Configure Dynamic Routing with OSPF or BGP
This section discusses how to configure dynamic routing with OSPF or BGP.
Edge learns routes from adjacent routers through OSPF and BGP. It sends the learned routes to the Gateway/Controller. The Gateway/Controller acts like a route reflector and sends the learned routes to other Edge. The Overlay Flow Control (OFC) enables enterprise-wide route visibility and control for ease of programming and for full and partial overlay.
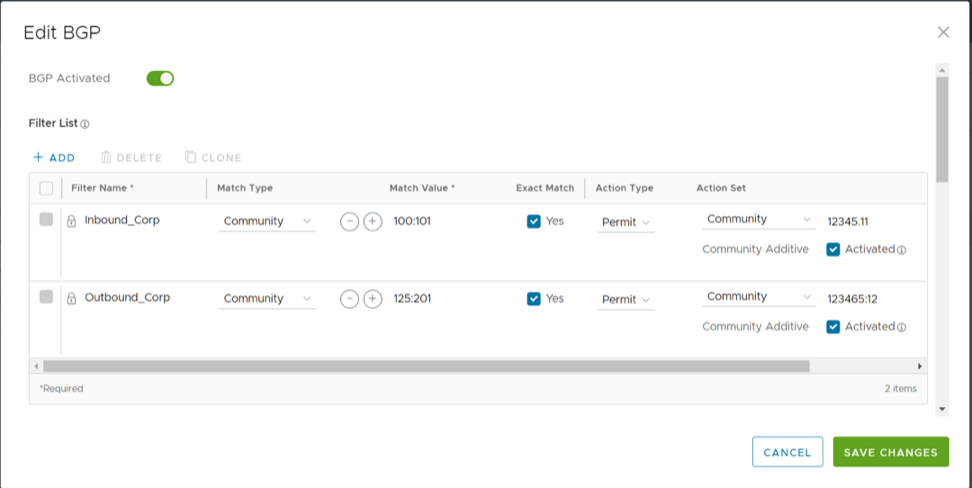
Arista supports Inbound/Outbound filters to OSPF neighbors, OE1/OE2 route types, MD5 authentication. Routes learned through OSPF will be automatically redistributed to the controller hosted in the cloud or on-premise. Support for BGP Inbound/Outbound filters and the filter can be set to Deny, or optionally you can Add/Change the BGP attribute to influence the path selection, i.e. RFC 1998 community, MED, and local preference.
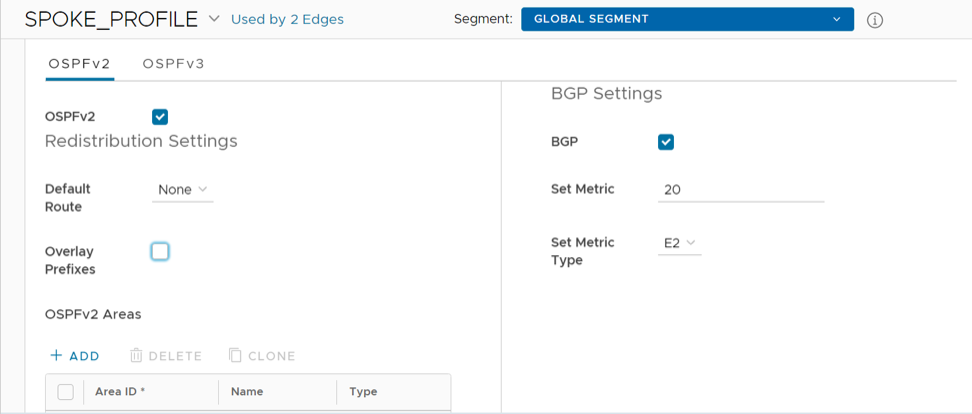
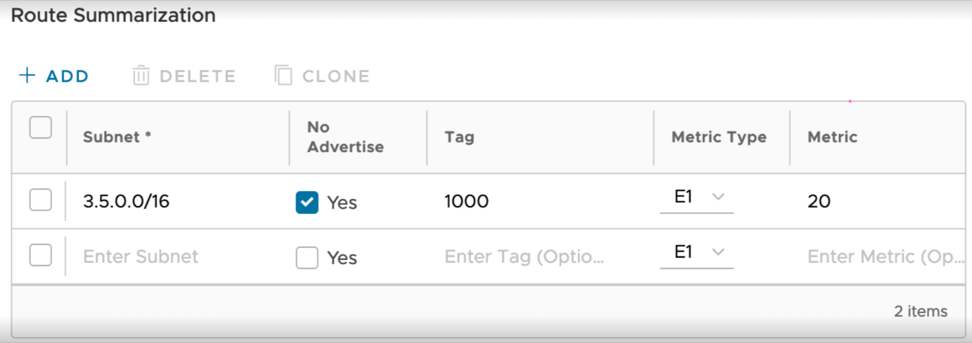
Activate OSPF for Profiles
Open Shortest Path First (OSPF) can be enabled only on a LAN interface as an active or passive interface. The Edge will only advertise the prefix associated with that LAN switch port. To get full OSPF functionality, you must use it in routed interfaces.
- Support for OSPFv3 is introduced in the SD-WAN Edge for IPv6 underlay routing in addition to existing BGPv6 support. The following is supported:
- Underlay IPv6 route learning.
- Redistribution of OSPFv3 routes into overlay/BGP and vice-versa.
- Support for Overlay Flow Control (OFC).
- OSPFv3 is implemented with feature parity to OSPFv2 with the following exceptions:
- Point to Point (P2P) is not supported.
- BFDv6 with OSPFv3 is not supported.
- md5 authentication is not available, as OSPFv3 header does not support it.
To activate OSPF, perform the steps in the procedure below:
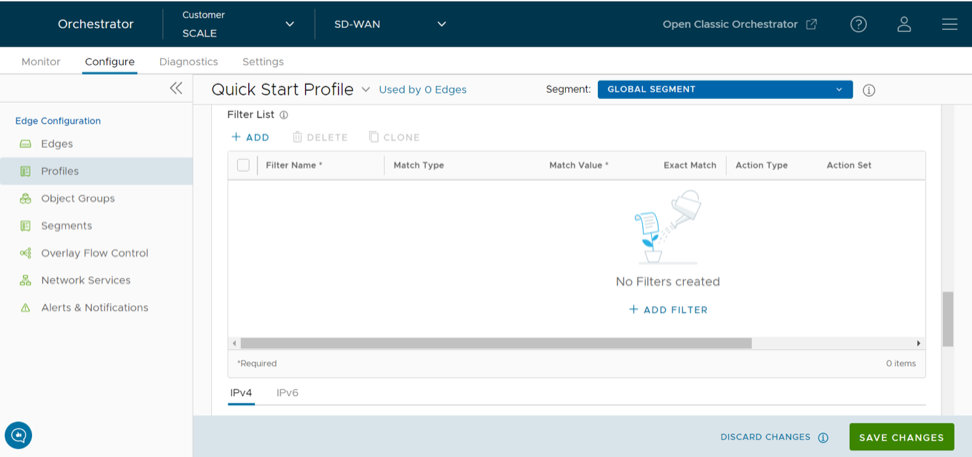
Route Filters
- Inbound Routing includes preferences that can be learned or ignored from OSPF and installed into the Overlay Flow Control.
- Outbound Routing indicates what prefixes can be redistributed into the OSPF.
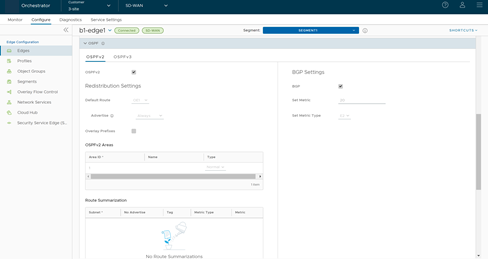
Activate OSPF for Edges
Open Shortest Path First (OSPF) can be enabled on a LAN (routed and switched) or a WAN interface. But only a LAN interface can be activated as an active or passive interface. The Edge will only advertise the prefix associated with that LAN switch port. To get full OSPF functionality, you must use it in routed interfaces. After you configure the OSPF settings at the Profile level, all the Edges associated with the Profile will inherit the OSPF configuration from the Profile. However, you cannot override the OSPF configuration settings at the Edge level.
If needed, you can view the OSPF configuration for a specific Edge as follows:
Configure BGP
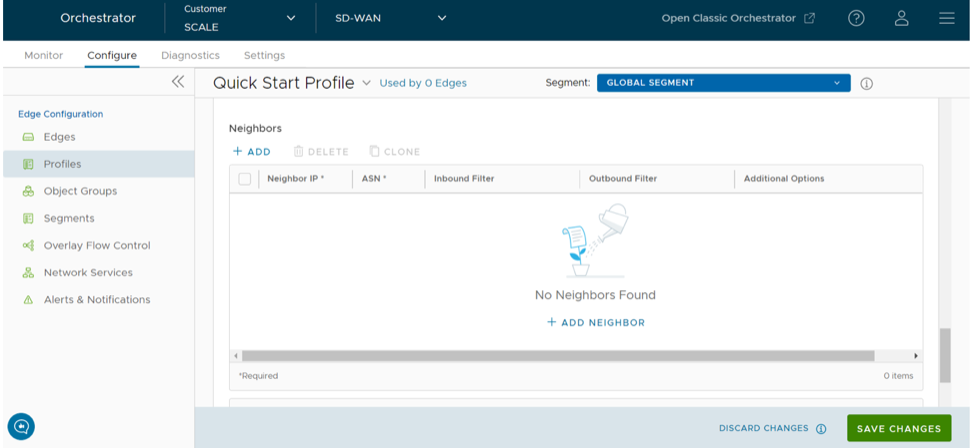
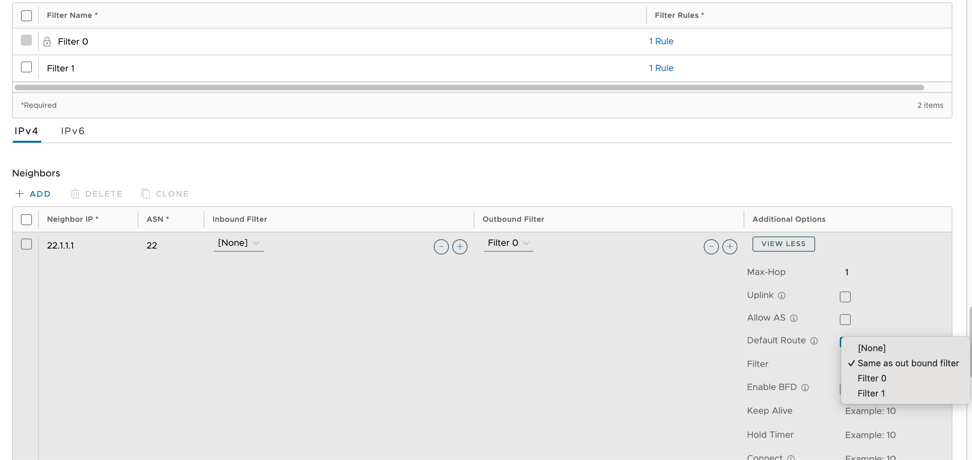
You can configure the BGP per segment for a Profile or an Edge. Configuring BGP is available for Underlay Neighbors and Non SD-WAN Neighbors.
- As the ASN of Edges.
- Peer to a neighbor with 4-Byte ASN.
- Accept 4-Byte ASNs in route advertisements.
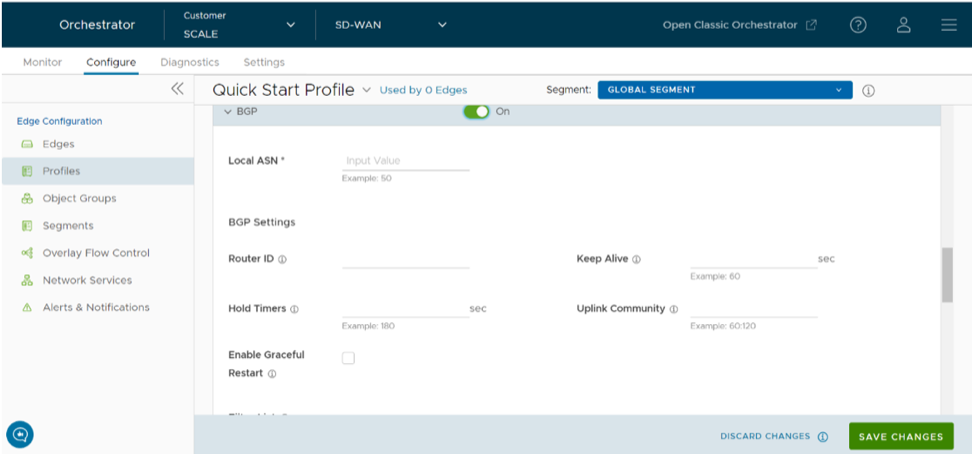
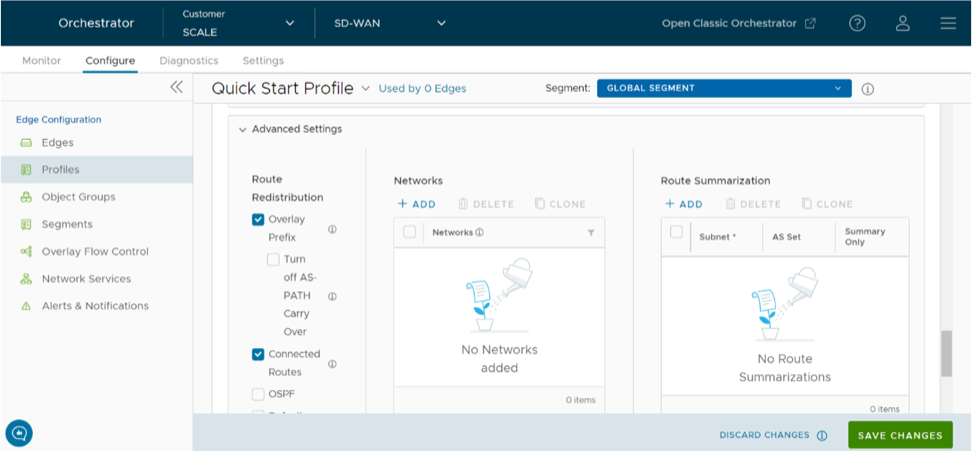
Configure BGP from Edge to Underlay Neighbors for Profiles
You can configure the BGP per segment at the Profile level as well as at the Edge level. This section provides steps on how to configure BGP with Underlay Neighbors.
Arista supports 4-Byte ASN BGP. See Configure BGP, for additional information.
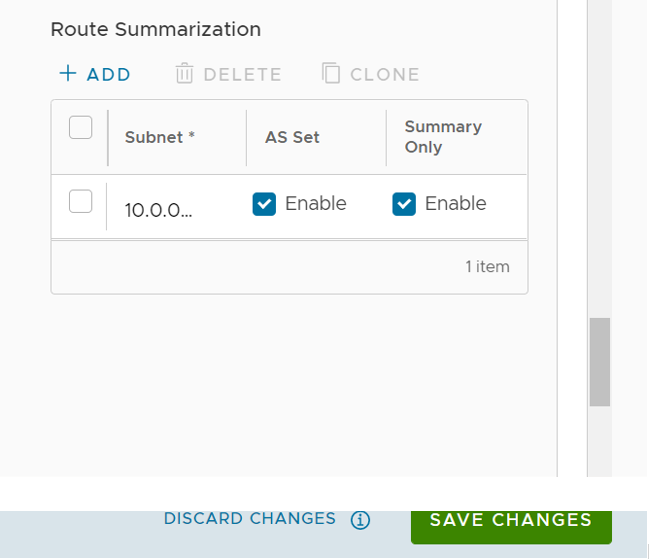
To configure BGP:
Configure BGP from Edge to Underlay Neighbors for Edges
You can override the inherited Profile settings at the Edge level when configuring BGP from the Edge to Underlay Neighbors.
If required, you can override the configuration for a specific Edge as follows:
Configure BGP Over IPsec from Edge to Non SD-WAN Neighbors
- Ensure that you have configured Configure a Tunnel Between a Branch and a Non SD-WAN Destinations via Edge to configure BGP with NSD Neighbors.
- The Local IP address from the Edge is required to configure BGP with NSD Neighbors.
The Non SD-WAN BGP Neighbors configuration is not applicable at Profile level. You can configure the NSD Neighbors only at the Edge level.
BGP is used to establish the BGP neighborship over the IPSec tunnels to the Non SD-WAN Sites. Direct IPSec tunnels are used for establishing a secure communication between the SD-WAN Edge and the Non SD-WAN Destination (NSD). In previous releases, Arista supported NSD tunnels from the SD-WAN Edge with the ability to add NVS static routes. In the 4.3 release, this functionality is extended to support BGP over IPSec to the NSD endpoint for a route-based VPN.
Use Case 1: BGP Over IPSec from an Edge to an Azure VPN
Each Azure VPN gateway allocates one set of public Virtual Public IPs (VIP) for a branch Edge to form IPSec tunnels. Similarly, Azure also allocates one internal private subnet and assigns one internal IP per VIP. This internal tunnel-ip (peer tunnel-ip) will be used for creating BGP peering with the Azure Gateway.
Azure has a restriction that the BGP peer IP (Edge's local tunnel-ip) shouldn't be in the same connected subnet or 169.x.x.x subnet, and therefore we need to support multi-hop BGP on the Edge. In BGP terminology, the local tunnel-ip maps to BGP source address and peer tunnel-ip maps to neighbor/peer address. We need to form a mesh of BGP connections- one per NSD tunnel so that the return traffic from the NVS could be load-balanced (flow-based)- design on the Azure Gateway side. In the below diagram for the physical Edge, we have two public WAN links and so four tunnels to an Azure Gateway. Each tunnel is associated with one BGP connection uniquely identified by the local tunnel_ip and remote peer tunnel_ip. On the Virtual Edge, the only difference is that we have one public WAN link and a maximum of two tunnels and two BGP sessions to the Azure Gateway.

Use Case 2: BGP Over IPSec from Edge to AWS VPN/Transit Gateway
Unlike Azure, AWS VPN Gateway allocates one set of public VIPs per link to a branch Edge. The total sets of public IPs allocated to a branch Edge from an AWS Gateway will be equal to the number of Edge public WAN links that will connect to the AWS VPN Gateway. Similarly, a /30 internal/private subnet would be allocated per tunnel, which are used for BGP peering on that tunnel. These IPs could be manually overridden in AWS Gateway configuration to ensure they are unique across different availability zones.
Similar to the Azure use-case, the Edge will form a mesh of BGP connections- one per tunnel to the AWS gateway. This will allow load-balancing of the return traffic from the AWS VPN Gateway- design on the AWS side. In the diagram below, for the physical Edge, the AWS Gateway allocates one set of public IPs and one set of tunnel-ips (/30) for each Edge WAN link. There are a total of four tunnels, but terminate in different public IPs on the AWS Gateway and four BGP connections.

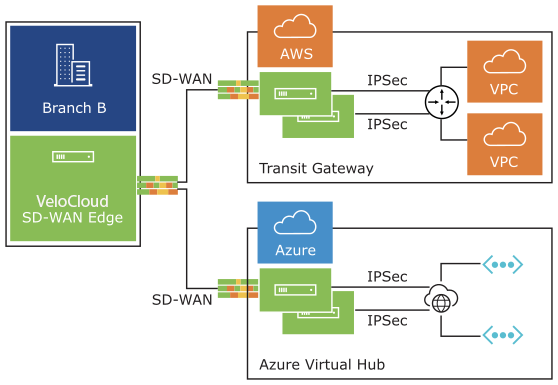
Use Case 3: Edge Connecting to Both AWS and Azure VPN Gateways (Hybrid Cloud)
One branch Edge could be connected to both Azure Gateway and AWS Gateway for redundancy purposes or some workloads/apps hosted in one cloud provider while other workloads/apps hosted in a different cloud provider. Regardless of the use-case, the Edge always establishes one BGP session per tunnel and propagates the routes between SD-WAN and IaaS. The diagram below is an example of one branch Edge connected to both Azure and AWS clouds.
Use Case 4: Hub Cluster Connecting to Azure/AWS Transit Gateways
The Hub cluster members can form IPSec tunnels to the Azure/AWS transit Gateways and leverage the transit Gateways as Layer 3 for routing traffic between different VPCs. Without the native BGP over IPSec functionality on Hub, the Hub needs to connect to an L3 router (Cisco CSR widely used here) using native BGP and the L3 router forming a mesh of BGP over IPSec tunnels with different VPCs. L3 router serves as a transit end-point between different VPCs. Usecase-1 (left diagram below): Use Hub as a transit node between different VPCs in different Availability Zones (AZ) so that one VPC can talk to another VPC. Usecase-2 (right diagram below): Connect all Hubs in the cluster directly to a cloud transit gateway and can use the cloud gateway as a PE(L3) router for routes distribution between cluster members. In both use-cases, without the support for BGP over IPSec on Hub, hub connects to an L3 router like CSR using native BGP and CSR peers with transit/VPC gateway using BGP over IPSec.

Use Case 5: Support Transit Functionality in Cloud Providers without Native Support
Some cloud providers like Google Cloud and AliCloud do not have native support for transit functionality (no transit Gateways), and with the support for BGP over IPSec, can rely on SD-WAN Edge/Hub deployed in the cloud to achieve the transit functionality between different VPCs/VNETs. Without the BGP over IPSec support, you must use an L3 router like CSR (solution (2)) to achieve the transit functionality.
To enable BGP with Non SD-WAN neighbors:
You can also configure BGP from Edge to underlay neighbors. For additional information, see Configure BGP from Edge to Underlay Neighbors for Edges.
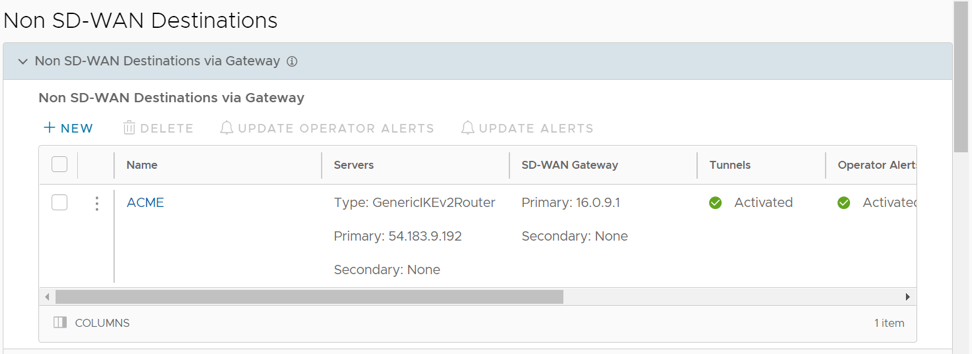
Configure BGP Over IPsec from Gateways
- Create a Non SD-WAN Destination via Gateway for one of the following sites:
- Configure a Non SD-WAN Destination of Type AWS VPN Gateway
- Configure a Non SD-WAN Destination of Type Check Point
- Configure a Non SD-WAN Destination of Type Cisco ASA
- Configure a Non SD-WAN Destination of Type Cisco ISR
- Configure a Non SD-WAN Destination of Type Generic IKEv2 Router (Route Based VPN)
- Configure a Non SD-WAN Destination of Type Microsoft Azure Virtual Hub
- Configure a Non SD-WAN Destination of Type Palo Alto
- Configure a Non SD-WAN Destination of Type SonicWALL
- Configure a Non SD-WAN Destination of Type Zscaler
- Configure a Non SD-WAN Site of Type Generic IKEv1 Router via Edge
- Configure a Non SD-WAN Destination of Type Generic Firewall (Policy Based VPN)
- Associate the Non SD-WAN Destination to a Profile See Configure a Tunnel Between a Branch and a Non SD-WAN Destinations via Gateway.
For additional information on Distributed Cost Calculation, refer to the Configure Distributed Cost Calculation section in the Arista VeloCloud SD-WAN Operator Guide.
You can configure BGP Settings for Gateways over IPsec tunnels.
Arista VeloCloud SD-WAN allows Enterprise users to define and configure a Non SD-WAN Destination instance in order to establish a secure IPsec tunnel to a Non SD-WAN Destination through an SD-WAN Gateway.
Monitor BGP Sessions
You can monitor the BGP sessions on Edges and Gateways.
Refer to the following sections to monitor the BGP sessions:
Monitor BGP Events
You can view the events related to the BGP sessions.
Troubleshooting BGP Settings
You can run Remote Diagnostics tests to view the logs of the BGP sessions and use the log information for troubleshooting purposes.
To run the tests for BGP:
OSPF/BGP Redistribution
Each of routing protocols OSPF and BGP may be enabled independently and the prior model of allowing only one routing protocol to be enabled on the system has been removed with this release. This release also allows the possibility of redistributing OSPF into BGP or BGP into OSPF (or both simultaneously), along with other possible route sources like prefixes learnt over the overlay, connected routes, static routes, etc.
In addition, with release 3.2, we are standardizing the redistribution behavior along more traditional lines (similar to that in other routing vendors). For example, if there is more than one route available for the same prefix, then only the best route for that prefix in the system RIB will be redistributed to the destination protocol if the configuration in the destination protocol allows redistribution for that route type.
Consider, as an example, redistribution of the prefix 192.168.1.0/24 into BGP. Let's say routes to the prefix 192.168.1.0/24 are locally available, learned from OSPF and separately learned as an Overlay prefix. Let's further assume that between the OFC flow ordering for the prefix, and route metrics, and route preference the OSPF route ranks above (is better than) the learned overlay route for that same prefix. Then, the OSPF route will be redistributed into BGP if OSPF redistribution has been turned on in BGP. Note that since the overlay learned prefix is not the best route for that prefix in the system RIB, it will not be redistributed into BGP even if the redistribution of overlay prefixes has been turned on in BGP.
In cases like the above, in order to facilitate the redistribution of the best route for a prefix into a given destination protocol, the user can enable redistribution for the specific route type that is the best route in the system.
Alternately, if the user prefers a different route source for that prefix to be redistributed into the destination protocol, the user can control the relative precedence of the route in the system RIB using the Overlay Flow Control facility provided by the management interface, or by varying the route metric.
OSPF/BGP Redistribution Metric Calculation
- The transit metric is (0) if the route is learned from a directly connected Edge.
- The transit metric is (90) if the route is learned via a Gateway.
- The transit metric is (32 + hub's order value) if the route is learned via a Hub Edge.
For BGP, this implies that the BGP MED value advertised by Hub Edges, which previously started from 9, 10, 11, and so forth, now starts from 33, 34, 35, and so forth.
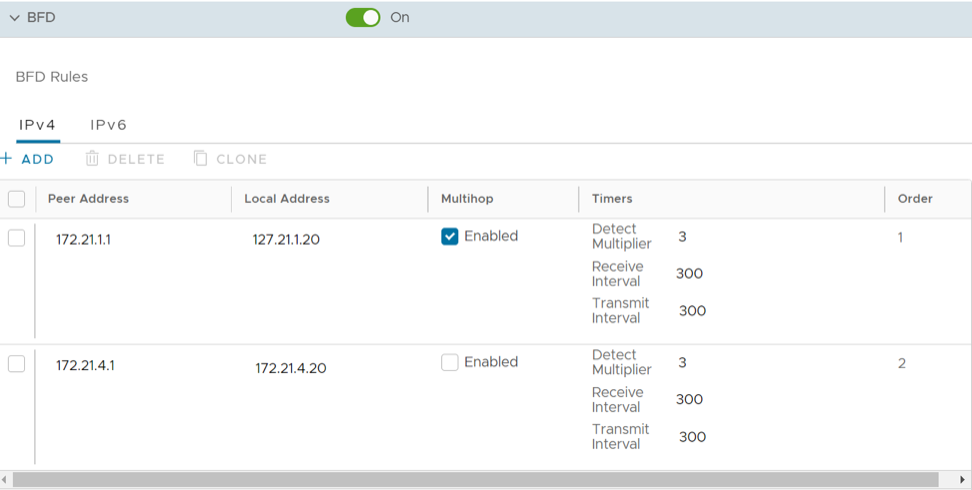
BFD Settings
Bidirectional Forwarding Detection (BFD) is a simple Hello protocol that is similar to detection components of well-known routing protocols. A pair of systems transmit BFD packets periodically over each path between the two systems, and if a system stops receiving BFD packets for long enough, the neighboring system is assumed to have failed.
A BFD session is established based on the needs of the application that would use BFD. The user has to explicitly configure the address and parameters for the BFD session and the subscribers/applications (BGP/OSPF) of the session, as there is no discovery mechanism in BFD.
Routing protocols like BGP or OSPF exchange the learned routes between Edges and Routers. These protocols exchange routes and detect route failures using their own mechanism. Generally, route failures are detected based on the keepalive mechanism where one entity echoes other entity on a frequent configured interval, that is the keepalive time. These routing protocols have higher keepalive timers which results in longer duration to detect the route failures. BFD detects route failures between two connected entities faster with low overhead on detection of failures.
- Fast route failure detection with low re-convergence time.
- Less overhead in route failure detection.
- Uniform rate of route failure detection across routing protocols.
BFD can be defined as a simple service. The service primitives provided by BFD are to create, destroy, and modify a session, given the destination address and other parameters. BFD in return provides a signal to the clients indicating when the BFD session goes up or down.
- BGP on Edges and Partner Gateways
- OSPF on Edges
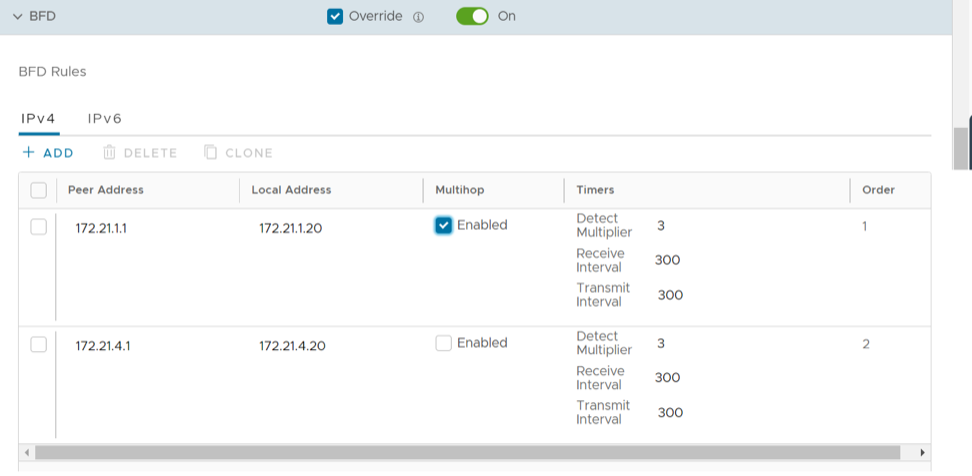
Configure BFD for Profiles
VeloCloud SD-WAN allows to configure BFD sessions to detect route failures between two connected entities.
To configure a BFD session for Profiles:
VeloCloud SD-WAN supports configuring BFD for BGP and OSPF.
- To enable BFD for BGP, see Configure BFD for BGP for Profiles.
- To enable BFD for OSPF, see Configure BFD for OSPF for Profiles.
- To view the BFD sessions, see Monitor BFD Sessions.
- To view the BFD events, see Monitor BFD Events.
- For troubleshooting and debugging BFD, see Troubleshooting BFD.
Configure BFD for Edges
VeloCloud SD-WAN allows to configure BFD sessions to detect route failures between two connected entities. Once you have configured BFD rules for a Profile, the rules are automatically applied to the Edges that are associated with the profile. Optionally, you can override the inherited settings at the Edge level.
To override the configuration for a specific Edge:
VeloCloud SD-WAN supports configuring BFD for BGP and OSPF.
- To enable BFD for BGP, see Configure BFD for BGP for Profiles.
- To enable BFD for OSPF, see Configure BFD for OSPF for Profiles.
- To view the BFD sessions, see Monitor BFD Sessions.
- To view the BFD events, see Monitor BFD Events.
- For troubleshooting and debugging BFD, see Troubleshooting BFD.
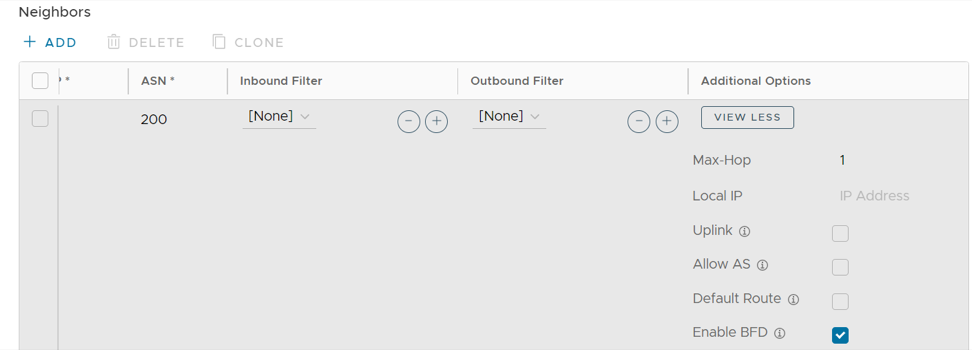
Configure BFD for BGP for Profiles
By default, BFD is deactivated in BGP neighbor. You can enable BFD for a BGP session to subscribe to BFD session updates.
Enabling BFD for a BGP neighbor does not create a BFD session. You must explicitly configure a BFD session. See Configure BFD for Profiles.
The following procedure describes how to enable BFD for an already configured BGP session on an Edge. To configure BGP settings, see Configure BGP from Edge to Underlay Neighbors for Profiles.
To enable BFD for BGP on partner Gateways, you must be an Operator super user. For additional information, see the Configure Partner Handoff section in the VeloCloud SD-WAN Operator Guide.
Configure BFD for BGP for Edges
You can override the inherited settings at the Edge level for BFD for BGP.
To override the configuration for a specific Edge:
Configure BFD for OSPF for Profiles
By default, BFD is deactivated in OSPF. You can enable BFD for OSPF to subscribe to BFD session updates.
Enabling BFD for an OSPF neighbor does not create a BFD session. You must explicitly configure a BFD session. See Configure BFD for Profiles.
The following procedure describes how to enable BFD for an already configured OSPF session on an Edge Interface. To configure OSPF settings, see Activate OSPF for Profiles.
To configure the Interface settings, see Configure Interface Settings for Profile.
Configure BFD for OSPF for Edges
You can modify the inherited Profile settings at the Edge level for BFD for OSPF.
If required, you can override the configuration for a specific Edge as follows:
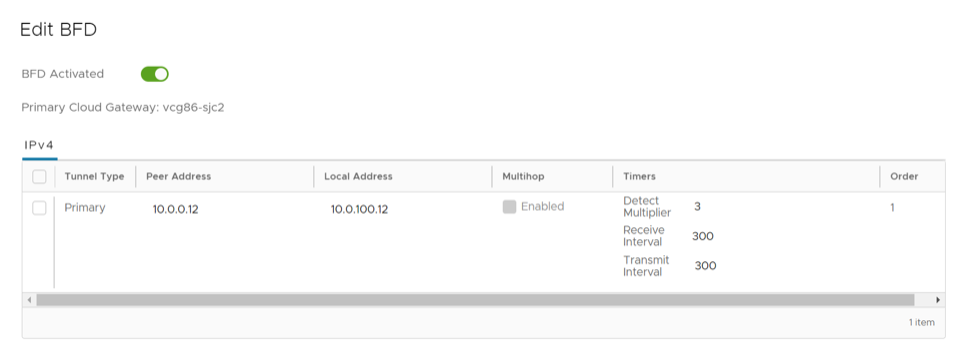
Configure BFD for Gateways
You can configure BFD Settings for Gateways over IPsec tunnels.
Ensure that you have configured the following:
- Create a Non SD-WAN Destination via Gateway for one of the following sites:
- Configure a Non SD-WAN Destination of Type AWS VPN Gateway
- Configure a Non SD-WAN Destination of Type Cisco ISR
- Configure a Non SD-WAN Destination of Type Generic IKEv1 Router (Route Based VPN)
- Configure a Non SD-WAN Destination of Type Generic IKEv2 Router (Route Based VPN)
- Configure a Non SD-WAN Destination of Type Microsoft Azure Virtual Hub
- Associate the Non SD-WAN Destination to a Profile See Configure a Tunnel Between a Branch and a Non SD-WAN Destinations via Gateway.
To configure BFD settings for a Gateway:
Monitor BFD Sessions
You can monitor the BFD sessions on Edges and Gateways.
To view the BFD sessions:
Monitor BFD Events
You can view the events related to the BFD sessions.
Troubleshooting BFD
You can run Remote Diagnostics tests to view the logs of the BFD sessions and use the log information for troubleshooting purposes.
To run the tests for BFD:
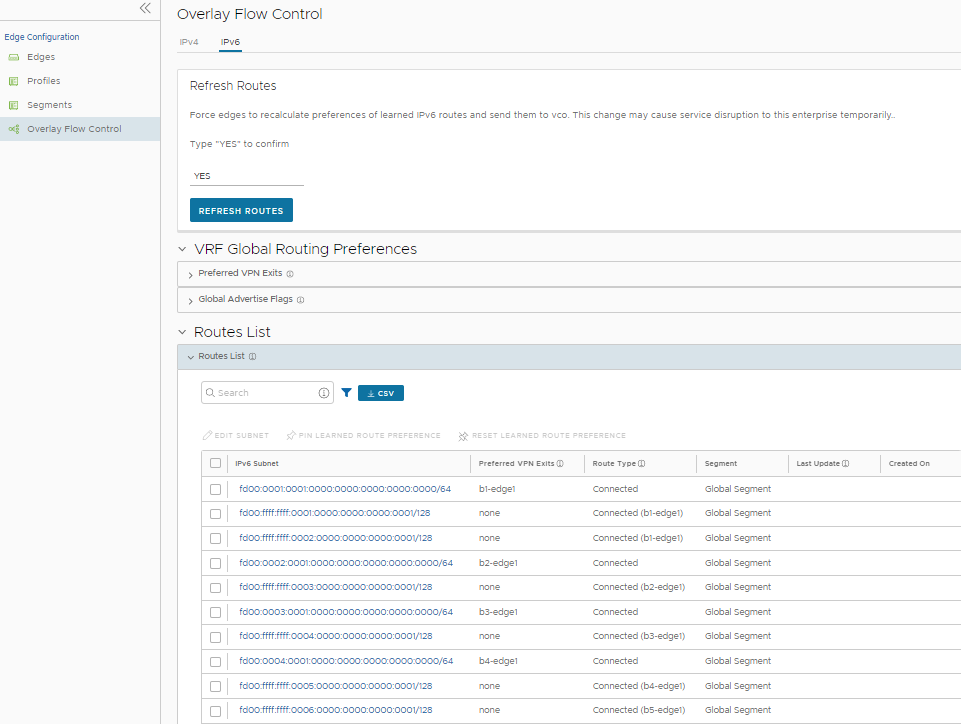
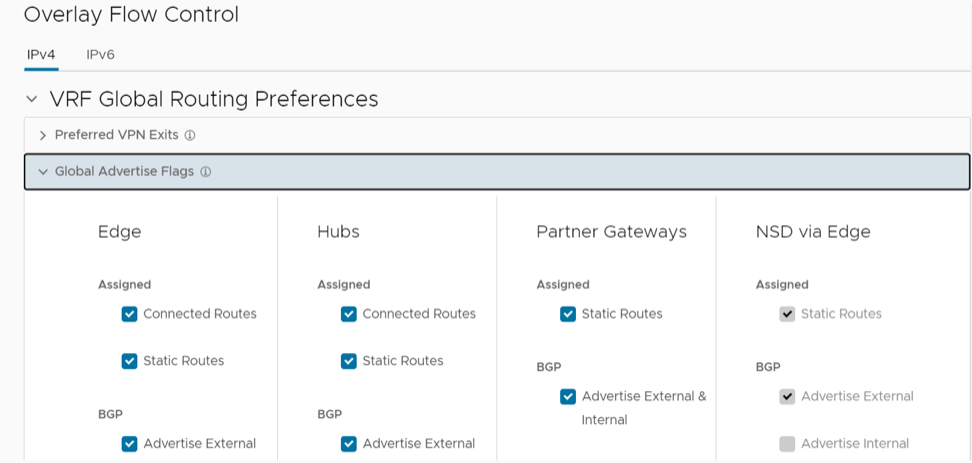
Overlay Flow Control
The Overlay Flow Control page displays a summarized view of all the routes in your network.
A new NSD bucket has been introduced for the classification of NSD Routes. The new NSD bucket preference logic will be applicable only when the Use NSD policy is enabled along with the Distributed Cost Calculation. The Use NSD policy can only be enabled after you enable the Distributed Cost Calculation.
You can view and edit the global routing preferences and the advertise actions for the Edges, Hubs, Partner Gateways, and Non SD-WAN Destinations via Edge and Gateway.
To configure the Overlay Flow Control settings, perform the following steps:
Configure Global Routing Preferences
In the Overlay Flow Control window, you can edit the global routing preferences, advertise actions, and modify the priorities of the destinations to where the traffic should be routed.
The VRF Global Routing Preferences section displays the Preferred VPN Exits and the Global Advertise Flags areas. To edit these areas, refer to the following procedural steps:
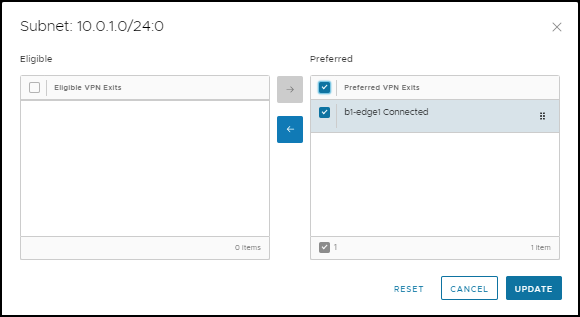
Configure Subnets
In the Overlay Flow Control window, you can update the priorities of the destinations for the learned routes in the subnets.