Test and Verify Security Policies
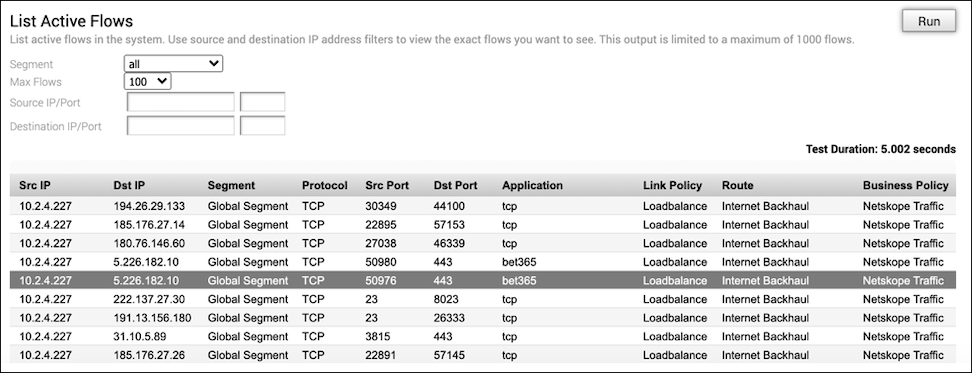
Configure security policies in the Netskope security cloud to validate connectivity between the Netskope and VeloCloud SD-WAN traffic.
Ensure that the IPSEC tunnels to both the Primary and Secondary Netskope POPs connected successfully.
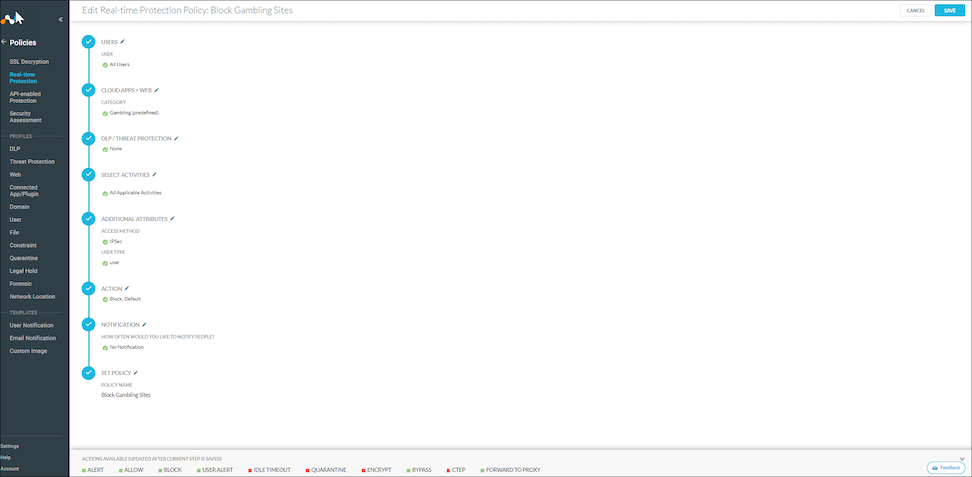
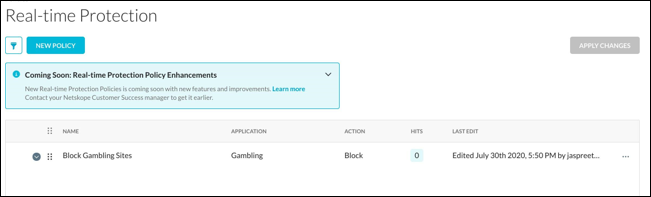
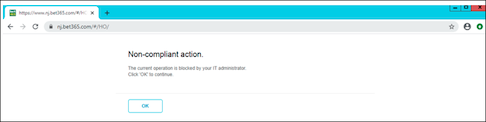
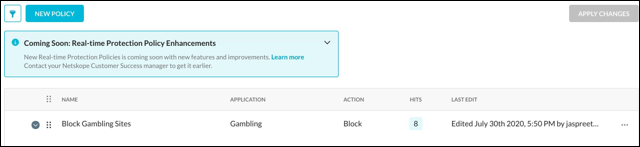
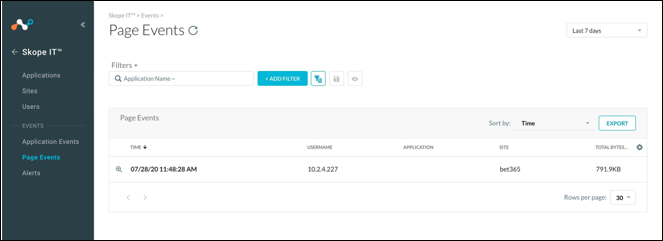
The following steps provide an example of blocking gambling-related websites by configuring the security policies.
Note: You can skip this procedure if you already have active production traffic through the portals.