References
Related Documents
The following documentation is available for Arista VeloCloud SD-WAN:
The following documentation is available for Arista VeloCloud SD-WAN:
The following is a simple guide on what tools are available in the Orchestrator, how to use the tools, and how to activate EFS to start inspecting traffic.
A False Positive, with regards to IDS/IPS, is a situation where legitimate traffic is being blocked/flagged by the IDS/IPS.
If you believe that the IDS/IPS might be incorrectly blocking legitimate traffic, follow the steps outlined below, starting from granular approaches and moving to more broad solutions, to resolve the problem.
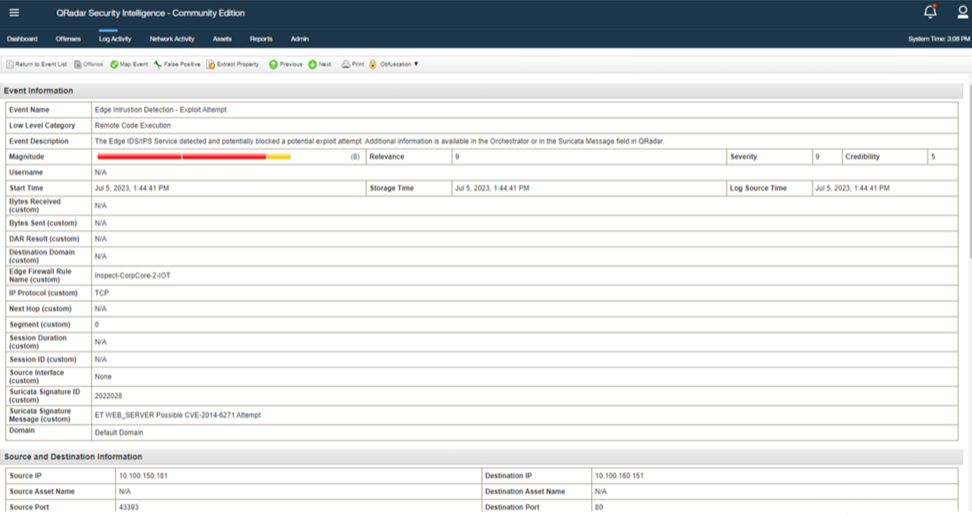
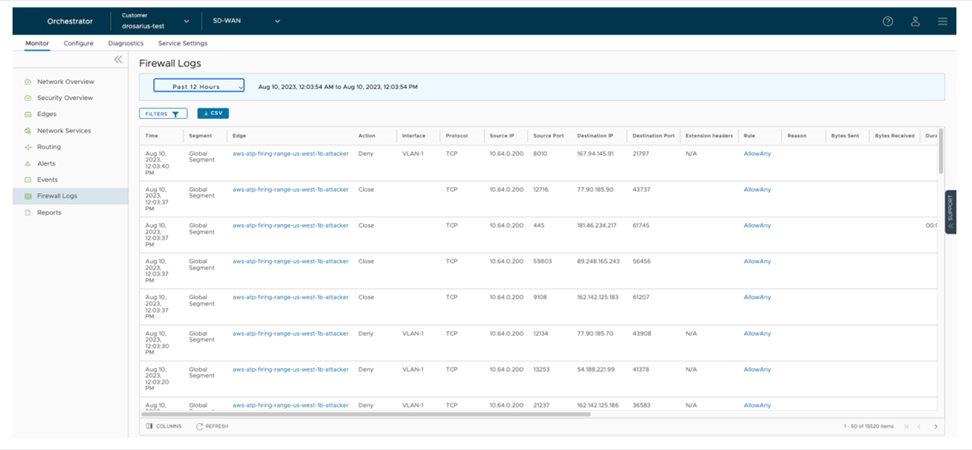
In all cases, submit a support ticket outlining the type of traffic being dropped and the Signature ID that the traffic is hitting. To collect the appropriate data to submit in your support ticket, refer to the Firewall logs or your logging infrastructure that is collecting your syslogs.
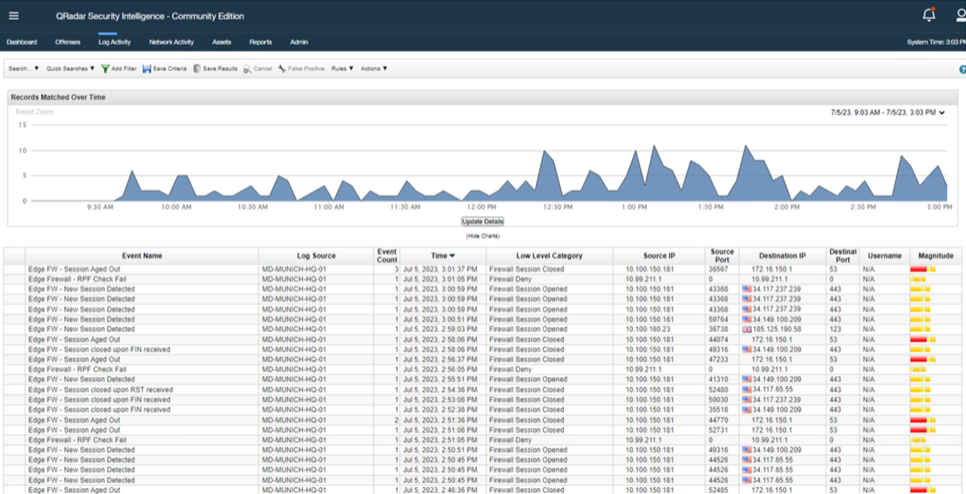
If you use the Orchestrator-hosted logging, navigate to and find the suspected traffic. From these logs, gather the Source IP, Destination IP, Application, and Signature ID and add that to your support ticket.
The deployment of EFS, or any new feature, requires careful consideration and planning.
Some of these factors can be understood through experience with the network, while others will require some investigative work. The Orchestrator provides you with easy-to-use tools and dashboards to accurately formulate a deployment strategy.
This section discusses monitoring and inspecting network traffic patterns to detect threats and troubleshoot performance issues.
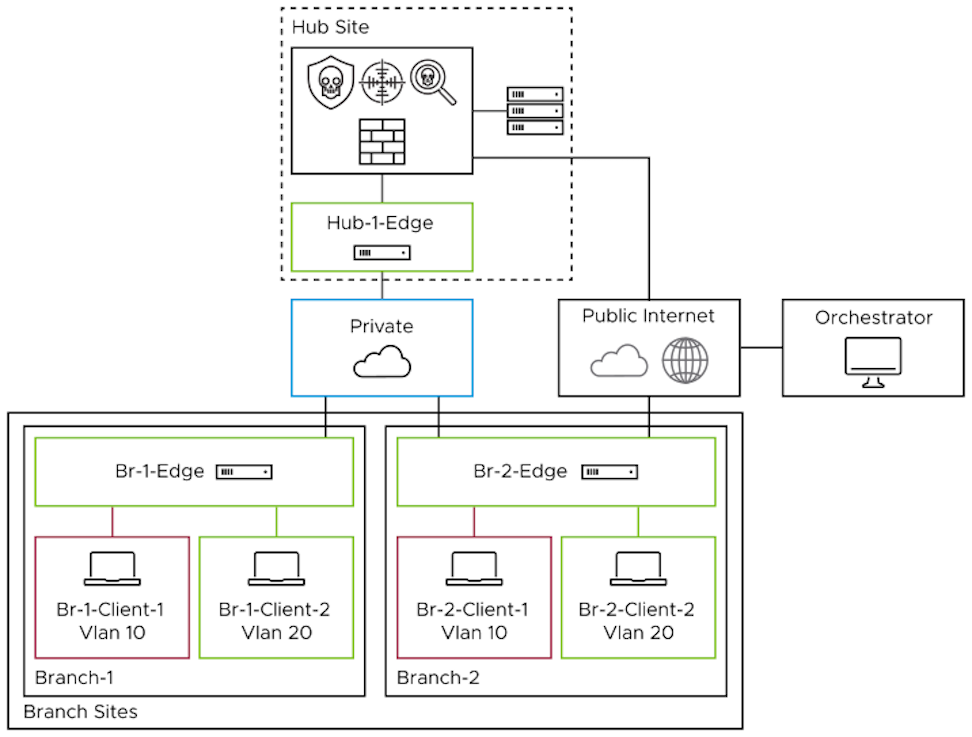
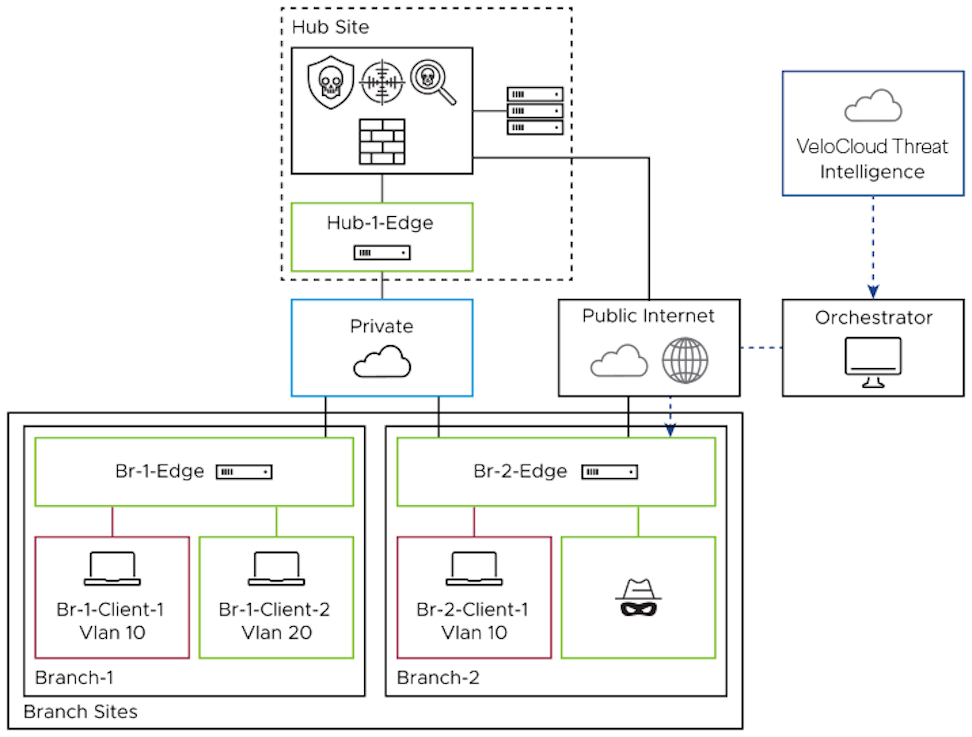
The Branch Attack Surface
Protecting internal traffic is as important as securing the network perimeter. Adversaries have multiple methods of bypassing a robust security stack that protects the boundary between the internal network and the outside world. Without a layered defense, a threat actor essentially has free rein over the internal network. A solid understanding of network segmentation will make it easier to create firewall policies that add the appropriate level of security without compromising performance.
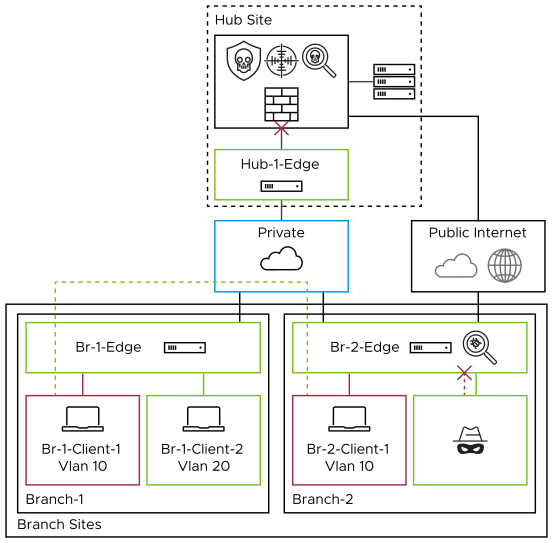
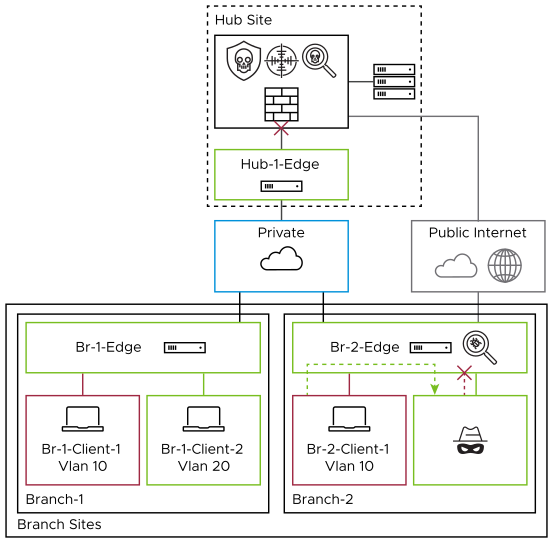
As branch sites typically have less security in place than hubs, it would be more prudent to add additional security checks for this traffic flow. The goal of EFS is to easily add these checks to secure the branch and limit the blast radius of an attack, thus hindering a hacker's ability to use techniques such as lateral movement.
Lateral Movement- Once an attacker gains access to a machine on an internal network, they will typically need to find a way to move laterally through the network in order to find sensitive information. One common way that an attacker might move laterally is by exploiting vulnerabilities in software that is used internally by the company. EFS can detect and prevent malicious movement that uses known exploits.
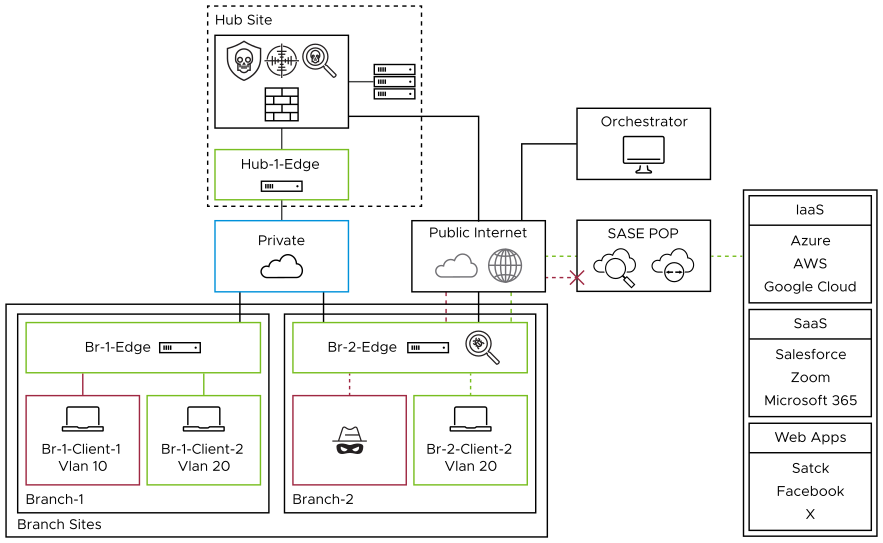
Combine EFS with any third-party SSE solution to provide a more well-rounded security approach. EFS protects your network from malicious activity by analyzing traffic patterns against signatures of known threats and anomalous behavior. In contrast, a third-party SSE primarily focuses on Internet-bound traffic, with features such as SSL Decryption, DLP, CASB, and URL and Content Filtering. Together, they provide a multi-tiered defense, protecting internal network operations and external web interactions from various cyber threats.
Although Enhanced Firewall Services (EFS) can be set up with a few mouse clicks, a thorough understanding of the network, traffic flows, and current configurations is required before activating and configuring the feature.
Traffic inspected by the IDPS with Stateful Firewall may experience a performance impact. There is a balancing act between securing the network and making it performant. By understanding your network, EFS can be applied to the appropriate traffic.
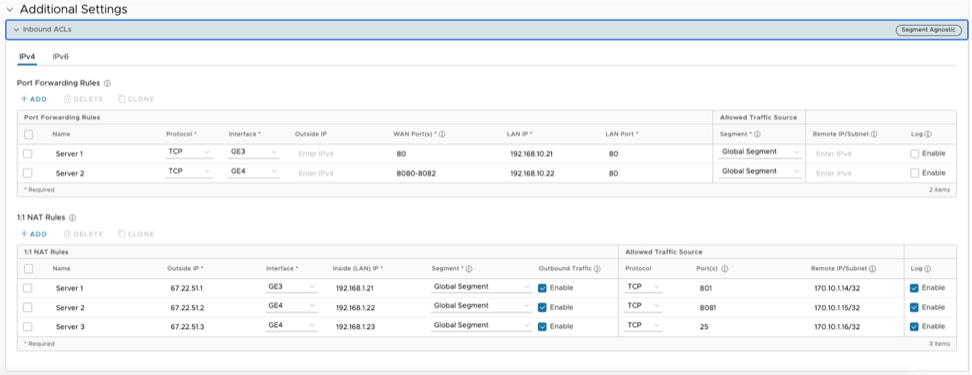
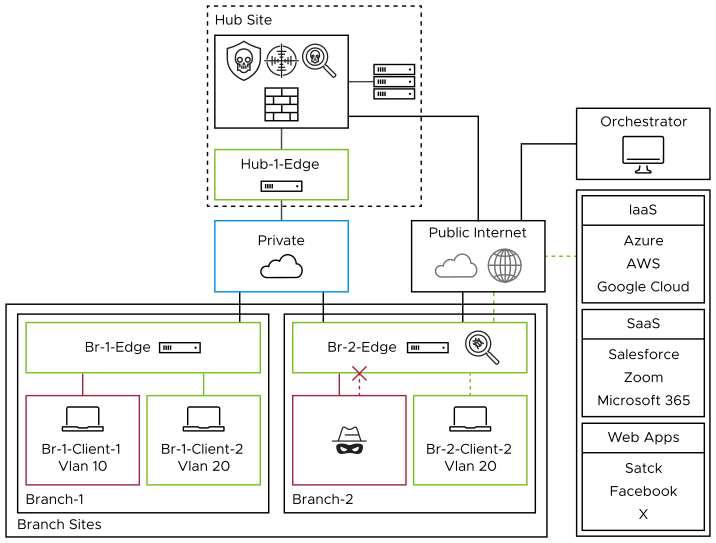
The reference architecture describes the basic topology, use cases, and functionality of the EFS components when activated for accessing applications in a multi-cloud environment, whether it be for branch-to-branch traffic, branch-to-hub traffic, or when accessing SaaS applications on the public cloud.
| Use Case | Description |
|---|---|
| Private Access | Private Access refers to those inter and intra-branch communications. While perimeter security is essential, internal traffic protection with EFS ensures that potential threats within the network are promptly identified and neutralized, thus maintaining the integrity and confidentiality of organizational assets. |
| Internet Access without Secure Web Gateway (SWG) | Direct Internet Access (DIA) provides direct connectivity to the Internet, which can improve efficiency and user experience. However, it also introduces new security challenges. Deploying EFS ensures that this convenience does not come at the cost of security, safeguarding your Enterprise from potential threats. |
| Internet Access with Secure Web Gateway (SWG) | A more comprehensive approach for securing Internet/SaaS traffic would be to pair EFS with a third party SSE (Secure Service Edge) and its many security capabilities, such as sandboxing, SSL decryption, URL and content filtering, Data Loss Prevention (DLP), and Cloud Access Security Broker (CASB). |
IDS/IPS
Hosted Logging
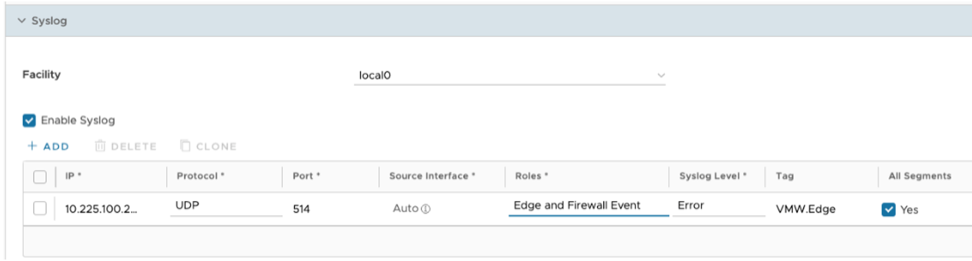
Regionally hosted logging is included in the base VeloCloud SD-WAN license. This means that logs are stored in the same region as the Orchestrator (virtual controller). By default, 15 GB of logs per Enterprise or seven days of logs per Edge, whichever comes first, kept. Logs can be viewed under the Firewall Logs section of the dashboard. There are options to search and filter for the specific data needed for troubleshooting or investigating. From this view, there is also a button to export the logs locally into a CSV format.
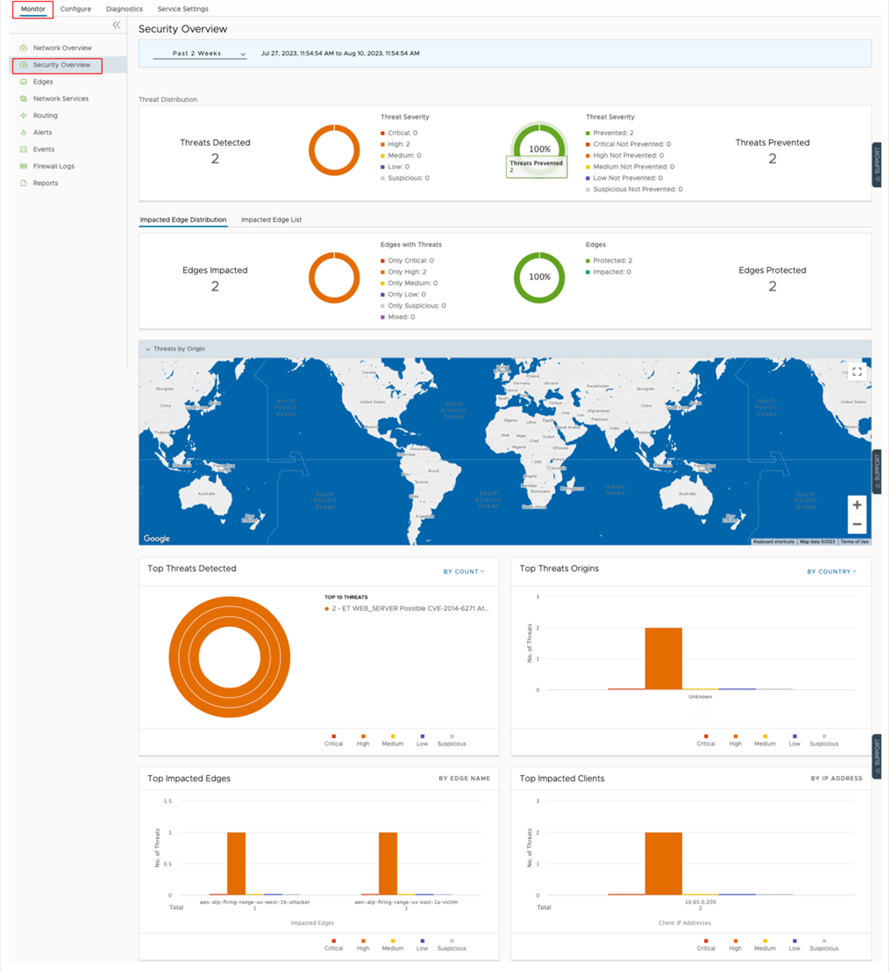
Security Overview Dashboard
The Security Overview dashboard provides a comprehensive overview of your Enterprise's threat landscape. A quick response is essential in addressing threats. This dashboard displays threats and their severity, the source of attacks, and the affected Edges, allowing you to take corrective action quickly.
To benefit from Enhanced Firewall Services (EFS), use a Premium V2 Arista VeloCloud license or an add-on license (SDEX-EFS-100M-1M) with all other SD-WAN license editions.
A significant number of network breaches originate in branch offices. Branch offices are vulnerable to a variety of attack vectors, including sophisticated phishing campaigns, lax physical security, and insider threats from disgruntled or careless users. These threats can be used to gain access to the network. With proper defenses, the damage from these attacks can be limited to the branch office and prevented from spreading to more sensitive areas of the network, such as the data center. Enhanced Firewall Services (EFS) are natively integrated security services in the VeloCloud Edge that can help protect branch offices from attacks.
This design guide is intended for all network and security architects, engineers, and administrators who design, deploy, or maintain a VeloCloud solution.
This design guide outlines how an organization can use the Enhanced Firewall Services (EFS) feature set to enhance its security footprint.
www.arista.com
Version 6.4
DOC-08385-02
|
Headquarters
5453 Great America Parkway
Santa Clara, CA 95054, USA +1-408 547-5500 www.arista.com
|
Support
+1-408 547-5502
+1-866 476-0000 This email address is being protected from spambots. You need JavaScript enabled to view it.
|
Sales
+1-408 547-5501
+1-866 497-0000 This email address is being protected from spambots. You need JavaScript enabled to view it.
|