Cloud Security Services
Cloud Security Service (CSS) is a cloud-hosted security that protects an Enterprise branch and/or data center. The security services include firewalls, URL filtering, and other such services.
In CSS, you can define and configure a cloud security service instance and establish a secure tunnel directly from the Edge to the CSS.
- Simplified configuration.
- Saves link bandwidth costs by offloading non-enterprise traffic to the internet.
- The branch sites are protected from malicious traffic by redirecting the Internet traffic to a cloud security service.
Configure a Cloud Security Service
The Cloud Security Service (CSS) establishes a secure tunnel from an Edge to the cloud security service sites. This ensures secured traffic flow to the cloud security services.
- In the SD-WAN service of the Enterprise portal, select .
- In the Network Services page, navigate to , select New.
Figure 1. Configuring a New Cloud Security Service 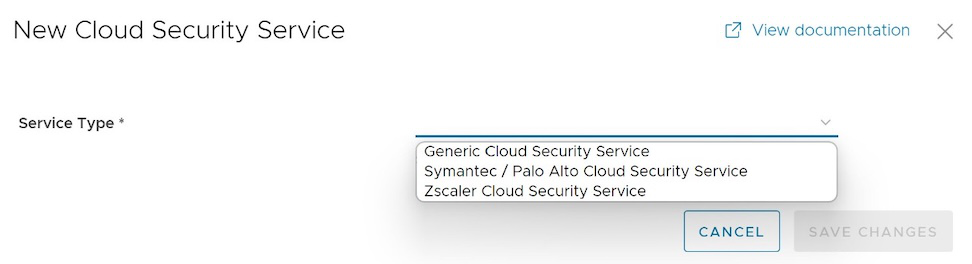
- In the New Cloud Security Provider window, select a service type from the menu. VeloCloud SD-WAN supports the following CSS types:
- Generic Cloud Security Service
- Symantec / Palo Alto Cloud Security Service
Note: Starting from 5.0.0 release, Palo Alto CSS are configured under the new service type template Symantec / Palo Alto Cloud Security Service. All customers who have an existing Palo Alto CSS configured under Generic Cloud Security Service must move to the new template Symantec / Palo Alto Cloud Security Service.
- Zscaler Cloud Security Service
- If you have selected either Generic or Symantec / Palo Alto Cloud Security Service as the Service Type, then configure the following required details and select Add.
Table 1. Security Options Option Description Service Name Enter a descriptive name for the cloud security service. Primary Point-of-Presence/Server Enter the IP address or hostname for the Primary server. Secondary Point-of-Presence/Server Enter the IP address or hostname for the Secondary server. This is optional. - If you have selected Zscaler Cloud Security Service as the Service Type, then you can choose between manual deployment and automated deployment by selecting the Automate Cloud Service Deployment checkbox. Also, you can configure additional settings such as Zscaler Cloud and Layer 7 (L7) Health Check details to determine and monitor the health of the Zscaler Server.
This section discusses how to automatically create a GRE or IPsec tunnel from SD-WAN Edge to Zscaler service provider.Configure Manual Tunnels from SD-WAN Edge to ZscalerFigure 2. Configuring Automatic Tunnels 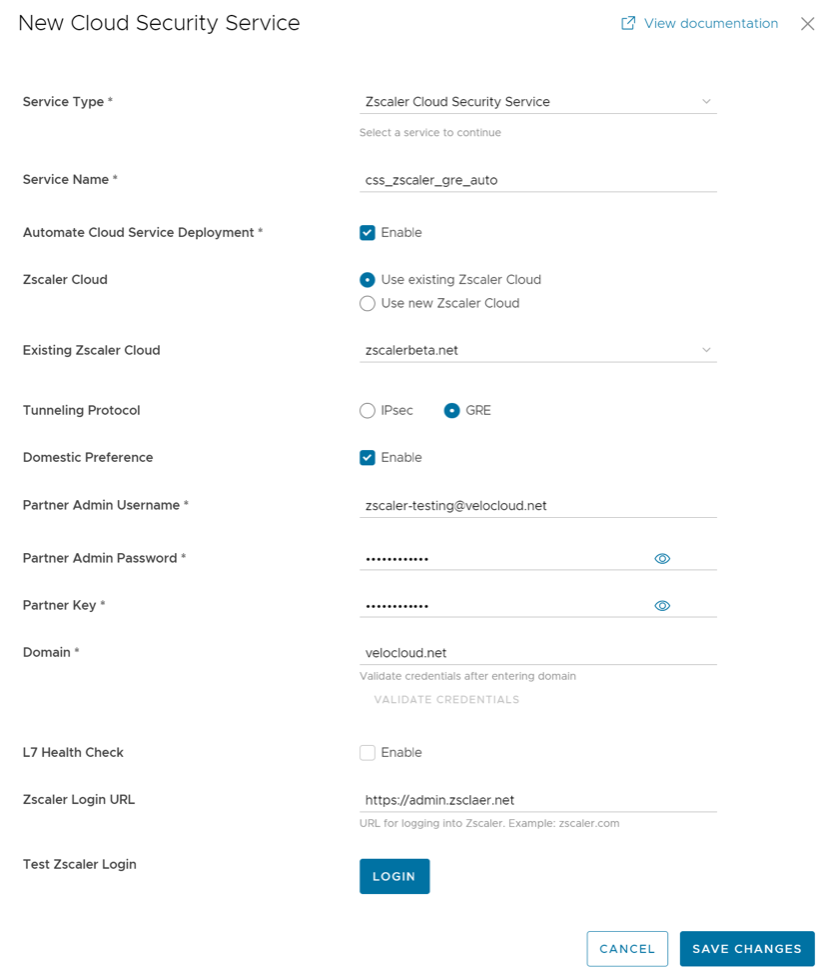
- In the New Cloud Security Provider window, enter a service name.
- Select the Automate Cloud Service Deployment checkbox.
- Select GRE or IPsec protocol for tunnel establishment.
Note: The total number of CSS Zscaler GRE tunnels that can be configured per customer depends on the customer's subscription on Zscaler. The default value is 100.
- Configure additional details such as Domestic Preference, Zscaler Cloud, Partner Admin Username, Password, Partner Key, and Domain, as described in the following table.
Table 2. Additional Configuration Parameters Option Description Domestic Preference Enable this option to prioritize Zscaler data centers from the country of origin of the IP address even if they are farther away from the other Zscaler data centers. Note: Previously, the Domestic Preference option was only available for GRE tunnels. Starting with the 6.0.0 release, this option is configurable for establishing IPsec tunnels as well.Zscaler Cloud You can choose to use the existing Zscaler clouds or use a new Zscaler Cloud. If you choose to use the existing cloud then select a Zscaler cloud service from the drop-down menu. For new Zscaler cloud, you must enter the Zscaler cloud service name in the textbox. Partner Admin Username Enter the provisioned username of the partner admin. Partner Admin Password Enter the provisioned password of the partner admin. Note: Starting from the 4.5 release, the use of the special character "<" in the password is no longer supported. In cases where users have already used "<" in their passwords in previous releases, they must remove it to save any changes on the page.Partner Key Enter the provisioned partner key. Domain Enter the domain name on which the cloud service would be deployed. Sub Cloud This is an optional parameter that Zscaler Internet Access (ZIA) customers use to have a custom pool of data centers for Geo-location purposes. Note: This option is available on CSS Zscaler automated deployment mode, if IPsec is selected for establishing tunnels. - Select Validate Credentials. If the validation is successful, the Save Changes button will be activated.
Note: You must validate the credentials to add a new CSS Provider.
- Optional: Configure the following L7 Health Check details to monitor the health of the Zscaler Server.
Note: The L7 Health Check feature tests HTTP reachability to the Zscaler backend server. Upon enabling L7 Health Check, the Edge sends HTTP L7 probes to a Zscaler destination (Example: http://<zscaler cloud>/vpntest) which is Zscaler's backend server for the HTTP health check. This method is an improvement over using network level keep-alive (GRE or IPsec) as that method only tests for network reachability to the frontend of a Zscaler server.
If an L7 response is not received after 3 successive retries, or if there is an HTTP error, the Primary Tunnel will be marked as 'Down' and the Edge will attempt to failover Zscaler traffic to the Standby Tunnel (if one is available). If the Edge successfully fails over Zscaler traffic to the Standby Tunnel, the Standby becomes the new Primary Tunnel.
In the unlikely event that the L7 Health Check marks both the Primary and Standby tunnels as 'Down', the Edge would route Zscaler traffic using a Conditional Backhaul policy (if such a policy has been configured).
The Edge only sends L7 probes over the Primary Tunnel towards the Primary Server, never over the Standby Tunnel.
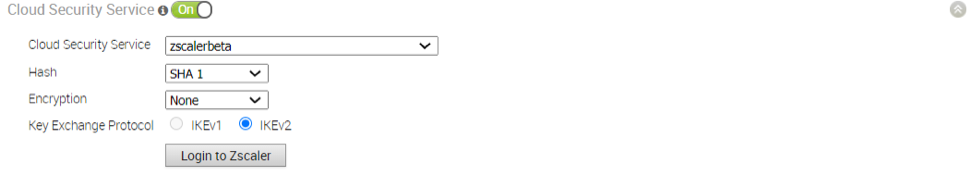
Table 3. L7 Configuration Options Option Description L7 Health Check Select the checkbox to enable L7 Health Check for the Zscaler Cloud Security Service provider, with default probe details (HTTP Probe interval = 5 seconds, Number of Retries = 3, RTT Threshold = 3000 milliseconds). By default, L7 Health Check is not enabled. Note: Configuration of health check probe details is not supported.Note: For a given Edge/Profile, a user cannot override the L7 health check parameters configured in the Network Service.HTTP Probe Interval The duration of the interval between individual HTTP probes. The default probe interval is 5 seconds. Number of Retries Specifies the number of probes retries allowed before marking the cloud service as DOWN. The default value is 3. RTT Threshold The round trip time (RTT) threshold, expressed in milliseconds, used to calculate the cloud service status. The cloud service is marked as DOWN if the measured RTT is above the configured threshold. The default value is 3000 milliseconds. Zscaler Login URL Enter the login URL and then select Login to Zscaler. This will redirect you to the Zscaler Admin portal of the selected Zscaler cloud. Note: The Login to Zscaler button will be enabled if you have entered the Zscaler login URL. - If you want to login to the Zscaler Admin portal from the Orchestrator, enter the Zscaler login URL and then select Login to Zscaler. This will redirect you to the Zscaler Admin portal of the selected Zscaler cloud.
Note: The Login to Zscaler button will be enabled if you have entered the Zscaler login URL.
Note: For additional information about Zscaler CSS automated deployment, see Zscaler and VeloCloud SD-WAN Deployment Guide.Note: For specific details on how Zscaler determines the best data center Virtual IP addresses (VIPs) to use for establishing IPsec VPN tunnels, see SD-WAN API Integration for IPSec VPN Tunnel Provisioning.This section discusses how to manually create a GRE or IPsec tunnel from an SD-WAN Edge to a Zscaler service provider. Unlike automatic tunnels, configuring manual tunnels requires you to specify a tunnel destination to bring up the tunnels.Figure 3. Configuring Manual Tunnels 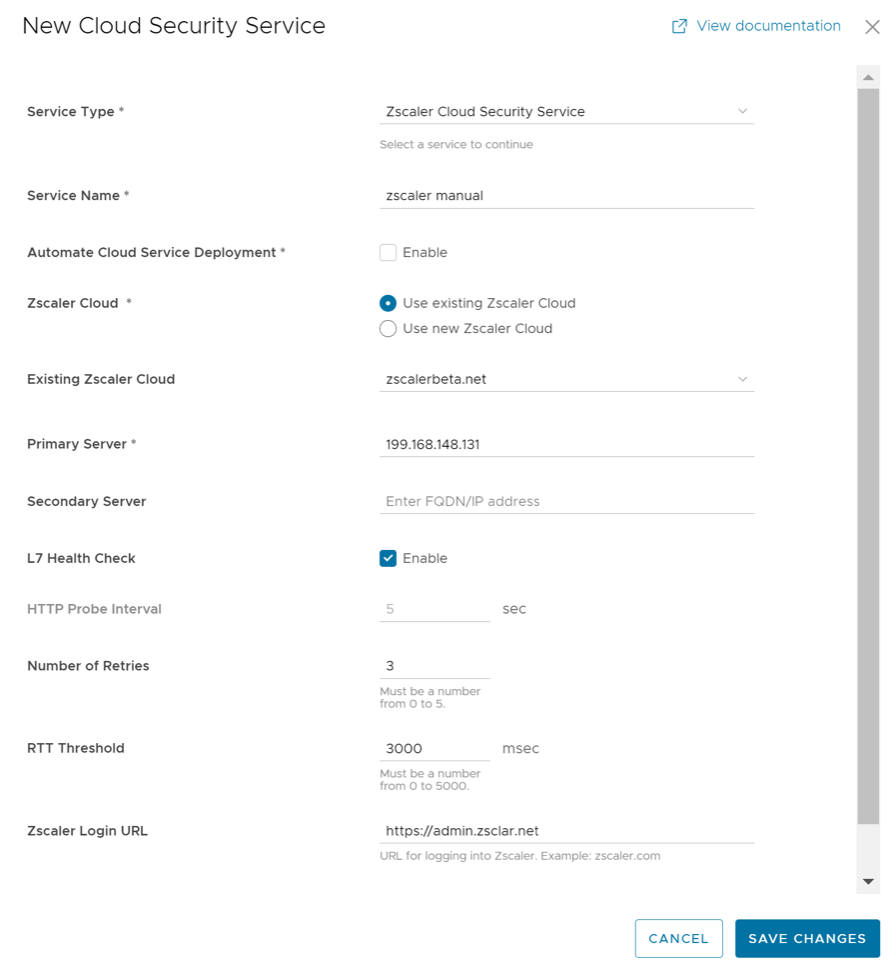
- In the New Cloud Security Provider window, enter a service name.
- Enter the IP address or hostname for the Primary server.
- Optionally, you can enter the IP address or hostname for the Secondary server.
- Select a Zscaler cloud service from the drop-down menu or enter the Zscaler cloud service name in the textbox.
- Configure other parameters as desired, and then select Save Changes.
Note: If you have selected Zscaler Cloud Security Service as the Service Type and planning to assign a GRE tunnel, it is recommended to enter only IP address in the Primary and Secondary server, and not the hostname, as GRE does not support hostnames.
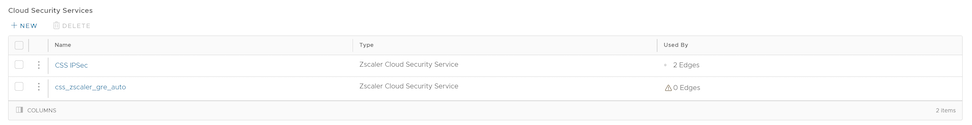
Configure Cloud Security Services for Profiles
Enable Cloud Security Service (CSS) to establish a secured tunnel from an Edge to cloud security service sites. This enables the secured traffic being redirected to third-party cloud security sites. At the Profile level, VeloCloud SD-WAN and Zscaler integration supports automation of IPsec and GRE tunnels.
- Ensure that you have access permission to configure network services.
- Ensure that your Orchestrator has version 3.3.x or above.
- You should have Cloud security service gateway endpoint IPs and FQDN credentials configured in the third party Cloud security service.
Configure Cloud Security Services for Edges
When you have assigned a profile to an Edge, the Edge automatically inherits the cloud security service (CSS) and attributes configured in the profile. You can override the settings to select a different cloud security provider or modify the attributes for each Edge.
To override the CSS configuration for a specific Edge, perform the following steps:
Manual Zscaler CSS Provider Configuration for Edges
At the Edge level, for a selected manual Zscaler CSS provider, you can override the settings inherited from the profile and can configure additional parameters manually based on the tunneling protocol selected for tunnel establishment.
If you choose to configure an IPsec tunnel manually, apart from the inherited attributes, you must configure a Fully Qualified Domain Name (FQDN) and Pre-Shared Key (PSK) for the IPsec session.
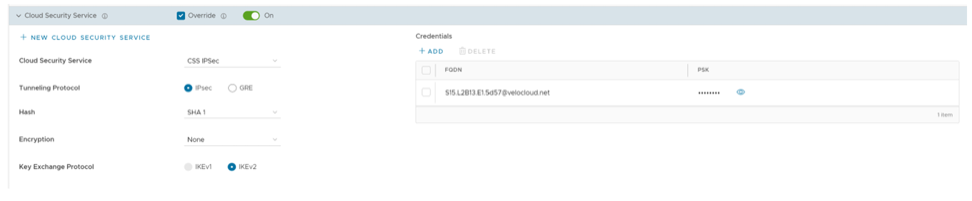
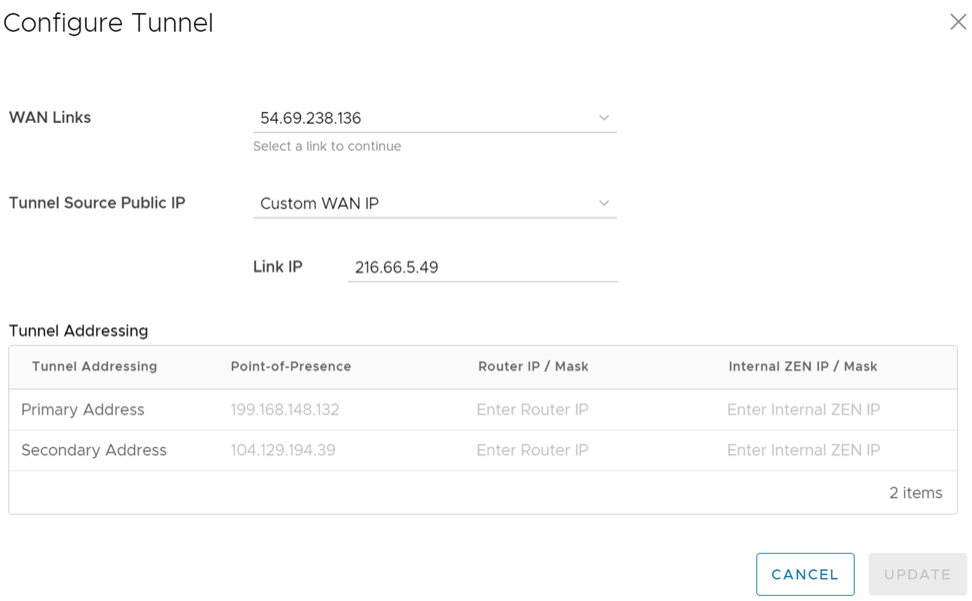
If you choose to configure a GRE tunnel manually, then you must configure GRE tunnel parameters manually for the selected WAN interface to be used as source by the GRE tunnel, by following the steps below.
Automated Zscaler CSS Provider Configuration for Edges
- IPsec/GRE Tunnel Automation
- Zscaler Location/Sub-Location Configuration
IPsec/GRE Tunnel Automation
IPsec/GRE tunnel automation can be configured for each Edge segment. Perform the following steps to establish automatic tunnels from an Edge.
Zscaler Location/Sub-Location Configuration
After you have established automatic IPsec/GRE tunnel for an Edge segment, Location is automatically created and appears under the Zscaler section of the Edge Device page.
- You check that the tunnel is established from the selected Edge and Location is automatically created. You will not be allowed to create a Sub-location if the VPN credentials or GRE options are not set up for the Edge. Before configuring Sub-locations, ensure you understand about Sub location and their limitations. See https://help.zscaler.com/zia/understanding-sublocations.
- You select the same Cloud Subscription that you used to create the Automatic CSS.
- In the SD-WAN service of the Enterprise portal, go to . The Edges page displays the existing Edges.
- Select an Edge and select the icon under the Device column. The Device Settings page for the selected Edge appears.
- Go to the Zscaler section and turn on the toggle button.
Figure 10. Override Zscaler Settings 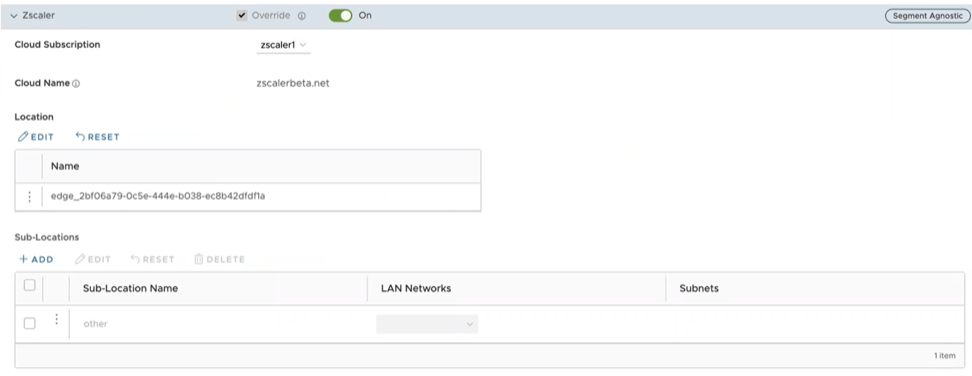
- From the Cloud Subscription drop-down menu, select the same Cloud Subscription that you used to create the Automatic CSS. The Cloud Name associated to the selected Cloud Subscription automatically appears.
Note:
- Cloud Subscription must have same Cloud name and Domain name as CSS.
- If you want to change provider for "Cloud Subscription", you must first remove the "Location" by deactivating CSS and Zscaler, and then perform the creation steps with the new provider.
In the Location table, selecting View under the Action Details column displays the actual values for the configuration fetched from Zscaler, if present. If you want to configure the Gateway options and Bandwidth controls for the Location, select the Edit button under Gateway Options. For additional information, see the section "Configure Zscaler Gateway Options and Bandwidth Control".
- To create a Sub-location, in the Sub-Locations table, select the '+' icon under the Action column.
- In the Sub-Location Name text box, enter a unique name for the Sub-location. The Sub location name should be unique across all segments for the Edge. The name can contain alphanumeric with a maximum word length of 32 characters.
- From the LAN Networks drop-down menu, select a VLAN configured for the Edge. The Subnet for the selected LAN network will be populated automatically.
Note: For a selected Edge, Sub-locations should not have overlapping Subnet IPs.
- Select Save Changes.
Figure 11. Create Sub-locations 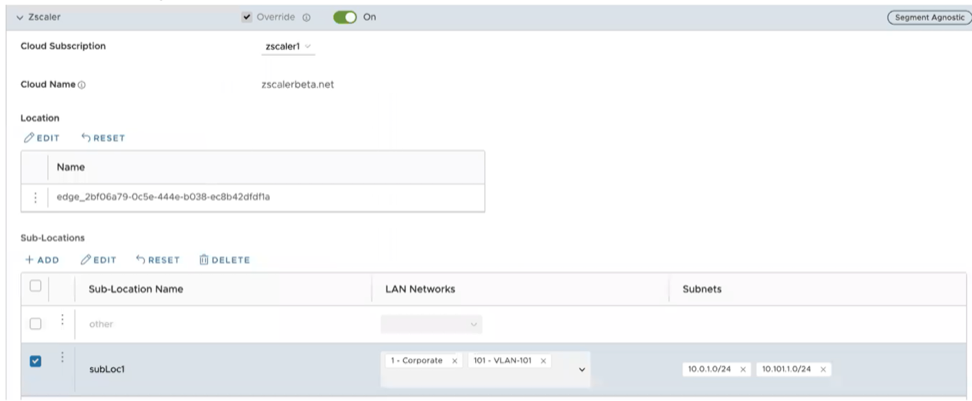 Note: After you create at least one Sub-location in the Orchestrator, an “Other” Sub location is automatically created in the Zscaler side, and it appears in the Orchestrator UI. You can also configure the “Other” Sub-location’s Gateway options by selecting the Edit button under Gateway Options in the Sub-Locations table. For additional information, see the section "Configure Zscaler Gateway Options and Bandwidth Control".
Note: After you create at least one Sub-location in the Orchestrator, an “Other” Sub location is automatically created in the Zscaler side, and it appears in the Orchestrator UI. You can also configure the “Other” Sub-location’s Gateway options by selecting the Edit button under Gateway Options in the Sub-Locations table. For additional information, see the section "Configure Zscaler Gateway Options and Bandwidth Control". - After creating a Sub-location, you can update the Sub-location configurations from the same Orchestrator page. Once you select Save Changes, the Sub-location configurations on the Zscaler side will be updated automatically.
- To delete a Sub-location, select the '-' icon under the Action column.
Note: When the last Sub-location is deleted from the table, the "other" Sub-location also gets deleted automatically.
Configure Zscaler Gateway Options and Bandwidth Control
To configure Gateway options and Bandwidth controls for the Location and Sub-location, select the Edit button under Gateway Options, in the respective table.
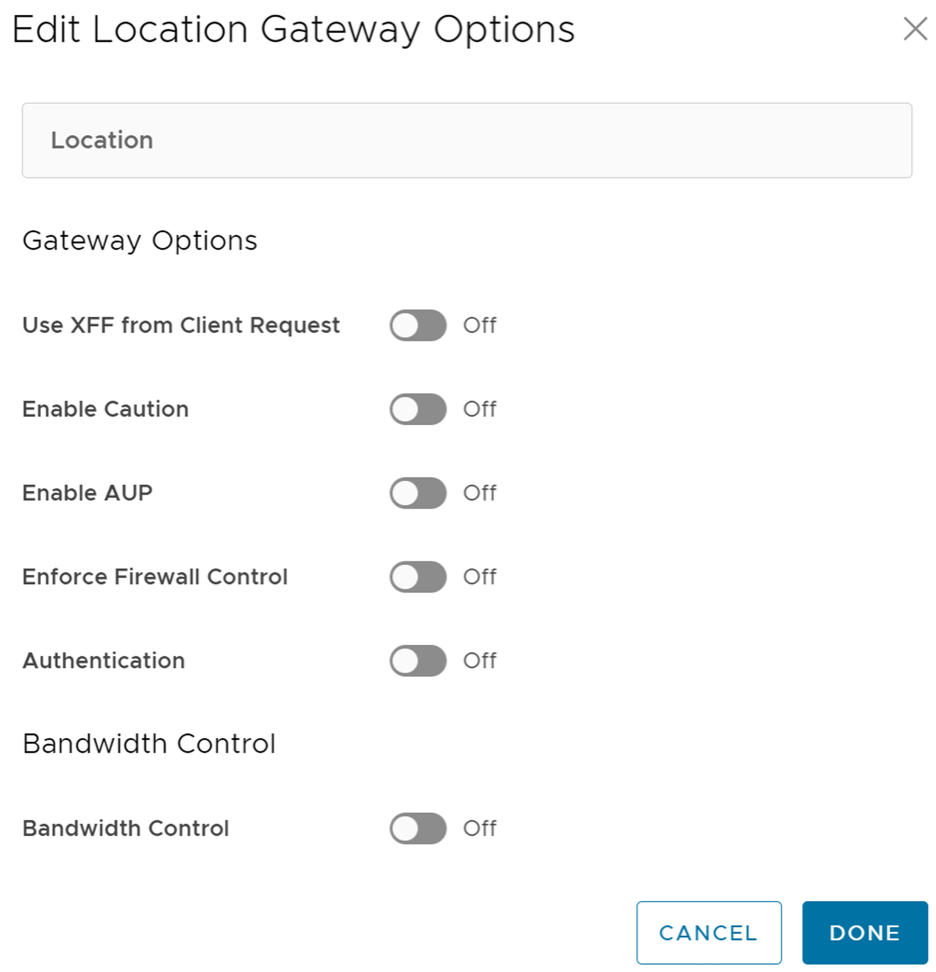
Configure the Gateway options and Bandwidth controls for the Location and Sub-location, as needed, and select Save Changes.
| Option | Description |
|---|---|
| Gateway Options for Location/Sub-Location | |
| Use XFF from Client Request | Enable this option if the location uses proxy chaining to forward traffic to the Zscaler service, and you want the service to discover the client IP address from the X-Forwarded-For (XFF) headers that your on premises proxy server inserts in outbound HTTP requests. The XFF header identifies the client IP address, which can be leveraged by the service to identify the client’s sub location. Using the XFF headers, the service can apply the appropriate sub location policy to the transaction, and if Enable IP Surrogate is turned on for the location or sub-location, the appropriate user policy is applied to the transaction. When the service forwards the traffic to its destination, it will remove the original XFF header and replace it with an XFF header that contains the IP address of the client gateway (the organization’s public IP address), ensuring that an organization's internal IP addresses are never exposed to externally.
Note: This Gateway option is only configurable for Parent location.
|
| Enable Caution | If you have not enabled Authentication, you can enable this feature to display a caution notification to unauthenticated users. |
| Enable AUP | If you have not enabled Authentication, you can enable this feature to display an Acceptable Use Policy (AUP) for unauthenticated traffic and require users to accept it. If you enable this feature:
|
| Enforce Firewall Control | Select to enable the service's firewall control.
Note: Before enabling this option, user must ensure if its Zscaler account has subscription for "Firewall Basic".
|
| Enable IPS Control | If you have enabled Enforce Firewall Control, select this to enable the service's IPS controls.
Note: Before enabling this option, user must ensure if its Zscaler account has subscription for "Firewall Basic" and "Firewall Cloud IPS".
|
| Authentication | Enable to require users from the Location or Sub-location to authenticate to the service. |
| IP Surrogate | If you enabled Authentication, select this option if you want to map users to device IP addresses. |
| Idle Time for Dissociation | If you enabled IP Surrogate, specify how long after a completed transaction, the service retains the IP address-to-user mapping. You can specify the Idle Time for Dissociation in Mins (default), or Hours, or Days.
|
| Surrogate IP for Known Browsers | Enable to use the existing IP address-to-user mapping (acquired from the surrogate IP) to authenticate users sending traffic from known browsers. |
| Refresh Time for re-validation of Surrogacy | If you enabled Surrogate IP for Known Browsers, specify the length of time that the Zscaler service can use IP address-to-user mapping for authenticating users sending traffic from known browsers. After the defined period of time elapses, the service will refresh and revalidate the existing IP-to-user mapping so that it can continue to use the mapping for authenticating users on browsers. You can specify the Refresh Time for re validation of Surrogacy in minutes (default), or hours, or days.
|
| Bandwidth Control Options for Location | |
| Bandwidth Control | Enable to enforce bandwidth controls for the location. If enabled, specify the maximum bandwidth limits for Download (Mbps) and Upload (Mbps). All sub locations will share the bandwidth limits assigned to this location. |
| Download | If you enabled Bandwidth Control, specify the maximum bandwidth limits for Download in Mbps. The allowable range is from 0.1 through 99999. |
| Upload | If you enabled Bandwidth Control, specify the maximum bandwidth limits for Upload in Mbps. The allowable range is from 0.1 through 99999. |
Bandwidth Control Options for Sub-Location (if Bandwidth Control is enabled on Parent Location)
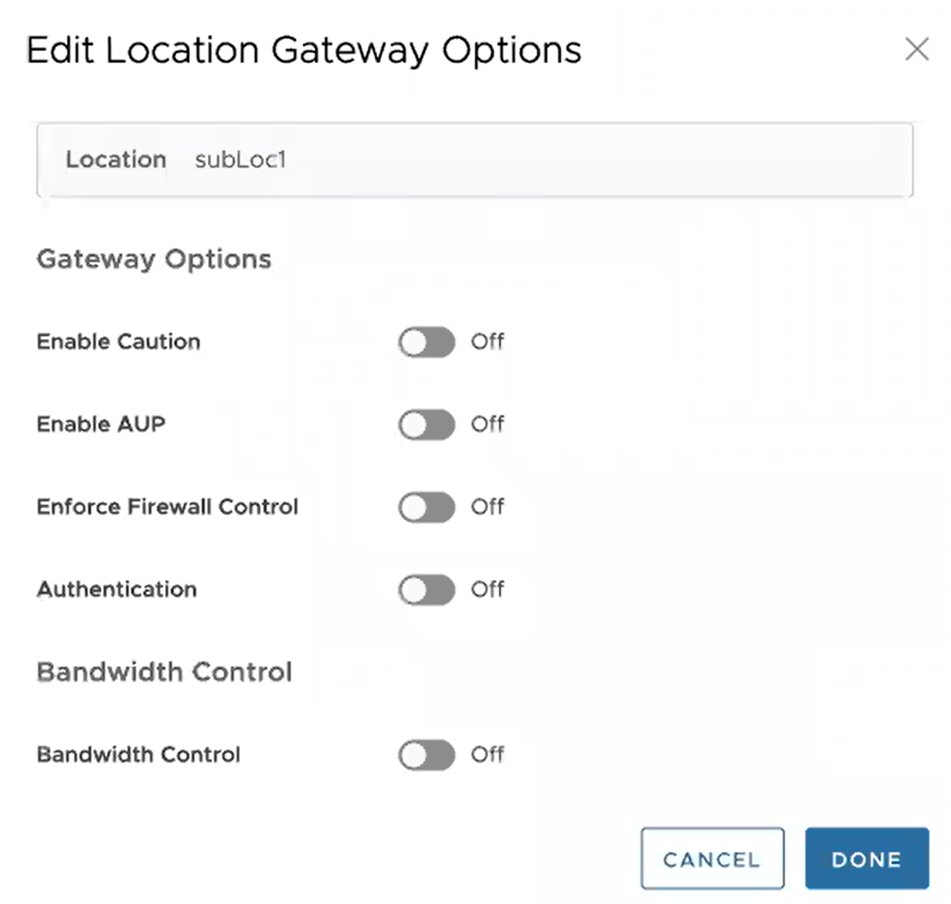 Note: The following bandwidth control options are configurable for sub-location only if you have bandwidth control enabled on the parent location. If the bandwidth control is not enabled on the parent location, then the bandwidth control options for sub-location are the same as location (Bandwidth Control, Download, Upload).
|
|
| Use Location Bandwidth | If you have bandwidth control enabled on the parent location, select this option to enable bandwidth control on the sub-location and use the download and upload maximum bandwidth limits as specified for the parent location. |
| Override | Select this option to enable bandwidth control on the sub-location and then specify the maximum bandwidth limits for Download (Mbps) and Upload (Mbps). This bandwidth is dedicated to the sub-location and not shared with others. |
| Disabled | Select this option to exempt the traffic from any Bandwidth Management policies. Sub-location with this option can only use up to a maximum of available shared bandwidth at any given time. |
Limitations
- In 4.5.0 release, when a Sub-location is created, Orchestrator automatically saves the "Other" Sub location. In earlier version of Orchestrator, the Zscaler "Other" Sub-location was not saved in Orchestrator. After upgrading Orchestrator to 4.5.0 release, the "Other" Sub-location will be imported automatically only after a new normal (non-Other) Sub-location is created using automation.
- Zscaler Sub-locations cannot have overlapping IP addresses (subnet IP ranges). Attempting to edit (add, update, or delete) multiple Sub-locations with conflicting IP addresses may cause the automation to fail.
- Users cannot update the bandwidth of Location and Sub-location at the same time.
- Sub-locations support Use Location Bandwidth option for bandwidth control when its Parent Location bandwidth control is enabled. When user turns off the Location bandwidth control on a Parent Location, the Orchestrator does not check or update the Sub-location bandwidth control option proactively.
Configure Business Policies with Cloud Security Services
Create business policies to redirect the traffic to a Cloud Security Service.
For additional information on business policies, see Create Business Policy Rule.
- In the SD-WAN service of the Enterprise portal, select .
- Select a profile from the list and select the Business Policy tab.
- Under Configure Business Policy > Business Policy Rules, select +ADD. The Add Rule dialog box appears.
- Enter a name for the business rule and select the IP version.
- Select the Match tab, choose the Match options to match the traffic.
- Select the Action tab and from the Network Service drop-down menu select Internet Backhaul and choose a Cloud Security Service from the drop-down menu. You must have already associated the cloud security service to the profile.
Figure 14. Adding a Business Rule 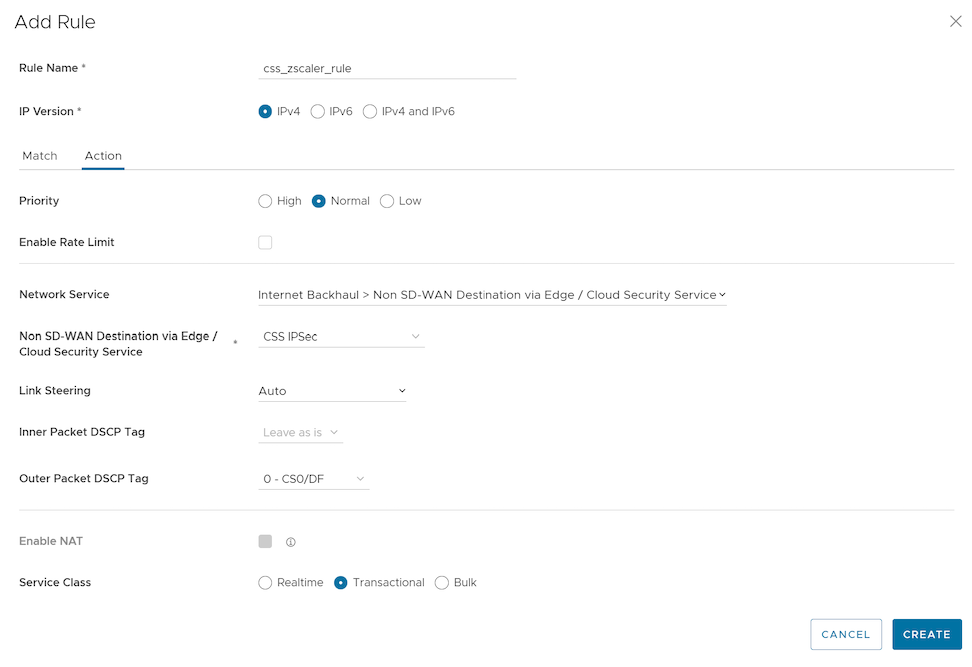
- Choose the other actions as required and select OK.
- Navigate to , select an Edge, and select the Business Policy tab.
- Under Configure Business Policy > Business Policy Rules, select +ADD. The Add Rule dialog box appears.
- Define the rule with cloud security service associated with the Edge.
The Business Policy tab of the Edge displays the policies from the associated profile along with the policies specific to the Edge.
Monitor Cloud Security Services
You can view the details of Cloud Security Services (CSS) configured for the Enterprise from the page.
To monitor the cloud security service sites:
- In the SD-WAN service of the Enterprise portal, select . The Network Services page appears.
- Select the Cloud Security Service Sites tab to view all the CSS configured for the Enterprise along with the following configuration details.
Figure 15. Displaying Cloud Security Services 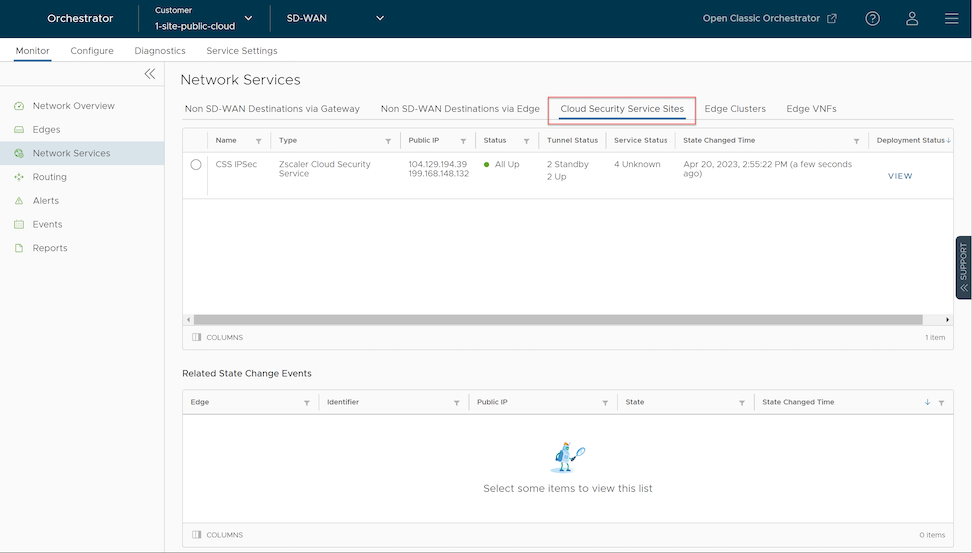
Table 7. Security Options Field Description Name The name of the CSS provider. Type The type of the CSS provider. Public IP The Public IP address of the CSS provider. Status The overall status of the CSS provider: - White- Specifies two possible states:
- ALL_STANDBY- The CSS provider is in this state if all the tunnels associated with the CSS provider are in STANDBY mode.
- UNKNOWN- The CSS provider is in this state if the overall status of the CSS provider is undetermined.
- Green- The CSS provider is in ALL_UP state if all the tunnels associated with the CSS provider are UP.
- Red- The CSS provider is in ALL_DOWN state if all the tunnels associated with the CSS provider are DOWN.
- Amber- The CSS provider is in PARTIAL state if the tunnels associated with the CSS provider are partially UP, DOWN, or in STANDBY mode.
Tunnel Status The status of tunnels created from the CSS provider from different Edges: - White- Specifies two possible states:
- UNKNOWN- The tunnel is in this state if the tunnel is unestablished.
- NOT ENABLED- The tunnel is in this state if the tunnel is not enabled.
- Gray- The tunnel associated with the CSS provider is in STANDBY mode.
- Green- Specifies two possible states:
- ALL_UP- All the tunnels associated with the CSS provider are UP.
- UP- A specific tunnel associated with the CSS provider is UP.
- Red- Specifies two possible states:
- ALL_DOWN- All the tunnels associated with the CSS provider are DOWN.
- DOWN- A specific tunnel associated with the CSS provider is DOWN.
Note: The numbers that appear on the Tunnel Status and Service Status icons signify the number of Edges associated with that state for the respective CSS provider.
Service Status The status of the external service as recorded by each Edge: - Green- The Layer 7 (L7) Health status of external service is UP.
- Red- The L7 Health status of external service is DOWN.
- Red- The L7 Health status of external service is DOWN due to one of the following reasons:
- The Zen service does not respond to 'N' (Default = 3) consecutive HTTP probe messages.
- The HTTP response (200 OK) time exceeds the set time (Default = 300 milliseconds).
- The Zen server responds with 4xx HTTP error code.
- Amber- The L7 Health status of external service is DEGRADED if the HTTP load time exceeds 'N' seconds (Default = 3 seconds).
- Gray- The L7 Health status of external service is UNKNOWN.
State Changed Time The date and time by when the state change occurred. Deployment Status Allows to view the deployment status of the CSS provider. - White- Specifies two possible states:
- Select the Radio button before the CSS provider Name to view the related state change events.
Figure 16. Displaying State Changes Events 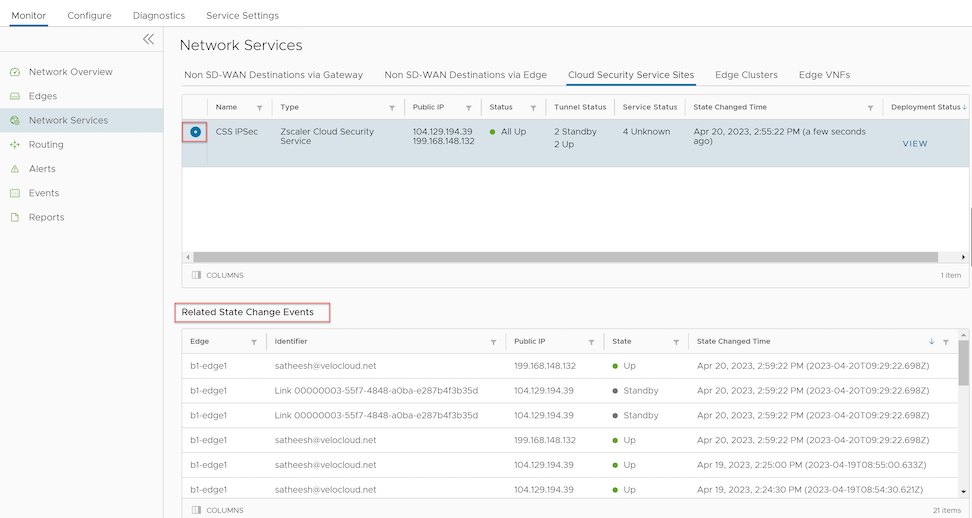
- Select the View link in the Deployment Status column to view the deployment status of the CSS provider.
Figure 17. Displaying Deployment Status 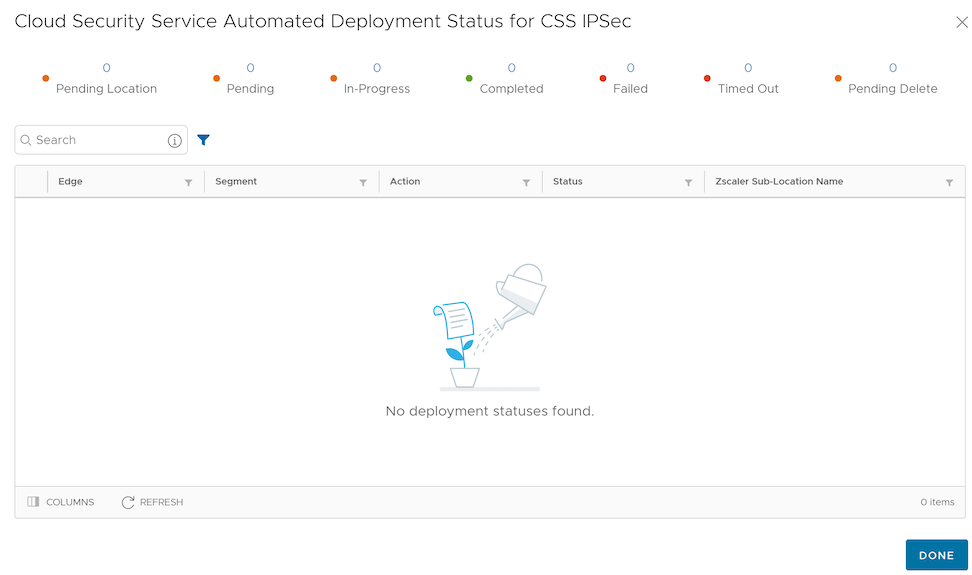 The following are the seven different states for an Edge action:
The following are the seven different states for an Edge action:- Pending Location- The Edge action is in this state until a Zscaler location is created. This state is only for applicable for Sub-location Edge actions.
- Pending- The Edge action is in this state as it waits for a backend worker process to pick it up and start working on it.
- In-Progress- The Edge action is in this state after a backend worker process picks up the Edge action and starts working on it.
- Completed- The Edge action is in this state if the Edge action task is successfully completed.
- Failed- The Edge action is in this state if an error has occurred.
- Timed Out- The Edge action is in this state if it takes more than the expected amount of time to complete the Edge action task.
- Pending Delete- The Edge action is in this state if it is pending deletion.
-
Note: Currently, the Pending Location and Pending Delete states are not used and these states will be removed from the UI in the future release.
- Select Details to view the Event details.
You can also view the Layer 7 (L7) health check statistics for Cloud Security Service from the menu.
Monitor Cloud Security Services Events
You can view the events related to cloud security services from the page.
In the SD-WAN service of the Enterprise portal, select .
To view the events related to cloud security service sites, you can use the Search and Filter options. Select the Filter icon and choose to filter either by the Event or by the Message column.
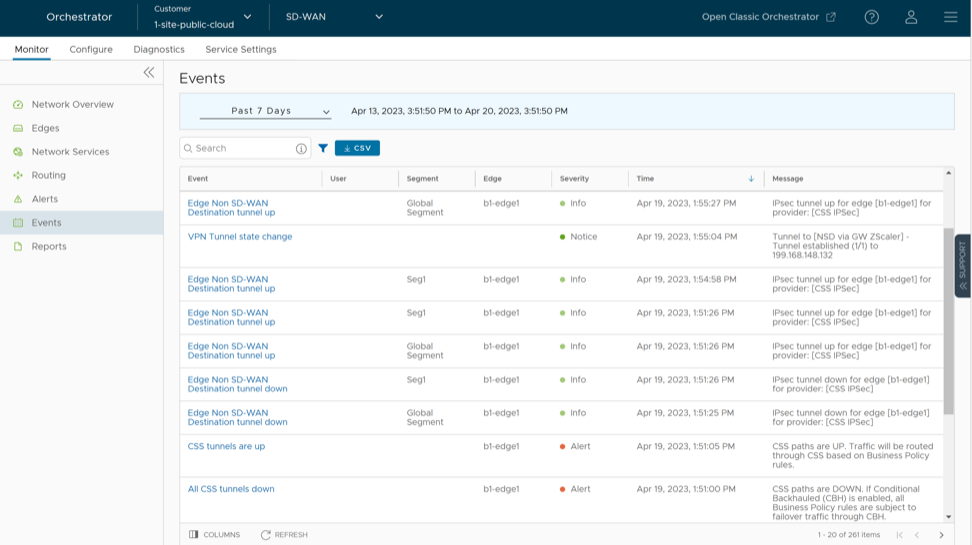
The following table includes the Enterprise events which help track various Edge actions related to CSS deployment, Location and Sub-location automation.
| Events | Description |
|---|---|
| Call made to external API | An API call to some external service has been made. |
| CLOUD_SECURITY_PROVIDER_ADDED | A new CSS provider has been added. |
| CLOUD_SECURITY_PROVIDER_UPDATED | A new CSS provider has been updated. |
| CLOUD_SECURITY_PROVIDER_REMOVED | A CSS provider has been removed. |
| Cloud Security Service site creation enqueued | A CSS site creation task has been enqueued. |
| Cloud Security Service site update enqueued | A CSS site update task has been enqueued. |
| Cloud Security Service site deletion enqueued | A CSS site deletion task has been enqueued. |
| Network Service created | A CSS site has been created. |
| Network Service updated | A CSS site has been updated. |
| Network Service deleted | A CSS site has been deleted. |
| CSS tunnels are up | The CSS paths are UP. The traffic will be routed through CSS based on the Business policy rules configured. |
| All CSS tunnels are down | The CSS paths are DOWN. |
| Edge Non SD-WAN Destination tunnel up | The tunnel is UP for the Edge. |
| Edge Non SD-WAN Destination tunnel down | The tunnel is DOWN for the Edge. |
| Zscaler Location creation enqueued | An Edge action has been enqueued to create a location. |
| Zscaler Location update enqueued | An Edge action has been enqueued to update a location. |
| Zscaler Location deletion enqueued | An Edge action has been enqueued to delete a location. |
| Zscaler Location object created | A Zscaler location object is created. |
| Zscaler Location object updated | A Zscaler location object is updated. |
| Zscaler Location object deleted | A Zscaler location object is deleted. |
| Zscaler Sub Location creation enqueued | An Edge action has been enqueued to create a sub-location. |
| Zscaler Sub Location update enqueued | An Edge action has been enqueued to update a sub-location. |
| Zscaler Sub Location deletion enqueued | An Edge action has been enqueued to delete a sub-location. |
| Zscaler Sub Location object created | A Zscaler Sub-location object is created. |
| Zscaler Sub Location object updated | A Zscaler Sub-location object is updated. |
| Zscaler Sub Location object deleted | A Zscaler Sub-location object is deleted. |