User Management - Partner
The User Management feature allows you to manage users, their roles, service permissions (formerly known as Role Customization), and authentication.
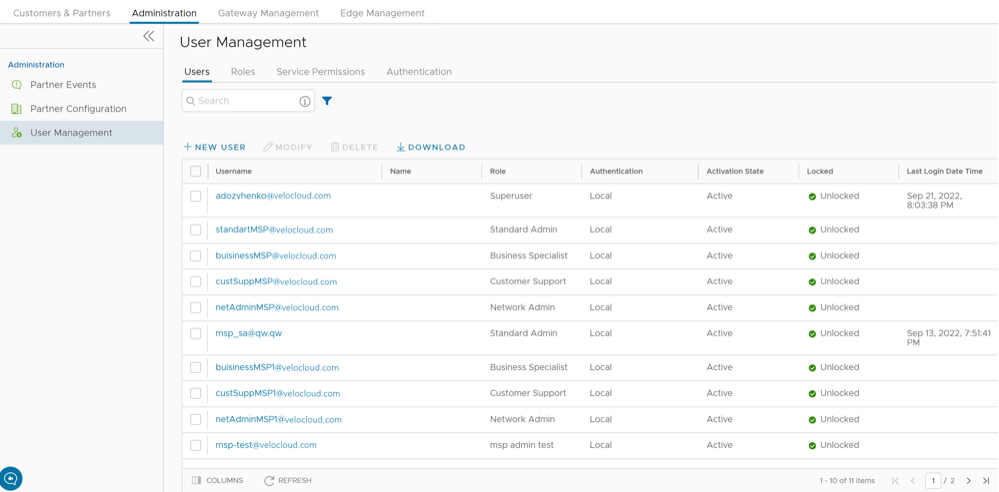
Users
To access the Users tab:
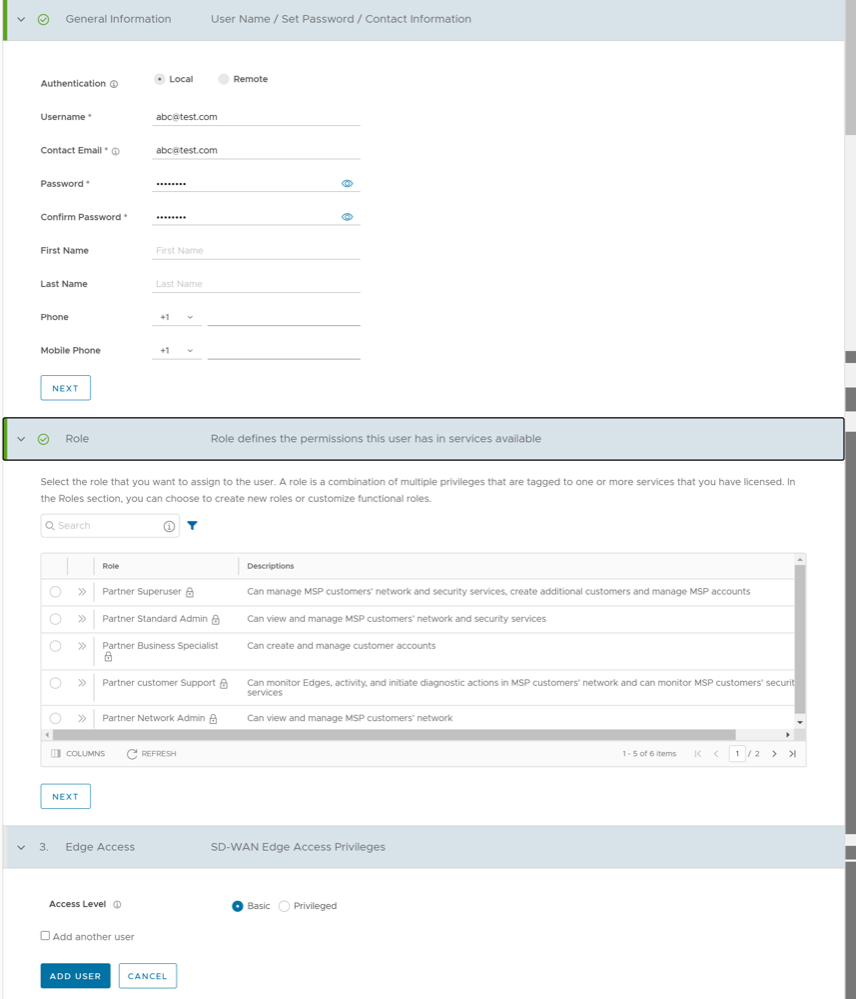
Add New User
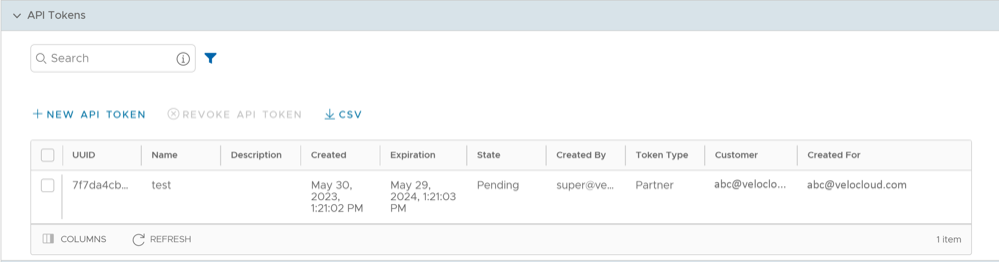
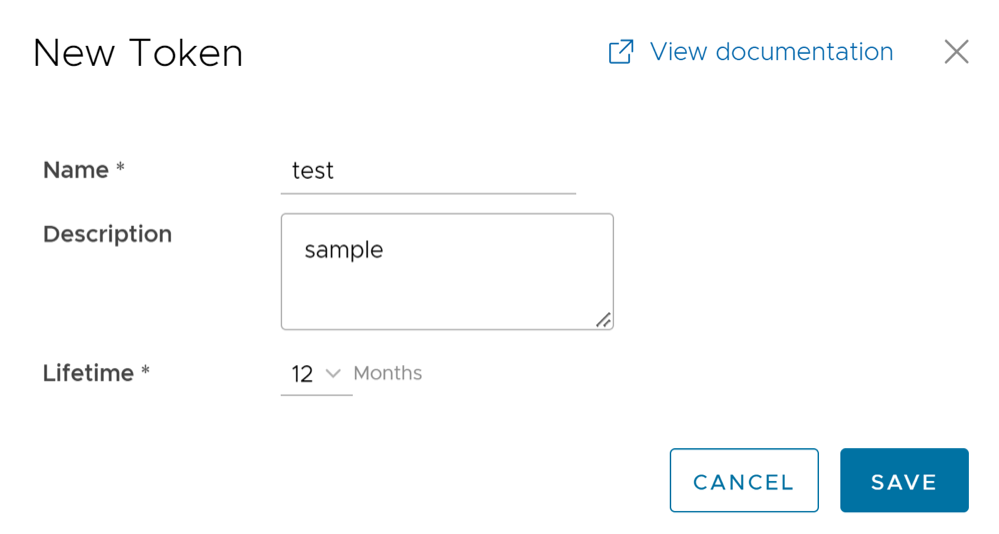
API Tokens
Any user can create tokens based on the privileges they have been assigned to their user roles, except the Business Specialist users.
- Enterprise users can Create, Download, and Revoke tokens for them.
- Partner Super users can manage tokens of Enterprise users, if the Enterprise user has delegated user permissions to the Partner.
- Partner Super users can only create and revoke the tokens for other users.
- Users can download only their own tokens and cannot download other users' tokens.
To manage the API tokens:
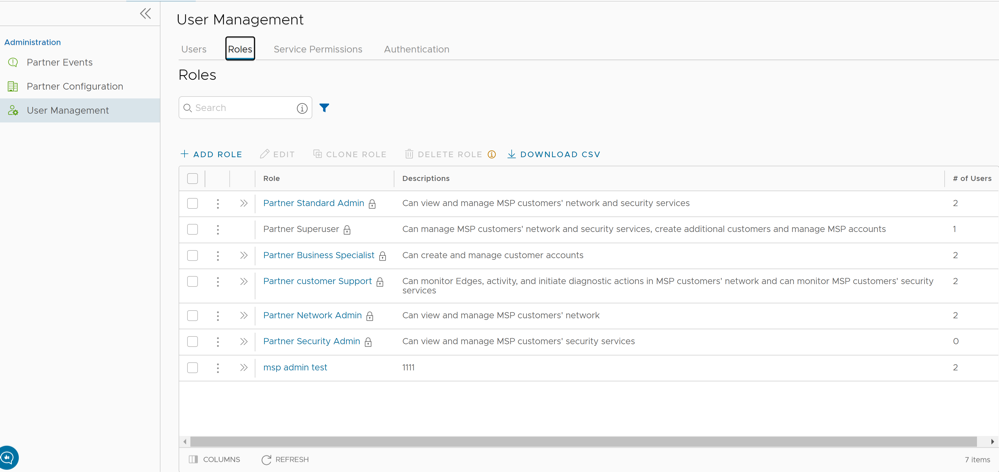
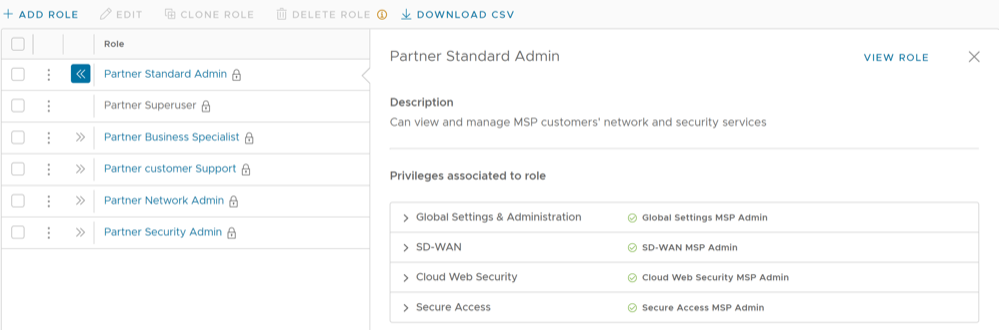
Roles
- Privileges – Privileges are a set of roles relevant to a service. A privilege can be tagged to the following services: SD-WAN and Global Settings. Users require privileges to carry out business processes. For example, a Customer support role in SD-WAN is a privilege required by an SD-WAN user to carry out various support activities. Every service defines such privileges based on its supported business functionality.
- Roles – The privileges from various categories can be grouped to form a role. By default, the following roles are available for a Partner administrator:
Table 5. Partner User Roles Role SD-WAN Service Global Settings Service Partner Standard Admin SD-WAN Partner Admin Global Settings Partner Admin Partner Security Admin SD-WAN Security Partner Admin Global Settings Partner Admin Partner Network Admin SD-WAN Partner Admin Global Settings Partner Admin Partner Superuser Full Access Full Access Partner Business Specialist SD-WAN Partner Business Global Settings Partner Business Partner Customer Support SD-WAN Partner Support Global Settings Partner Support If required, you can customize the privileges of these roles. For additional information, see Service Permissions.
As a Partner, you can view the list of existing roles and their corresponding descriptions. You can add a new role, clone an existing role, edit or delete a custom role. You cannot edit or delete a default role.
To access the Roles tab:
Add Role
To add a new role for a Partner, perform the following steps:
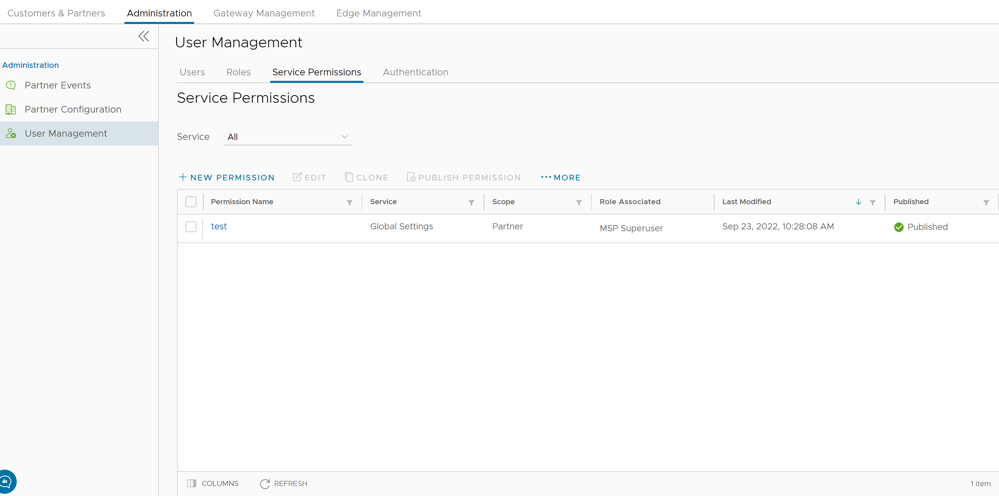
Service Permissions
- Starting from the 5.1.0 release, Role Customization is renamed as Service Permissions.
- Only an Operator Superuser can activate Role Customization for a Partner Superuser. If the Role Customization option is not available for you, contact your Operator.
When you customize a Service Permission, the changes impact the roles associated with it. For additional information, see the topic Roles.
- The customizations done at the Enterprise level override the Partner or Operator level customizations.
- The customizations done at the Partner level override the Operator level customizations.
- Only when there are no customizations done at the Partner level or Enterprise level, the customizations made by the Operator are applied globally across all users in the Orchestrator.
To access the Service Permissions tab:
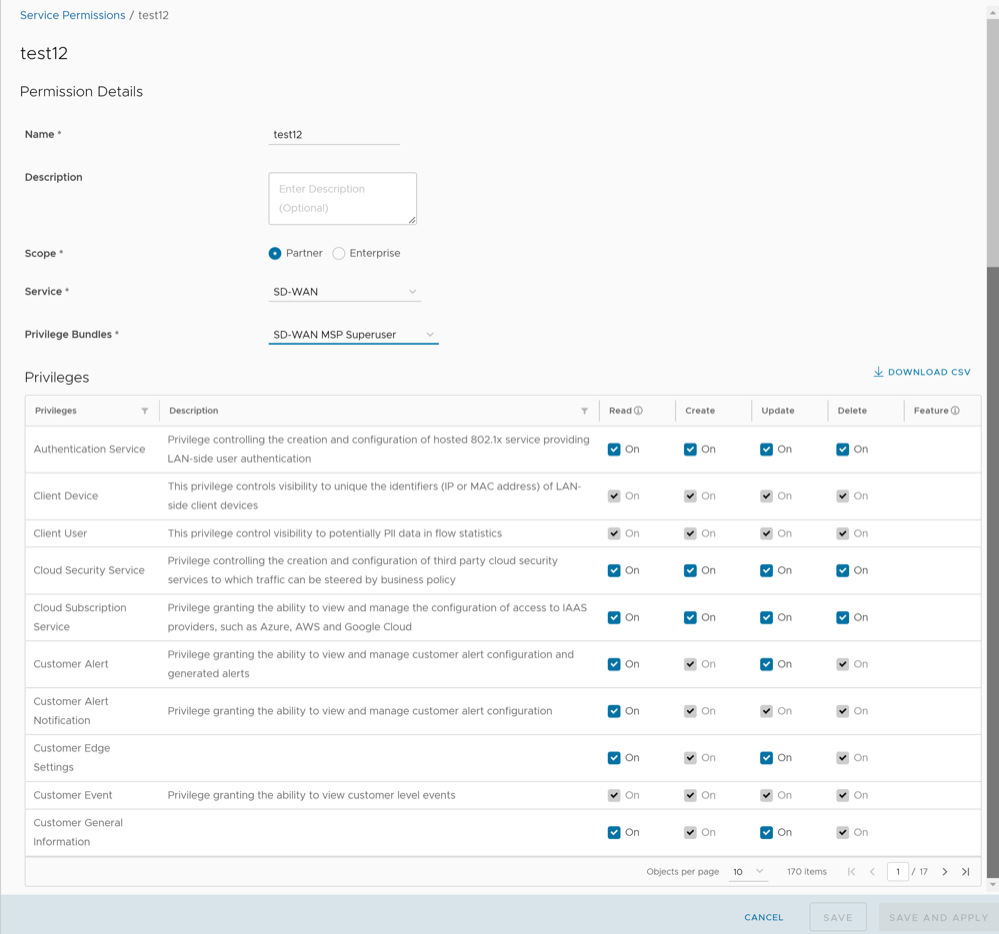
New Permission
To add a new permission, perform the following steps:
List of User Privileges
This section lists all the role privileges available in the Partner portal of the Orchestrator.
- Allow Privilege – Do the privileges have allow access?
- Deny Privilege – Do the privileges have deny access?
- Customizable – Is the privilege available for customization in the Service Permissions tab?
| Feature | Name of the Privilege | Description | Allow Privilege | Deny Privilege | Customizable |
|---|---|---|---|---|---|
| Manage Customers | Create Customer | Grants ability to view and manage Customers, from the Partner or Operator level | Yes | No | No |
| Read Customer | |||||
| Update Customer | Yes | Yes | |||
| Delete Customer | No | No | |||
| Manage Customer | |||||
| Partner Events | Create Partner Event | Grants access to view Partner events | Yes | No | No |
| Read Partner Event | Yes | Yes | |||
| Update Partner Event | No | No | |||
| Delete Partner Event | |||||
| Manage Partner Event | |||||
| Partner Admins | Create Partner User | Grants access to view and configure Partner administrators | Yes | No | No |
| Read Partner User | Yes | Yes | |||
| Update Partner User | No | No | |||
| Delete Partner User | |||||
| Manage Partner User | |||||
| Create Partner Token | Grants ability to view and manage operator authentication tokens | Yes | No | No | |
| Read Partner Token | |||||
| Update Partner Token | |||||
| Delete Partner Token | |||||
| Manage Partner Token | |||||
| Service Permissions | Create Service Permissions Package | Grants access to manage Service Permissions packages | Yes | No | No |
| Read Service Permissions Package | |||||
| Update Service Permissions Package | |||||
| Delete Service Permissions Package | |||||
| Manage Service Permissions Package | |||||
| Partner Overview | Update Partner | Grants access to view and Partners | Yes | No | No |
| Read User Agreement | Grants access to configure the customer user agreement feature | Yes | No | No | |
| Update User Agreement | |||||
| Partner Settings | Read Partner Delegation | Grants ability to view and edit the delegation of Partner privileges to the Operator | Yes | No | No |
| Read Customer Delegation | Grants ability to view and manage the delegation of privileges from the customer to Partners or the Operator | Yes | Yes | Yes | |
| Update Customer Delegation | No | ||||
| Create Partner Authentication | Grants ability to view and edit Partner authentication mode and associated configuration | Yes | No | No | |
| Read Partner Authentication | |||||
| Update Partner Authentication | |||||
| Delete Partner Authentication | |||||
| Manage Partner Authentication | |||||
| Create Partner Token | Grants ability to view and manage operator authentication tokens | Yes | No | No | |
| Read Partner Token | |||||
| Update Partner Token | |||||
| Delete Partner Token | |||||
| Manage Partner Token | |||||
| Edge Licensing | Create License | Grants ability to view and manage Edge licensing | Yes | No | No |
| Read License | Yes | Yes | |||
| Update License | |||||
| Delete License | No | No | |||
| Manage License | |||||
| Gateway Pools Gateways Gateway Diagnostic bundles | Create Gateway | Grants ability to view and manage Gateways, from the Partner or Operator level | Yes | Yes | Yes |
| Read Gateway | |||||
| Update Gateway | |||||
| Delete Gateway | |||||
| Manage Gateway | |||||
| View Tab Gateway List | Grants ability to view the Gateway list tab | No | Yes | Yes | |
| Download Gateway Diagnostics | Grants ability to download Gateway Diagnostics | No | Yes | Yes | |
| VeloCloud Support Access Role | Create Partner Delegation | Grants ability to view and edit the delegation of Partner privileges to the Operator | Yes | No | No |
| Read Partner Delegation | |||||
| Update Partner Delegation | |||||
| Delete Partner Delegation | |||||
| Manage Partner Delegation |
When the corresponding user privilege is denied, the Orchestrator window displays the 404 resource not found error.
| Navigation Path in the Enterprise Portal | Name of the Tab | Name of the Privilege | Description |
|---|---|---|---|
| Overview | Assign Edge Profile | Grants ability to assign a Profile to Edges | |
| Firewall | Configure Edge Firewall Logging | Grants ability to configure Edge level firewall logging | |
| Firewall | Configure Profile Firewall Logging | Grants ability to configure Profile level firewall logging | |
| Deactivate Edge | Grants ability to reset the device configuration to its factory default state | ||
| Enforce PCI Compliance | Deny PCI Operations | Denies access to sensitive Customer data including PCAPs, etc. on the Edges and Gateways, for all users including Arista Support | |
| Download Edge Diagnostics | Grants ability to download Edge Diagnostics | ||
| Download Gateway Diagnostics | Grants ability to download Gateway Diagnostics | ||
| Duplicate | Duplicate Customer Profile | Grants ability to edit duplicate customer level Profiles | |
| Segments drop-down menu | Edit Tab Segments | Grants ability to edit within the Segments tab | |
| Device | Enable HA Cluster | Grants ability to configure HA Clustering | |
| Device | Enable HA Active/Standby Pair | Grants ability to configure active/standby HA | |
| Device | Enable HA VRRP Pair | Grants ability to configure VRRP HA | |
| Clear ARP Cache | Remote Clear ARP Cache | Grants ability to clear the ARP cache for a given interface | |
| Cloud Traffic Routing (drop-down menu) | Remote Cloud Traffic Routing | Grants ability to route cloud traffic remotely | |
| DNS/DHCP Service Restart | Remote DNS/DHCP Restart | Grants ability to restart the DNS/DHCP service | |
| Flush Flows | Remote Flush Flows | Grants ability to flush the Flow table, causing user traffic to be re-classified | |
| Flush NAT | Remote Flush NAT | Grants ability to flush the NAT table | |
| LTE Switch SIM Slot
Note: This is for 610-LTE devices only.
|
Remote LTE Switch SIM Slot | Grants ability to activate the SIM Switchover feature. After the test is successful, you can check the status from Monitor > Edges > Overview tab | |
| List Paths | Remote List Paths | Grants ability to view the list of active paths between local WAN links and each peer | |
| List current IKE Child SAs | Remote List current IKE Child SAs | Grants ability to use filters to view the exact Child SAs you want to see | |
| List current IKE SAs | Remote List Current IKE SAs | Grants ability to use filters to view the exact SAs you want to see | |
| MIBs for Edge | Remote MIBS for Edge | Grants ability to dump Edge MIBs | |
| NAT Table Dump | Remote NAT Table Dump | Grants ability to view the contents of the NAT table | |
| Remote Rebalance Hub Cluster | Grants ability to either redistribute Spokes in Hub Cluster or redistribute Spokes excluding this Hub | ||
| Remote Reset SFP Firmware Configuration | Grants ability to reset the SFP Firmware Configuration | ||
| Reset USB Modem | Remote Reset USB Modem | Grants ability to execute the Edge USB modem reset remote action | |
| Scan for Wi-Fi Access Points | Remote Scan for Wi-Fi Access Points | Grants ability to scan the Wi-Fi functionality for the SD-WAN Edge | |
| System Information | Remote System Information | Grants ability to view system information such as system load, recent WAN stability statistics, monitoring services | |
| VPN Test | Remote VPN Test | Grants ability to execute the Edge VPN test remote action | |
| WAN Link Bandwidth Test | Remote WAN link Bandwidth Test | Grants ability to re-test the bandwidth of a WAN link | |
| Shutdown Edge | Grants ability to execute the Edge shutdown remote action | ||
| Update Customer SMS Alert | Grants ability to configure SMS alerts at the customer level | ||
| Top Sources | View Edge Sources | Grants ability to view Monitor Edge Sources tab | |
| Firewall Logging | View Firewall Logs | Grants ability to view collected firewall logs | |
| Top Sources | View Flow Stats | Grants ability to view collected flow statistics | |
| Monitor Firewall Logs | Firewall Logs | View Profile Firewall Logging | Grants ability to view the details of firewall logs originating from Edges |
| Firewall | View Stateful Firewall | Grants ability to view collected flow statistics | |
| View Syslog Forwarding | Grants ability to view logs that are forwarded to a configured syslog collector | ||
| Gateways | View Tab Gateway List | Grants ability to view the Gateway list tab | |
| Operator Profiles | View Tab Operator Profile | Grants ability to view and configure settings within the Operator Profile menu tab | |
| Top Sources | View User Identifiable Flow Stats | Grants ability to view potentially user identifiable flow source attributes |
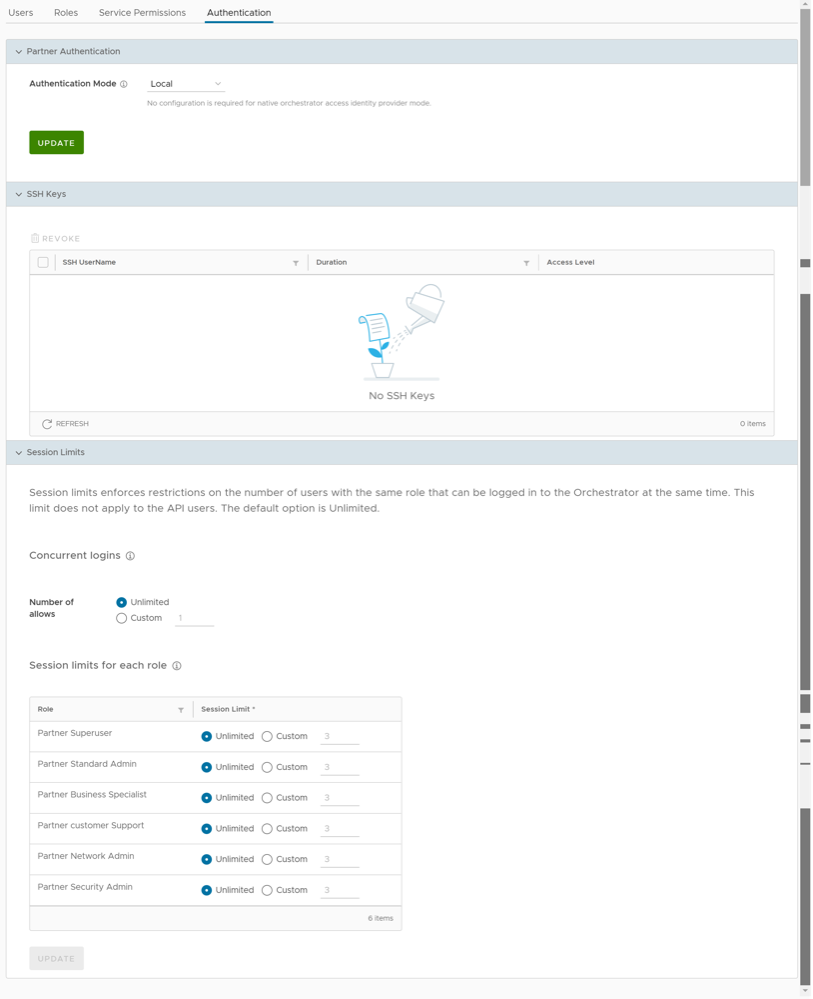
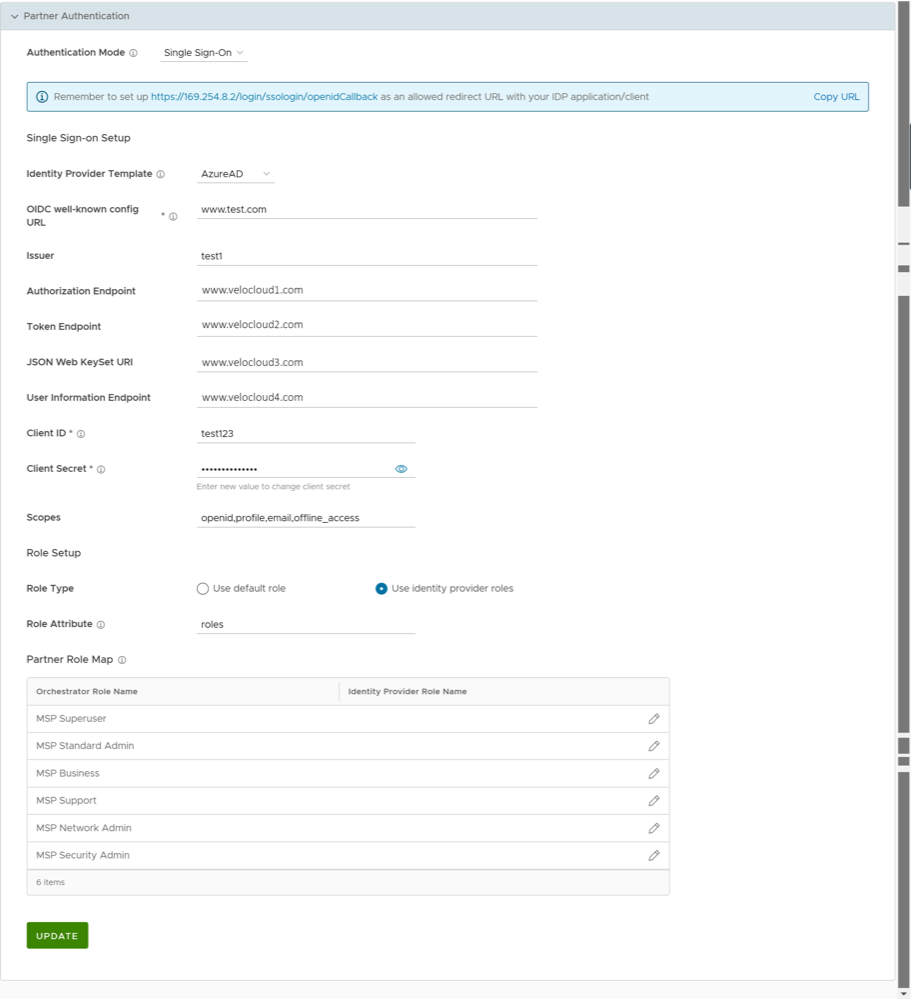
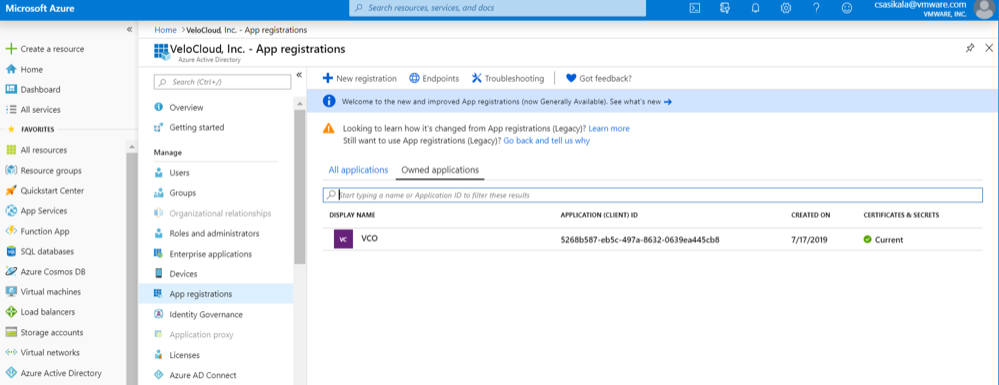
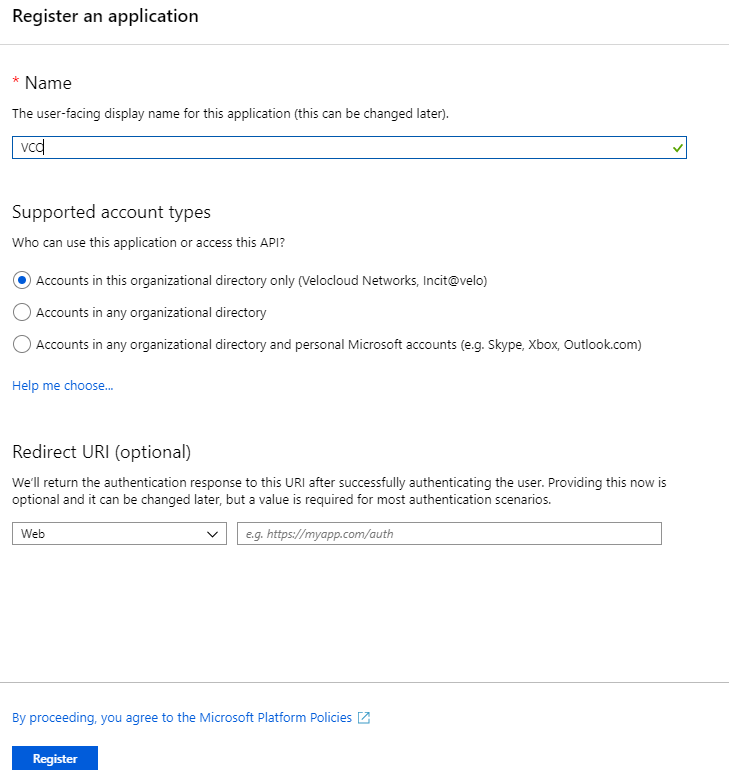
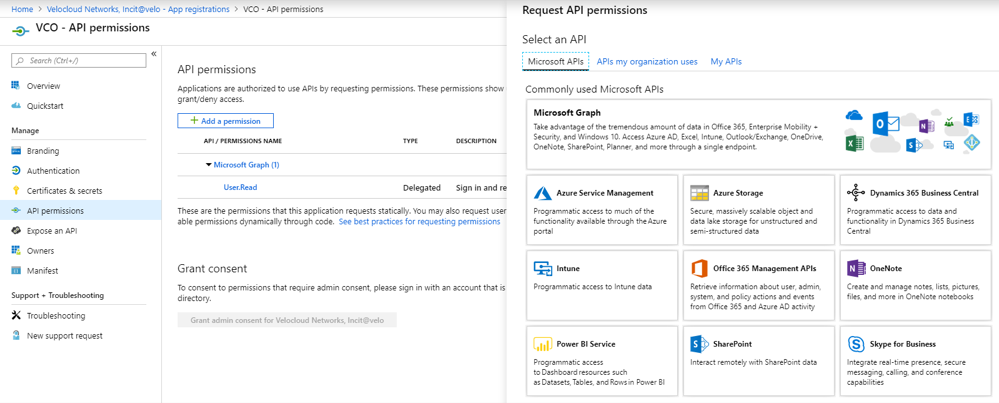
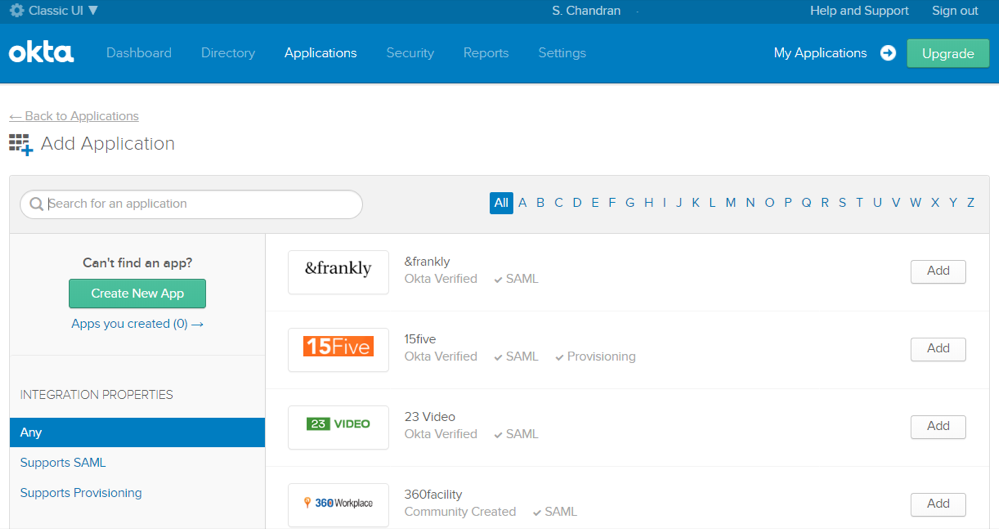
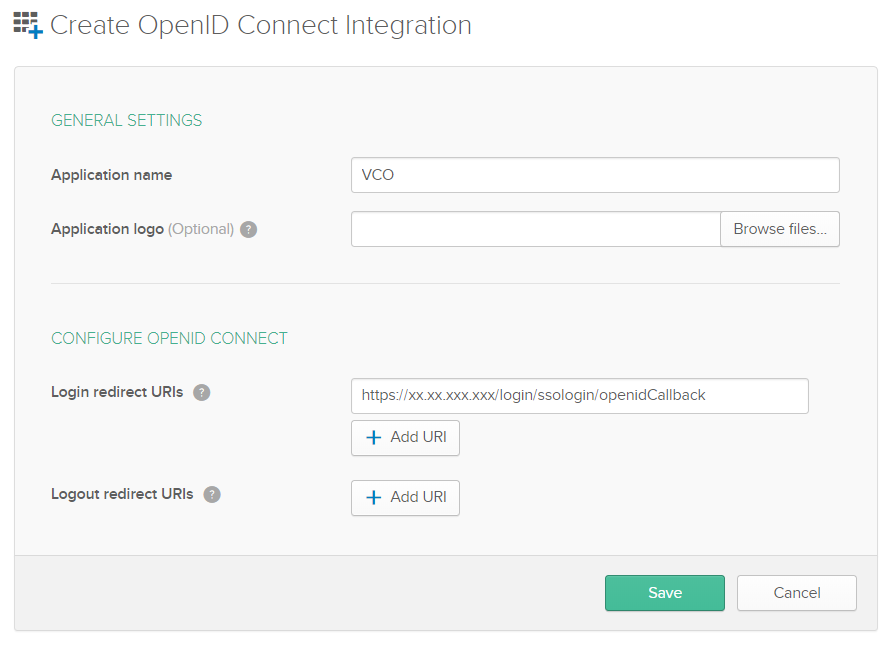
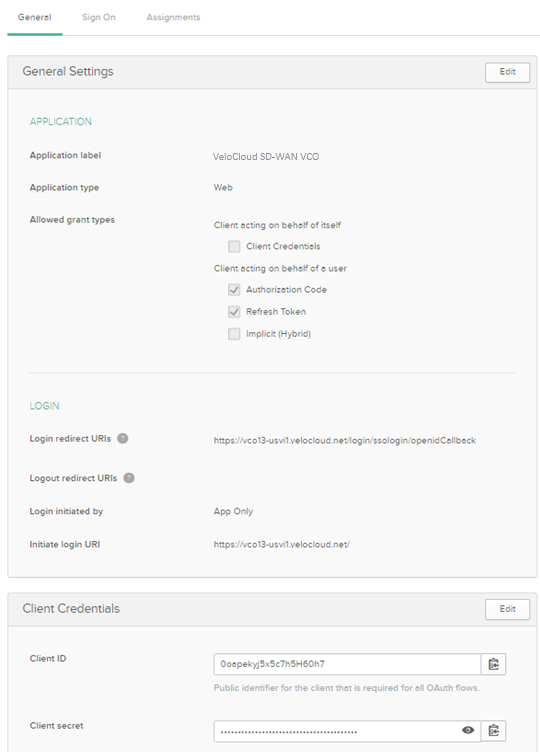
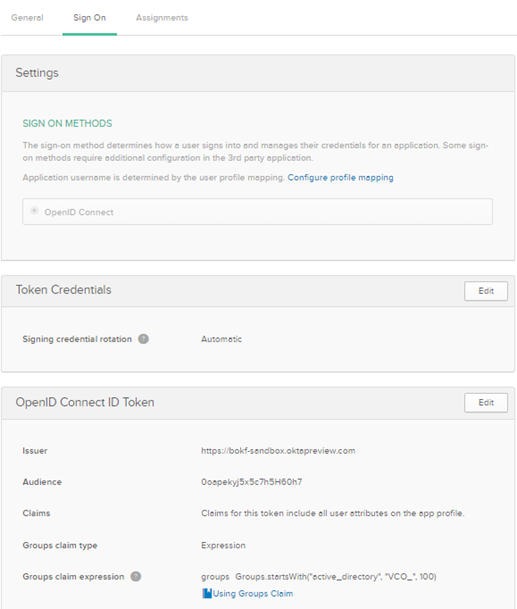
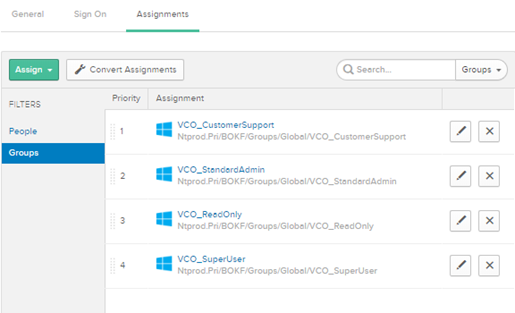
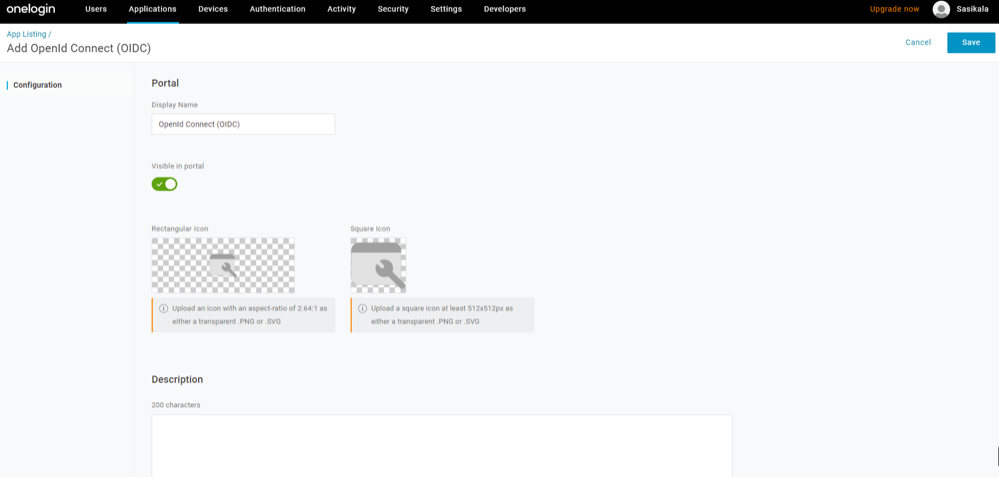
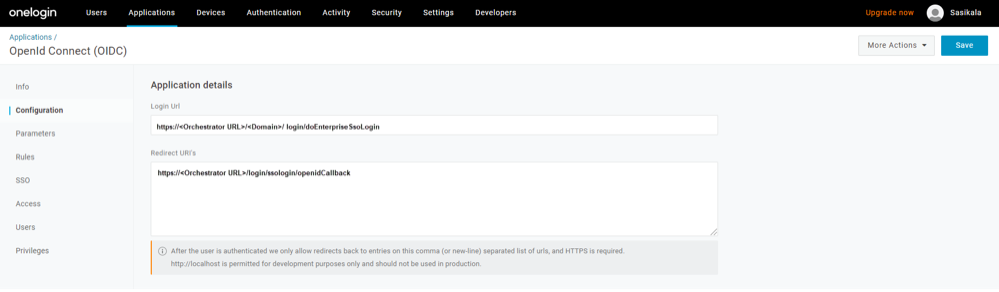
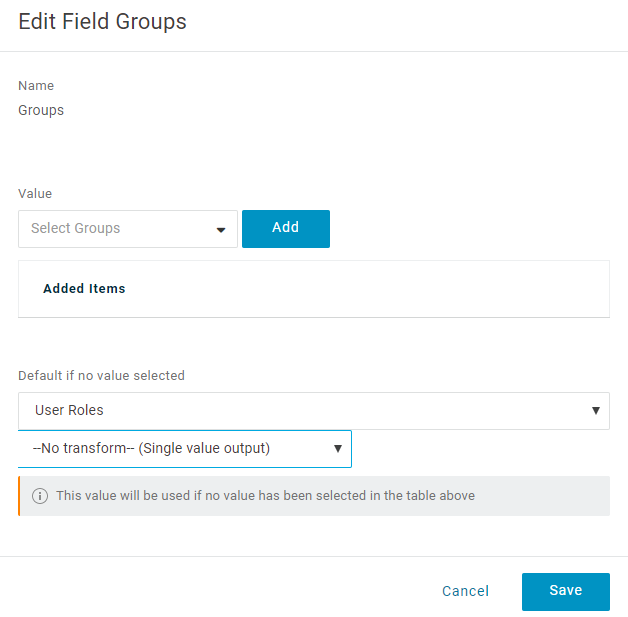
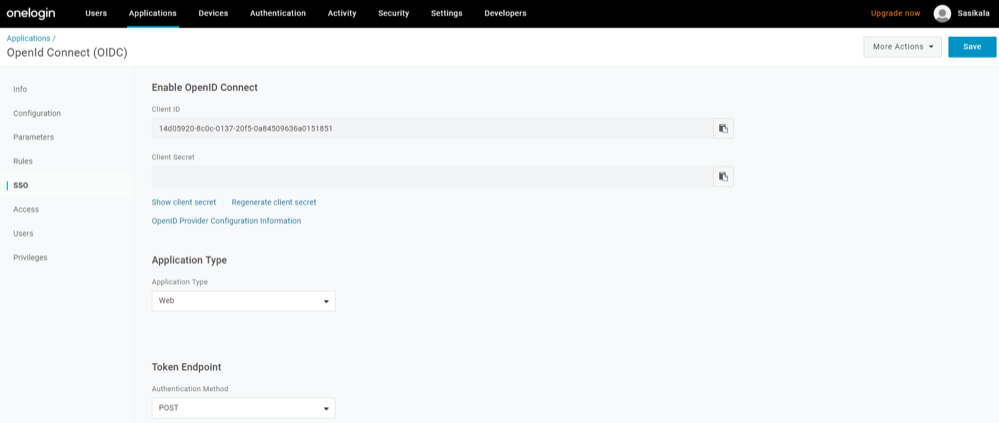
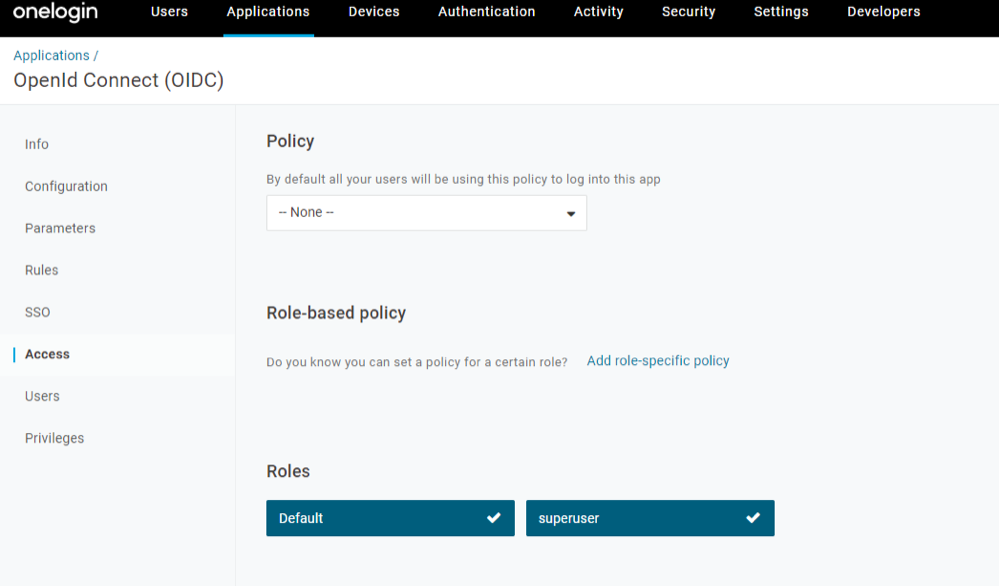
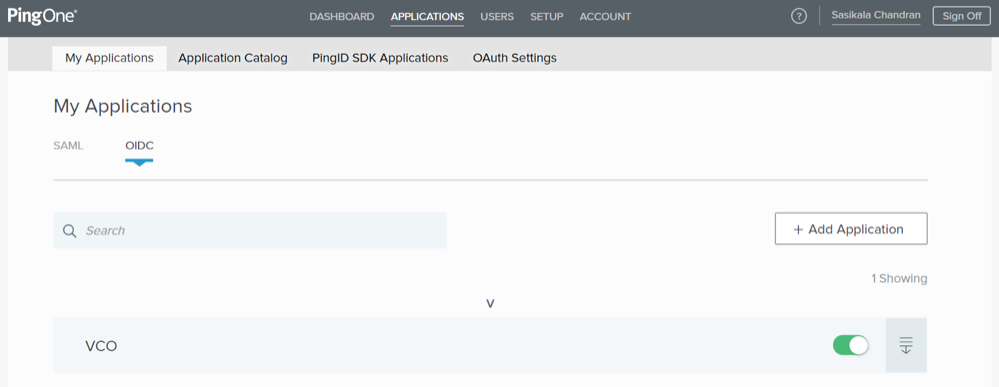
Authentication
To access the Authentication tab: