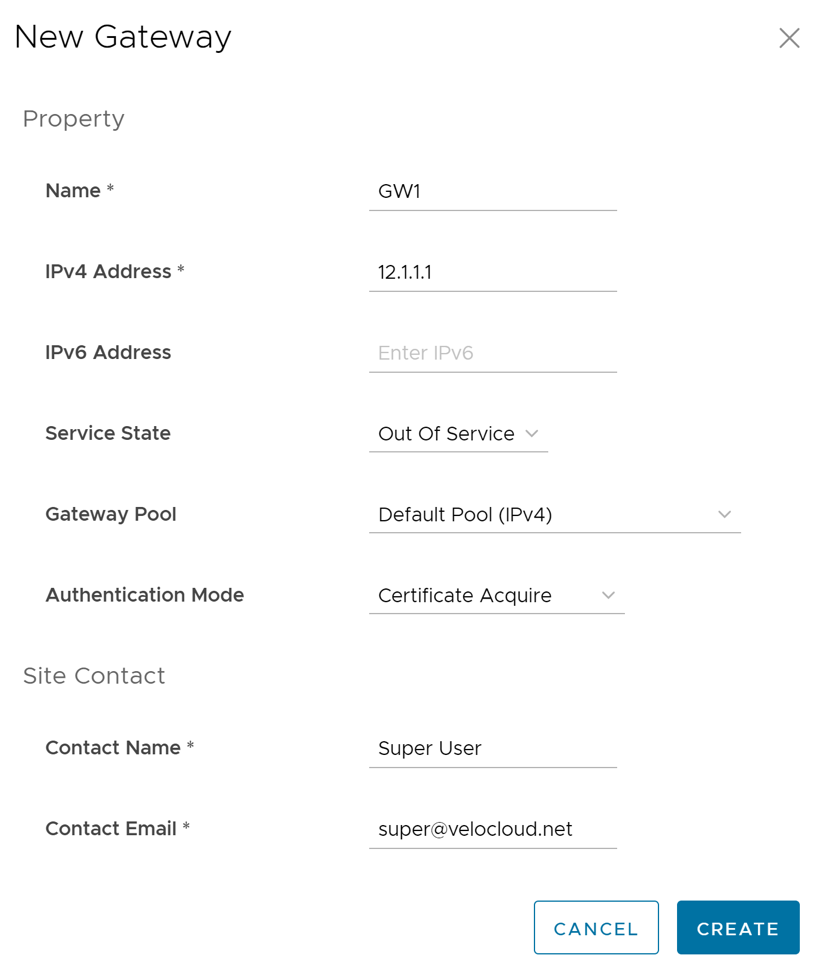
Create New Gateway
In addition to the default Gateways, you can create Gateways and associate them with Enterprise Customers.
To create a Gateway, perform the following steps.
Once you create a new Gateway, you are redirected to the Configure Gateways page, where you can configure additional settings for the newly created Gateway.
To configure additional settings for the Gateway, see Configure Gateways.
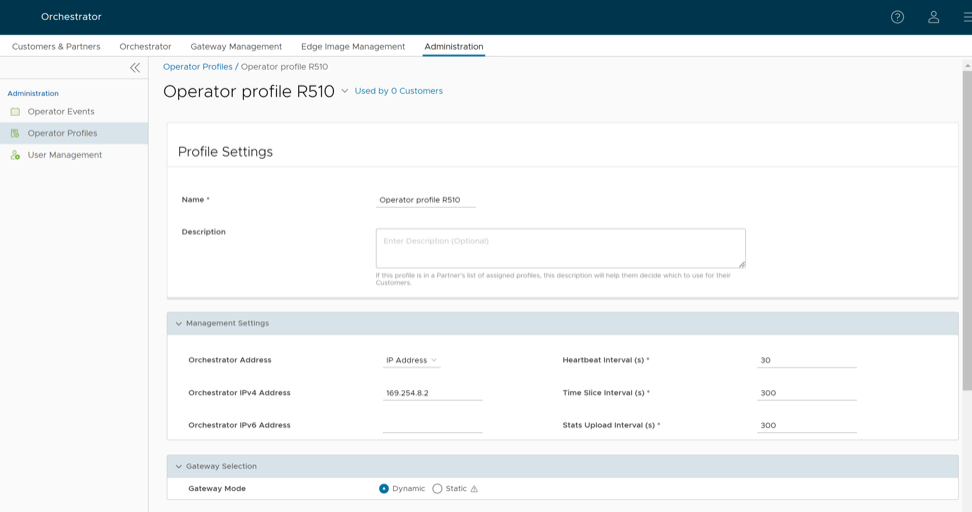
Configure Gateways
When you create a new Gateway, you are automatically redirected to the Configure Gateways page, where you can configure the properties and other additional settings for the Gateway.
To configure an existing Gateway:
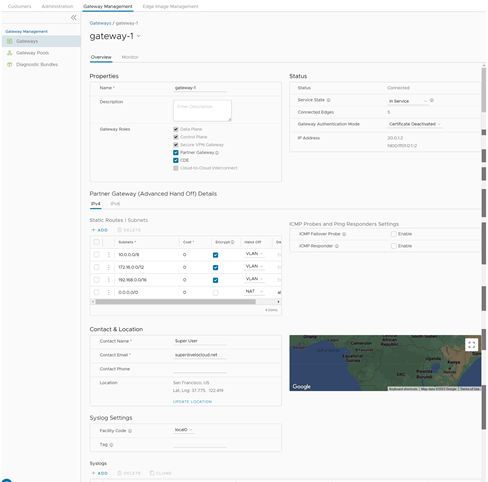
Partner Gateway (Advanced Handoff) Details
You can configure the following advanced handoff settings for the Partner Gateway:
| Option | Description |
|---|---|
| Static Routes | Subnets – Specify the subnets or routes that the Gateway should advertise to the Edge. This is global per Gateway and applies to ALL customers. With BGP, this section is used only if there is a shared subnet that all customers need to access and if NAT handoff is required.
Remove the unused subnets from the Static Route list if you do not have any subnets that you need to advertise to the Edge and have the handoff of type NAT. You can select the IPv4 or IPv6 tab to configure the corresponding address type for the Subnets. |
|
| Subnets | Enter the IPv4 or IPv6 address of the Static Route Subnet that the Gateway should advertise to the Edge. |
| Cost | Enter the cost to apply weightage on the routes. The range is from 0 to 255. |
| Encrypt | Select the check box to encrypt the traffic between Edge and Gateway. |
| Hand off | Select the handoff type as VLAN or NAT. |
| Description | Optionally, enter a descriptive text for the static route. |
| ICMP Probes and Ping Responders Settings | |
| ICMP Failover Probe – The Gateway uses ICMP probe to check for the reachability of a particular IP address and notifies the Edge to failover to the secondary Gateway if the IP address is not reachable. This option supports only IPv4 addresses. | |
| VLAN Tagging | Select the VLAN tag from the drop-down list to apply to the ICMP probe packets. The following are the available options:
|
| Destination IP address | Enter the IP address to be pinged. |
| Frequency | Enter the time interval, in seconds, to send the ping request. The range is from 1 to 60 seconds. |
| Threshold | Enter the number of times the ping replies can be missed to mark the routes as unreachable. The range is from 1 to 10. |
| ICMP Responder- Allows the Gateway to respond to the ICMP probe from the next hop router when the tunnels are up. This option supports only IPv4 addresses. | |
| IP address | Enter the virtual IP address that will respond to the ping requests. |
| Mode | Select one of the following modes from the drop-down list:
|
Upgrade Orchestrator for Dual Stack Support
To upgrade Orchestrator to release 5.0.0 to support dual stack, perform the following:
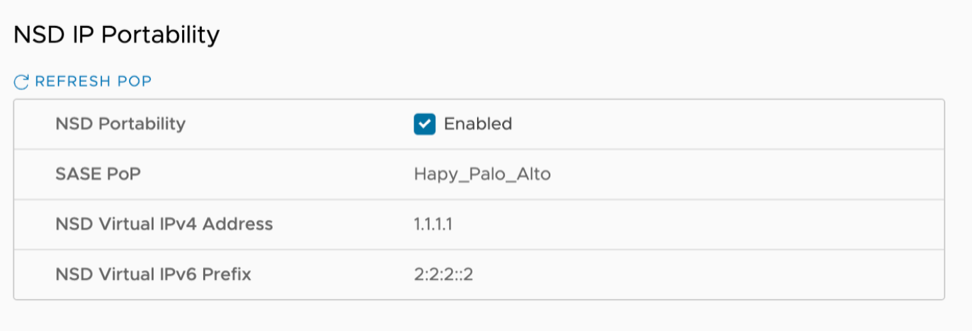
Configure IPv6 Address on Gateways
Ensure that the Orchestrator is running version 5.0.0 as described in Upgrade Orchestrator for Dual Stack Support.
You can provision a Gateway with both IPv4 and IPv6 addresses.
Partner Gateways
Partner Gateway can be configured with multiple subnets, each of which can be configured with a hand-off of NAT or VLAN. Each subnet can also be configured with a relative cost and whether the traffic should be encrypted or not.
The examples below illustrate two use cases for Partner Gateways configuration.
Gateway Configuration Use Case #1
In the following illustration, a Gateway is connected over VLAN/VRF mode to a VRF that has no access to the public Internet. However, the Partner Gateway must be able to contact the Orchestrator in the public cloud, and there must be a path to reach the cloud. The Gateway can selectively NAT certain traffic (such as the IP address of an Orchestrator, or the subnets used to reach public DNS servers) even though it is operating in VLAN/VRF mode.
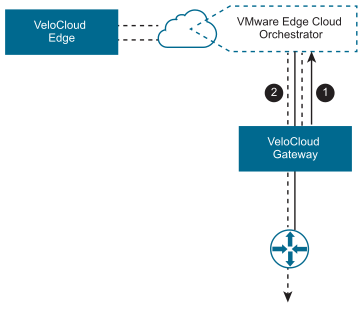
- #1- Orchestrator traffic is routed using IP addresses to NAT.
- #2- Corporate Traffic is routed through subnets to VLAN/VRF.
Gateway Configuration Use Case #2
It is common for a Partner Gateway to tie into a corporate network, providing connectivity to legacy sites. This need can occur even when not all corporate sites have been converted to Aristanetwork. For this use case, it is necessary to specify traffic by subnet on the Partner Gateway. Each subnet can also be configured to encrypt network traffic.
The following illustration shows an example where only the traffic to legacy sites is encrypted. If the Gateway is already configured with a 0.0.0.0/0 subnet to allow all traffic (which is a common configuration), all that would be required is to add the private subnet for your legacy sites and mark it as encrypted.
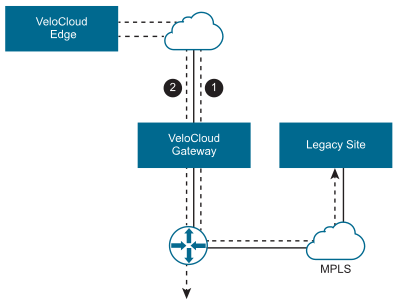
- #1- Subnet (e.g., 10.0.0.0/8) defined for Legacy Sites and marked for encryption. Traffic is transmitted between Edge and Gateway over the IPsec tunnel.
- #2- Remaining traffic is sent unencrypted to the Edge, and then to its final destination.
- For an IPsec tunnel via Partner Gateway, the VCMP tunnel failure causes the existing flows to timeout. The expected behavior for existing flows is to remain on the current path. Any new flow will begin to go (direct) causing the tunnel to remain down.
- Use application map flags
mustUseGatewayanddropIfPartnerGatewayDownto force or drop traffic through the Gateway until the path is restored. If these flags are not active, a flow flush is required once tunnel path is restored.
Partner Gateway Resiliency
The Partner Gateway provides resiliency by detecting failures and failing over to an alternate Partner Gateway. This includes the ability of a Partner Gateway to detect failure conditions and for the surrounding infrastructure to detect failures of the Gateway itself.
Consider the following Gateway topology:
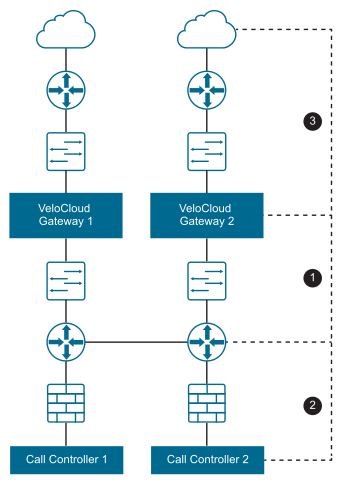
| Failure Zone | Component | Description |
|---|---|---|
| 1 | Provider Edge | The Provider Edge is one instance in which failure can be detected either from the Provider Edge router pinging the Gateway, or from the Gateway to the Provider Edge router. |
| 2 | Call Controller | The Gateway should be able to ping the Provider Edge router or Call Controller to verify connectivity. |
| 3 | WAN | The Gateway should have a stateful ping responder that responds only if the WAN zone is available. |
The Partner Gateway also supports configurable route costs to allow for more flexible failure scenarios. Finally, there is an additional hand-off type required where neither NAT nor VLAN tags are applied to the packets and they are simply passed through to the Provider Edge router.
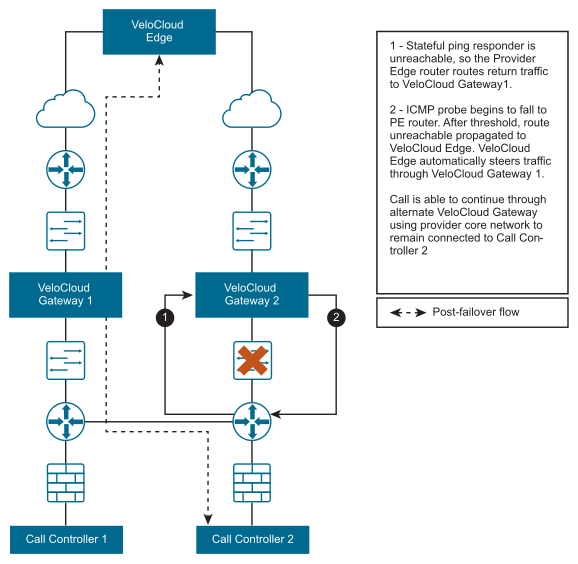
ICMP Failover Probes
This section discusses ICMP failover probes.
In order to address a failure in zones #1 or #2 of the Gateway topology diagram, the Gateway supports the optional ability to send failover probes. These probes will ping a single destination IP address at the specified frequency. If the threshold for successive missed ping replies is exceeded, the VeloCloud Gateway will mark the Gateway’s routes as unreachable. While the routes are marked as unreachable due to this probe failure state, probes continue to be sent. If the same threshold is exceeded for successive successful pings replies, the Gateway will mark the routes as reachable again.
Example Scenario
For example, consider the case in which a user has configured a frequency of two seconds and a threshold of three.
- VeloCloud Edges connect to the primary Gateway. The primary Gateway marks routes as reachable.
- The Primary Gateway fails to receive a reply for three successive probes (~6 seconds).
- The Primary Gateway marks routes as unreachable and communicates this to all connected Edges.
- Edges begin routing Gateway traffic via the alternate Gateway.
- Connectivity is restored and the primary Gateway receives three successive replies from probes.
- The Primary Gateway marks routes as reachable and communicates this to all connected Edges.
- Edges route traffic back through the primary Gateway.
This could be used in failure scenario #1 to ping an IP address on the Provider Edge router itself. This could be used in failure scenario #2 to ping the actual Call Controller.
Stateful Ping Responder
To address a failure in zone #2 or #3 of the Partner Gateway topology diagram, the Gateway supports an optional stateful ping responder. This allows the configuration of a virtual IP address (which must be different from the interface IP address) within the Gateway that will, based on configuration, either respond to pings always ( Gateway service is running) or conditionally based on WAN connectivity (the Gateway has VPN tunnels connected).
This can be used in failure scenario #1 by having the Provider Edge router ping the ping responder, as the Gateway becoming unreachable would cause the IP SLA on the Provider Edge router to fail. This could also be used in failure scenario #3 by having the Gateway only respond if VPN tunnels are connected- this is similar to the behavior with BGP (no clients connected means no client routes).
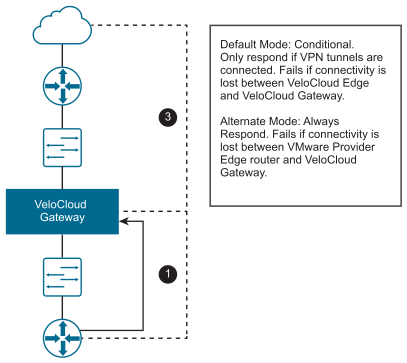
The Partner Gateway will respond back to the Provider Edge (PE) router ICMP request based on the IP SLA configured in the PE router. The Stateful Ping Responder PE router should be configured as shown below with proper VLAN tag information.
!IP-SLA configuration to send ICMP request to gateway virtual IP ip sla 1 icmp-echo 192.168.10.10 source-ip 192.168.10.1 vrf CUSTOMER1 threshold 1000 timeout 1000 frequency 2 ip sla schedule 1 life forever start-time now !tracking the IP SLA for its reachability track 1 ip sla 1 reachability !all the routes will reachable only when SLA probe succeeds ip route vrf CUSTOMER1 0.0.0.0 0.0.0.0 192.168.11.101 track 1 ip route vrf CUSTOMER2 0.0.0.0 0.0.0.0 192.168.12.101 track 1 ip route vrf CUSTOMER1 10.0.0.0 255.0.0.0 192.168.10.10 track 1 ip route vrf CUSTOMER2 10.0.0.0 255.0.0.0 192.168.10.10 track 1 ip route vrf CUSTOMER1 192.168.100.0 255.255.255.0 192.168.10.10 track 1Caveats When Using NAT Hand-off Mode
- For VLAN hand-off mode, the Partner Gateway can listen on any IP if it is reachable to the PE router (including its interface IP). For NAT hand-off mode, the Partner Gateway will not respond if the ICMP request comes to its own interface (WAN) IP address.
- Reverse flow is not supported in the NAT hand-off mode.
Active/Backup Subnets
This section describes how to configure active and backup subnets for a Partner Gateway.
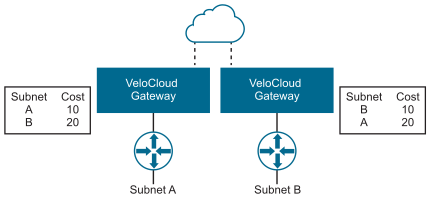
Subnets on a Partner Gateway
Subnets configured on a Partner Gateway are input as subnets and optional descriptions. A Cost field is included to allow for weighting between routes. Lower-cost routes are preferred over higher-cost routes. The following figure shows Cost settings per subnet.
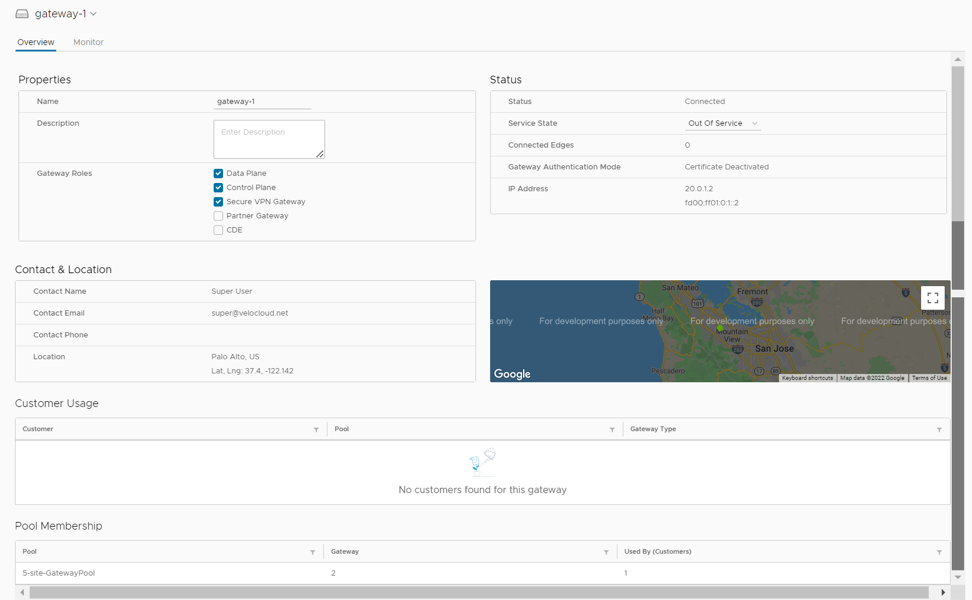
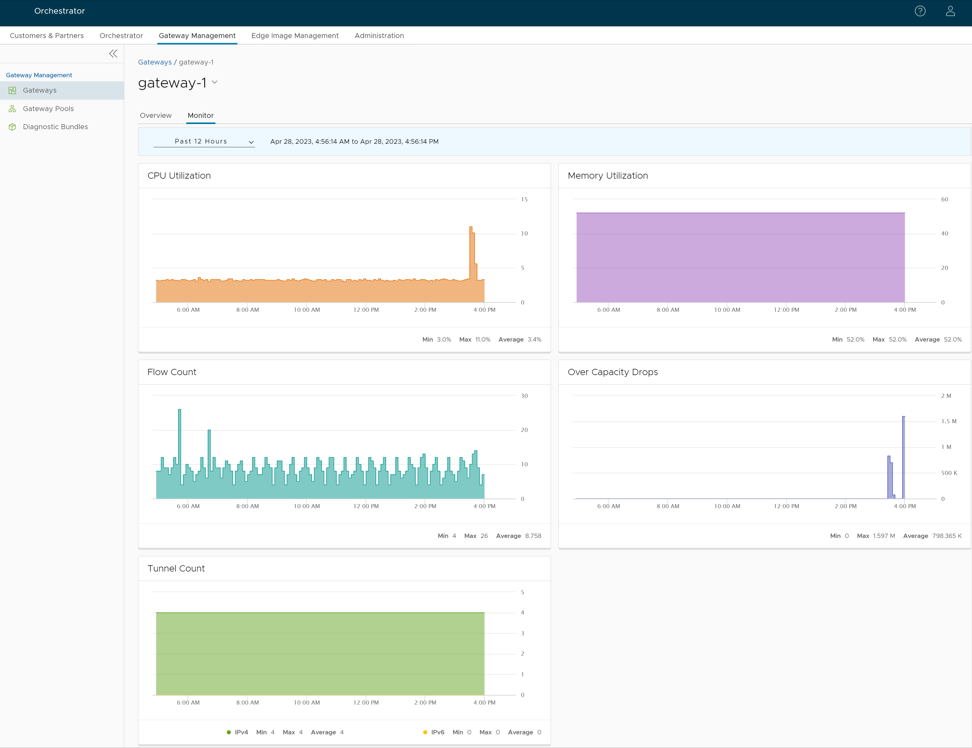
Monitor Gateways
You can monitor the status and network usage data of Gateways available in the Operator portal.
To monitor the Gateways:
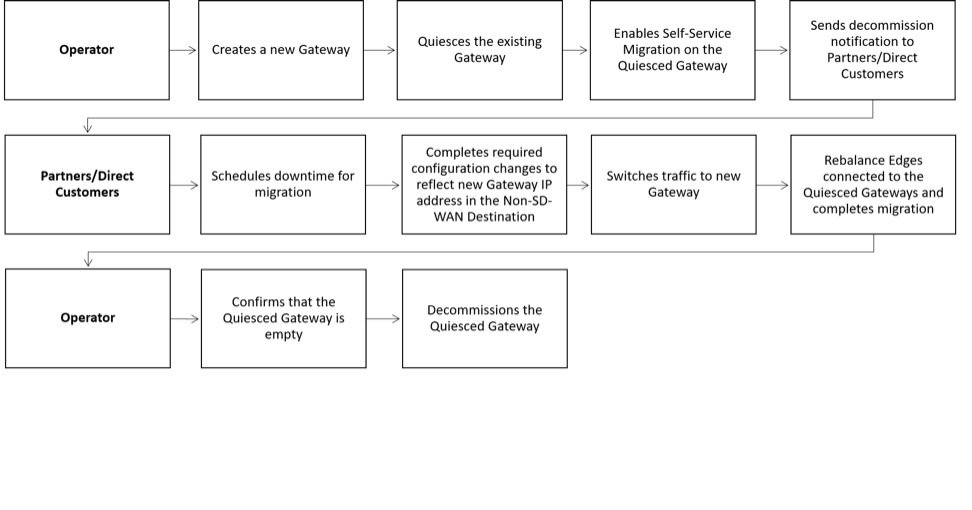
SD-WAN Gateway Migration
VeloCloud Orchestrator provides a self-service migration functionality that allows you to migrate from your existing Gateway to a new Gateway without your Operator’s support.
- Achieve operational efficiency.
- Decommission old Gateways.
Gateways are configured with specific roles. For example, a Gateway with data plane role is used to forward data plane traffic from source to destination. Similarly, a Gateway with Control Plane role is called a Super Gateway and is assigned to an Enterprise. Edges within the Enterprise are connected to the Super Gateway. Also, there is a Gateway with Secure VPN role that is used to establish an IPSec tunnel to a Non SD-WAN destination (NSD). The migration steps may vary based on the role configured for the Gateway. For additional information about the Gateway roles, see the “Configure Gateways” section in the Arista VeloCloud SD-WAN Operator Guide.
The following figure illustrates the migration process of the Secure VPN Gateway:
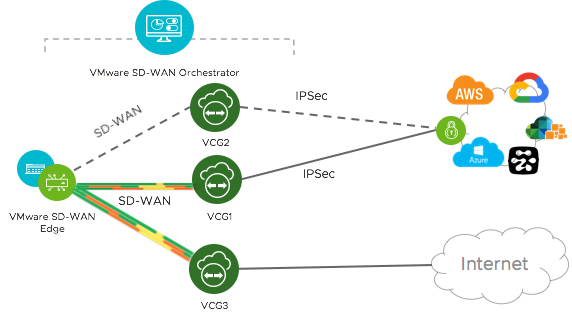
In this example, an SD-WAN Edge is connected to an NSD through a Secure VPN Gateway, VCG1. The VCG1 Gateway is planned to be decommissioned. Before decommissioning, a new Gateway, VCG2 is created. It is assigned with the same role and attached to the same Gateway pool as VCG1 so that VCG2 can be considered as a replacement to VCG1. The service state of VCG1 is changed to Quiesced. No new tunnels or NSDs can be added to VCG1. However, the existing assignments remain in VCG1. Configuration changes with respect to the IP address of VCG2 are made in the NSD, an IPSec tunnel is established between VCG2 and NSD, and the traffic is switched from VCG1 to VCG2. After confirming that VCG1 is empty, it is decommissioned.
Following is the high-level workflow of Secure VPN Gateway migration based on the User roles:
Limitations of VeloCloud Gateway Migration
- Self-service migration is not supported on Partner Gateways.
- There will be a minimum service disruption based on the time taken to switch Non SD-WAN Destinations (NSDs) from the quiesced Gateway to the new Gateway and to rebalance the Edges connected to the quiesced Gateway.
- If the NSD is configured with redundant Gateways and one of the Gateways is quiesced, the redundant Gateway cannot be the replacement Gateway for the quiesced Gateway.
- During self-service migration of a quiesced Gateway, the replacement Gateway must have the same Gateway Authentication mode as the quiesced Gateway.
- For a customer deploying a NSD via Gateway where BGP is configured on the NSD, if the customer migrates the NSD to a different Gateway using the Self-Service Gateway Migration feature on the Orchestrator, the BGP configurations are not migrated and all BGP sessions are dropped post-migration.
In this scenario, the existing Gateway assigned to the NSD is in a quiesced state and requires migration to another Gateway. The customer then navigates to on the Orchestrator and initiates the Gateway Migration process to move their NSD to another Gateway. Post-migration, the BGP Local ASN & Router ID information is not populated on the new Gateway and results in NSD BGP sessions not coming up with all routes being lost and traffic using those routes is disrupted until the user manually recreates all BGP settings.
This is a Day 1 issue and while the Gateway Migration feature accounts for many critical NSD settings, the NSD's BGP settings that are not accounted for, and their loss post-migration is an expected behavior.
Workaround: The migration of a Gateway should be done in a maintenance window only. Prior to the migration, the user should document all BGP settings and be prepared to manually reconfigure these settings post-migration to minimize impact to customer users.
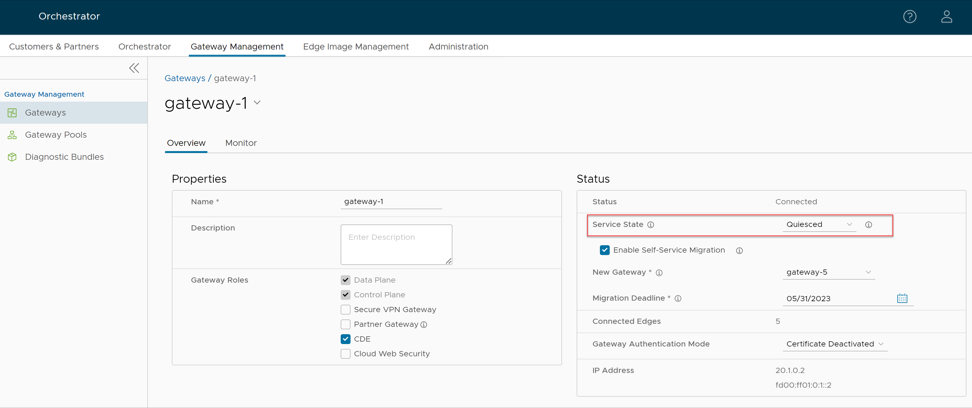
Quiesce Gateways
When you choose to decommission a Gateway, you must change the Gateway to Quiesced state so that no new tunnels or NSDs can be configured on the Gateway. Ensure that you have Operator Super User role to quiesce Gateways.
Before you quiesce the existing Gateway, ensure that you create a new Gateway as a replacement. Assign the new Gateway with the same role and attach it to the same Gateway pool as the existing Gateway. For instructions, see the “Configure Gateways” section in the VeloCloud SD-WAN Operator Guide. Also, review the Limitations of VeloCloud Gateway Migration before you proceed with quiescing the Gateway.
To quiesce the Gateway and enable self-service migration:
Send decommission notification to Partners and direct customers who are impacted. The notification email provides the migration deadline and detailed instructions on how to migrate the Edges and NSDs from the quiesced Gateway to the new Gateway.
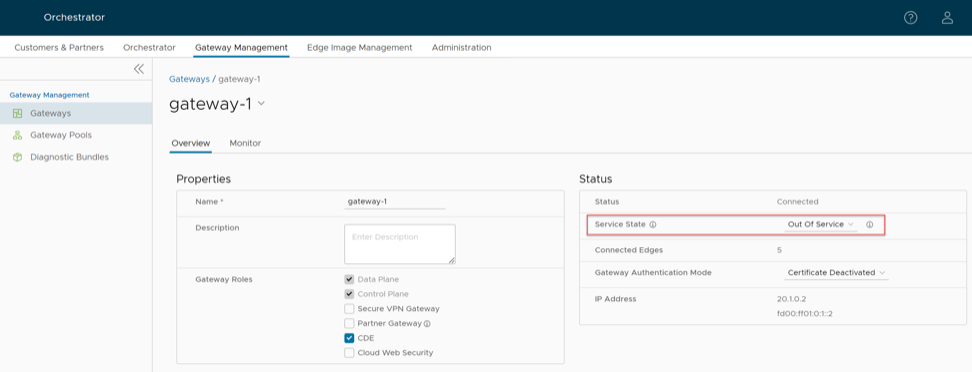
Decommission Quiesced Gateways
Before you decommission the quiesced Gateways, ensure that there are no Edges or NSDs connected to the Gateway.
In case there are Partners or direct customers who have not yet migrated from the quiesced Gateways, follow-up with them to ensure that they migrate from the quiesced Gateway. Verify that the quiesced Gateway is empty and then decommission it.
To decommission a quiesced Gateway:
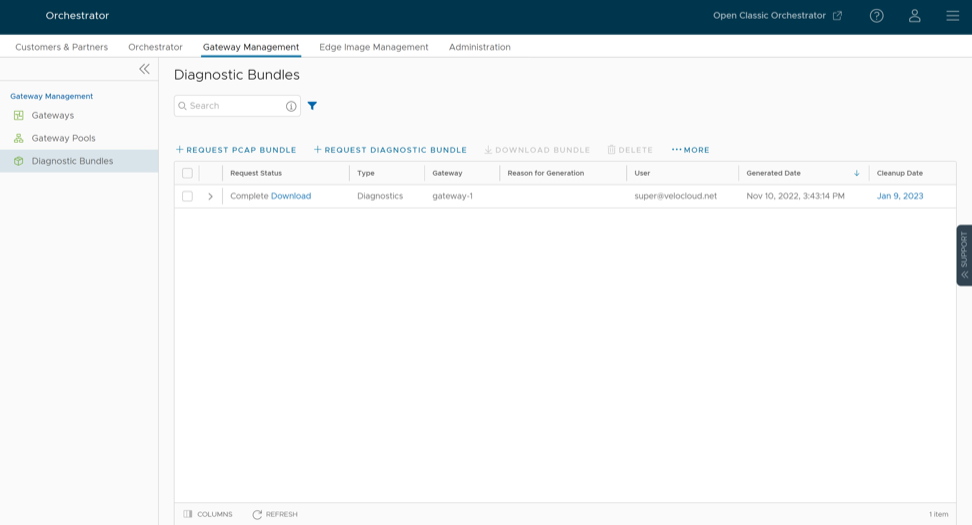
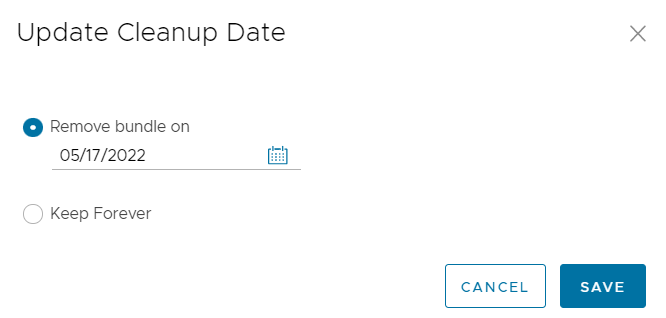
Diagnostic Bundles for Gateways
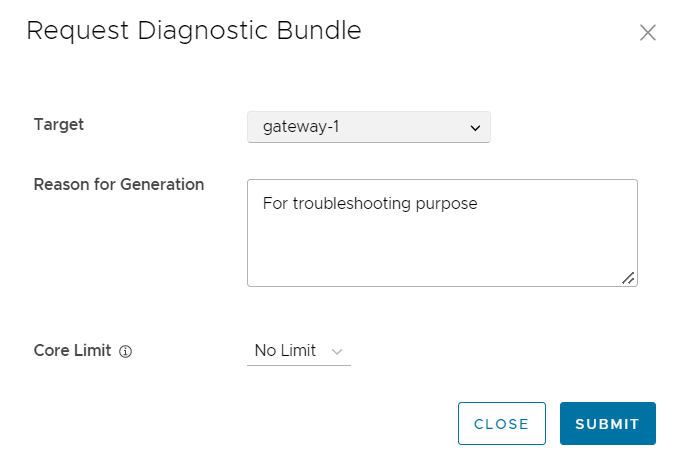
Request Diagnostic Bundles for Gateways
Diagnostic bundles allow users to collect all the configuration files and log files from a specific VeloCloud Gateway into a consolidated zipped file. The data available in the diagnostic bundles can be used for troubleshooting the Gateways.
To generate a new Diagnostic bundle:
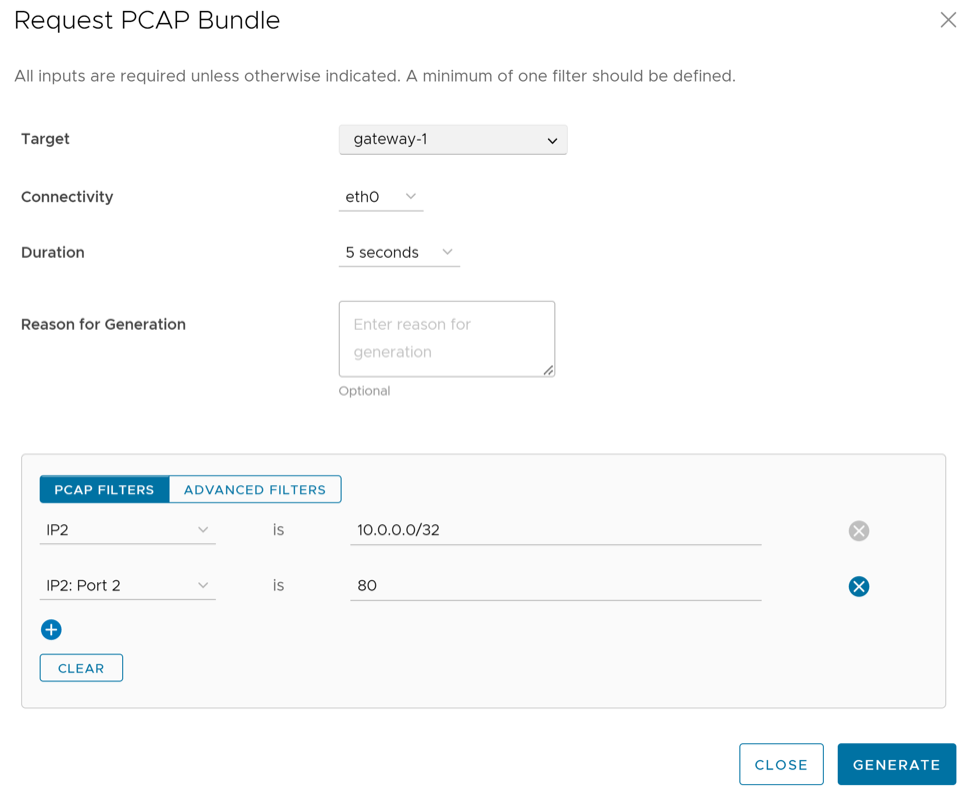
Request Packet Capture Bundle for Gateways
The Packet Capture bundle collects the packets data of a network. These files are used in analyzing the network characteristics. You can use the data for debugging the network traffic and determining network status.
To generate a PCAP bundle: