Integrate VeloCloud SD-WAN with Microsoft Route Server
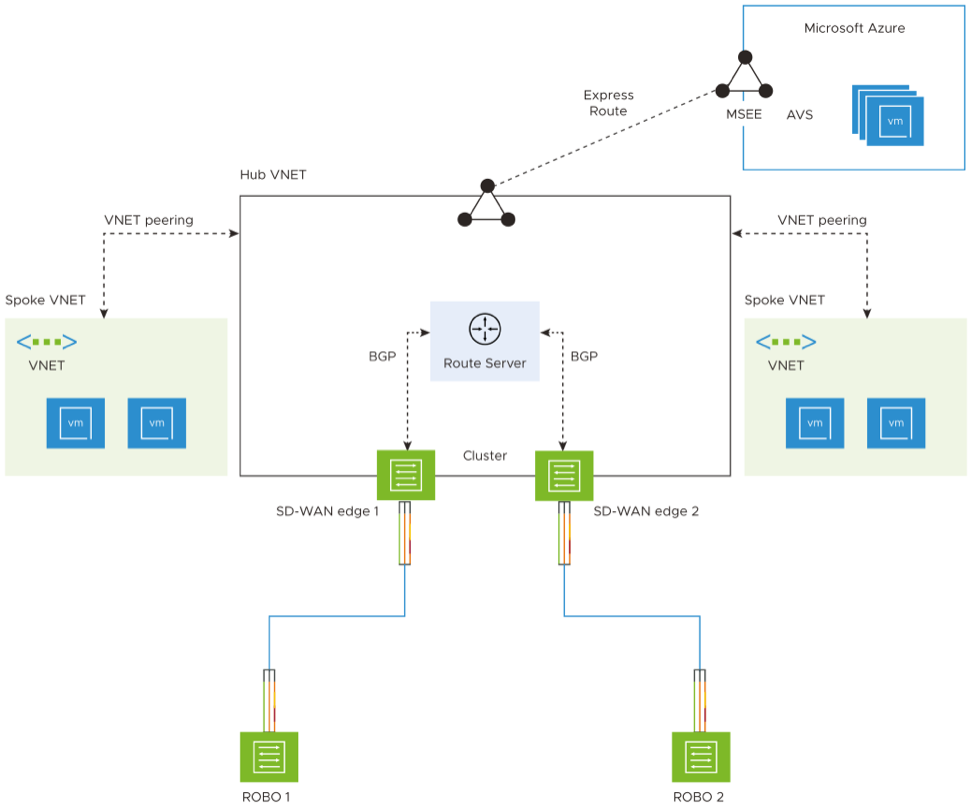
You can integrate VeloCloud SD-WAN with Microsoft Route Server for the Establish Branch-to-Cloud Connectivity and Establish Branch-to-AVS Connectivity use cases.
Prerequisites
- Obtain Enterprise account access to VeloCloud Orchestrator.
- On the VeloCloud Edges, run software version 4.2.0 or newer.
- Obtain access to the Microsoft Azure portal with the appropriate IAM roles.
Establish Connectivity
- Deploy a 2-member cluster in a region.
- Deploy the Route Server.
- Connect on-premises either to Microsoft Azure resources and/or to Azure VeloCloud Solutions (AVS)
Establish Branch-to-Cloud Connectivity
This section describes the steps to integrate VeloCloud SD-WAN with Microsoft Route Server for the Establish Branch-to-Cloud Connectivity use case.
The following figure illustrates the branch-to-cloud connectivity.
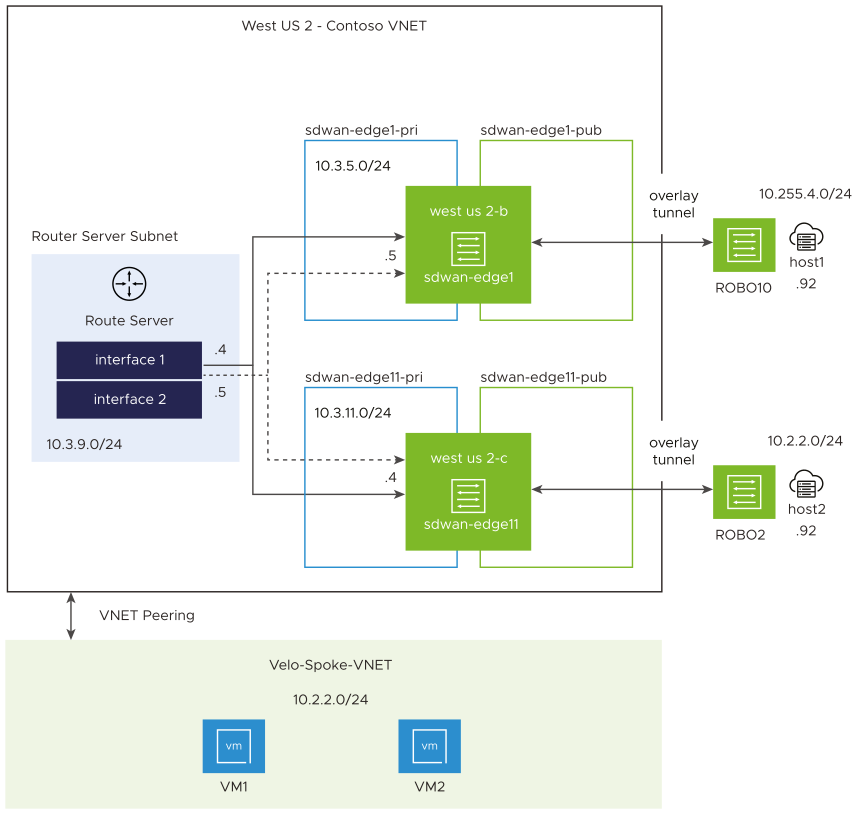
To create Edge instances and Route Server and to establish branch-to-cloud connectivity, perform the following tasks:
Run a ping test to verify the connection between the ROBO Edge instance and VM1 or VM2.
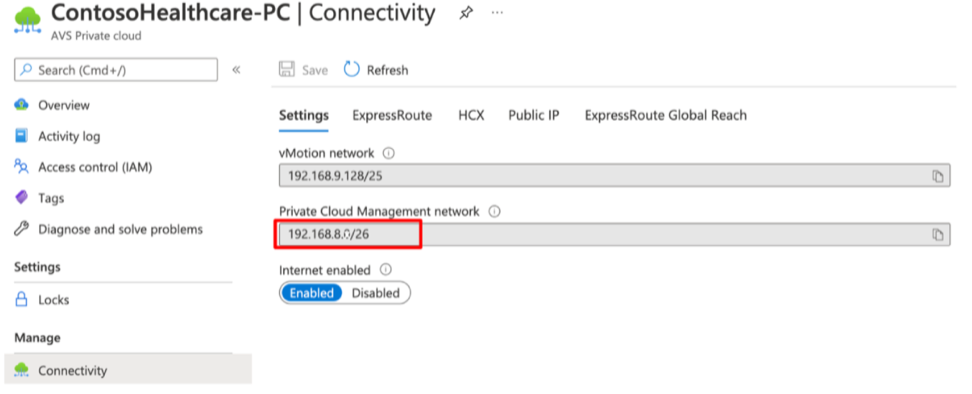
Establish Branch-to-AVS Connectivity
This section describes the steps to integrate VeloCloud SD-WAN with Microsoft Route Server for the Establish Branch-to-AVS Connectivity use case.
Azure VeloCloud Solution (AVS) enables enterprises to set up private clouds in Azure. The private cloud contains Arista’s software defined datacenter clusters, built from dedicated bare-metal infrastructure from Azure. All private clouds are provisioned with vCenter Server, vSphere, vSAN, and NSX-T. Organizations can migrate workloads from on-premises environments, create or deploy new virtual machines, and consume Azure services from private clouds using the familiar Arista tools.
Complete the following tasks to establish branch-to-AVS connectivity:
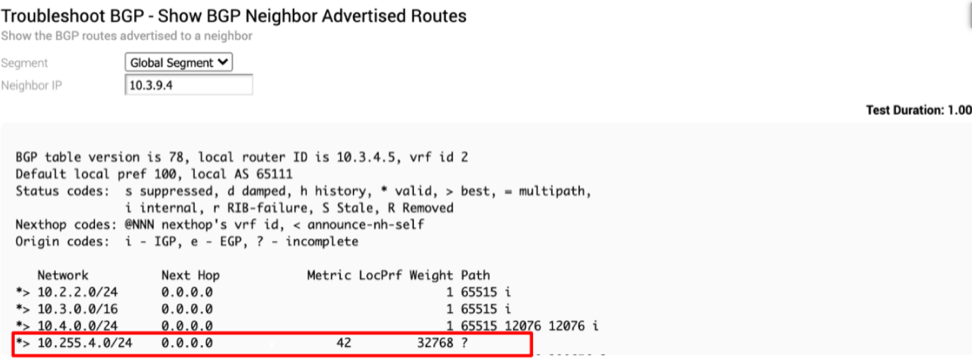
Run a ping test to verify the connection between the on-prem Edge instance, host1 and your workloads that reside in AVS.