Configure Amazon Web Services
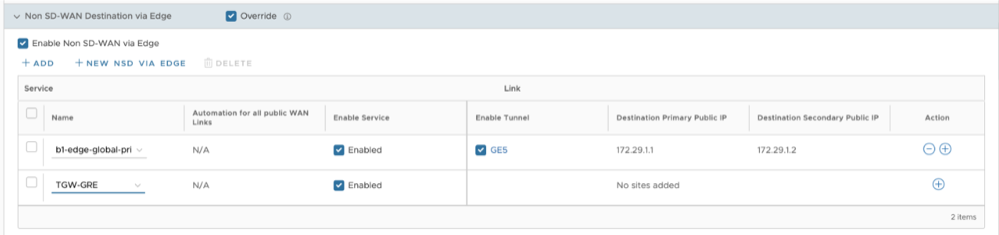
Arista VeloCloud supports Amazon Web Services (AWS) configuration in Non SD-WAN Destination.
- Obtain Public IP, Inside IP, and PSK details from the Amazon Web Services website.
- Enter the details you obtained from the AWS website into the Non- SD-WAN Network Service in the Orchestrator.
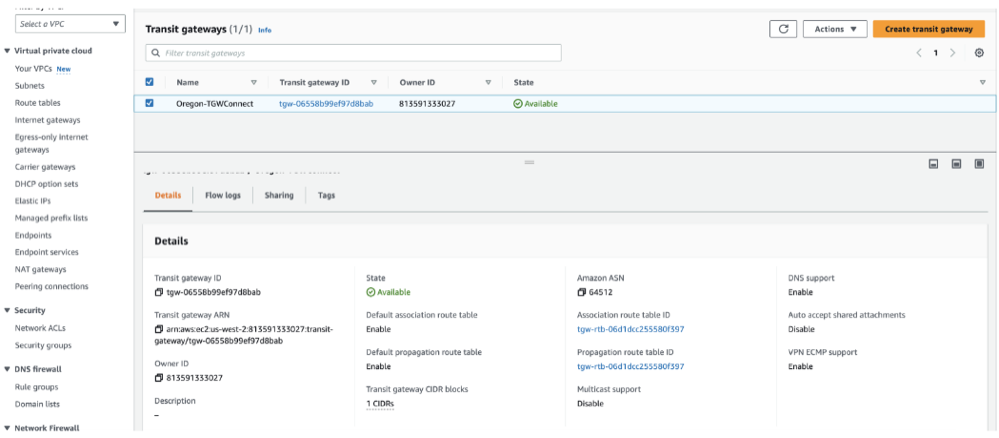
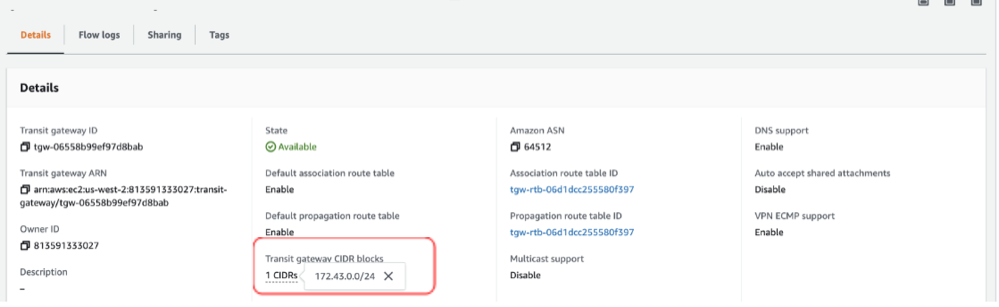
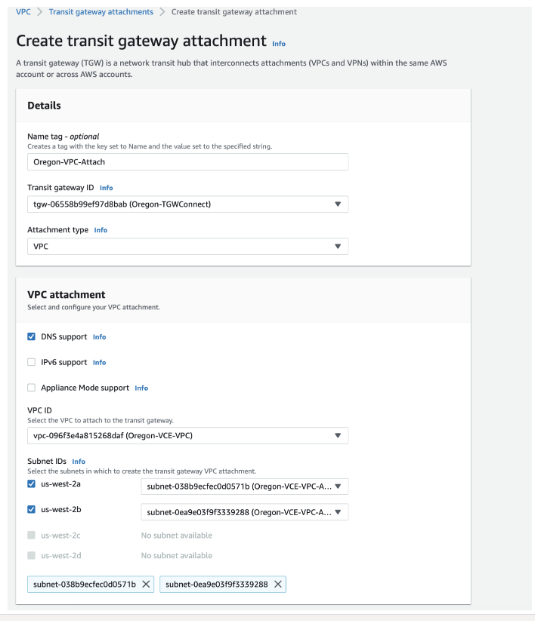
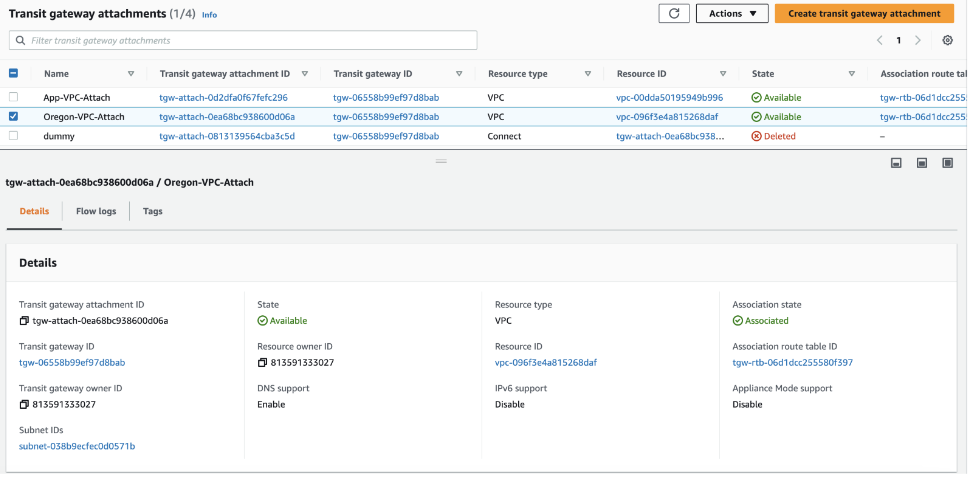
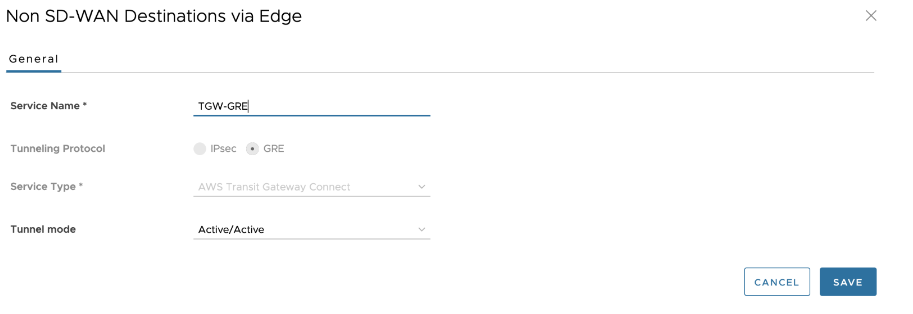
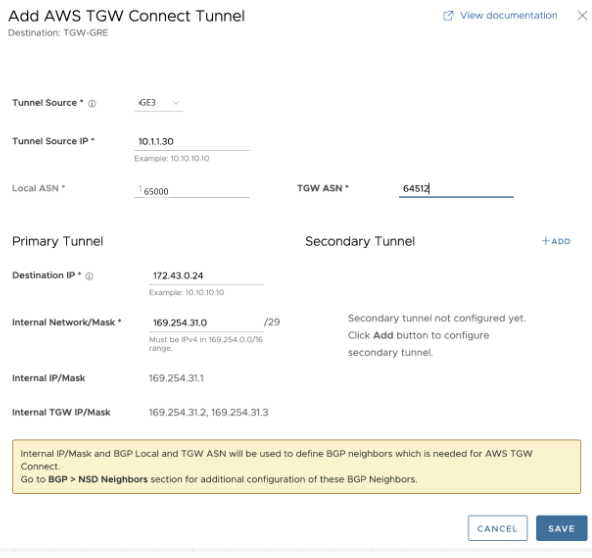
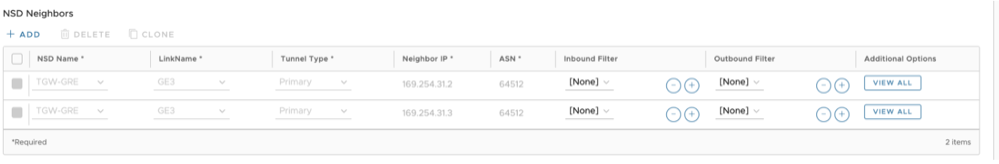
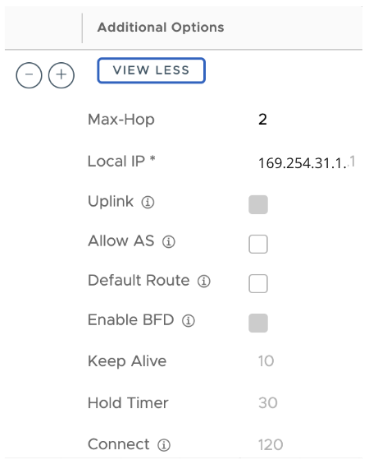
Configure Edge for Amazon Web Services (AWS) Transit Gateway (TGW) Connect Service
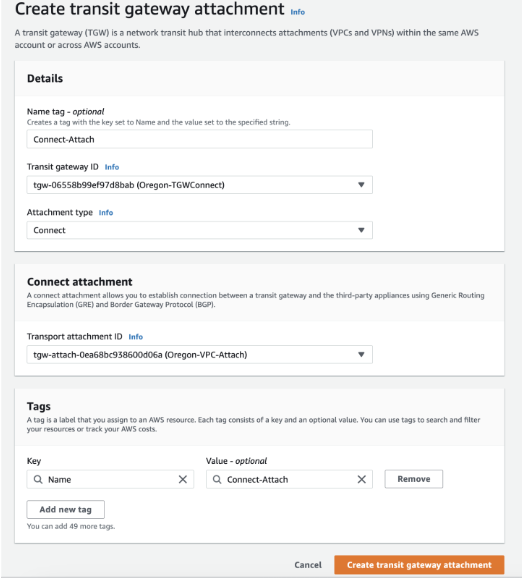
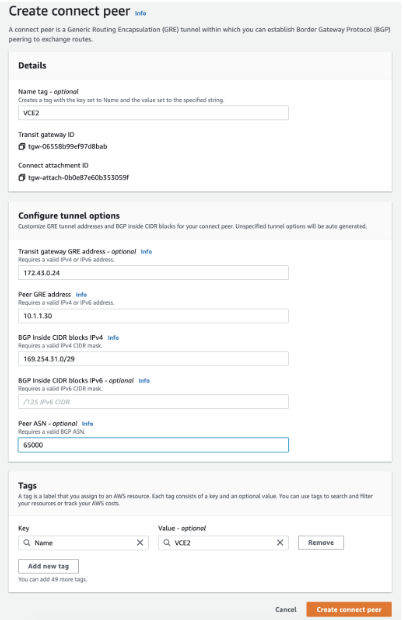
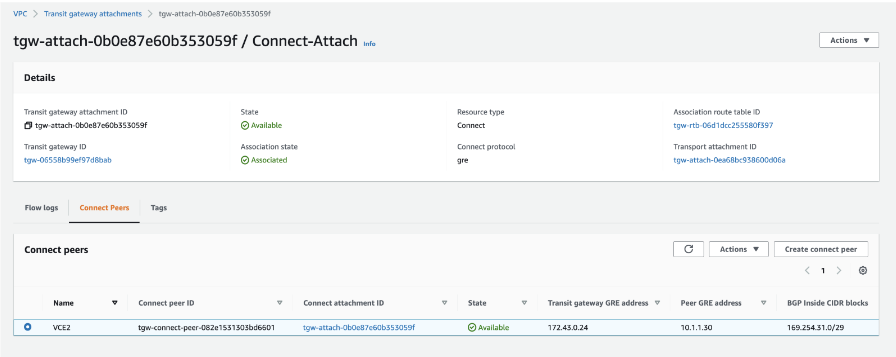
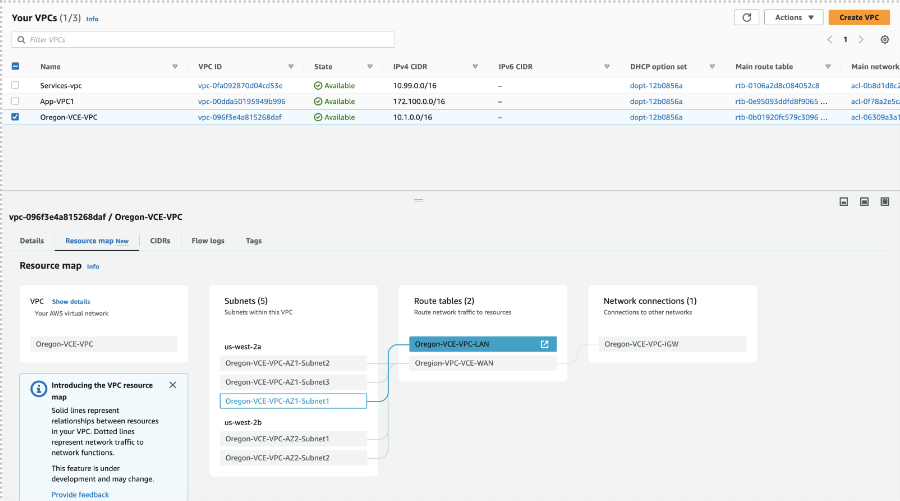
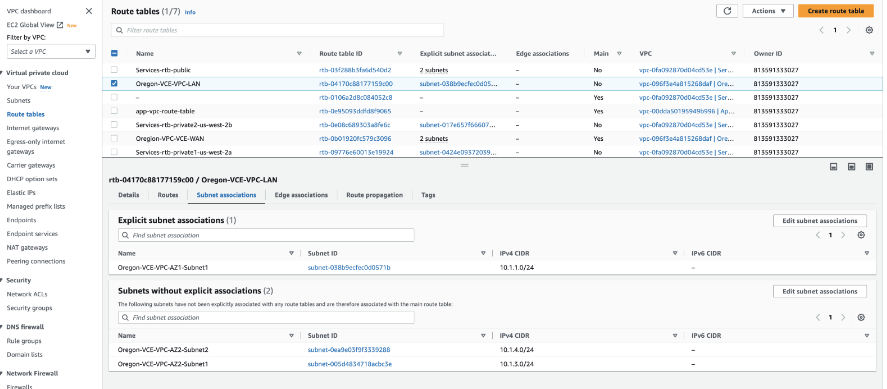
VeloCloud Edges typically get deployed in a Transit VPC on Amazon Web Services (AWS). AWS introduced the support for AWS TGW (Transit Gateway) Connect Service for SD-WAN appliances to connect to the Transit Gateway. VeloCloud Edge now has a feature (BGP over GRE support on LAN), which enables support on the VeloCloud Edge to use the AWS TGW Connect Service for connectivity to the AWS Transit Gateway.
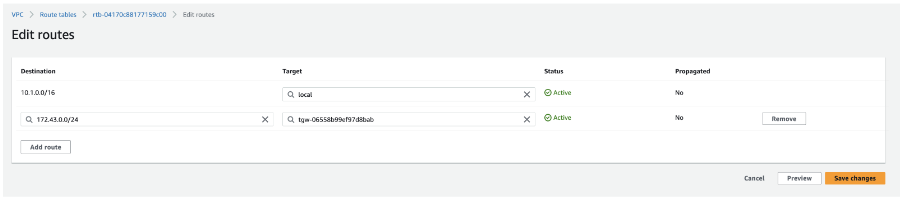
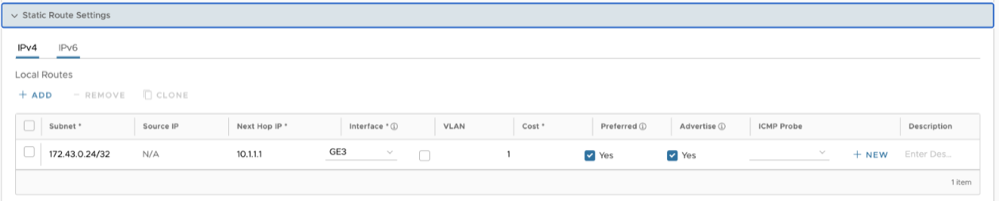
For the AWS TGW Connect Service, the Edge provisioned in the Transit VPC needs to use the LAN (routed, non-WAN) interface to set up the GRE tunnel. This effectively uses the Private IP configured on the Edge Intelligence (EI) to set up the GRE tunnel to the Transit Gateway.
To configure Amazon Web Services (AWS) Transit Gateway (TGW) Connect Service for Edges, perform the following steps:
Amazon Web Services (AWS) Configuration Procedure
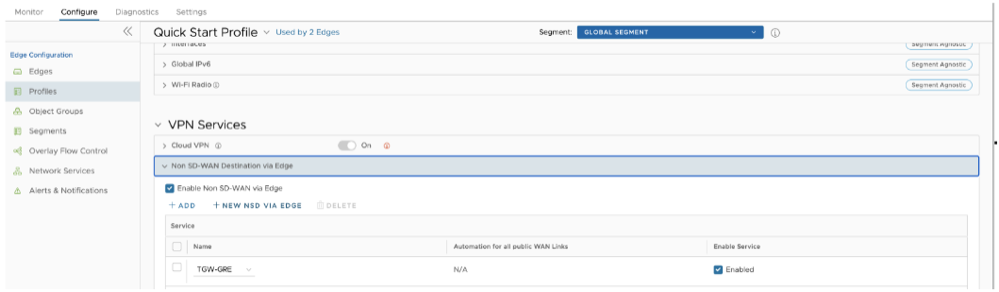
VeloCloud Orchestrator Configuration Procedure
Obtain Amazon Web Services Configuration Details
Discusses how to obtain Amazon Web Services configuration details.
- From Amazon's Web Services, create VPC and VPN Connections. Refer to the instructions in Amazon's documentation: http://awsdocs.s3.amazonaws.com/VPC/latest/vpc-nag.pdf.
- Make note of the Gateways associated with the enterprise account in the Orchestrator that might be needed to create a virtual private gateway in the Amazon Web Services.
- Make a note of the Public IP, Inside IP and PSK details associated with the Virtual Private Gateway. You need to enter this information in the Orchestrator when you create a Non SD-WAN Destination.
Configure a Non SD-WAN Destination
After you obtain Public IP, Inside IP, and PSK information from the Amazon Web Services (AWS) website, you can configure a Non SD-WAN Destination.