User Management - Partner
The User Management feature allows you to manage users, their roles, service permissions (formerly known as Role Customization), and authentication.
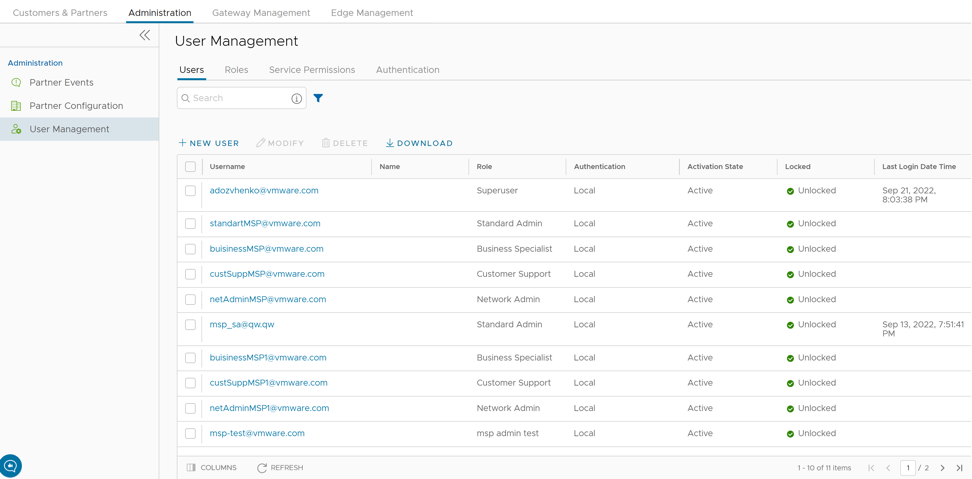
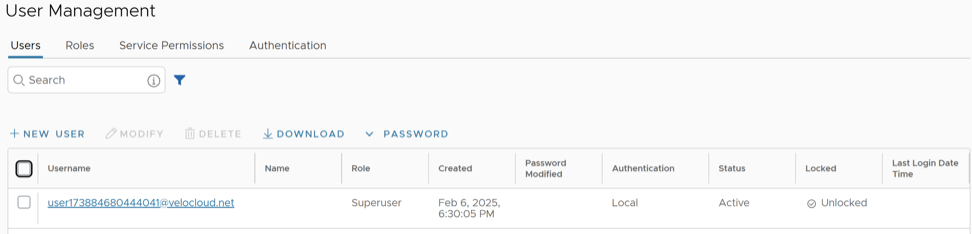
Users
As a Partner, you can view the list of existing users and their corresponding details. You can add, modify, or delete a user. However, you cannot delete a default user.
To access the Users tab:
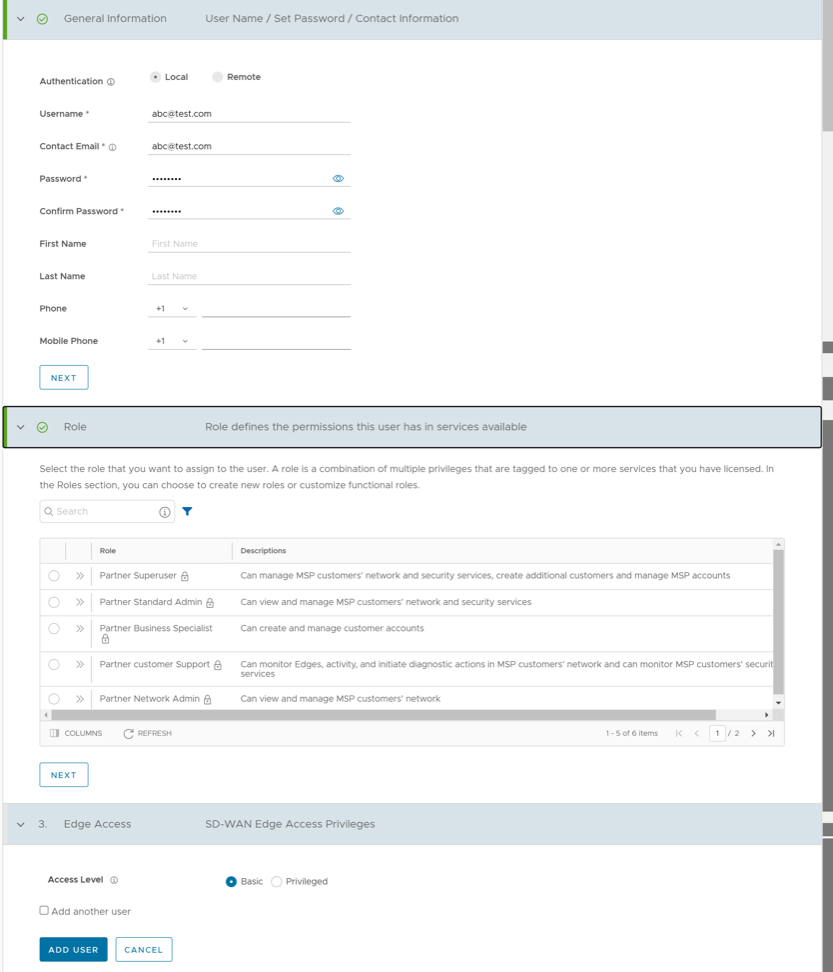
Add New User
In the Partner portal of the Orchestrator, you can add new users and configure the user settings. To add a new user, perform the following steps:
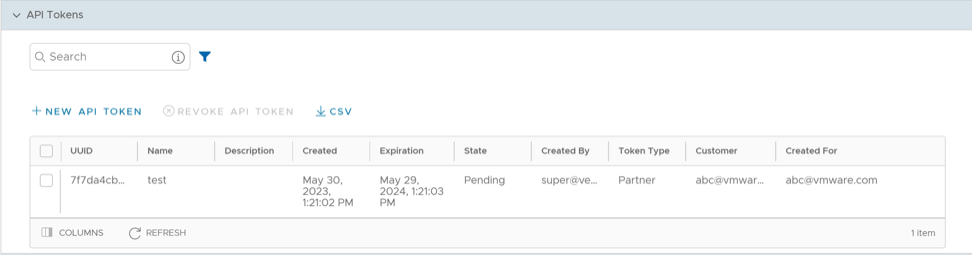
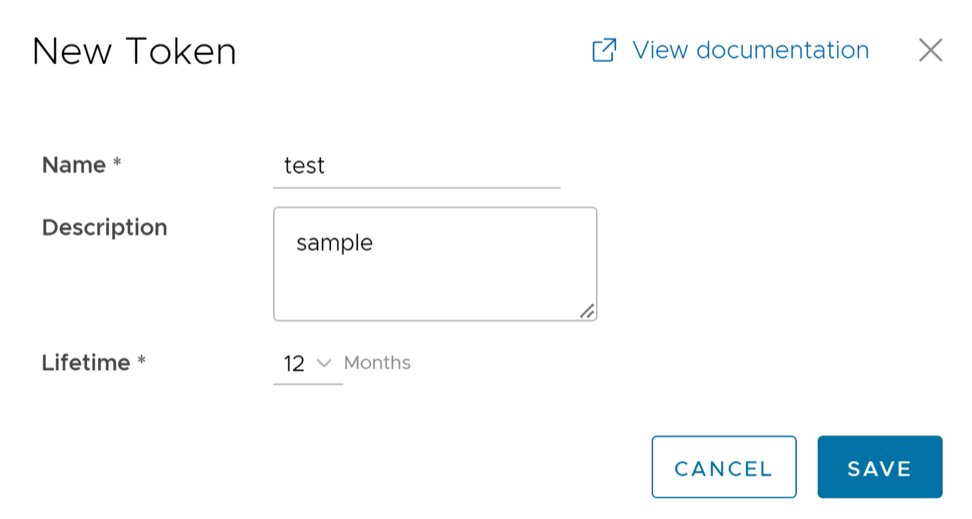
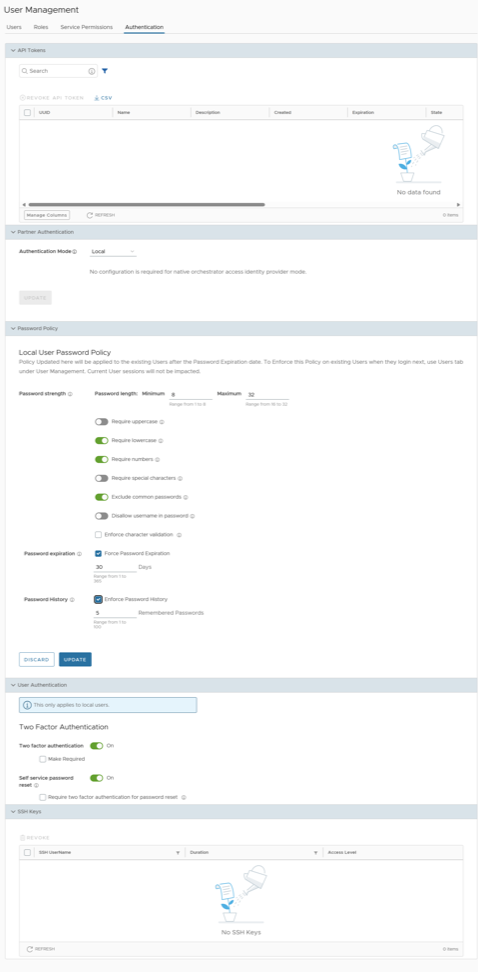
API Tokens
The users can access the Orchestrator APIs using tokens instead of session-based authentication. As Partner Super User, you can manage the API tokens for your enterprise users. You can create multiple API tokens for a user.
Any user can create tokens based on the privileges they have been assigned to their user roles, except the Business Specialist users.
- Enterprise users can Create, Download, and Revoke tokens for them.
- Partner Super users can manage tokens of Enterprise users, if the Enterprise user has delegated user permissions to the Partner.
- Partner Super users can only create and revoke the tokens for other users.
- Users can download only their own tokens and cannot download other users' tokens.
To manage the API tokens:
curl -k -H "Authorization: Token <Token>"
-X POST https://vco/portal/
-d '{ "id": 1, "jsonrpc": "2.0", "method": "enterprise/getEnterpriseUsers", "params": { "enterpriseId": 1 }}'Roles
Starting from the 5.1.0 release, Functional Roles are renamed as Privileges, and Composite Roles are renamed as Roles.
- Privileges – Privileges are a set of roles relevant to a service. A privilege can be tagged to one or more services. Users require privileges to carry out business processes. For example, a Customer support role in SD-WAN is a privilege required by an SD-WAN user to carry out various support activities. Every service defines such privileges based on its supported business functionality.
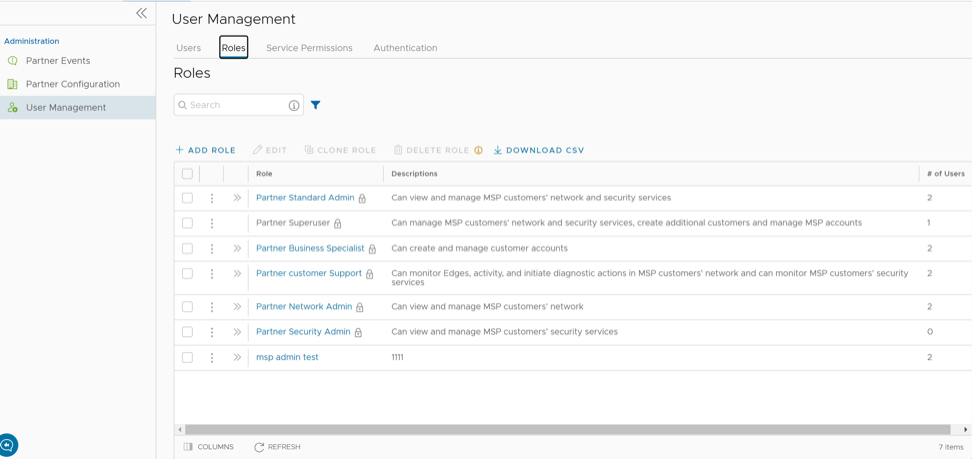
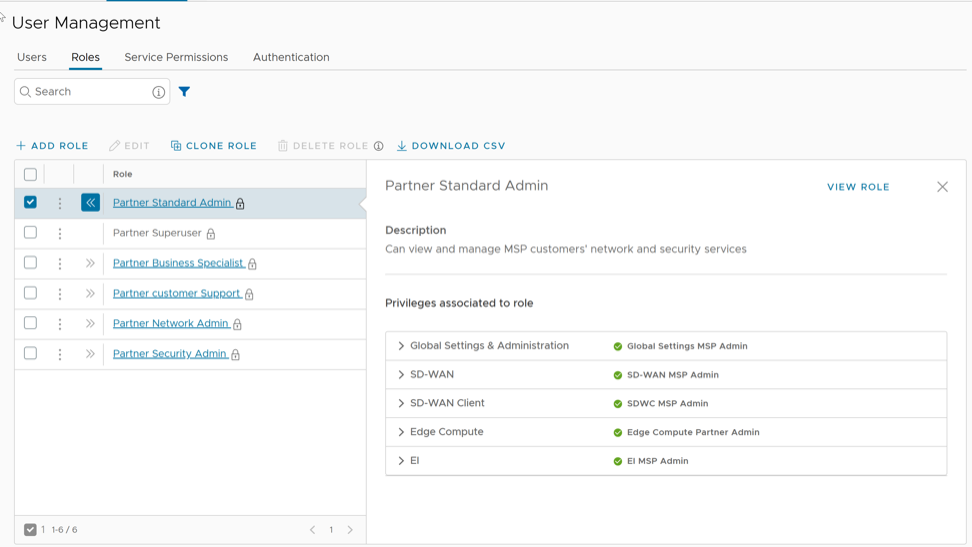
- Roles – The privileges from various categories can be grouped to form a role. By default, the following roles are available for a Partner administrator:
Table 5. Roles Role SD-WAN Service Global Settings Service Partner Standard Admin SD-WAN Partner Admin Global Settings Partner Admin Partner Security Admin SD-WAN Security Partner Admin Global Settings Partner Admin Partner Network Admin SD-WAN Partner Admin Global Settings Partner Admin Partner Superuser Full Access Full Access Partner Business Specialist SD-WAN Partner Business Global Settings Partner Business Partner Customer Support SD-WAN Partner Support Global Settings Partner Support If required, you can customize the privileges of these roles. For additional information, see Service Permissions.
As a Partner, you can view the list of existing roles and their corresponding descriptions. You can add a new role, clone an existing role, edit or delete a custom role. You cannot edit or delete a default role.
To access the Roles tab:
Add Role
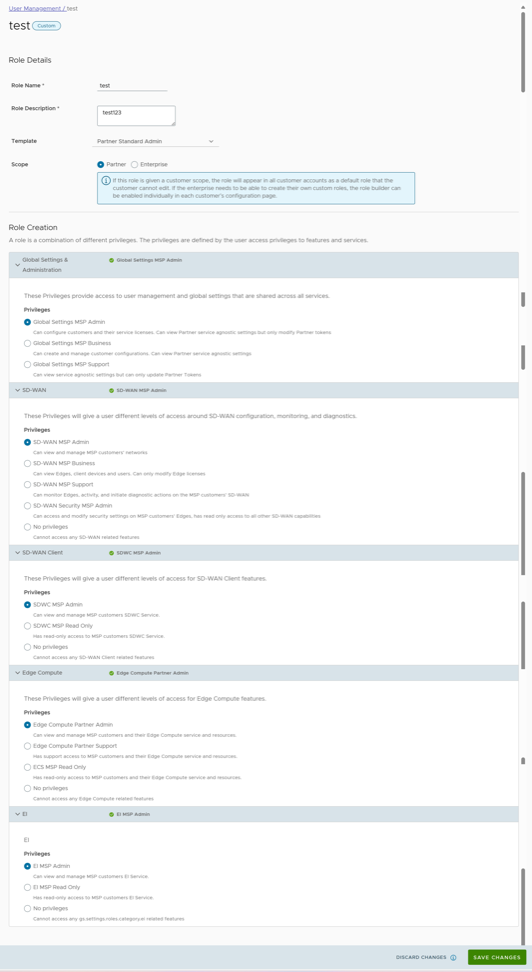
To add a new role for a Partner, perform the following steps:
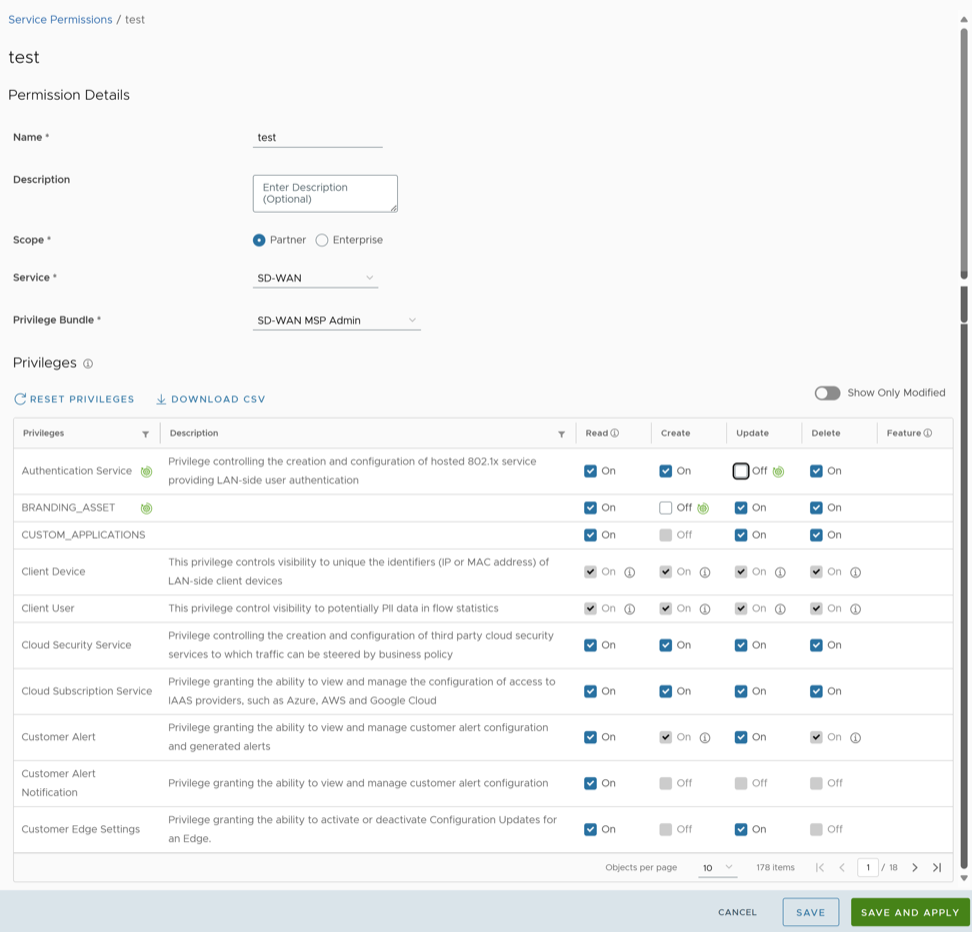
Service Permissions
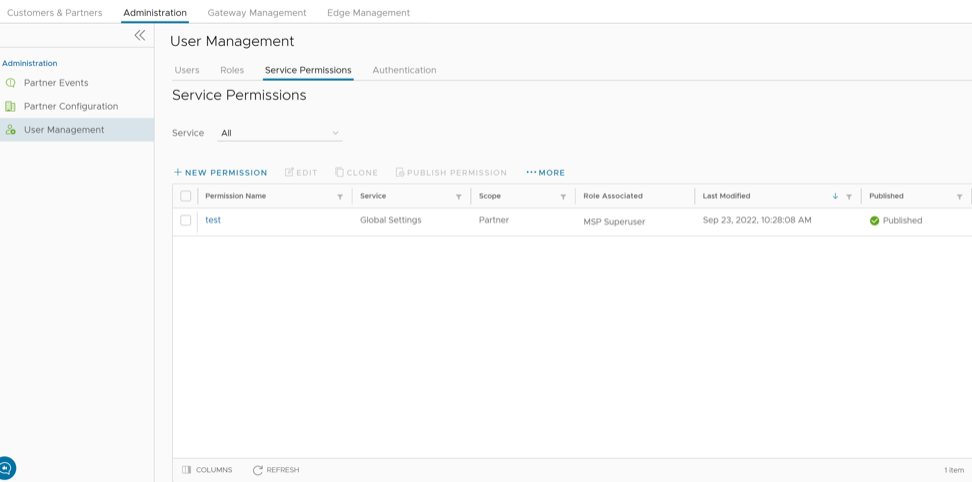
Service Permissions allow you to granularly define actions (Read, Create, Update, and Delete) assigned to each Privilege (such as Cloud Security Service and Customer Segment configuration) within a Privilege Bundle.
- Starting from the 5.1.0 release, Role Customization is renamed as Service Permissions.
- Only an Operator Superuser can activate Role Customization for a Partner Superuser. If the Role Customization option is not available for you, contact your Operator.
Roles can be customized by changing the service permissions held by each role. You can customize both, default roles and new roles. Roles are created based on the selected default role. Operator, Partner, and Enterprise roles are defined separately. So, there are default roles for each level, such as Operator Superuser, Partner Standard Admin, and Enterprise Support.
When customizing a role, you must select both, the user level and the role. Typically, Operator roles have more privileges by default, than Partners or Enterprise Customers. When creating a user, you must assign a role to the user. Any change to that specific role's privileges is immediately applied to all users assigned to that role. Role customizations only apply to one role at a time. For example, changes to Operator Standard Admin roles do not get applied to Enterprise Standard Admin roles.
For additional information, see the topic Roles.
- The customizations done at the Enterprise level override the Partner or Operator level customizations.
- The customizations done at the Partner level override the Operator level customizations.
- Only when there are no customizations done at the Partner level or Enterprise level, the customizations made by the Operator are applied globally across all users in the Orchestrator.
To access the Service Permissions tab:
New Permission
You can customize the privileges and apply them to the existing permission in the Orchestrator.
To add a new permission, perform the following steps:
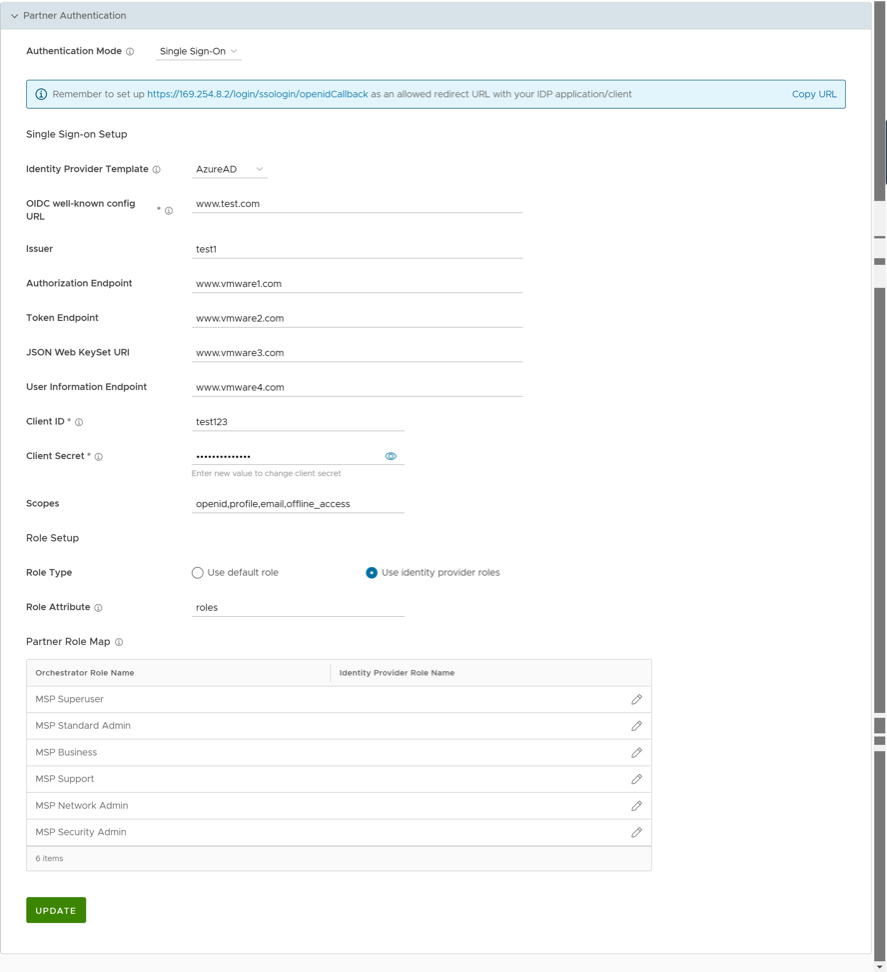
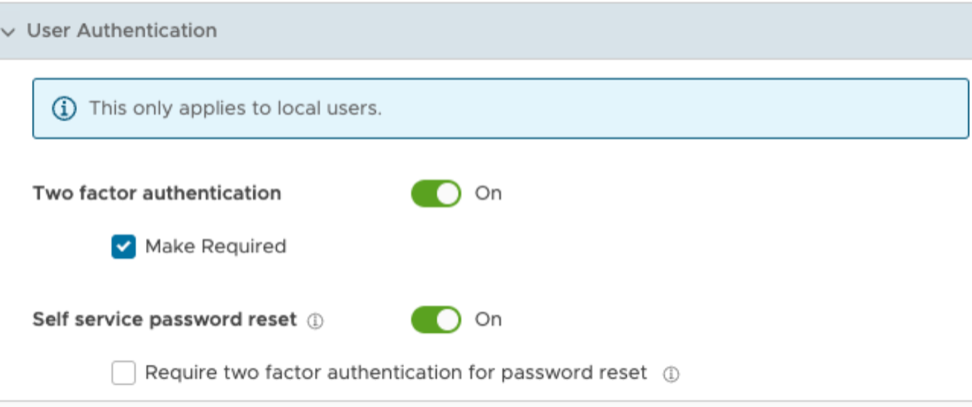
Authentication
The Authentication feature allows you to set the authentication mode for a Partner and an Enterprise user.
To set theauthentication mode:
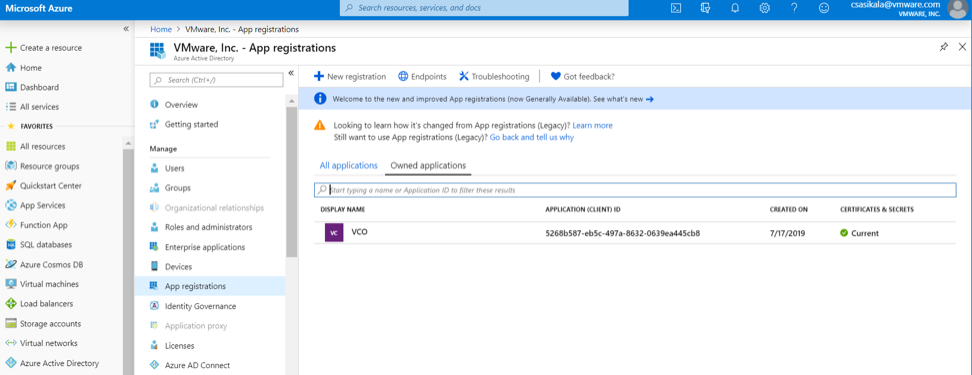
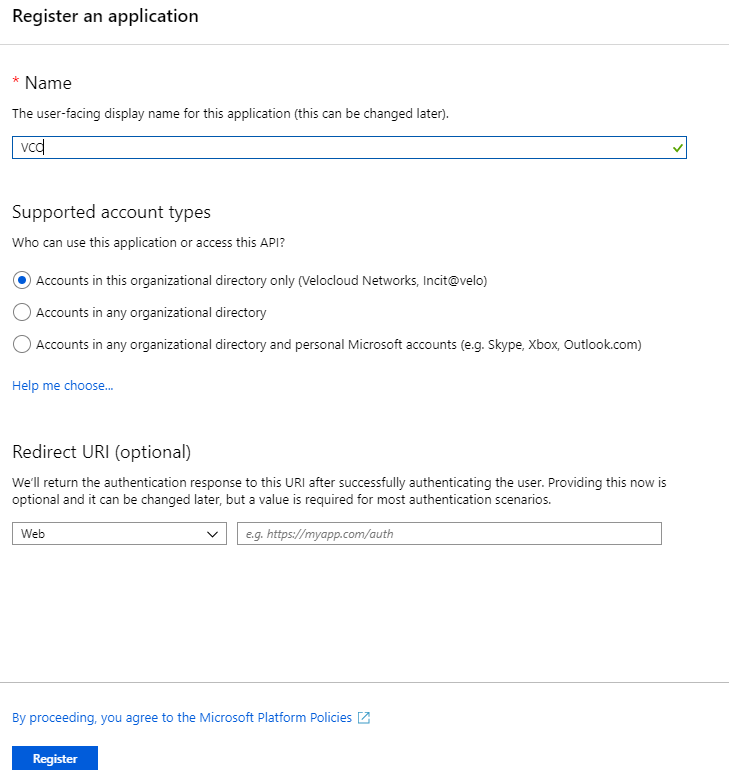
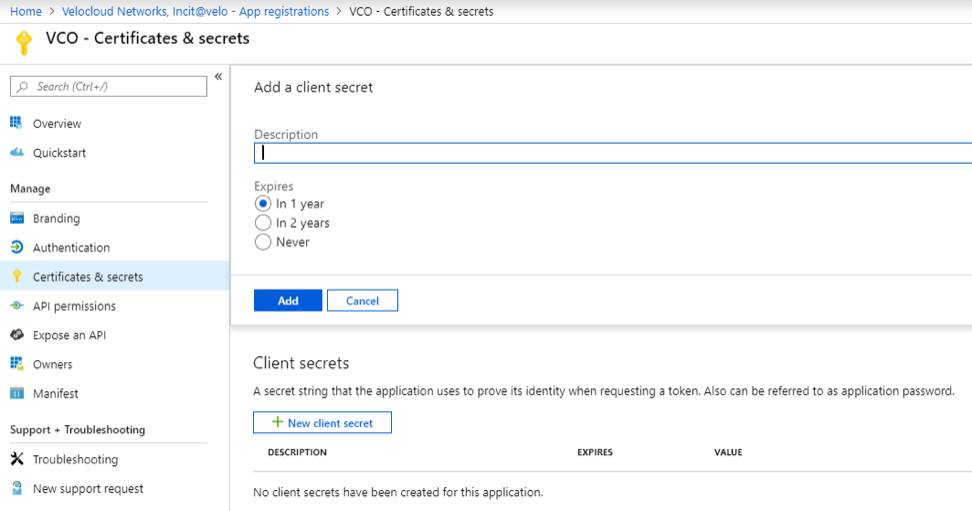
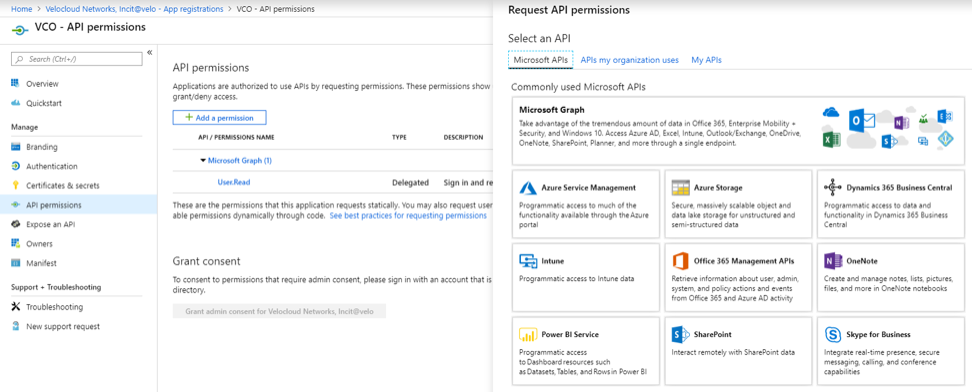
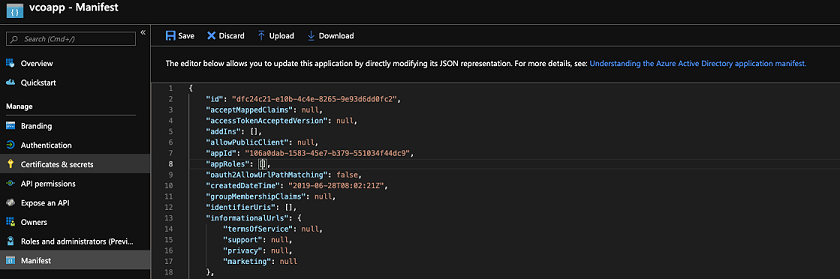
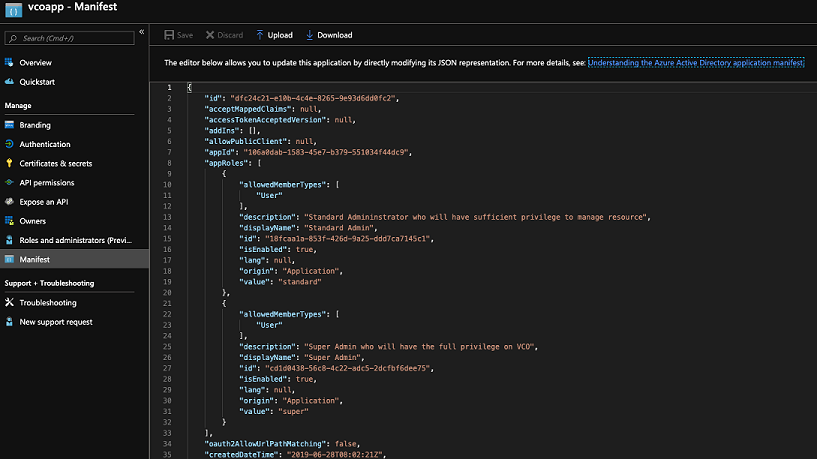
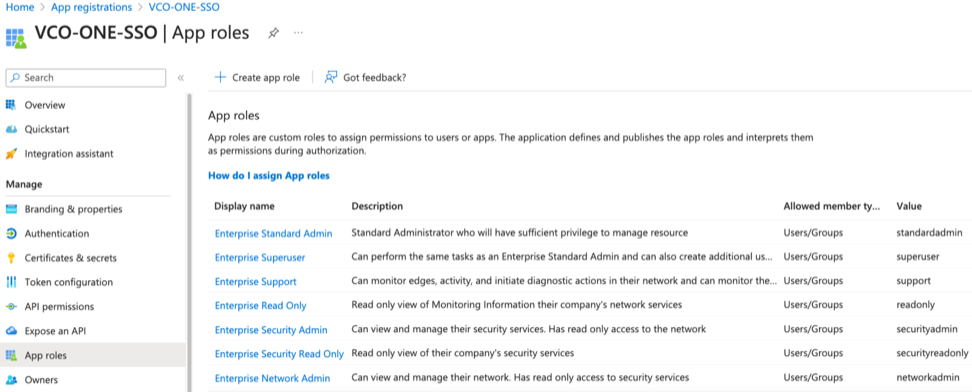
Configure Azure Active Directory for Single Sign On
To set up an OpenID Connect (OIDC)-based application in Microsoft Azure Active Directory (Azure AD) for Single Sign On (SSO), perform the following steps.
Ensure you have a valid Azure AD account.
Configure Okta for Single Sign On
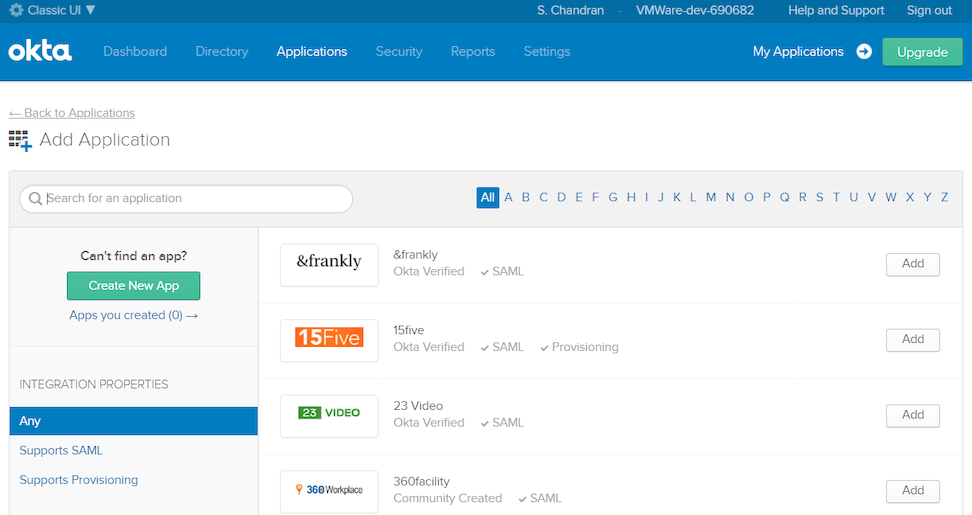
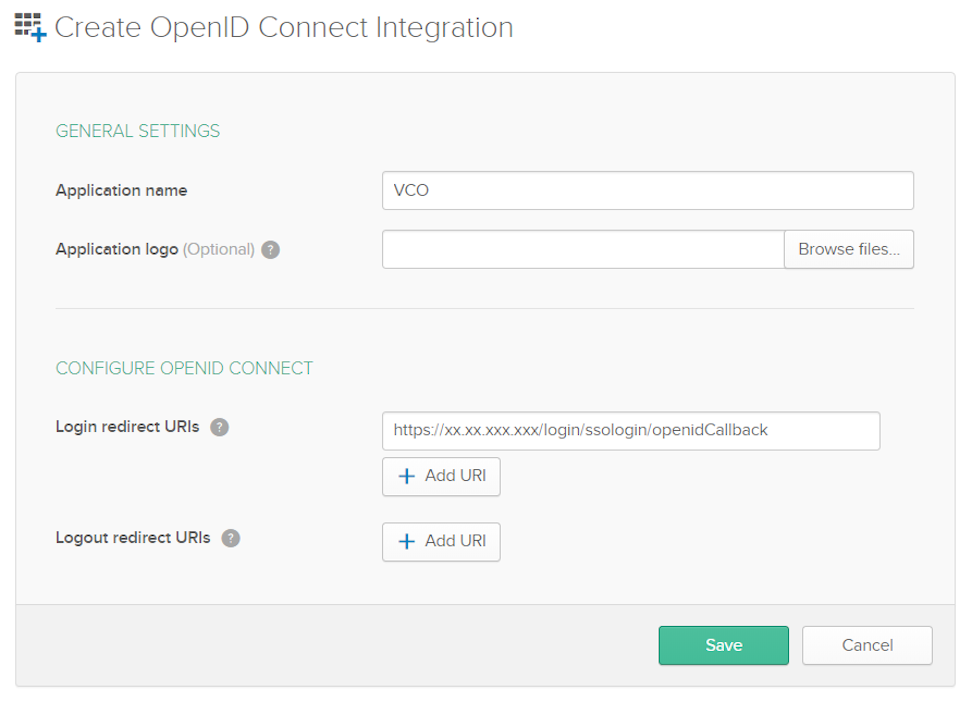
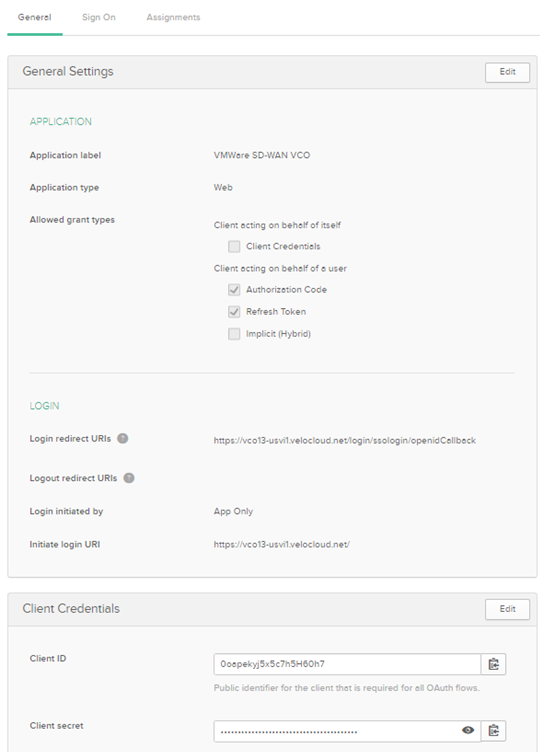
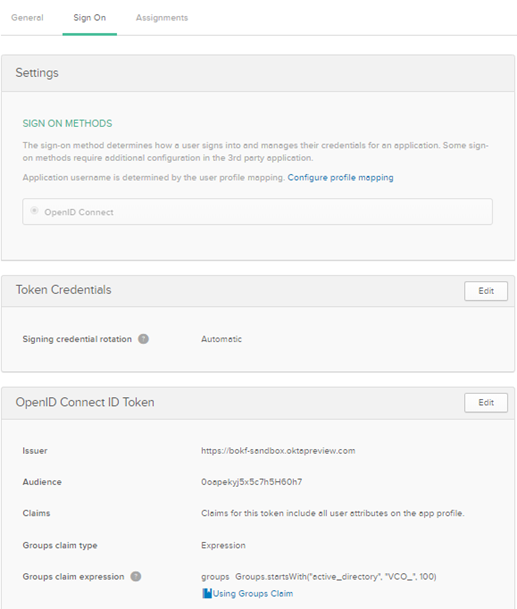
To support OpenID Connect (OIDC)-based Single Sign On (SSO) from Okta, you must first set up an application in Okta. To set up an OIDC-based application in Okta for SSO, perform the steps on this procedure.
Ensure you have an Okta account to sign in.
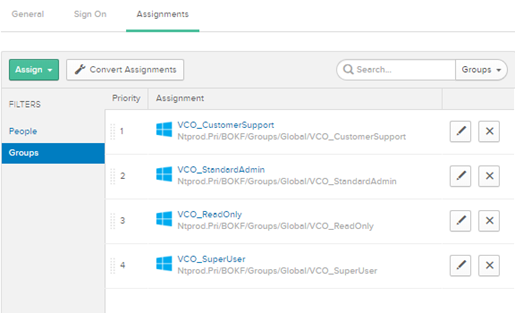
Assigning Users and Groups
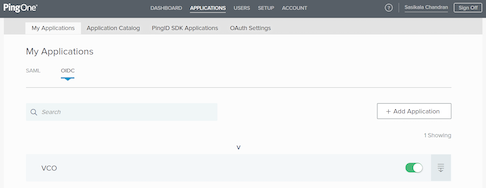
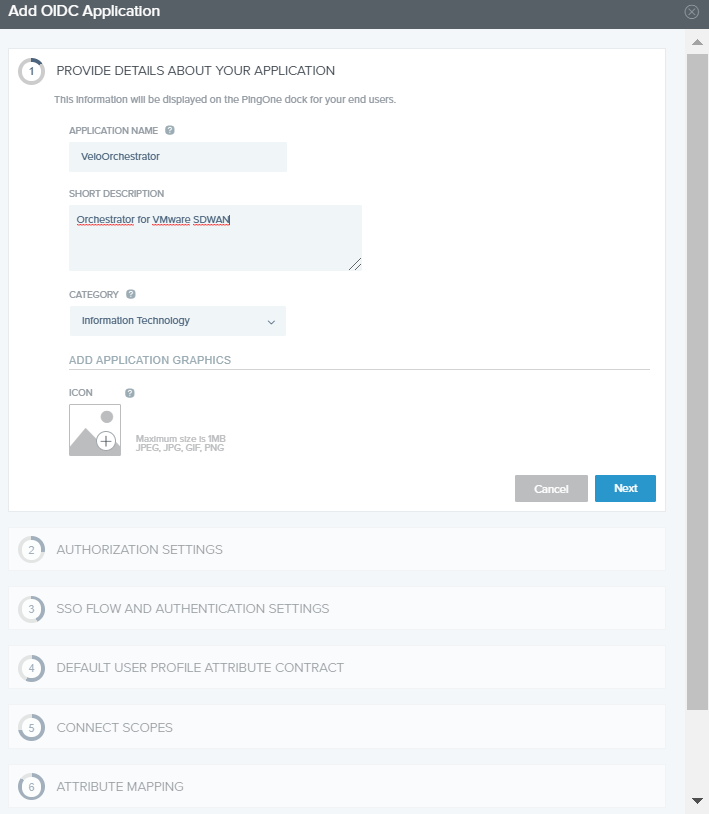
Configure PingIdentity for Single Sign On
To set up an OpenID Connect (OIDC)-based application in PingIdentity for Single Sign On (SSO), perform the steps on this procedure.
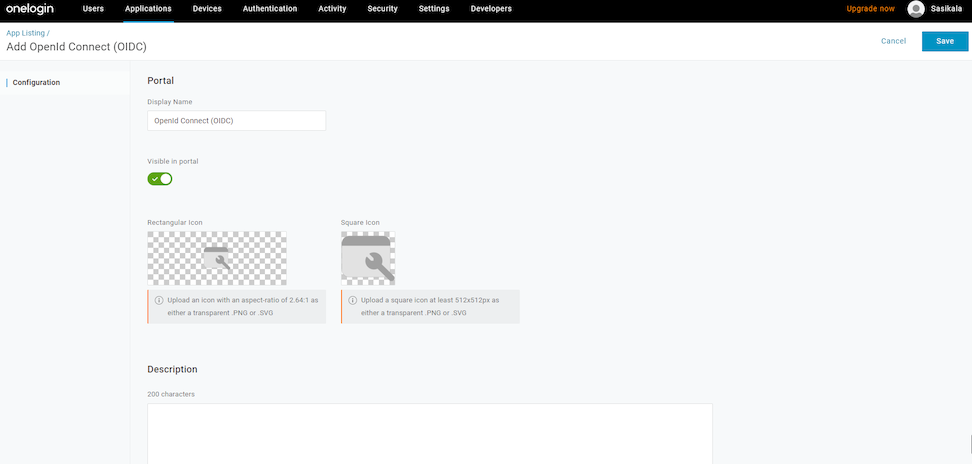
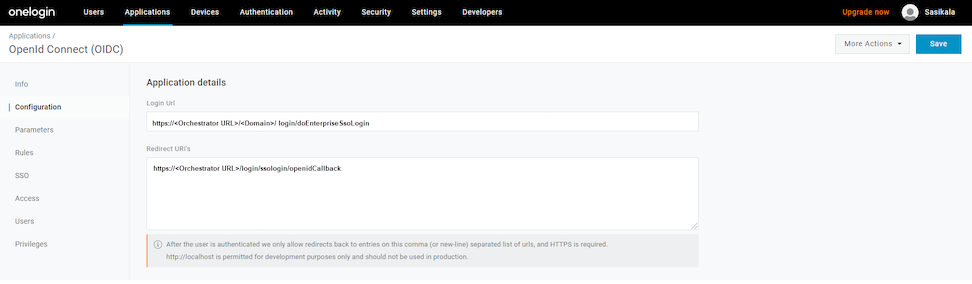
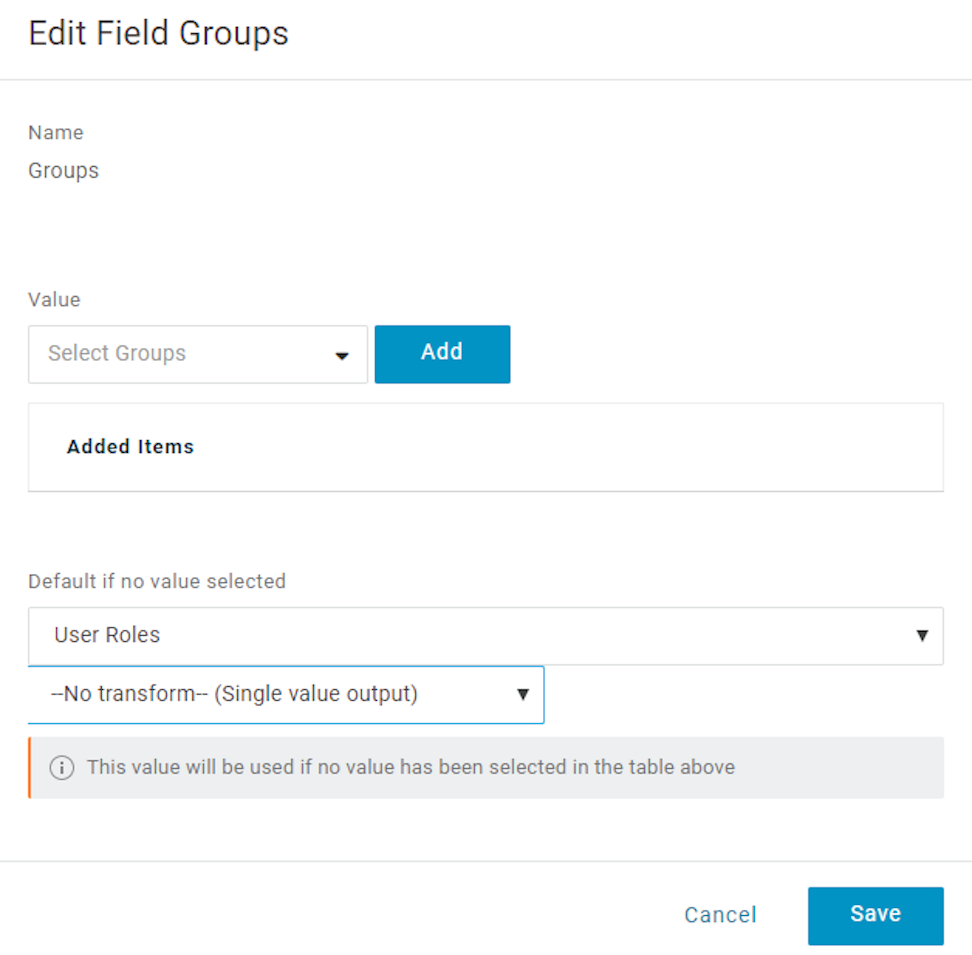
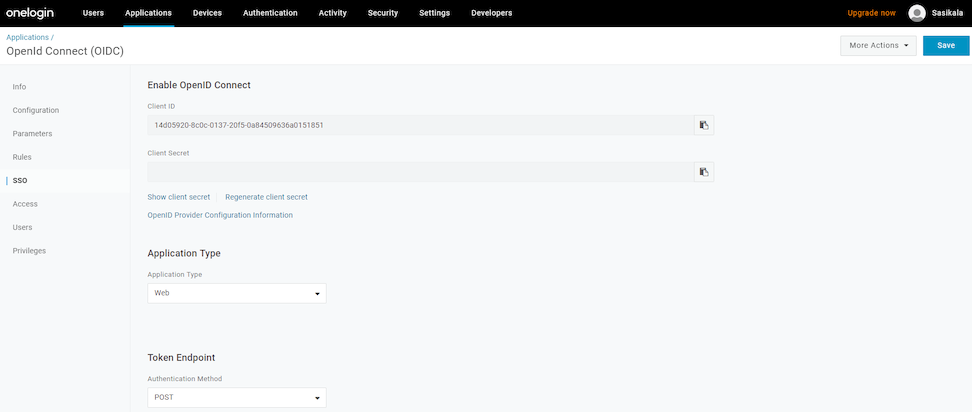
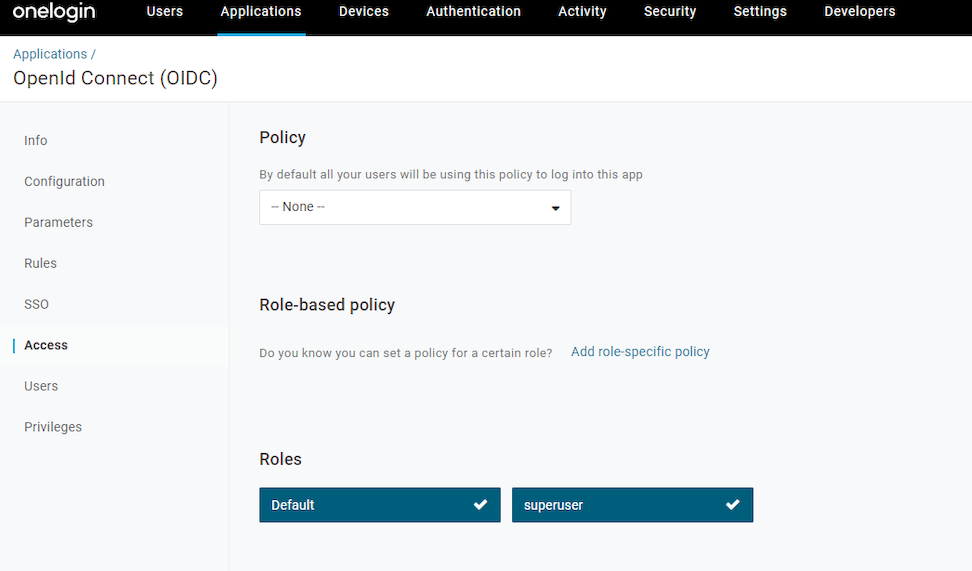
Configure OneLogin for Single Sign On
To set up an OpenID Connect (OIDC)-based application in OneLogin for Single Sign On (SSO), perform the steps below:
Ensure you have an active OneLogin account.