Azure Virtual WAN IPsec Tunnel Automation
VeloCloud Orchestrator supports integration and automation of Azure Virtual WAN from VeloCloud Gateway and VeloCloud Edge to enable Branch-to-Azure VPN Connectivity.
Azure Virtual WAN IPsec Tunnel Automation Overview
Azure Virtual WAN is a network service that facilitates optimized and automated Virtual Private Network (VPN) connectivity from enterprise branch locations to or through Microsoft Azure. Azure subscribers provision Virtual Hubs corresponding to Azure regions and connect branches (which may or may not be SD-WAN enabled) through IP Security (IPsec) VPN connections.
- IPsec from Gateway to Azure virtual WAN hub with automation.
- Direct IPsec from Edge to Azure virtual WAN hub with automation.
Azure Virtual WAN Gateway Automation
The following diagram illustrates the IPsec tunnel from Gateway to Azure virtual WAN hub.
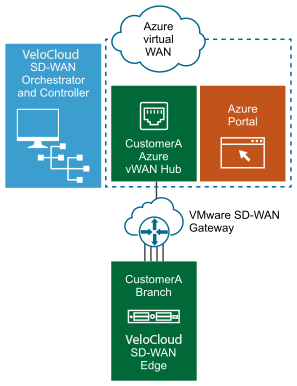
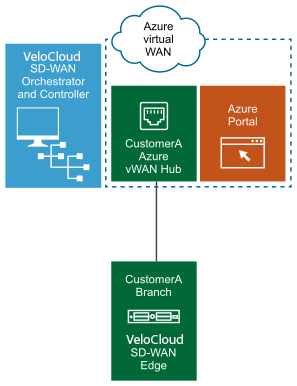
Azure Virtual WAN Edge Automation
The following diagram illustrates the IPsec tunnel directly from Edge to Azure virtual WAN hub.
Prerequisite Azure Configuration
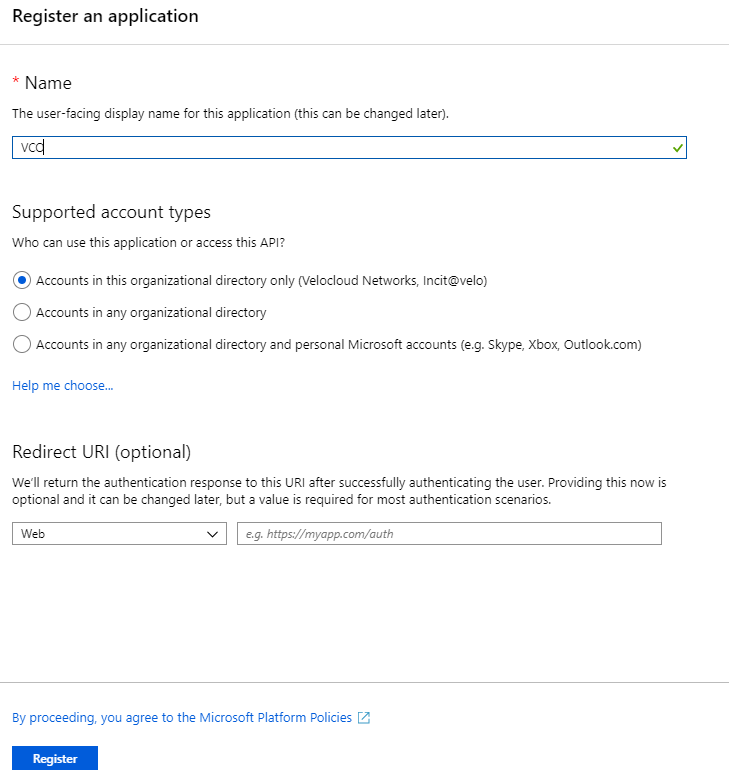
Register Orchestrator Application
- Ensure you have an Azure subscription. If not, create a free account.
To register a new application in Azure AD:
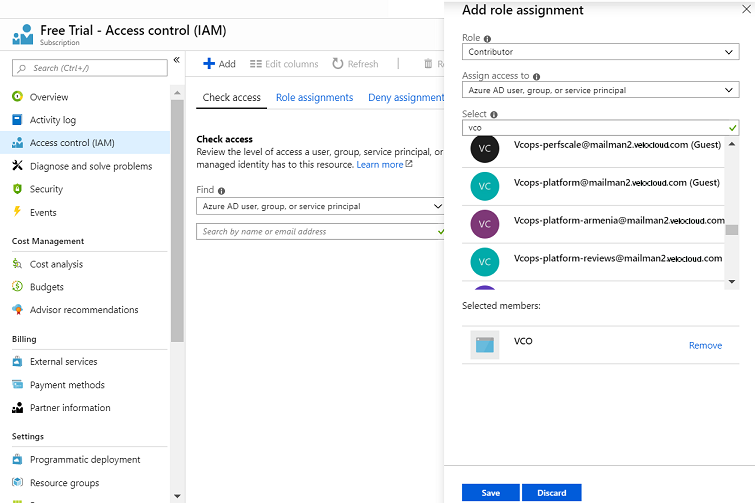
Assign the Orchestrator Application to Contributor Role
- Ensure you have an Azure subscription. If not, create a free account.
To assign a Contributor role at the subscription scope:
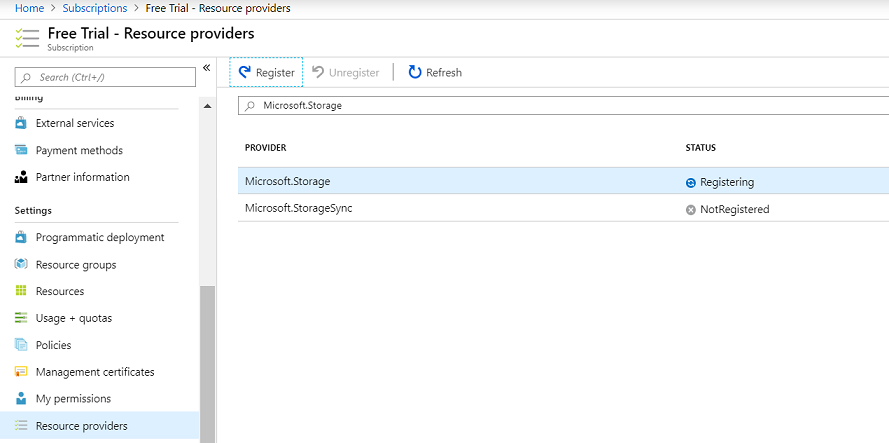
Register a Resource Provider
Microsoft.Storage resource provider on your Azure Subscription. By default, the Microsoft.Storage resource provider is not registered on Azure Subscriptions.
- Ensure you have an Azure subscription. If not, create a free account.
- Ensure you have the Contributor or Owner roles permission.
To register a resource provider for your subscription:
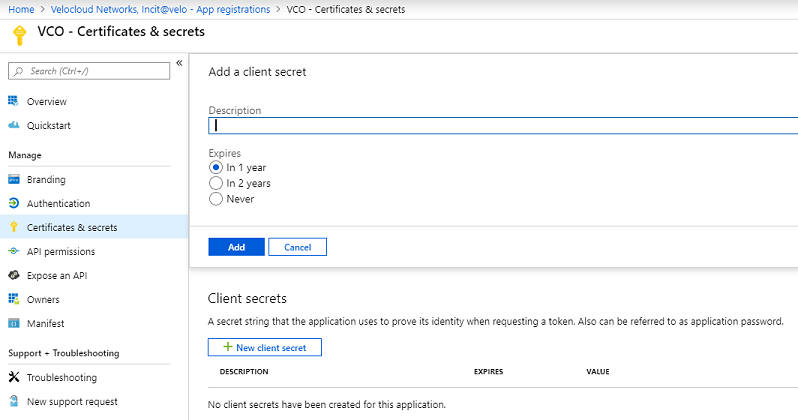
Create a Client Secret
- Ensure you have an Azure subscription. If not, create a free account.
To create a new client secret in Azure AD:
Configure Azure Virtual WAN for Branch-to-Azure VPN Connectivity
This section discusses the procedures to configure Azure for integrating Azure Virtual WAN and Gateway to enable the branch-to-Azure VPN connectivity.
- Verify that none of the subnets of your on-premises network overlap with the existing virtual networks that you want to connect to. Your virtual network does not require a gateway subnet and cannot have any virtual network gateways. For steps to create a virtual network, see Create a Virtual Network.
- Obtain an IP address range for your Hub region and ensure that the address range that you specify for the Hub region does not overlap with any of your existing virtual networks that you connect to.
- Ensure you have an Azure subscription. If not, create a free account.
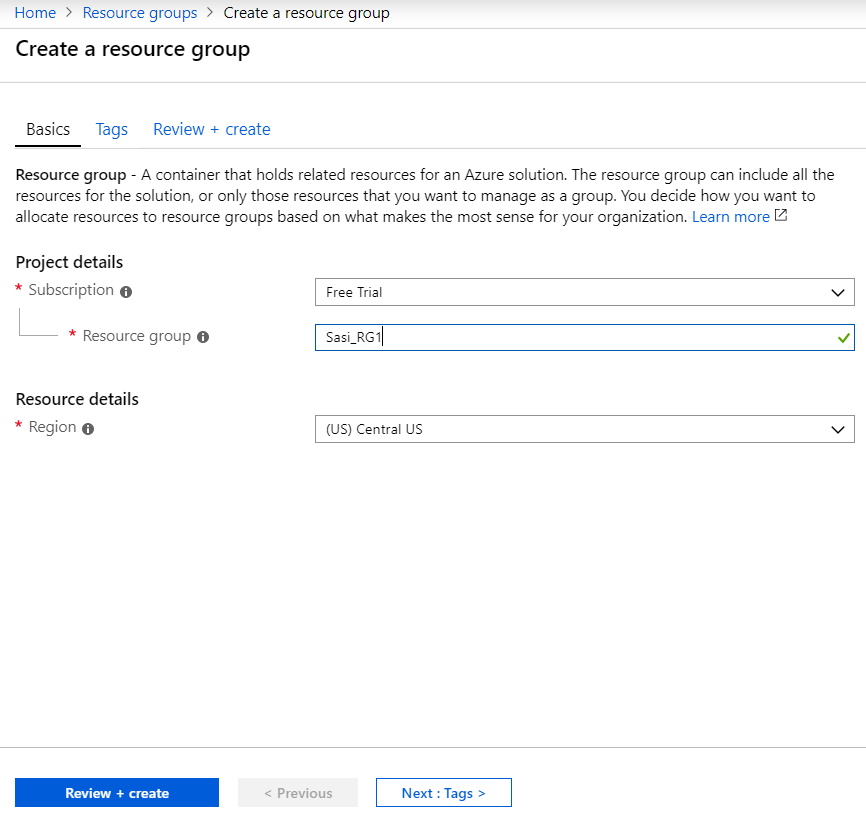
Create a Resource Group
- Ensure you have an Azure subscription. If not, create a free account.
To create a resource group in Azure:
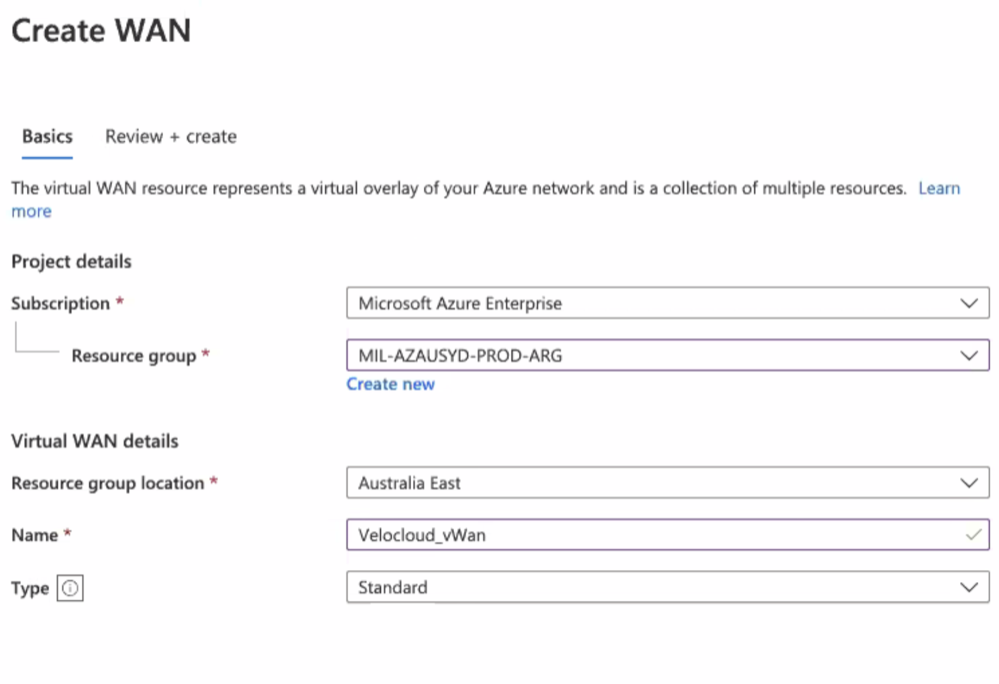
Create a Virtual WAN
- Ensure you have an Azure subscription. If not, create a free account.
- Ensure you have a resource group created to add the Virtual WAN.
To create a Virtual WAN in Azure:
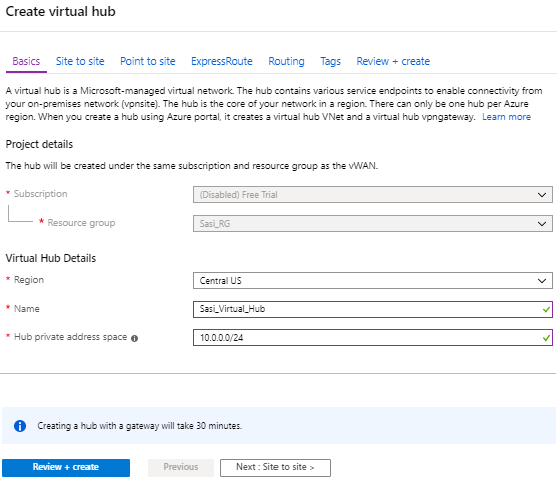
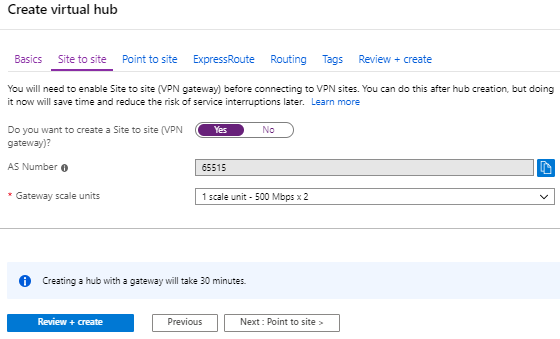
Create a Virtual Hub
- Ensure you have an Azure subscription. If not, create a free account.
- Ensure that you have a resource group created to add the Azure resources.
To create a Virtual Hub in Azure:
- Create Virtual Connection between Hubs and Virtual Networks (VNets). For steps, see Create a Virtual Connection between VNet and Hub.
- If you do not have an existing VNet, you can create one by following the steps in Create a Virtual Network.
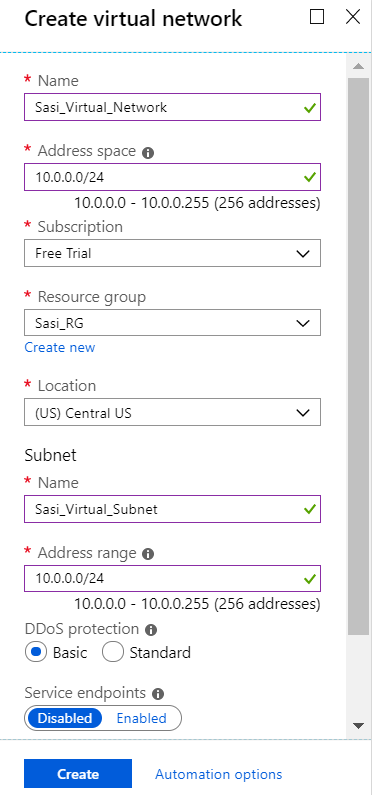
Create a Virtual Network
- Ensure you have an Azure subscription. If not, create a free account.
To create a Virtual Network in Azure:
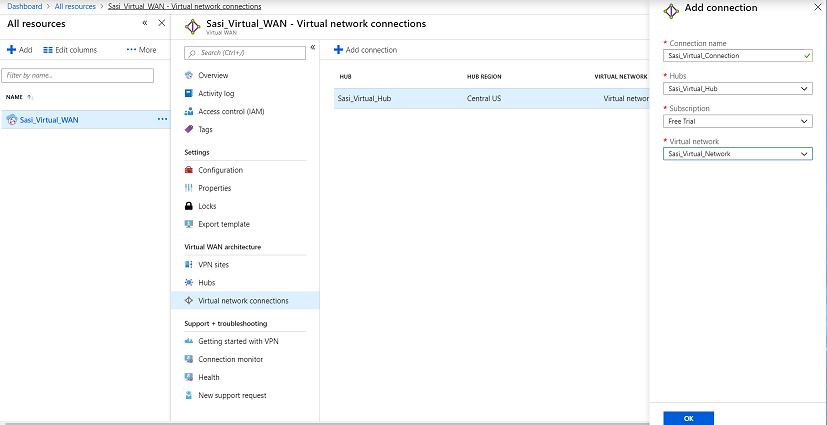
Create a Virtual Connection between VNet and Hub
- Ensure you have an Azure subscription. If not, create a free account.
- Ensure you have Virtual Hubs and Virtual Networks created.
To create a virtual network connection between a VNet and a Virtual Hub in a particular Azure region:
Configure Orchestrator for Azure Virtual WAN IPsec Automation from Gateway
You can configure Orchestrator for integrating Azure Virtual WAN and Gateway to enable the branch-to-Azure VPN connectivity.
session.options.enableAzureVirtualWAN system property to true.Before you begin the Orchestrator configuration for Azure Virtual WAN- Gateway automation, ensure you have completed all the steps explained in the Prerequisite Azure Configuration and Configure Azure Virtual WAN for Branch-to-Azure VPN Connectivity sections.
To view the details of Non SD-WAN Destinations network services configured for an enterprise, see Monitor Non SD-WAN Destinations.
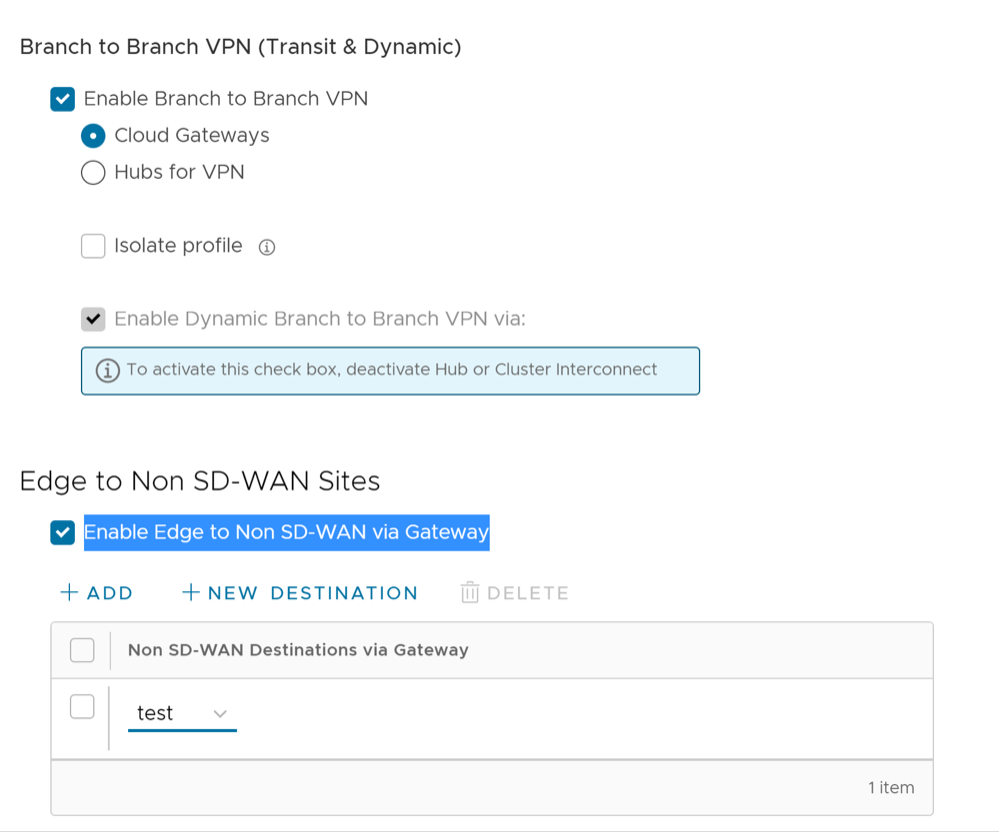
Associate a Microsoft Azure Non SD-WAN Destination to an SD-WAN Profile
To associate a Non SD-WAN Destination to a Profile, perform the following steps:
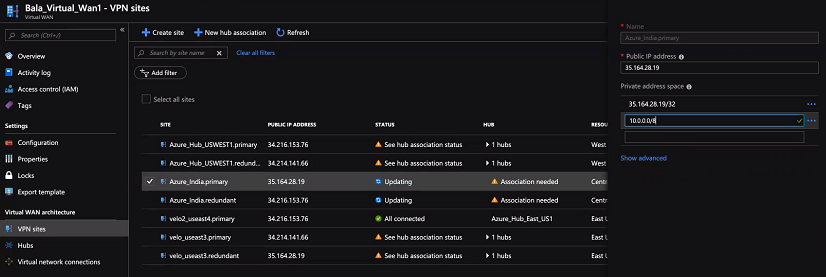
Edit a VPN Site
Discusses how to add SD-WAN routes into the Azure network manually.
Ensure you have completed provisioning the Azure VPN sites at the Orchestrator side.
To add SD-WAN routes manually into the Azure network:
Synchronize VPN Configuration
After successful Non SD-WAN Destination provisioning, whenever there are changes in the endpoint IP address of the Azure Hub or static routes, you need to resynchronize Azure Virtual Hub and Non SD-WAN Destination configurations. Selecting the Re-sync configuration button in the Non-VeloCloud Sites area will automatically fetch the VPN configuration details from the Azure portal and will update the Orchestrator local configuration.
Configure Orchestrator for Azure Virtual WAN IPsec Automation from Edge
You can configure Orchestrator for integrating Azure Virtual WAN and Edge to enable the branch-to-Azure VPN connectivity directly from Edge.
Before you begin the Orchestrator configuration for Azure Virtual WAN- Edge automation, ensure you have completed all the steps explained in the Prerequisite Azure Configuration and Configure Azure Virtual WAN for Branch-to-Azure VPN Connectivity sections.
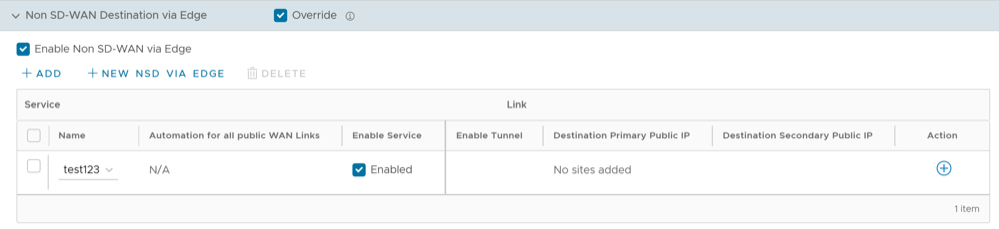
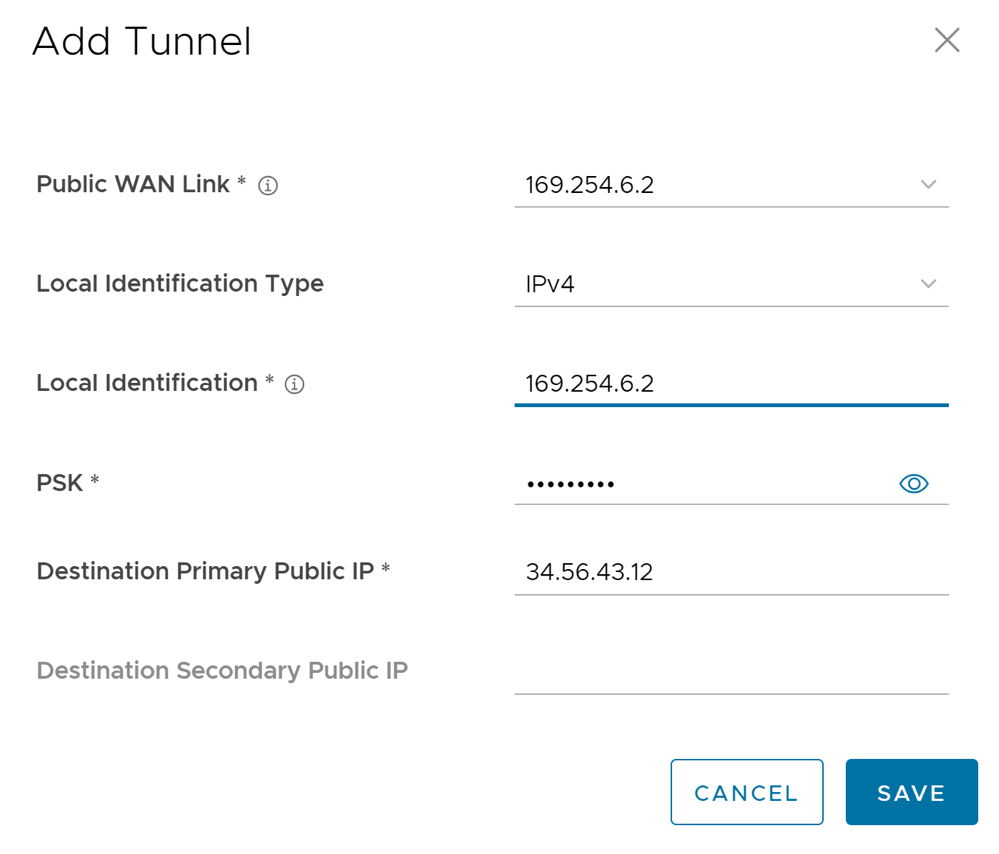
Associate a Microsoft Azure Non SD-WAN Destination to an Edge and Add Tunnels
At the Edge level, to associate a Non SD-WAN Destination to an Edge, perform the following steps:
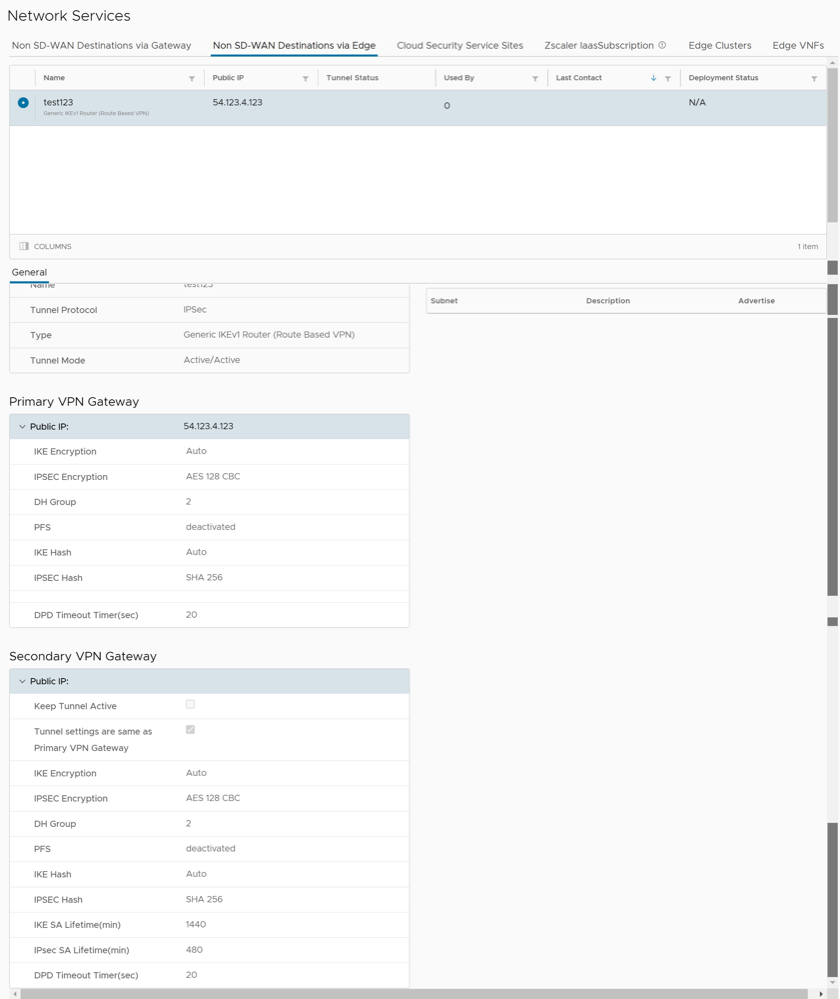
Monitor Non SD-WAN Destinations
- Non SD-WAN Destinations via Gateway- Displays the configured Non SD-WAN Destinations along with the other configuration details such as Name of the Non SD-WAN Destination, Public IP Address, Status of the Non SD-WAN Destination, Status of the tunnel, Number of profiles and Edges that use the Non SD-WAN Destination, Last contacted date and time, and Number of related state change Events.
- Non SD-WAN Destinations via Edge- Displays the configured Non SD-WAN Destinations along with the other configuration details such as Name of the Non SD-WAN Destination, Public IP Address, Status of the tunnel, Number of profiles and Edges that use the Non SD-WAN Destination, Last contacted date and time, and Deployment status.
Note: Tunnel deployment status monitoring is only supported for Non SD-WAN Destinations via Edge network service.
To monitor the automation deployment status of Microsoft Azure Non SD-WAN Destinations via Edge: