evpn Layer 3 Core Operations
The evpn standard defines a number of operations and functionality to allow the dynamic learning of MAC and IP bindings, management of MAC moves (VM/host mobility), ARP suppression, automated discovery of remote VTEPs and multi-homing to support active-active topologies.
MAC Address Learning
MAC address learning on the local interface of a VTEP is flow-based learning. However once the MAC addresses are learned locally, they are advertised to BGP peers within the EVI via an evpn route update. The next hop of the update is set to IP of the advertising VTEP. In the case of evpn VXLAN the advertised label in the update is the VNI, which identifies the MAC-VRF in the case of a VLAN Based service, or the EVI for a VLAN aware bundle service.
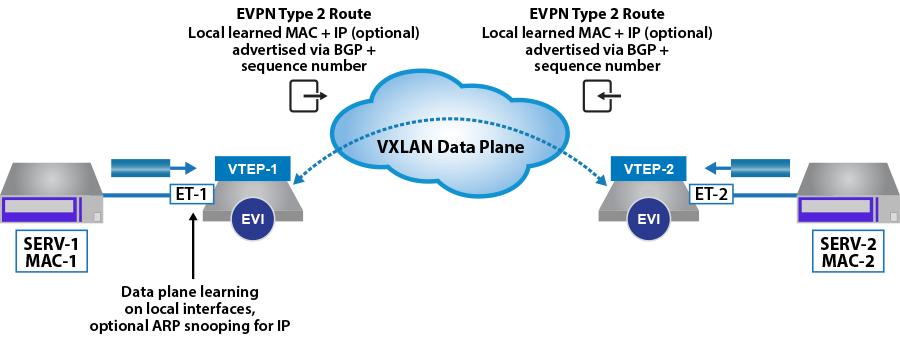
The route advertisements are evpn type-2 routes, which can advertise just the MAC address of the host, or optionally the MAC and IP address of the host. The format of the type-2 route is illustrated in the figure below, along with the mandatory, and optional extended community attached to the route.
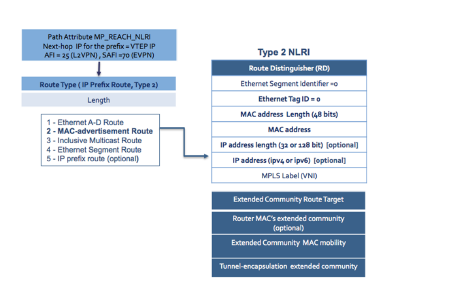
- Multi-protocol Reachable NLRI (MP_REACH_NLRI) attribute of the route is used to carry the next-hop hop for the advertised route. In the context of a VXLAN forwarding plane, this will be the source address (VTI) of the advertising VTEP.
- Route Distinguisher of the advertising node’s MAC-VRF.
- Ethernet Segment Identifier (ESI), this field is populated when the VTEP participating in a multi-homed topology. This is discussed in the following sections.
- Ethernet tag ID that will be 0 for VLAN-based service, and the customer VLAN ID in a VLAN-aware bundle service.
- The IP address of the host, which is associated with advertised MAC address. The advertisement of the Host’s IP address is optional.
- Label in the context of a VXLAN forwarding plane is the VNI associated with the MAC-VRF/Layer 2 domain the advertised MAC address has been learned on.
- Route Target associated with the MAC-VRF advertised with route to allow the control of the import and export of routes.
The MAC mobility extended community, as discussed in the following section is used during MAC moves to update all VTEPs of the new location of the host.
ARP Suppression
Address Resolution Protocol (ARP) suppression can be supported on the remote VTEPs, providing the option to advertise the MAC and IP binding in the type-2 route. The MAC to IP binding can be learned locally via ARP snooping or DHCP traffic on the VTEP. After the MAC and IP binding has been learned, it is advertised to the remote VTEPs as a type-2 route. This allows remote VTEPs to respond to any ARP requests for the host locally, thus reducing the amount of ARP traffic across the EVI.
MAC Mobility
A common scenario in a data center environment is Virtual Machines (VMs) moving between physical servers, for maintenance or performance reasons. This will result in the MAC of the VM being learned and advertised by a new VTEP.
To cater to this situation, a sequence number is attached to the new MAC advertisement, ensuring an EVI wide refresh of the MAC table, with VTEPs updating their forwarding tables to point to the advertising VTEP as the new next-hop for MAC address.
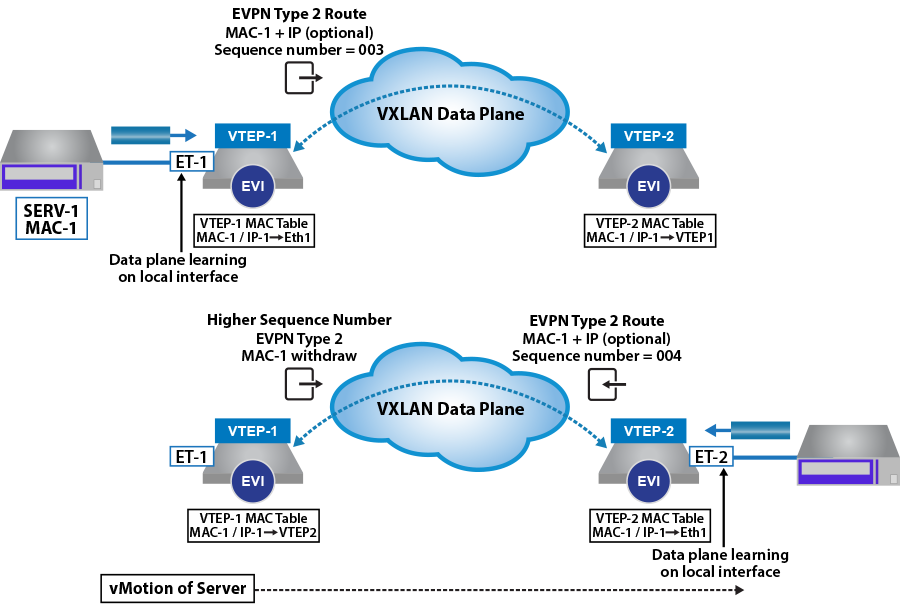
When a MAC address is learned and advertised for the first time, it is advertised without a sequence number and the receiving VTEP assume the sequence to be zero. On detection of a MAC move, such as a MAC is learned locally when the same MAC route is active via a type-2 advertisement, then the sequence number is incremented by one, and the MAC route is advertised to the remote peers. The original advertising VTEP, receives the MAC route with a now higher sequence number and withdraws its own local MAC route. All other VTEPs flush the original MAC route, and update their tables with the new higher sequence number route.
MAC Address Damping
In addition to MAC mobility, evpn defines a protection mechanism to detect and prevent MAC routes from flapping between VTEPs, which can occur during network instability or when hosts have been misconfigured with the same (duplicate) MAC address.
When advertising a locally learned MAC, the VTEP will start a M-second counter (default is 180s), if the VTEP detects N MAC moves (default is 5) for the route within the M-second window, it will generate a syslog message and stops sending and processing any further updates for the route.
Broadcast and Multicast Traffic
Broadcast, Unknown unicast and Multicast (BUM) traffic is handled within the evpn forwarding model using ingress replication. Where the BUM frame is replicated on the ingress VTEP to each of the remote VTEPs in the associated EVI/VNI. The VTEP replication list for the EVI, is dynamically populated based on Type-3 route advertisements (Inclusive Multicast Ethernet Tag Route), where VTEPs advertise type-3 routes for each EVI they are members.
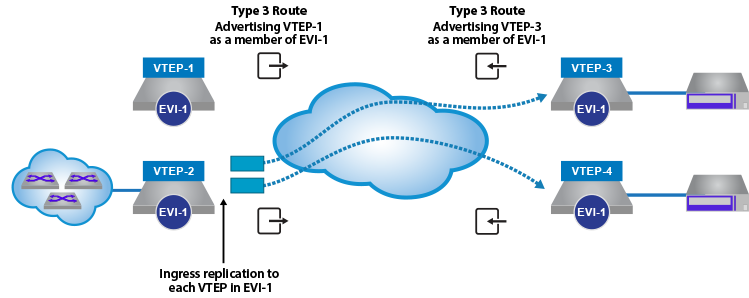
The format of the type-3 route is illustrated below.
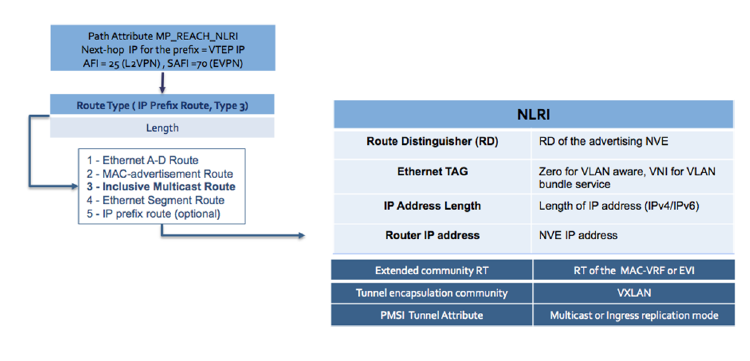
- Multi-protocol Reachable NLRI (MP_REACH_NLRI) attribute of the route is used to carry the next-hop hop for the advertised route. In the context of a VXLAN forwarding plane, this will be the source address (VTI) of the advertising VTEP.
- Route Distinguisher of the advertising node’s MAC-VRF.
- Ethernet tag that will be 0 for VLAN-based service, and the MAC-VRF VNI for a VLAN-aware bundle service.
- IP address of the VTEP advertising the type 3 route.
- Route Target associated with the MAC-VRF or the EVI in a VLAN-aware bundle service.
- PMSI Tunnel Attribute, to advertise the replication model the VTEP is supporting. The supported options defined within the standard are ingress replication and IP multicast.
